Avoid being scammed by fake "National UK Lottery" emails
Phishing/ScamAlso Known As: National UK Lottery spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the fake "National UK Lottery" email?
"National UK Lottery email scam" refers to a phishing spam campaign. The term "spam campaign" is used to define a mass-scale operation, during which thousands of deceptive emails are sent.
The messages sent through this spam campaign supposedly concern an extremely valuable prize from the "National UK Lottery" that the recipient has won and which has been mistakenly sent to a different address. Therefore, recipients are asked to pay storage fees and provide their personal information to have these packages shipped to them.
All information provided by these emails is false and is in no way associated with any official lotteries based in the United Kingdom or elsewhere. The goal of this spam campaign is to extract personal data and/or generate profit via payments received under false pretences.
More about the "National UK Lottery" scam email
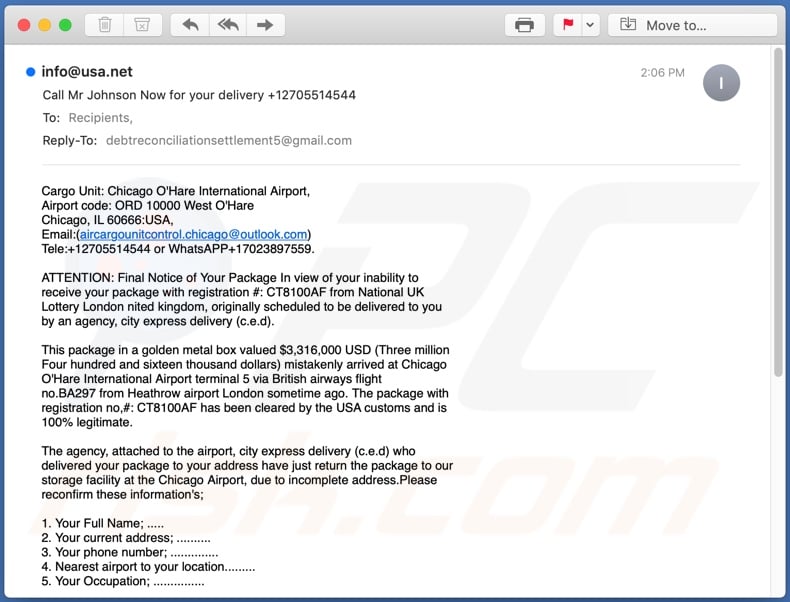
The "National UK Lottery" scam emails (with subject/title "Call Mr Johnson Now for your delivery +12705514544", which might vary) inform recipients that their packages from the "National UK Lottery" arrived at the Chicago O'Hare International Airport due to an error. The package has been verified as legitimate and cleared by US customs.
The nonexistent parcel allegedly contains a box made from gold and is valued at over three million US dollars. The package is currently in the storage facility at the Chicago Airport, as it cannot be shipped out due to an incorrect address.
The messages ask recipients to provide the following information: full name, current address, telephone number, occupation, and nearest airport in relation to their current location to have the parcel shipped to them. Additionally, the period of free storage has ended.
Therefore, recipients will start being charged US$125 (USD) per day until the fake package is sent out. Apparently, shipping is free of charge, however, storage is not indefinite and, unless users address the issues, the parcel will be listed as an unclaimed consignment and potentially seized.
As mentioned, the "National UK Lottery" emails are scams and none of the information provided by them is valid. The purpose of these messages is to trick recipients into providing their personal data and possibly embroil them into a scam featuring various bogus monetary transactions.
To summarize, by trusting the "National UK Lottery" scam emails, users can experience serious privacy issues, financial loss, and even identity theft.
| Name | National UK Lottery Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Scam emails claim that recipients' extremely valuable packages have arrived at the wrong address, and they need to provide the correct shipping information as well as pay the storage fees. |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similar scams in general
"Zoom Email Scam", "Deactivating All Inactive Accounts", "You Have Used Zoom Recently - I Have Very Unfortunate News" and "Google Forms Email Scam" are some examples of other spam campaigns.
The deceptive emails are usually presented as "official", "important", "urgent" and similar, and might even be disguised as mail from legitimate institutions, organizations, companies and other entities. Spam campaigns are not used just for phishing and other scams, they are also employed to proliferate Trojans, ransomware and other malware.
Regardless of what these messages claim, offer, request or demand, the purpose is to generate revenue for the scammers/cyber criminals behind them.
How do spam campaigns infect computers?
Systems are often infected via malicious files distributed through spam campaigns. These files can be attached and/or linked inside the emails. Infectious files can be in various formats (e.g. Microsoft Office and PDF documents, archive and executable files, JavaScript, etc.).
When these files are executed, run or otherwise opened, the infection process (i.e. malware download/installation) is triggered. For example, Microsoft Office documents (e.g. "Invoice_24077.xlsb") cause infections by executing malicious macro commands.
In Microsoft Office versions released prior to 2010, malware download/installation begins when an infectious document is opened, however, newer versions have "Protected View" mode that prevents automatic execution of macros.
Instead, users are asked to enable macro commands (i.e., to enable editing/content) and hence infection processes can only be started by manually enabling macros.
How to avoid installation of malware
To avoid malware spread via spam mail, you are strongly advised against opening suspicious or irrelevant emails, especially those with any attachments or links present within them. Additionally, use Microsoft Office versions released after 2010.
Malicious programs also proliferate through untrusted download channels (e.g. unofficial and free file-hosting sites, Peer-to-Peer sharing networks and other third party downloaders), illegal software activation ("cracking") tools, and fake updaters.
Therefore, only download from official/verified sources and activate and update software with tools/functions provided by legitimate developers. To ensure device integrity and user privacy, have a reputable anti-virus/anti-spyware suite installed and kept updated.
Furthermore, use these programs to run regular system scans and to remove detected/potential threats. If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "National UK Lottery" scam email message:
Subject: Call Mr Johnson Now for your delivery +12705514544
Cargo Unit: Chicago O'Hare International Airport,
Airport code: ORD 10000 West O'Hare
Chicago, IL 60666:USA,
Email:(aircargounitcontrol.chicago@outlook.com)
Tele:+12705514544 or WhatsAPP+17023897559.
ATTENTION: Final Notice of Your Package In view of your inability to
receive your package with registration #: CT8100AF from National UK
Lottery London nited kingdom, originally scheduled to be delivered to you
by an agency, city express delivery (c.e.d).
This package in a golden metal box valued $3,316,000 USD (Three million
Four hundred and sixteen thousand dollars) mistakenly arrived at Chicago
O'Hare International Airport terminal 5 via British airways flight
no.BA297 from Heathrow airport London sometime ago. The package with
registration no,#: CT8100AF has been cleared by the USA customs and is
100% legitimate.
The agency, attached to the airport, city express delivery (c.e.d) who
delivered your package to your address have just return the package to our
storage facility at the Chicago Airport, due to incomplete address.Please
reconfirm these information's;
1. Your Full Name; .....
2. Your current address; ..........
3. Your phone number; ..............
4. Nearest airport to your location.........
5. Your Occupation; ...............
Therefore, I am writing to inform you that the days of grace has elapsed
and we shall begin to charge the daily storage fee of $125 USD ONLY, and
the fee will be direct to united nation head office Benin Republic. Please
call: Mr Johnson Nugent UN AGENT, on +12705514544 or WhatsAPP+1703897559
he will email you the name to wire the money to united nation head office
Benin Republic. Extension 21 terminal 5 or contact Email
address:(aircargounitcontrol.chicago@outlook.com)
to release this package directly to you.
Note that this notice serves as our last recovery notice to you as our
department will be compelled to shortlist your package as an unclaimed
consignment, and maybe forfeited. Note: Delivery of your package from the
airport to your residential address is free.
Best regards,
Mrs Sandra Leon
STORAGE OFFICER Terminal 5 Extension 11
Phone:+1703897559.
Consignment from United nation payment Delegation west Africa state.
Mrs Sandra Leon
UN CHIEF ON PAYMENT MATTERS.
Benin Republic
Whatsap Number: +17023897559
Appearance of the "National UK Lottery" scam email (GIF):
A German variant of national UK lottery-themed spam email:
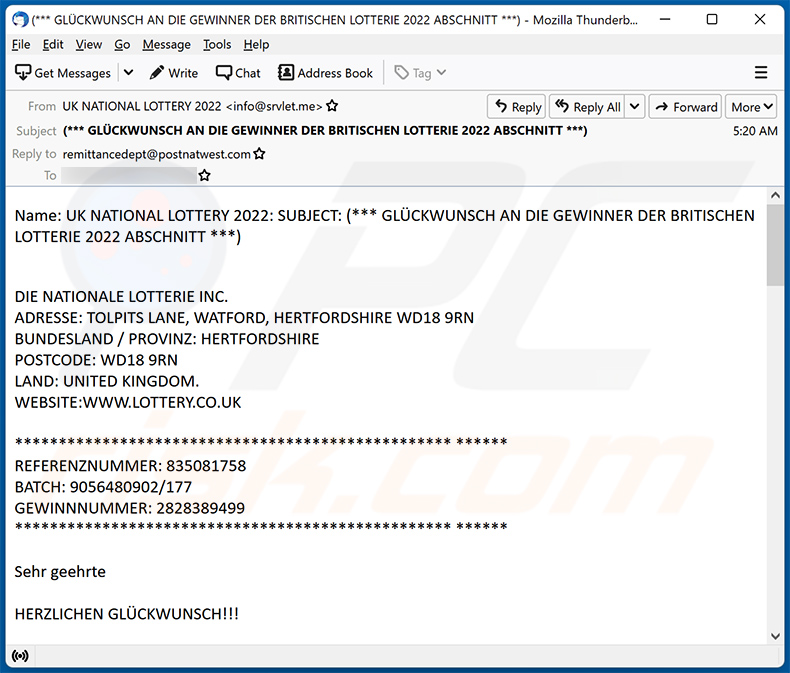
Text presented within:
Subject: (*** GLÜCKWUNSCH AN DIE GEWINNER DER BRITISCHEN LOTTERIE 2022 ABSCHNITT ***)
Name: UK NATIONAL LOTTERY 2022: SUBJECT: (*** GLÜCKWUNSCH AN DIE GEWINNER DER BRITISCHEN LOTTERIE 2022 ABSCHNITT ***)
DIE NATIONALE LOTTERIE INC.
ADRESSE: TOLPITS LANE, WATFORD, HERTFORDSHIRE WD18 9RN
BUNDESLAND / PROVINZ: HERTFORDSHIRE
POSTCODE: WD18 9RN
LAND: UNITED KINGDOM.
WEBSITE:WWW.LOTTERY.CO.UK
************************************************** ******
REFERENZNUMMER: 835081758
BATCH: 9056480902/177
GEWINNNUMMER: 2828389499
************************************************** ******
Sehr geehrte
HERZLICHEN GLÜCKWUNSCH!!!
Wir, die Geschäftsführer der United Kingdom National Lottery Inc, informieren Sie hiermit per E-Mail über die Ergebnisse des Ballot Lottery International Program. Die letzten Züge wurden am 10. Mai.2022 durchgeführt. Ihr E-Mail-Konto wurde als Gewinner für den £ 4.500.000,00 GBP (£ 4,5 Millionen GBP) Bargeldpreis ausgewählt. Dieses Ergebnis wird Ihnen heute, am 19. Mai.2022, mitgeteilt, und Ihre E-Mail-Adresse in der Kategorie Eins hat £ 4,5 Millionen,00 GBP (£ 4,5 Millionen britische Pfund Sterling) gewonnen.
Die Geschäftsleitung der UK National Lottery Inc, Zahlungsabteilung: Hiermit wird Ihnen rechtlich bescheinigt, dass Sie als rechtmäßiger und glücklicher Gewinner und Empfänger der genehmigten Zahlung von £ 4,5 Millionen,00 GBP im Vereinigten Königreich, National Annual Lottery Programs, Kapitel 22, Abschnitt 107A, in dem Ihr E-Mail-Konto als der glückliche Gewinner ausgewählt wurde, in der dritten (3) Kategorie mit der genehmigten Zahlung von £ 4.500.000,00 Britische Pfund Sterling, sind.
Zahlungsreferenznummer: - *** (National Lottery.- REF NO: .835081758 / STAPEL NO: .8687869789 / 657) ***Aus Sicherheitsgründen): - Bitte teilen Sie uns umgehend mit, dass diese E-Mail-Adresse Ihnen gehört und für die Bearbeitung Ihres Gewinnscheins sowie für die sofortige Bearbeitung der genehmigten Zahlung von £4.500.000,00 GBP an Sie als rechtmäßigen Begünstigten verwendet wird.
Wir bitten um Ihre sofortige Antwort.Dies ist Teil unseres Sicherheitsprotokolls, um doppelte Ansprüche und ungerechtfertigten Missbrauch dieses Programms durch Betrug zu vermeiden, zu vermeiden. Sie müssen Ihre Gewinne spätestens bis zum 15.Oktober .2022 einfordern. Nach diesem Datum werden alle nicht beanspruchten Gelder an unser Zentralbüro zurückgegeben (als nicht beansprucht). Bitte beachten Sie, dass Sie, um unnötige Verzögerungen und Komplikationen zu vermeiden, in Ihrer gesamten Korrespondenz mit uns immer Ihre REF-NUMMER: 835081758 angeben müssen. Wir informieren Sie daher darüber, wie Sie Ihren Gewinn einfordern können.
Sie müssen die Bank direkt über ihre Bankverbindung kontaktieren.
=============================================
Kontakt: National Westminster Bank Plc:
Adresse:#135 Bishopsgate London EC2M 3UR
Code :2021-HK78 / 890.74
Kontaktperson: Mr. Patrick Flynn.
EMAIL: remittancedept@postnatwest.com
=============================================
Zur Bearbeitung und Bestätigung Ihres Gewinns füllen Sie bitte das untenstehende Formular aus und reichen es bei der auszahlenden Bank ein: National Westminster Bank Plc, Zahlungszentrum von E-MAIL: remittancedept@postnatwest.com
==================================================
{DIE NATIONALE LOTTERIE GEWINNER ANMELDEFORMULAR FÜR DIE ZAHLUNG}.
**************************************************
VORNAME...............
NACHNAME...............
GEBURTSDATUM .............
FAMILIENSTAND ...........
GESCHLECHT................
ADRESSE..............
NATIONALITÄT.............
BERUF............
TELEFONNUMMER ............
GEWINNSUMME ............
************************
REFERENZNUMMER, 835081758
************************
GEWINNNUMMER: 2828389499
************************
ZUR ZAHLUNG FREIGEGEBEN
==================================================
Wir bitten um Ihre sofortige Antwort.
Unterzeichnet,
Dipl.-Ing. Dr.-Ing. E.h.,Friedrich
Ingelmann Geschäftsführung:
Hans-Peter Thomas
Vorsitzender)
David KarlCopyright © 2022 UK. Nationale Lotterie. Alle Rechte vorbehalten. Bedingungen und Konditionen Hilfe Hinweis: Auf diesen Seiten sammeln wir persönliche Informationen. Für weitere Einzelheiten lesen Sie bitte unsere Datenschutzrichtlinie
Another example of an email from "National UK Lottery" email scam:
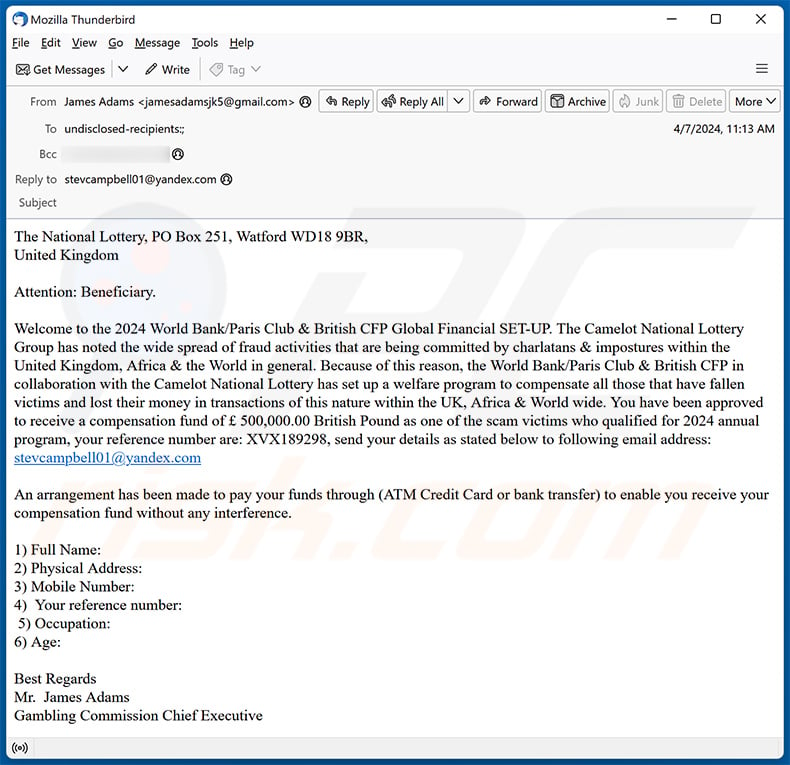
Text presented within:
The National Lottery, PO Box 251, Watford WD18 9BR,
United KingdomAttention: Beneficiary.
Welcome to the 2024 World Bank/Paris Club & British CFP Global Financial SET-UP. The Camelot National Lottery Group has noted the wide spread of fraud activities that are being committed by charlatans & impostures within the United Kingdom, Africa & the World in general. Because of this reason, the World Bank/Paris Club & British CFP in collaboration with the Camelot National Lottery has set up a welfare program to compensate all those that have fallen victims and lost their money in transactions of this nature within the UK, Africa & World wide. You have been approved to receive a compensation fund of £ 500,000.00 British Pound as one of the scam victims who qualified for 2024 annual program, your reference number are: XVX189298, send your details as stated below to following email address: stevcampbell01@yandex.com
An arrangement has been made to pay your funds through (ATM Credit Card or bank transfer) to enable you receive your compensation fund without any interference.1) Full Name:
2) Physical Address:
3) Mobile Number:
4) Your reference number:
5) Occupation:
6) Age:Best Regards
Mr. James Adams
Gambling Commission Chief Executive
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is National UK Lottery spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Scammers send out mass emails, identical to thousands of others, in hopes of tricking someone into taking the bait. These emails are not personalized and are sent out in bulk.
I have provided my personal information when tricked by this email, what should I do?
Contact the corresponding authorities and monitor your accounts closely for any signs of unauthorized activity. In addition, consider changing any compromised passwords and enabling extra security measures.
I have downloaded and opened a malicious file attached to an email, is my computer infected?
The possibility of infection depends on the type of malicious file you downloaded and opened. Some file types, like executable files (.exe), are more likely to contain malware that can infect your system, while others, like documents or images, may pose less of a threat.
I have sent cryptocurrency to the address presented in such email, can I get my money back?
No, cryptocurrency transactions are typically irreversible, so it is unlikely to retrieve your funds once they have been sent.
I have read the email but did not open the attachment, is my computer infected?
Merely opening an email poses no threat. However, clicking on links or opening attachments can result in system infections.
Will Combo Cleaner remove malware infections that were present in email attachment?
Combo Cleaner effectively detects and removes most known malware. Advanced malware may hide deeply within the system, necessitating a full system scan for comprehensive removal.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion