Do not participate in the Cardano fake giveaway
Phishing/ScamAlso Known As: Fake Cardano cryptocurrency giveaway
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Cardano giveaway scam?
Cardano is the name of a legitimate blockchain platform, and the cryptocurrency which operated in its network is called ADA. There are many cryptocurrency giveaway scams on the Internet offering to receive a certain amount of cryptocurrency in exchange for contribution in the "giveaway".
Simply said, scammers behind such scams attempt to steal cryptocurrency from unsuspecting people. It is common that scam websites (fake giveaways) like this one are promoted through deceptive advertisements, other shady pages, videos on YouTube, or potentially unwanted applications (PUAs) that users unknowingly install on their browsers or computers.
Usually, cryptocurrency giveaway scams declare that contributors' funds will be doubled if they send an initial amount to the provided crypto wallet address. Whoever participates in these fake giveaways receives nothing in return.
This particular scam offers to double ADA (Cardano's internal cryptocurrency). This fake giveaway claims to run a 100,000.000 ADA giveaway where users can send from 5,000 ADA to 50,000 ADA to the contribution address and promises to return twice as much ADA sent immediately.
It also offers bonuses, for example, 10% for 50,000+ ADA, 20% for 100,000+ ADA, 40% for 250,000+ ADA, and 50% for 500,000+ ADA and claims that users can participate in this giveaway only once. Simply said, scammers attempt to trick unsuspecting users to send more of the Cardano's cryptocurrency than they probably would if they could participate in a giveaway more than once.
This scam page also has a fake counter supposedly indicating how much people have already participated in a giveaway to lure users into sending ADA cryptocurrency without taking too long to think about it. In conclusion, scams (fake cryptocurrency or other giveaways) like this one have to be ignored.
Users who send cryptocurrency to the addresses provided in these scams never receive anything in return. They simply lose the cryptocurrency they have transferred.
As mentioned in the introduction, it is common for such scams to be promoted via PUAs. Apps of this type can be designed to collect certain information and serve advertisements as well.
It is common that PUAs gather details like IP addresses, geolocations, addresses of visited websites, entered search queries, etc. In some cases, they are capable of accessing sensitive information.
The biggest problem is that developers of PUAs are likely to sell gathered data to third parties (potentially cyber criminals) or monetize it in other ways.
Also, PUAs can be designed to generate coupons, banners, pop-up ads, surveys, or other advertisements that could be used to promote shady pages or distribute other PUAs. There are ads that can cause unwanted downloads or even installations.
| Name | Fake Cardano cryptocurrency giveaway |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Participants can double their ADA cryptocurrency |
| Scammer Crypto Wallet Address |
addr1qy0hf7rkkgpu94raw07lulkpvs70gcq0m86yrcfty65 ruvh7ktwhp7rsmrf30w678mknrc767aj7fratdsfjk0yz8myqz3u7zd |
| Related Domain | ada-cardano[.]us, cardano[.]gift, cardano-binance[.]net |
| Detection Names | CyRadar (Malicious), Emsisoft (Phishing), Kaspersky (Phishing), Netcraft (Malicious), Full List Of Detections (VirusTotal) |
| Serving IP Address | 186.2.161.160 |
| Symptoms | Fake error messages, fake system warnings, pop-up errors, hoax computer scan. |
| Distribution methods | Compromised websites, rogue online pop-up ads, potentially unwanted applications. |
| Damage | Monetary loss |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
More examples of fake giveaways are "Doge Giveaway", "BTC giveaway", and "Double Your Bitcoins". It is noteworthy that names of people like Elon Musk, Jeff Bezos, Steve Wozniak, Bill Gates, etc., are often used to promote these scams.
If a browser opens scam pages of other untrustworthy pages by itself regularly, then it is likely that it has some PUA installed on it. Typically, users download and install apps of this type unknowingly.
How did potentially unwanted applications install on my computer?
Typically, developers distribute potentially unwanted applications by including them in downloaders or installers of other programs as additional offers. This distribution method is known as "bundling". In most cases, users can decline offers to download or install PUAs via Custom", "Advanced", or other settings, or by unticking checkboxes before completing downloads, installations.
However, if users download or install programs without checking and changing the aforementioned settings, they often agree to download or install bundled applications as well. Sometimes users cause unwanted downloads, installations by clicking on deceptive advertisements that are designed to execute certain scripts. It is noteworthy that ads of this type appear mostly on shady, unreliable websites.
How to avoid installation of potentially unwanted applications?
Downloaders, installers that have settings like "Advanced" "Custom", "Manual", or include checkboxes should be examined: they should be checked for offers to download or install bundled unwanted applications. Files and programs should be downloaded from official web pages, and via direct links.
Other channels for downloading them like unofficial pages, through third-party downloaders, Peer-to-Peer networks (e.g., torrent clients, eMule) and so on, are not trustworthy. Advertisements that appear while visiting some questionable pages should not be clicked as well.
It is common that users who click on those ads open other sites of this kind or allow those ads to execute scripts that cause download, or even installation of unwanted software. Unwanted, unknown, suspicious applications (e.g., extensions, plug-ins, add-ons) installed on a browser should be removed.
Any software of this kind installed on the operating system should be uninstalled too. If your computer is already infected with PUAs, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
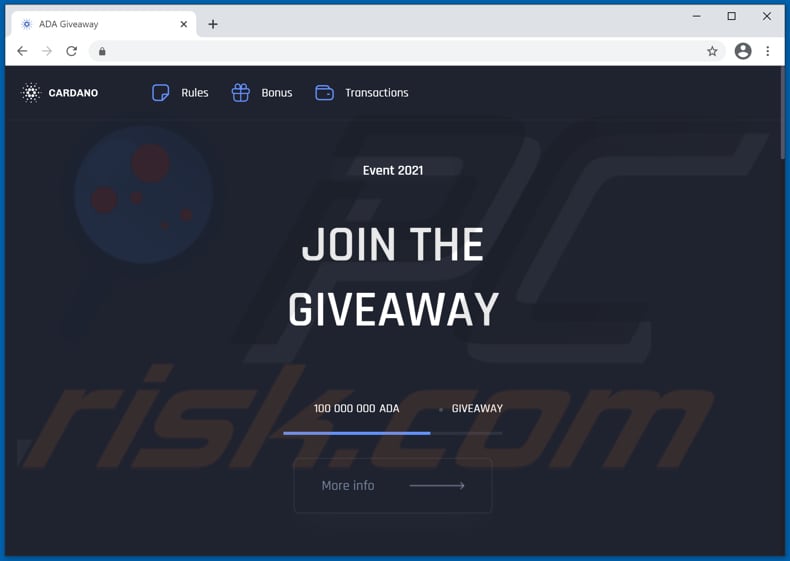
The appearance of Cardano giveaway scam website (GIF):
Text in this website:
Event 2021
JOIN THE GIVEAWAY
More info100 000 000
ADA • GIVEAWAY
We believe that Blockchain and ADA coin will make the world more fair. To speed up the process of cryptocurrency mass adoption, We decided to run 100.000.000 ADA giveaway. To participate you just need to send from 5,000 ADA to 500,000 ADA to the contribution address and we will immediately send you back 10,000 ADA to 1,000,000 ADA (x2 back) to the address you sent it from.NOTE: You can do it only one time.
For example:
Send 5,000 ADA, you will be get 10,000 ADA back.
Send 10,000 ADA, you will be get 20,000 ADA back.
Send 50,000 ADA, you will be get 100,000 ADA back.
Send 100,000 ADA, you will be get 200,000 ADA back.
Send 250,000 ADA, you will be get 500,000 ADA back.
Send 500,000 ADA, you will be get 1,000,000 ADA back.
Contribution Special BONUS:
50,000+ ADA = 10% Bonus
100,000+ ADA = 20% Bonus
250,000+ ADA = 40% Bonus
500,000+ ADA = 50% Bonus
Payment Address
You can send ADA to the following address:addr1qy0hf7rkkgpu94raw07lulkpvs70gcq0m86yrcfty65 ruvh7ktwhp7rsmrf30w678mknrc767aj7fratdsfjk0yz8myqz3u7zd
Waiting for payment
100 000 000/43 443 000
Last chance to get your ADA!
43.443
Instruction
To make a transaction, you can use any wallet or exchange to participate!
Once we receive your transaction, the outgoing transaction is processed to your address.
Once we receive your transaction, we will immediately send the requested amount back to you.
Every address that is sent too late, gets their ADA immediately sent back.
Transactions for Address
addr1qy0hf7rkkgpu94raw07lulkpvs70gcq0m86yrcfty65 ruvh7ktwhp7rsmrf30w678mknrc767aj7fratdsfjk0yz8myqz3u7zd
Another example of a Cardano giveaway-themed scam website:
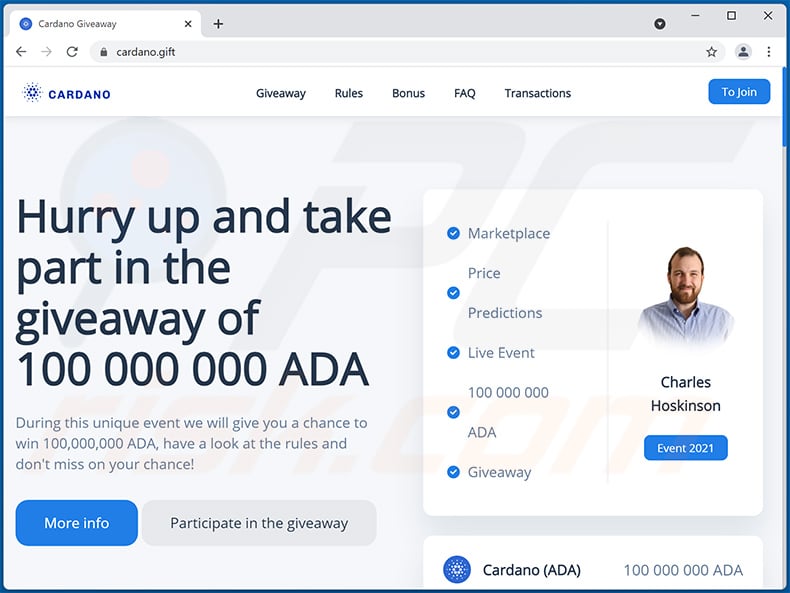
Text presented within:
Giveaway Rules Bonus FAQ Transactions
To Join
Hurry up and take part in the giveaway of
100 000 000 ADA
During this unique event we will give you a chance to win 100,000,000 ADA, have a look at the rules and don't miss on your chance!
More info Participate in the giveaway
Marketplace
Price Predictions
Live Event
100 000 000 ADA GiveawayEvent 2021
Cardano (ADA)
100 000 000 ADA
About
We believe that Blockchain and ADA coin will make the world more fair. To speed up the process of cryptocurrency mass adoption, We decided to run 100 000 000 ADA giveaway.
Rules
To participate you just need to send from 2,500 ADA to 1,000,000 ADA to the contribution address and we will immediately send you back - 5,000 ADA to 2,000,000 ADA (x2) to the address you sent it from.
Bonus
For example
If you send
2,500+ ADA , you will get 5,000+ ADA back.
If you send 5,000+ ADA, you will get 10,000+ ADA back.
If you send 10,000+ ADA, you will get 20,000+ ADA back.
If you send 25,000+ ADA, you will get 50,000+ ADA back.
If you send 50,000+ ADA, you will get 100,000+ ADA back.
If you send 100,000+ ADA, you will get 200,000+ ADA back.
Extra bonuses
10,000+ ADA = 20% Bonus
25,000+ ADA = 30% Bonus
100,000+ ADA = 40% Bonus
500,000+ ADA = 50% Bonus
You can only participate once.31 715 016 ADA already sent to participants!
Hurry up and take part in the giveaway!
Use this QR code to participate31 715 016 ADA
100 000 000 ADA
You can send ADA to the following address:
addr1qxlettls0xnmsctdfrj3a3rx7n3z3ry0hcz4dygdr4q9tfd czmevay8rzefmjyvh7yymnpplrzldfehspa9kda6dkacsckd4qcWaiting for payment
FAQ
What do I have to do to participate in the giveaway?
How long will it take me to get my bonus?
Who is the sponsor of this giveaway?
How many times can I participate in the giveaway?
How do I get my bonus?
Transactions for Address
addr1qxlettls0xnmsctdfrj3a3rx7n3z3ry0hcz4dygdr4q9tfd czmevay8rzefmjyvh7yymnpplrzldfehspa9kda6dkacsckd4qc
Giveaway Rules Bonus FAQ Transactions
To Join
Yet another example of Cardano (ADA) giveaway-themed scam website (cardano-binance[.]net):
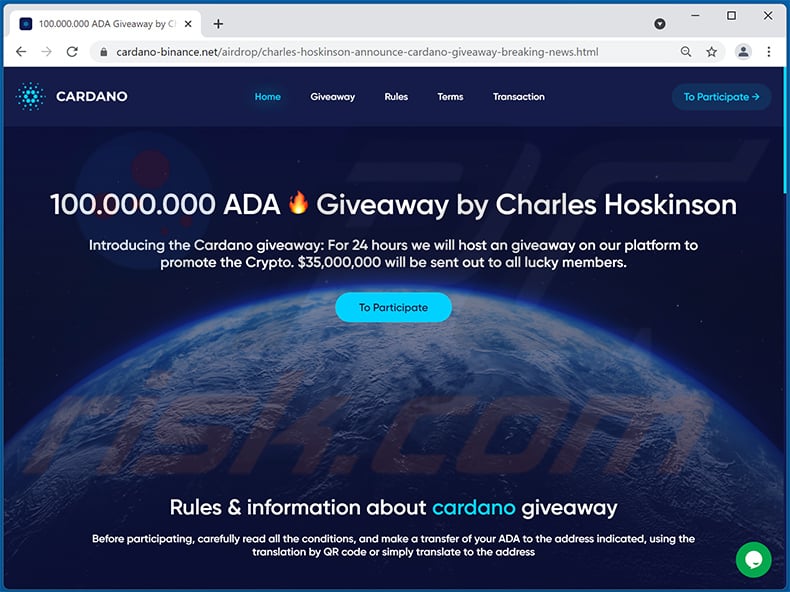
Text presented within:
To Participate →
100.000.000 ADA
Giveaway by Charles Hoskinson
Introducing the Cardano giveaway: For 24 hours we will host an giveaway on our platform to promote the Crypto. $35,000,000 will be sent out to all lucky members.To Participate
Rules & information about cardano giveaway
Before participating, carefully read all the conditions, and make a transfer of your ADA to the address indicated, using the translation by QR code or simply translate to the address
About cardano giveaway eventDuring this unique event we will give you a chance to win 100 000 000 ADA, have a look at the rules and don't miss on your chance! You can only participate once!
Rules & informationTo participate you just need to send from 1 000 ADA to 1 000 000 ADA to the contribution address and we will immediately send you back 2 000 ADA to 2 000 000 ADA (x2) to the address you sent it from.
Terms of our distribution→ You can participate only once;
→ The number of coins for distribution is limited;
→ Hurry up and get your coins
You can send ADA to the following address:
addr1q82hv2mldjz0g8a7chv4mnhlkhwc76gljaa33qk7q697twltc78n72zqy7y4pml2xm7qy746xz8a88yd30xzs724llqse0d32h
COPY ADDRESS TO CLIPBOARD
Waiting for paymentHow can I participate?
Everything is very simple, carefully read each paragraph, and you will definitely succeed!
To make a transaction, you can use any wallet or exchange to participate!
Once we receive your transaction, the outgoing transaction is processed to your address.
Once we receive your transaction, we will immediately send the requested amount back to you.
Every address that is sent too late, gets their ADA immediately sent back.LIVE TRANSACTIONS
addr1q82hv2mldjz0g8a7chv4mnhlkhwc76gljaa33qk7q697twltc78n72zqy7y4pml2xm7qy746xz8a88yd30xzs724llqse0d32h
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Cardano giveaway scam?
- STEP 1. Uninstall deceptive applications using Control Panel.
- STEP 2. Remove rogue extensions from Google Chrome.
- STEP 3. Remove potentially unwanted plug-ins from Mozilla Firefox.
- STEP 4. Remove rogue extensions from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
- STEP 6. Remove adware from Internet Explorer.
Removal of potentially unwanted applications:
Windows 11 users:
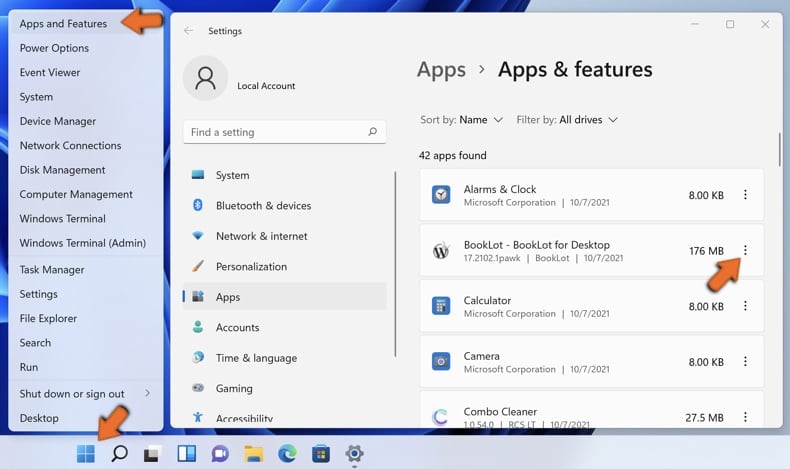
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
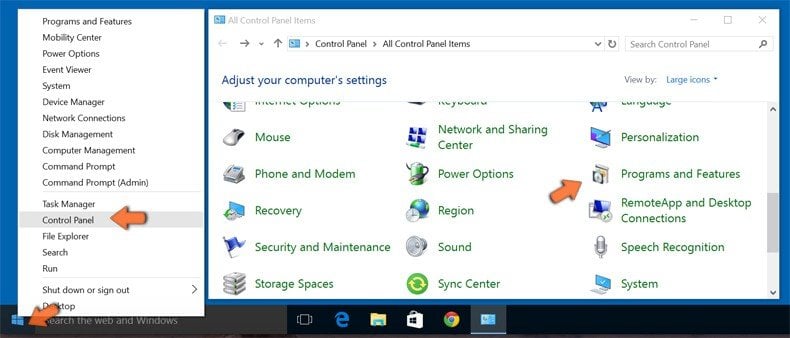
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.
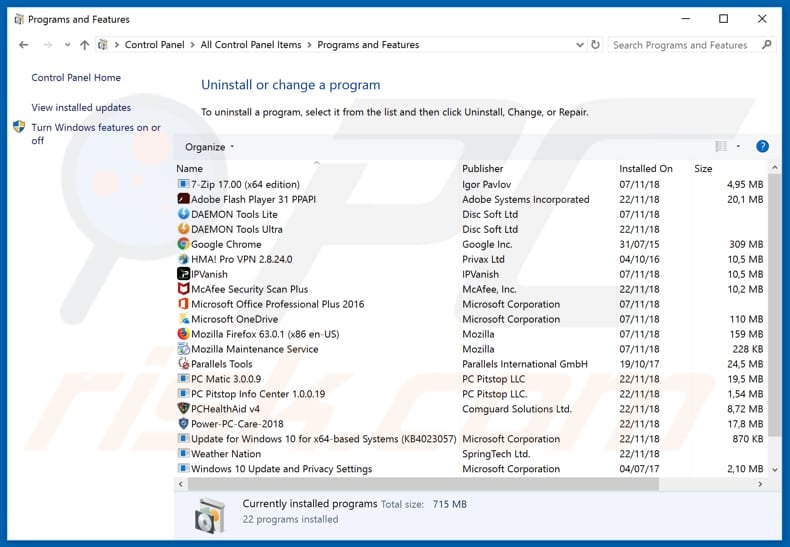
In the uninstall programs window, look for any suspicious/recently-installed applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the potentially unwanted application, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove rogue extensions from Internet browsers:
Video showing how to remove potentially unwanted browser add-ons:
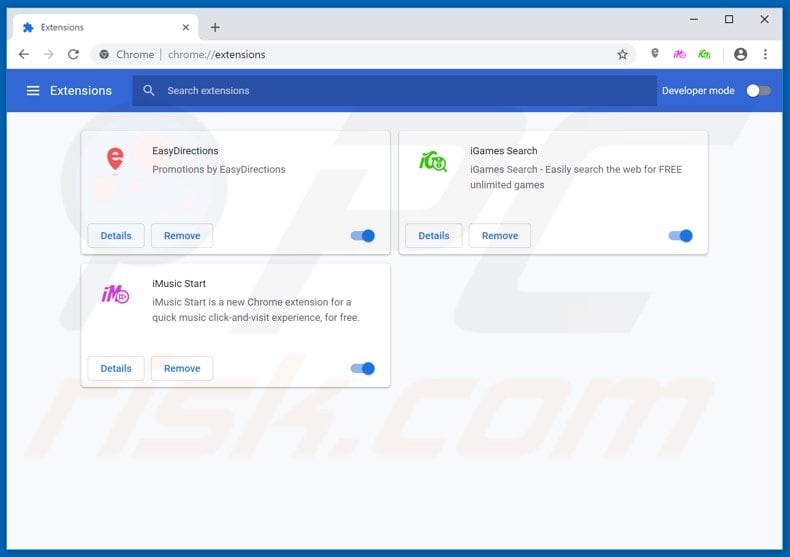
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
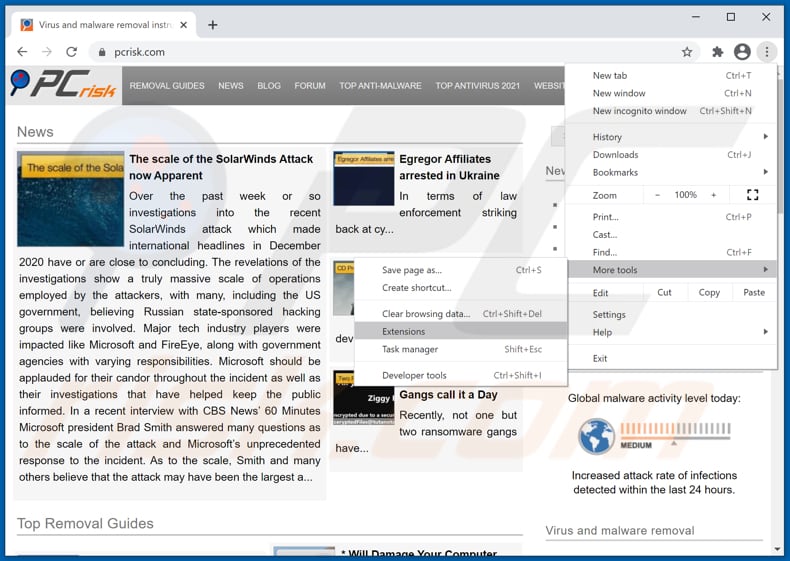
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate all recently-installed suspicious browser add-ons and remove them.
(at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate all recently-installed suspicious browser add-ons and remove them.
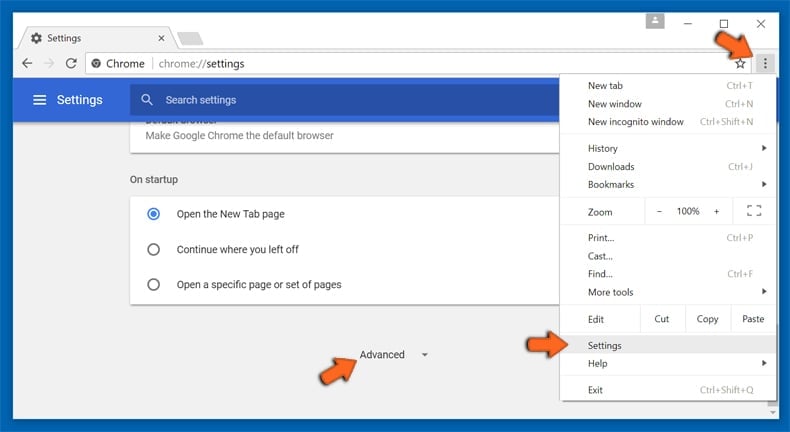
Optional method:
If you continue to have problems with removal of the fake cardano cryptocurrency giveaway, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
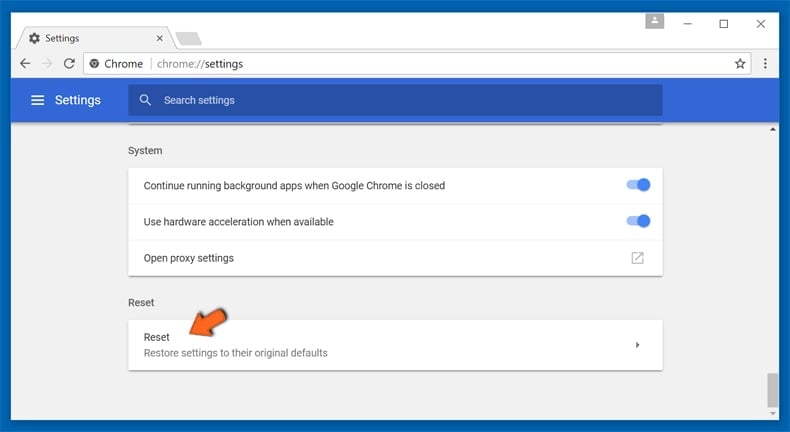
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
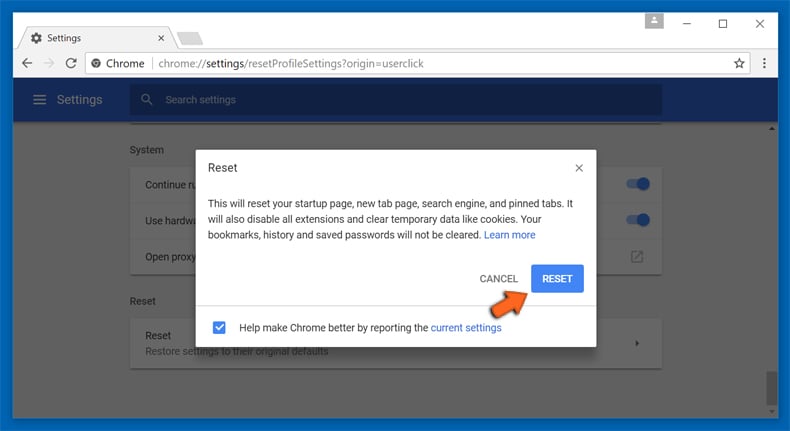
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious plugins from Mozilla Firefox:
Remove malicious plugins from Mozilla Firefox:
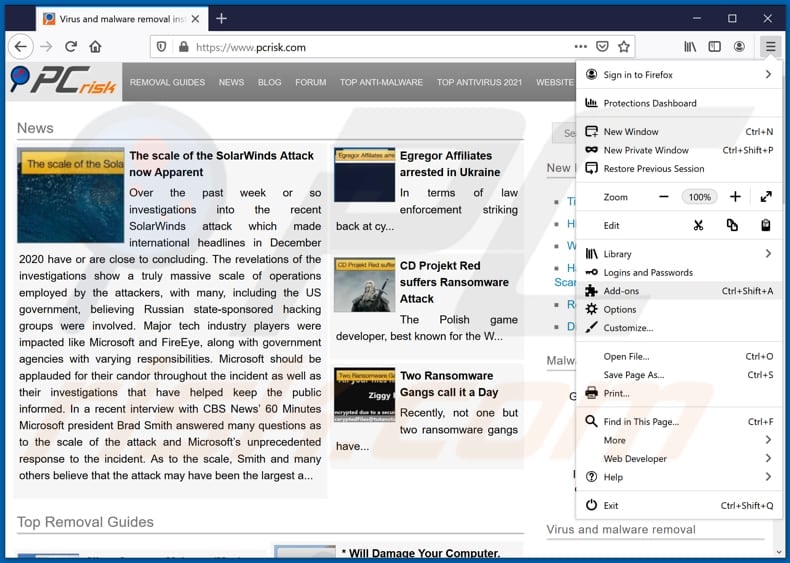
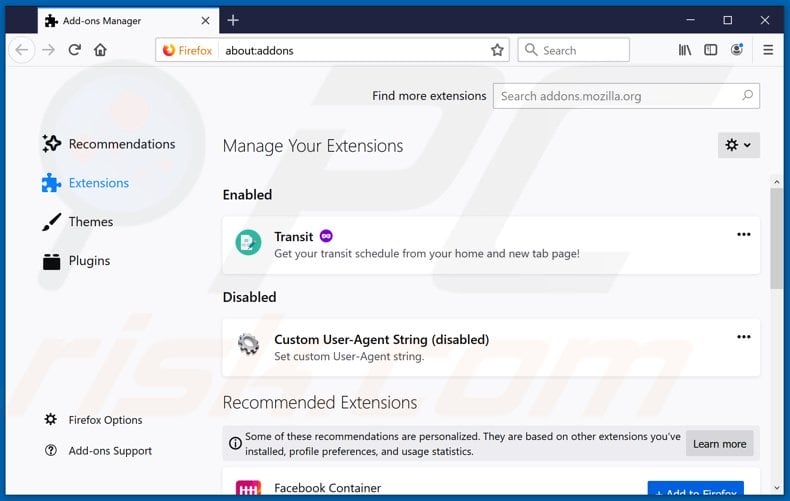
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons". Click on "Extensions", in the opened window remove all recently-installed suspicious browser plug-ins.
(at the top right corner of the main window), select "Add-ons". Click on "Extensions", in the opened window remove all recently-installed suspicious browser plug-ins.
Optional method:
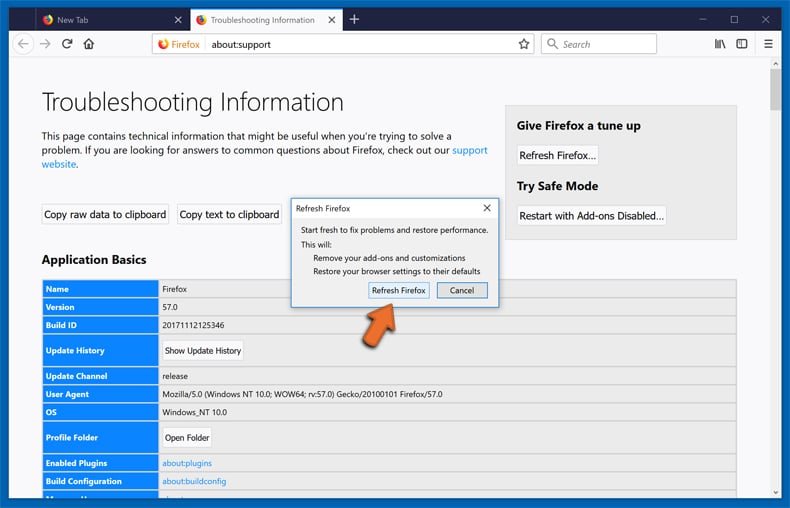
Computer users who have problems with fake cardano cryptocurrency giveaway removal can reset their Mozilla Firefox settings.
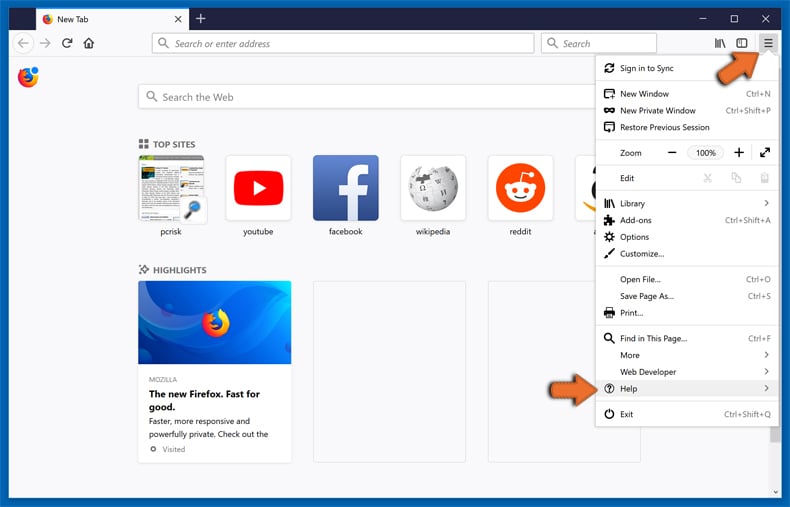
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
Select Troubleshooting Information.
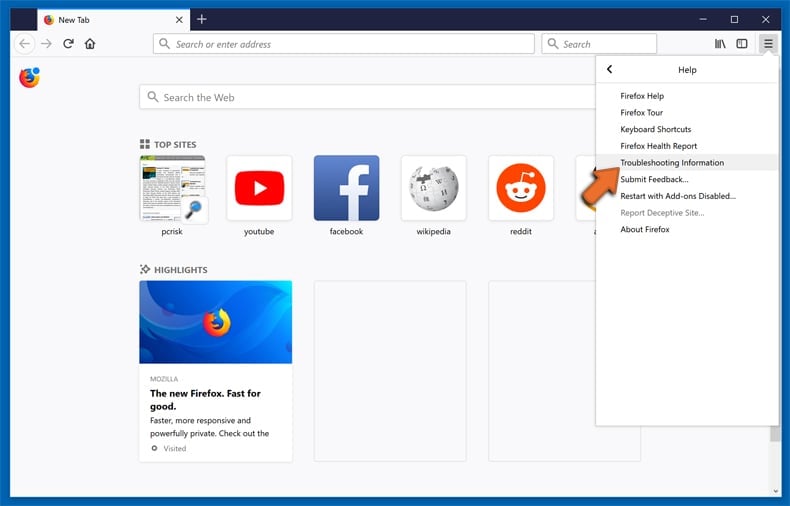
In the opened window, click the Refresh Firefox button.
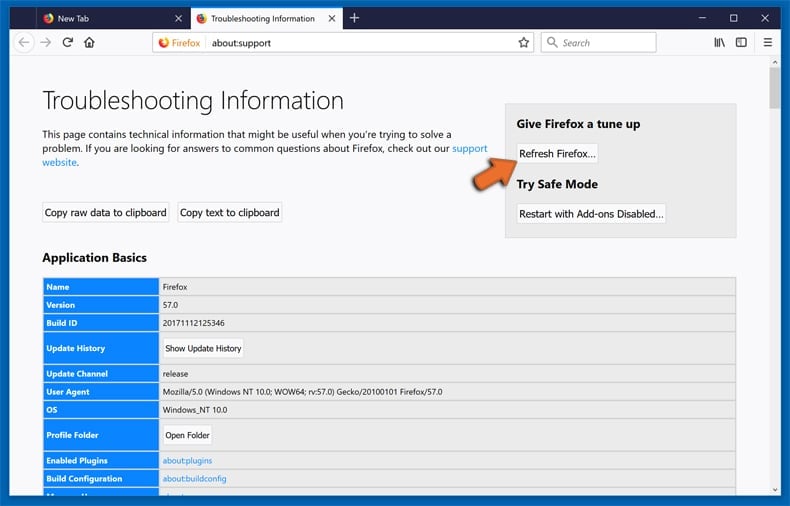
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
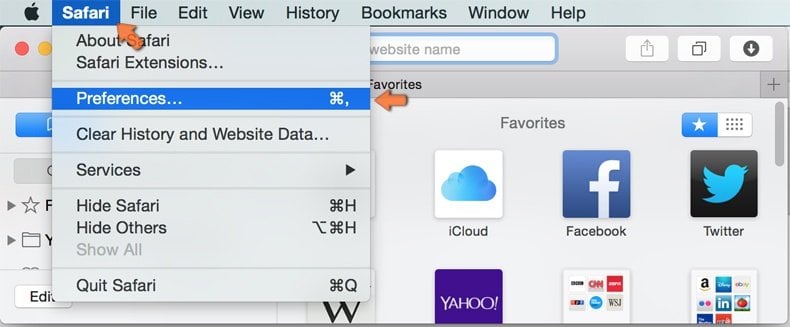
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
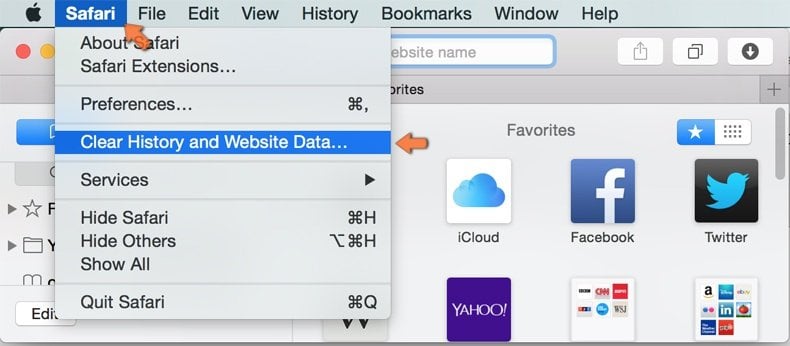
In the opened window select all history and click the Clear History button.

 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
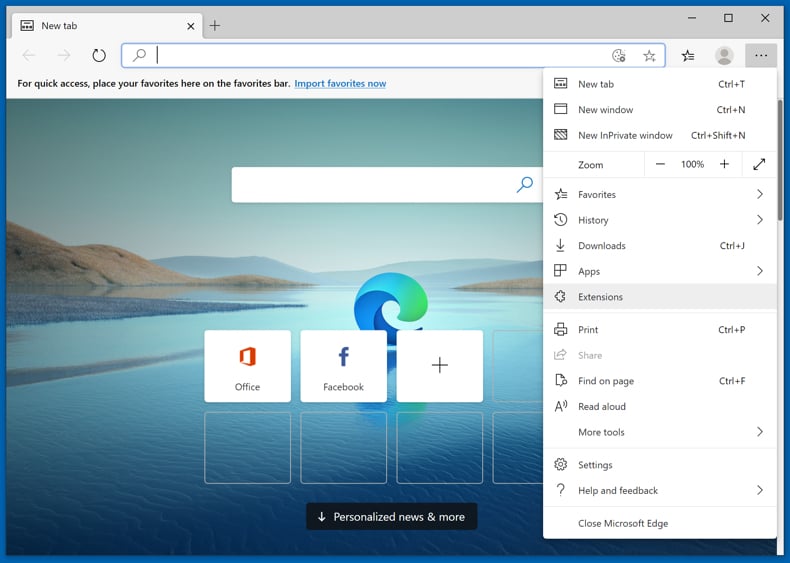
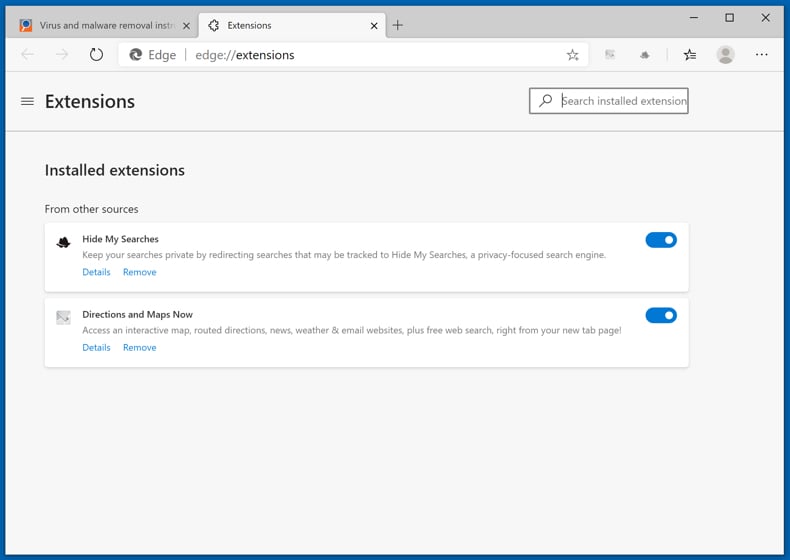
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
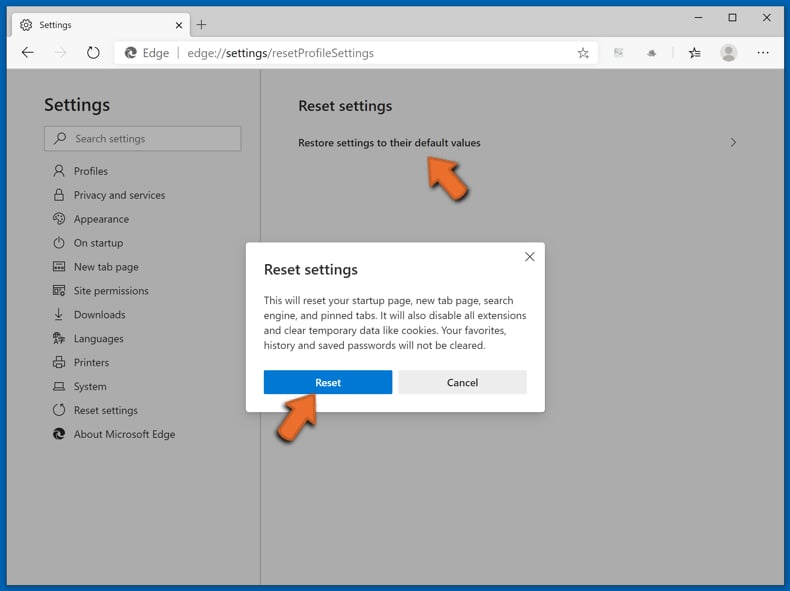
Optional method:
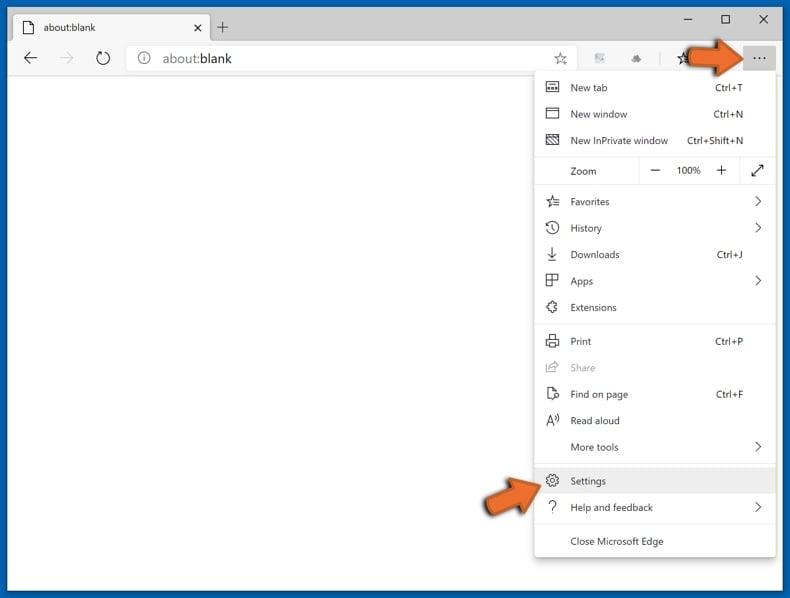
If you continue to have problems with removal of the fake cardano cryptocurrency giveaway, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
In the opened settings menu select Reset settings.
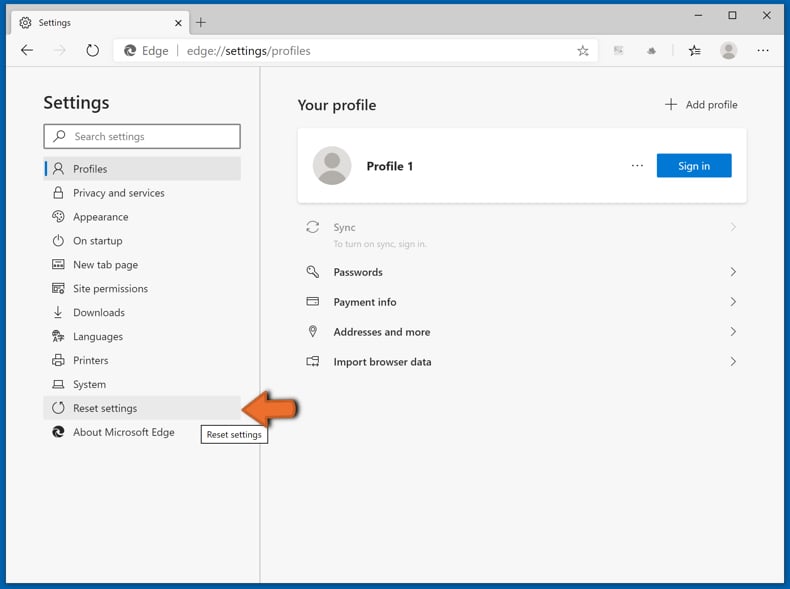
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
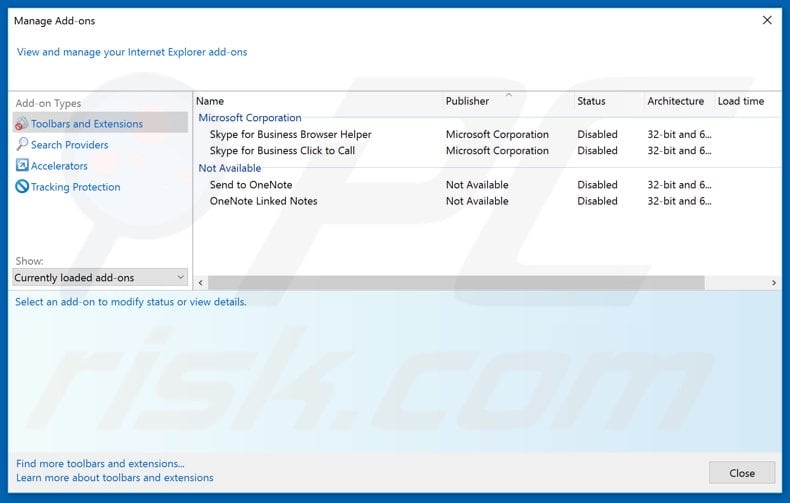
 Remove malicious add-ons from Internet Explorer:
Remove malicious add-ons from Internet Explorer:
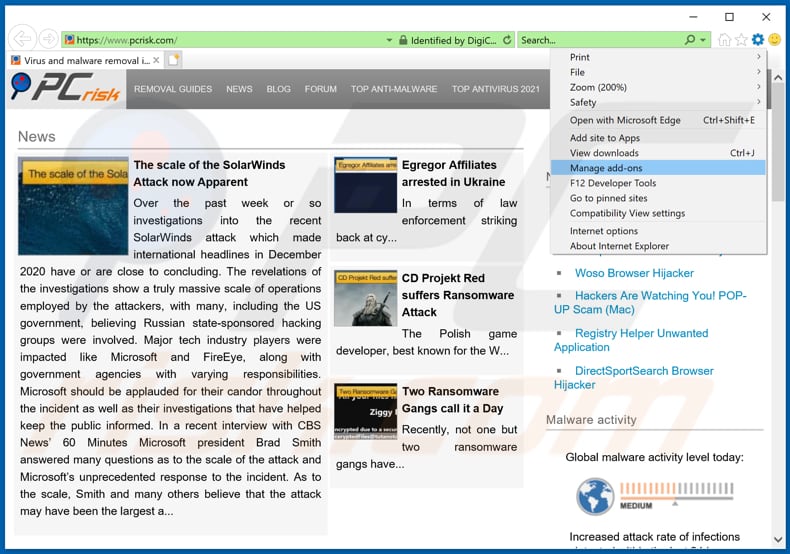
Click the "gear" icon ![]() (at the top right corner of Internet Explorer), select "Manage Add-ons". Look for any recently-installed suspicious browser extensions, select these entries and click "Remove".
(at the top right corner of Internet Explorer), select "Manage Add-ons". Look for any recently-installed suspicious browser extensions, select these entries and click "Remove".
Optional method:
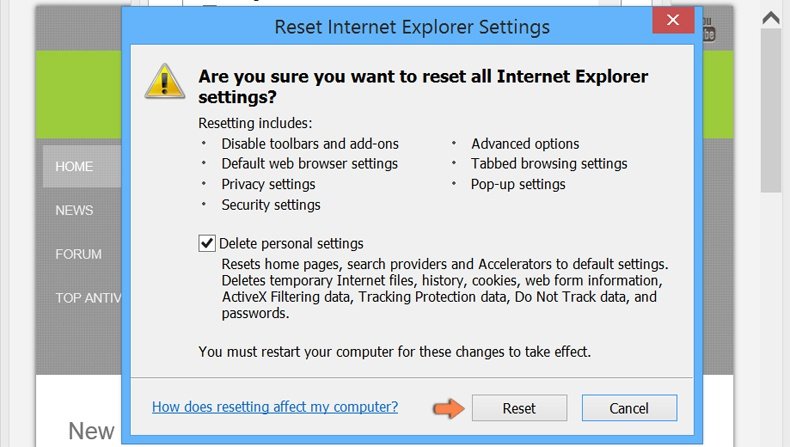
If you continue to have problems with removal of the fake cardano cryptocurrency giveaway, reset your Internet Explorer settings to default.
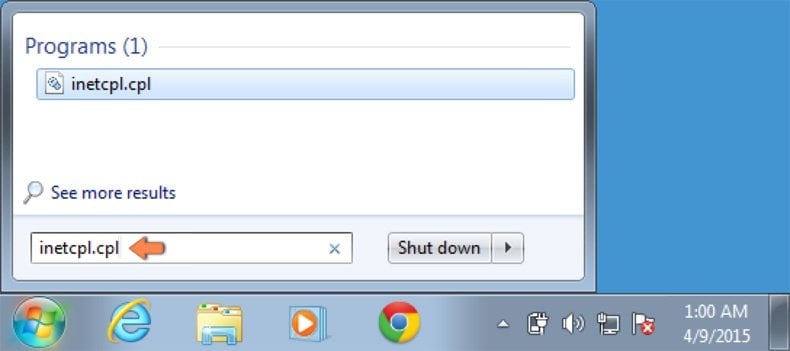
Windows XP users: Click Start, click Run, in the opened window type inetcpl.cpl In the opened window click the Advanced tab, then click Reset.
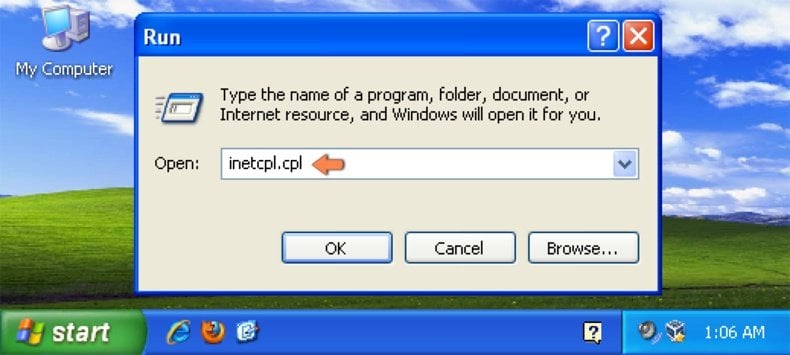
Windows Vista and Windows 7 users: Click the Windows logo, in the start search box type inetcpl.cpl and click enter. In the opened window click the Advanced tab, then click Reset.
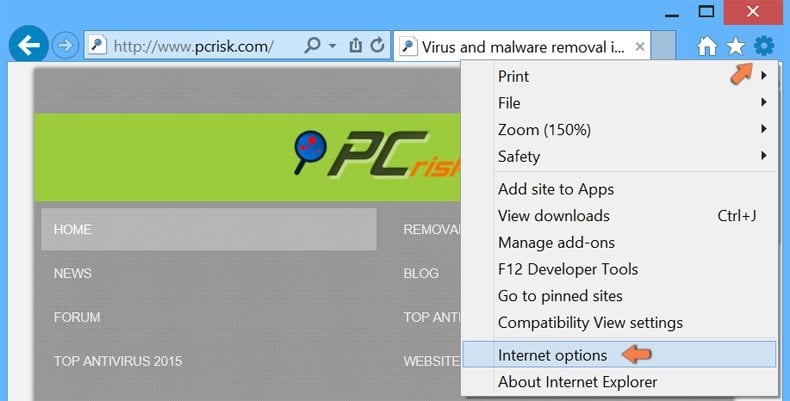
Windows 8 users: Open Internet Explorer and click the gear icon. Select Internet Options.
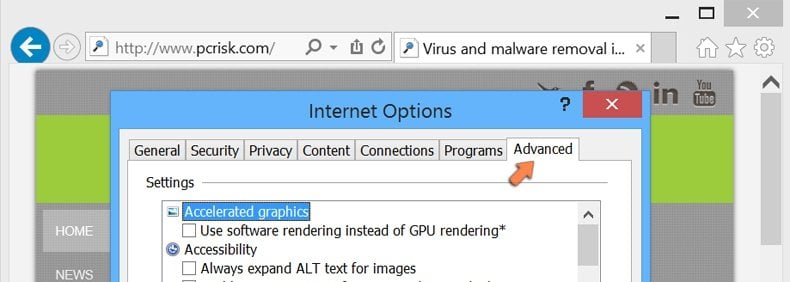
In the opened window, select the Advanced tab.
Click the Reset button.
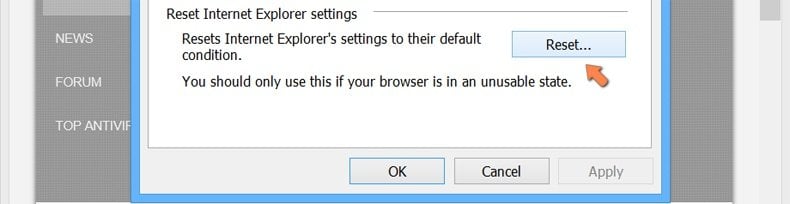
Confirm that you wish to reset Internet Explorer settings to default by clicking the Reset button.
Summary:
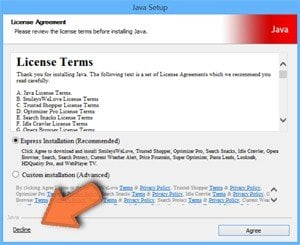 Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Post a comment:
If you have additional information on fake cardano cryptocurrency giveaway or it's removal please share your knowledge in the comments section below.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion