How to uninstall Unicom unwanted program from computers
AdwareAlso Known As: Unicom malicious application
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of program is Unicom?
Our analysis determined that Unicom is a malicious application (unrelated to UNICOM Global) disseminated through a malicious installer hosted on an unreliable webpage. The specific intent of Unicom remains unclear. It is important to highlight that the installer responsible for distributing Unicom includes additional undesirable components.
Unicom in detail
Unicom, with its dubious nature, could potentially harvest a broad spectrum of sensitive information from unsuspecting users. This may include personally identifiable information (PII) such as names, addresses, and contact details, as well as login credentials for various online accounts.
Additionally, Unicom might seek to collect browsing habits, location data, and device information, allowing for a comprehensive profile of users that could be exploited for malicious purposes. It is also common for shady apps like Unicom to function as cryptocurrency miners.
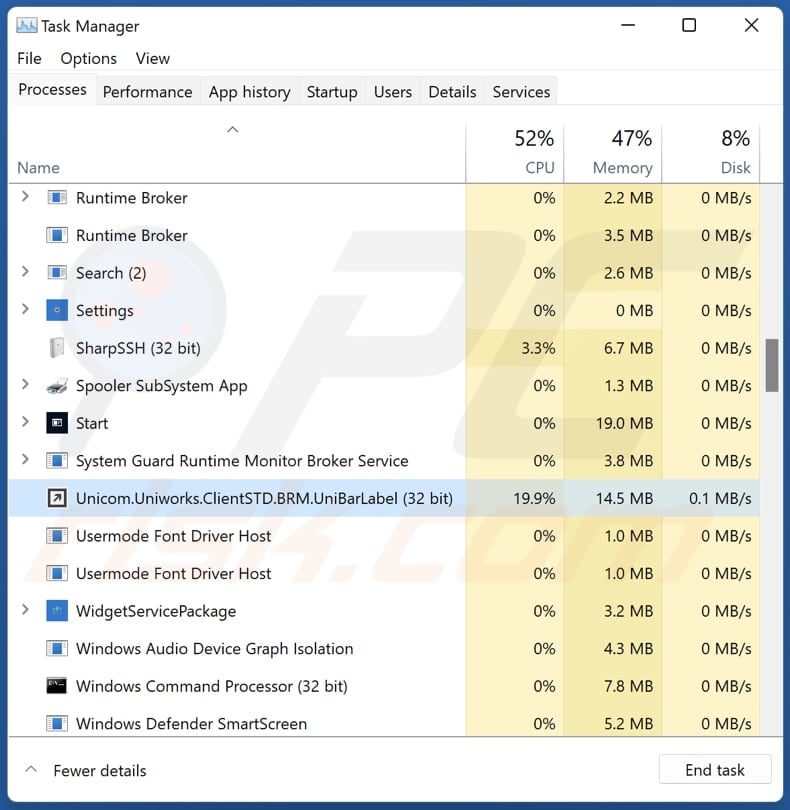
Once installed on a user's device, Unicom may initiate resource-intensive processes in the background, using the device's CPU or GPU power to mine cryptocurrencies like Bitcoin, Ethereum, or others. Users may experience increased energy consumption, slowed device performance, system crashes, and other issues.
Another concern surrounding Unicom is the presence of unwanted components within the installer responsible for delivering the application. It is possible that Unicom is distributed alongside browser hijackers, adware, and other unwanted software that changes the settings of web browsers, displays ads, or causes other issues.
| Name | Unicom malicious application |
| Threat Type | Malicious Application, Unwanted Application |
| Detection Names (Installer) | N/A (VirusTotal) |
| Detection Names (Application) | Avast (Win32:Malware-gen), Combo Cleaner (Trojan.GenericKD.70997595), ESET-NOD32 (A Variant Of Win32/Packed.VMProtect.BC Suspicious), Kaspersky (Trojan.Win32.Nymaim.ccda), Full List (VirusTotal) |
| Symptoms | Your computer becomes slower than normal, you see unwanted pop-up ads, you are redirected to dubious websites. |
| Distribution methods | Shady website, malicious installer |
| Damage | Internet browser tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites, loss of private information, and possibly other issues. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
The application's clandestine nature, coupled with the inclusion of more unwanted components within its installer and the possibility of data harvesting or cryptocurrency mining, underscores the evolving challenges in the digital landscape. Users are urged to exercise heightened caution, adopting proactive cybersecurity measures to mitigate the risks associated with such harmful applications.
How did unwanted software install on my computer?
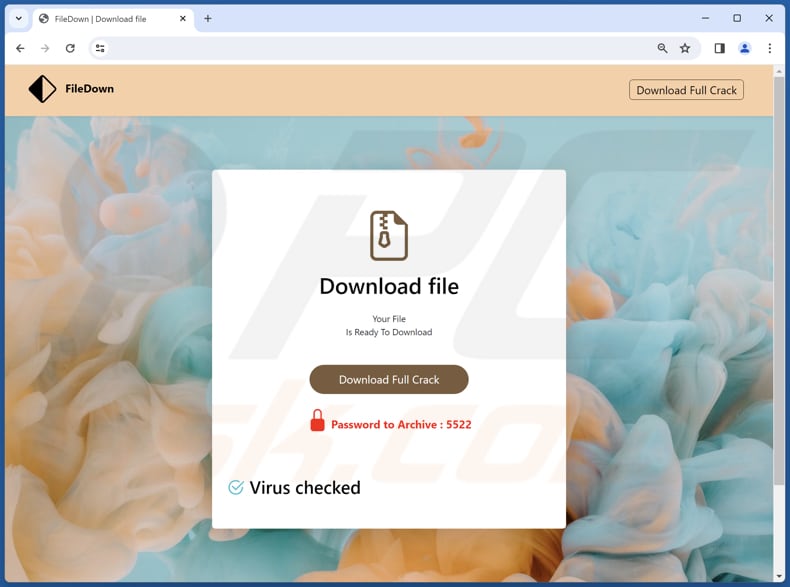
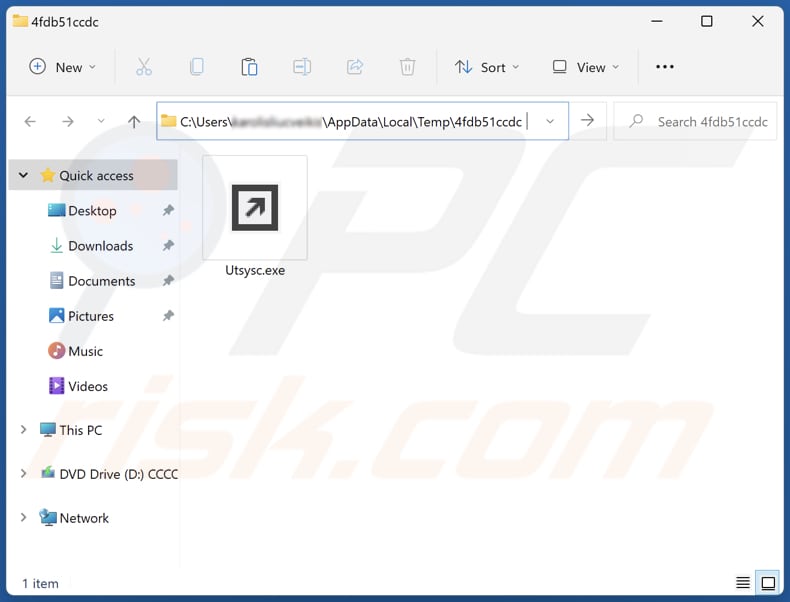
Unicom is distributed via a shady installer hosted on a page offering suspicious content. The app infiltrates the system along with other unwanted elements after completing the installation.
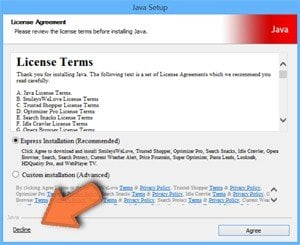
Also, developers bundle unwanted apps with free (often dubious) software products. Users who hastily click through installation prompts without carefully reviewing them may unintentionally agree to the installation of additional software.
Some websites employ misleading tactics, such as fake system alerts or pop-up ads that claim the user's computer is infected and encourage them to download a supposed security (or other) tool. Unwary users who fall for these tricks may install unwanted apps instead of other software. Additionally, malicious ads or compromised websites may trigger automatic downloads of rogue apps.
How to avoid installation of unwanted applications?
Exercise caution when downloading and installing software. Download apps from legitimate sources such as official pages and app stores and review each installation step. Opt for custom or advanced installation settings whenever possible and deselect any bundled software or additional components.
Avoid clicking on suspicious ads and be wary of pop-up alerts and similar content on shady pages. Implementing and regularly updating reliable antivirus and anti-malware software is also recommended. If your computer is already infected with rogue applications, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Website hosting the installer containing Unicom:
Installation folder of Unicom malware:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Unicom?
- STEP 1. Uninstall unwanted applications using Control Panel.
- STEP 2. Remove rogue plug-ins from Google Chrome.
- STEP 3. Remove shady extensions from Mozilla Firefox.
- STEP 4. Remove malicious extensions from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
Unwanted software removal:
Windows 11 users:
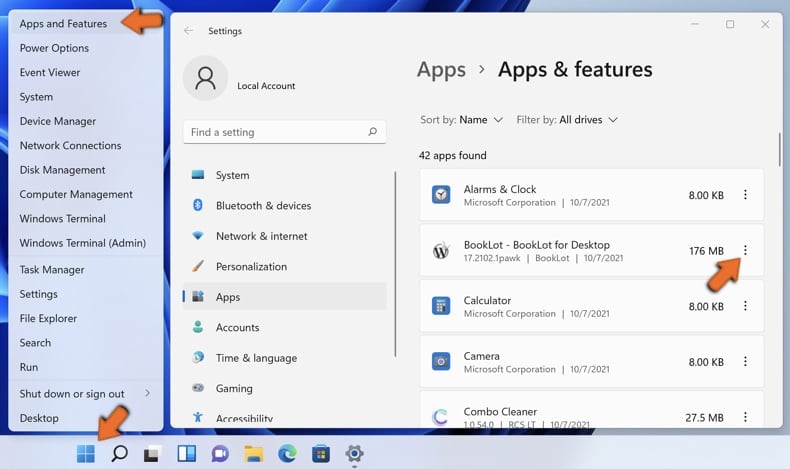
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
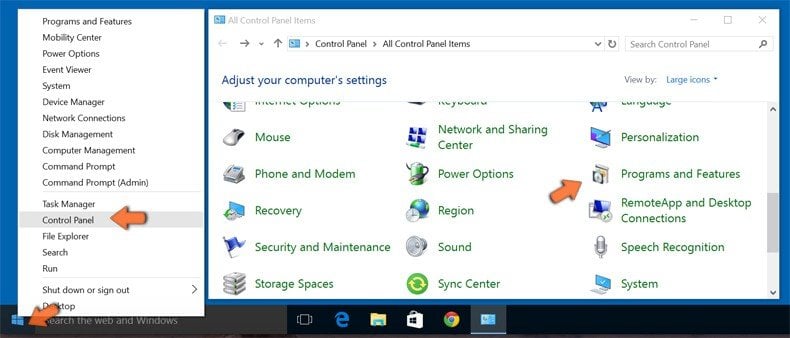
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.
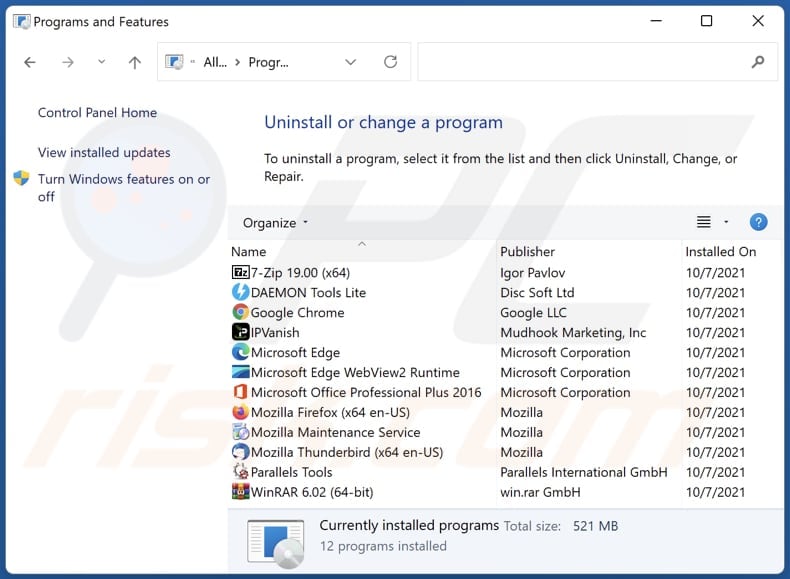
In the uninstall programs window, look for any unwanted applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the unwanted application, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove unwanted apps from Internet browsers:
Video showing how to remove unwanted browser add-ons:
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
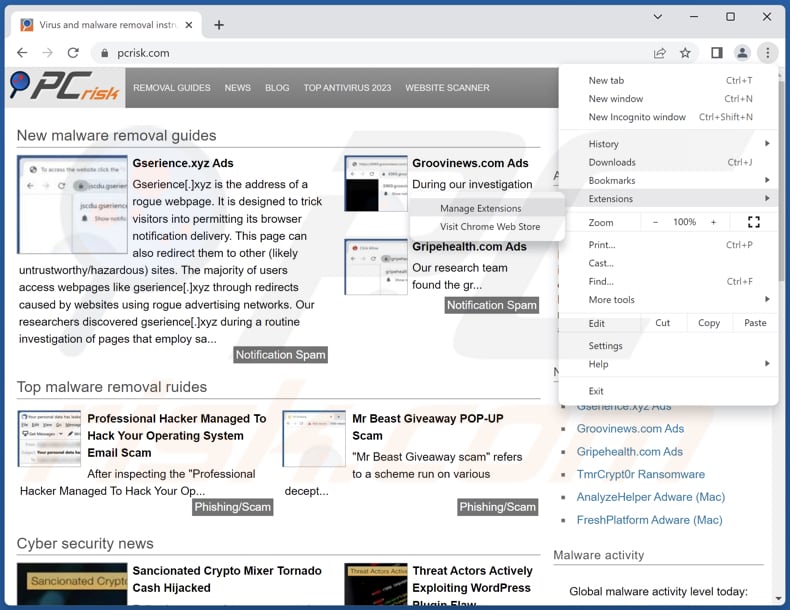
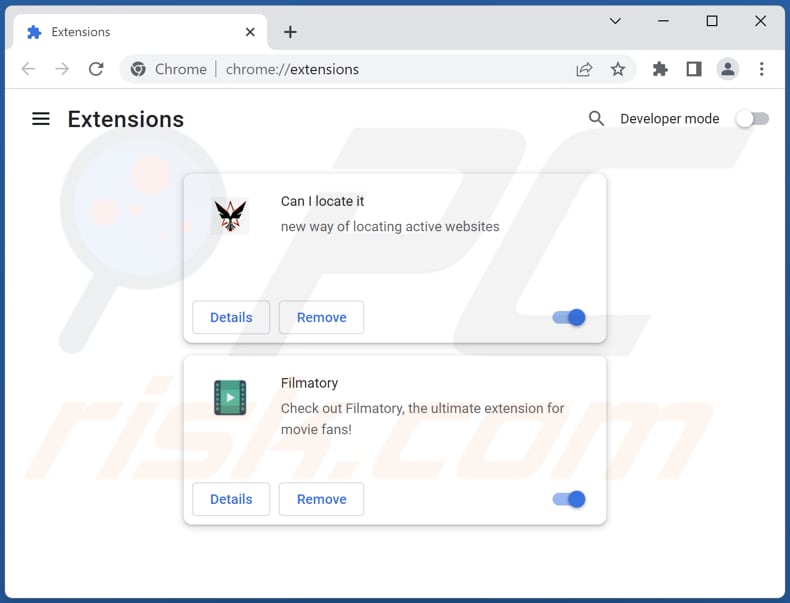
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
Optional method:
If you continue to have problems with removal of the unicom malicious application, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
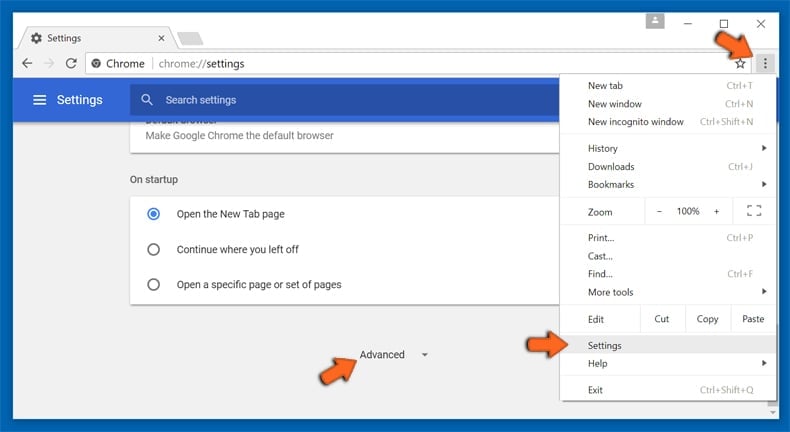
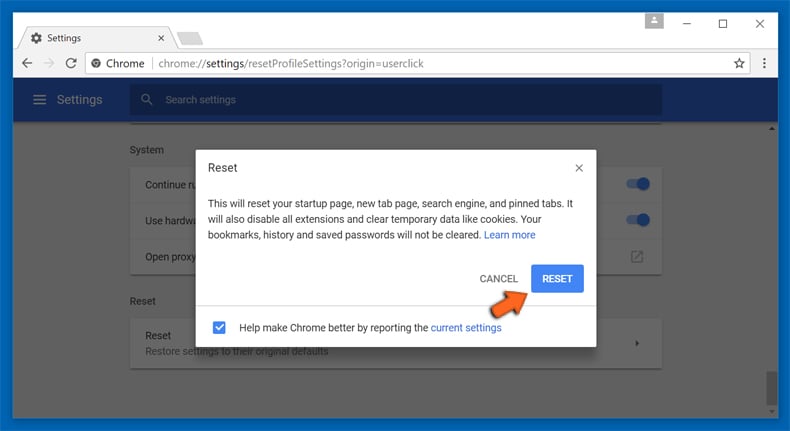
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
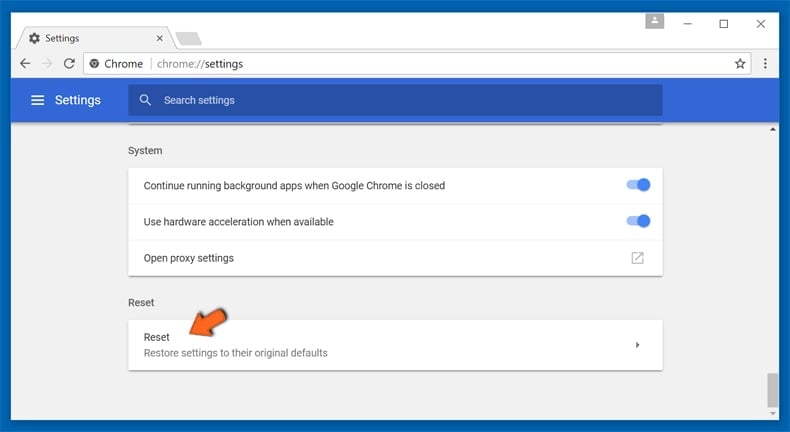
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious plug-ins from Mozilla Firefox:
Remove malicious plug-ins from Mozilla Firefox:
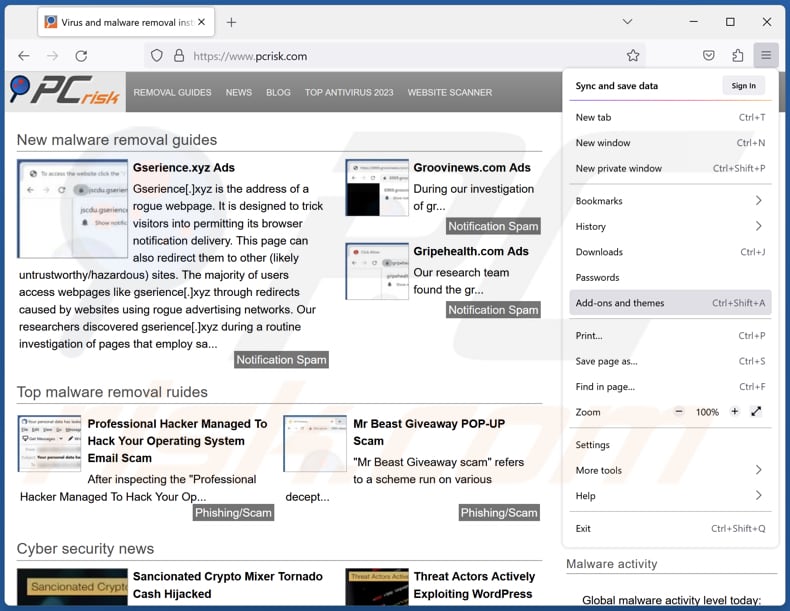
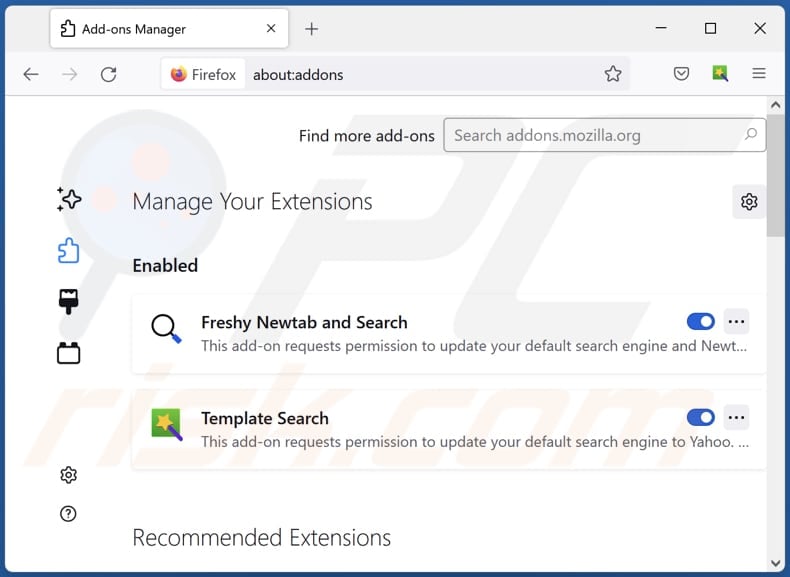
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
Optional method:
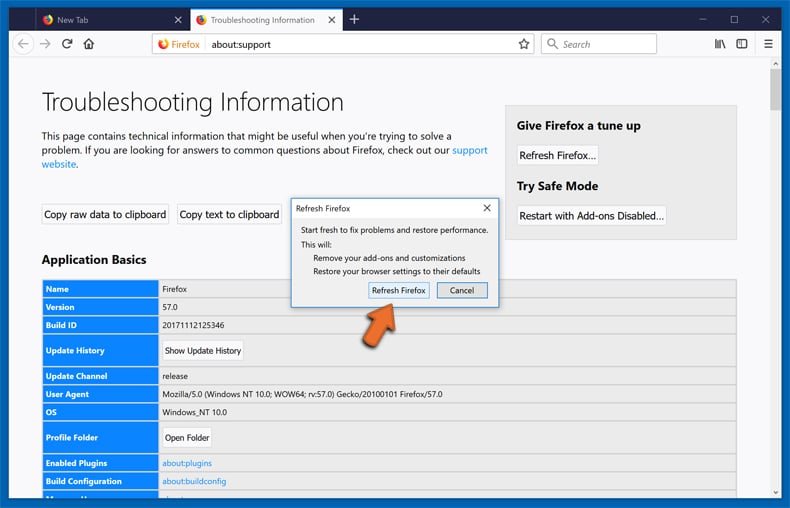
Computer users who have problems with unicom malicious application removal can reset their Mozilla Firefox settings.
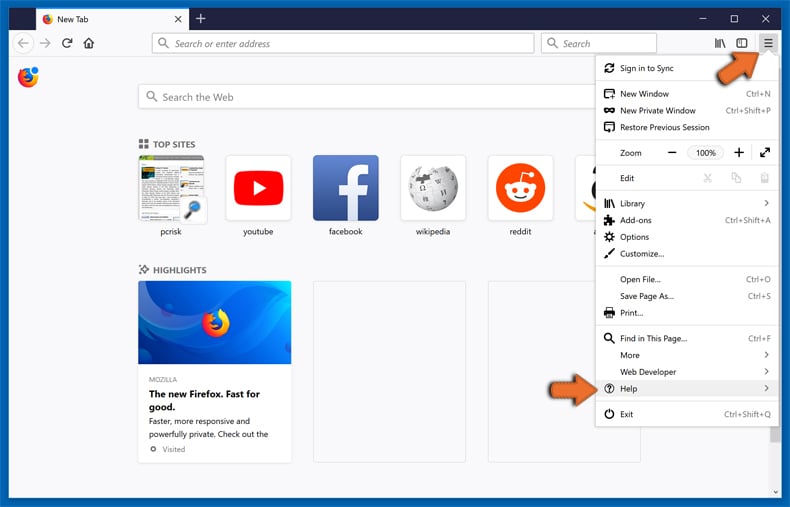
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
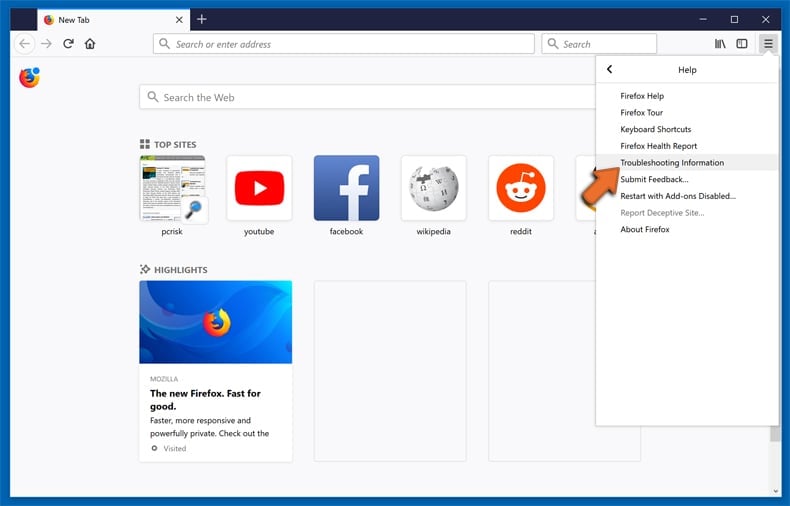
Select Troubleshooting Information.
In the opened window, click the Refresh Firefox button.
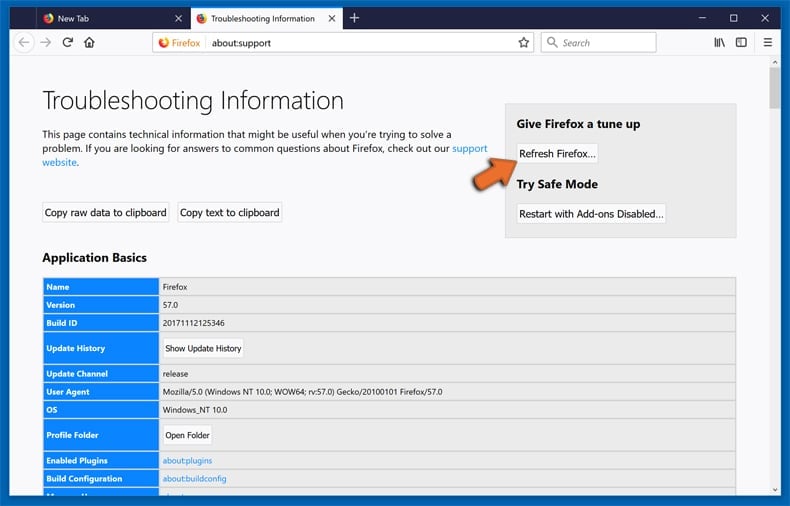
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
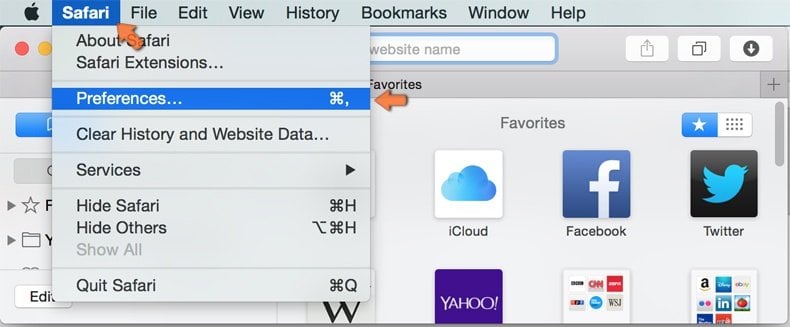
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
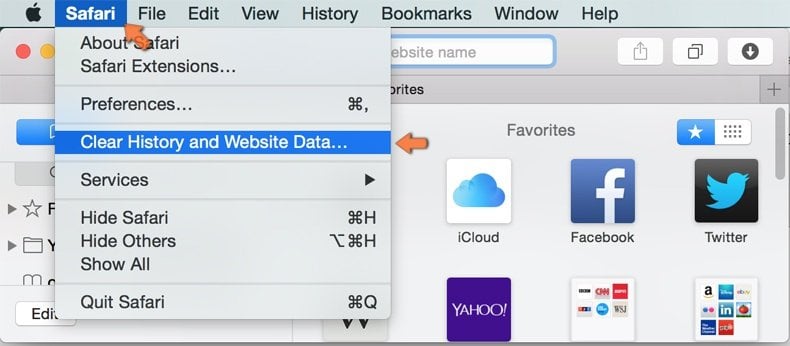
In the opened window select all history and click the Clear History button.

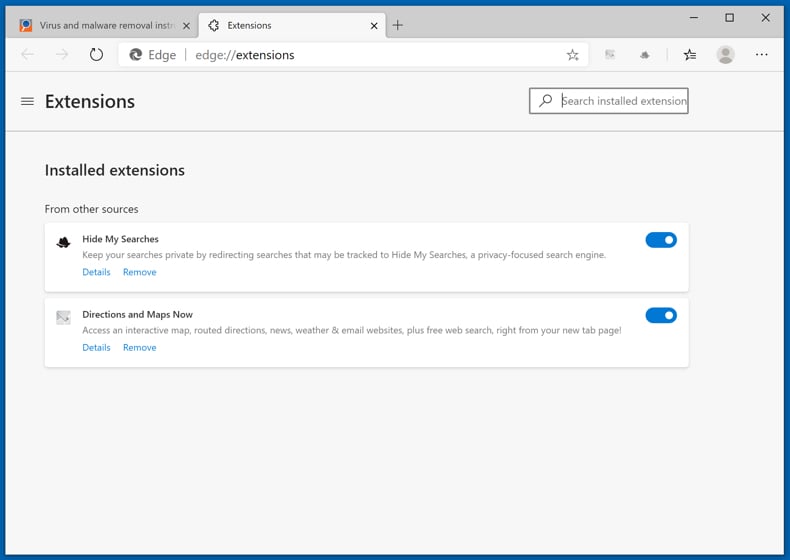
 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
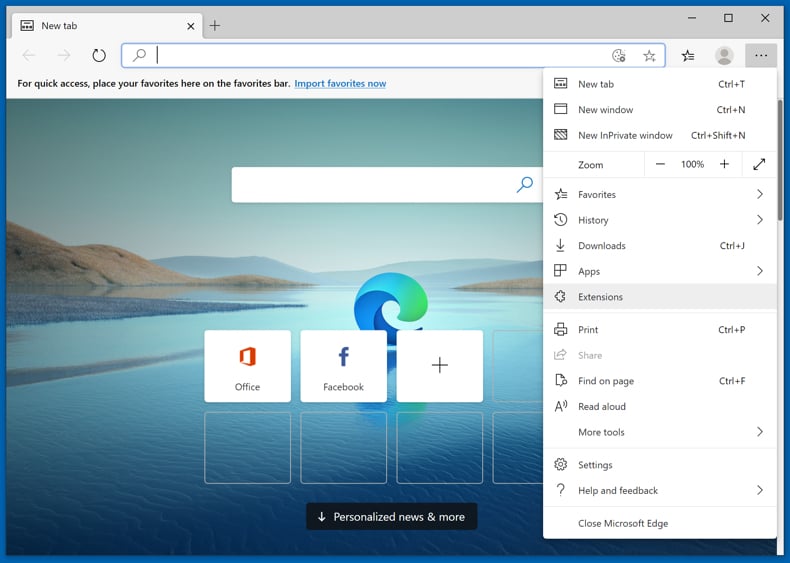
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
Optional method:
If you continue to have problems with removal of the unicom malicious application, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
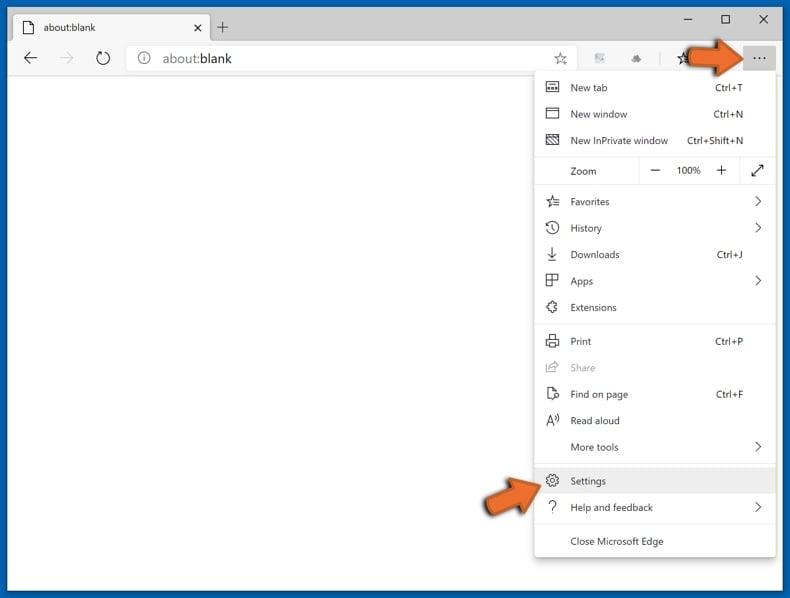
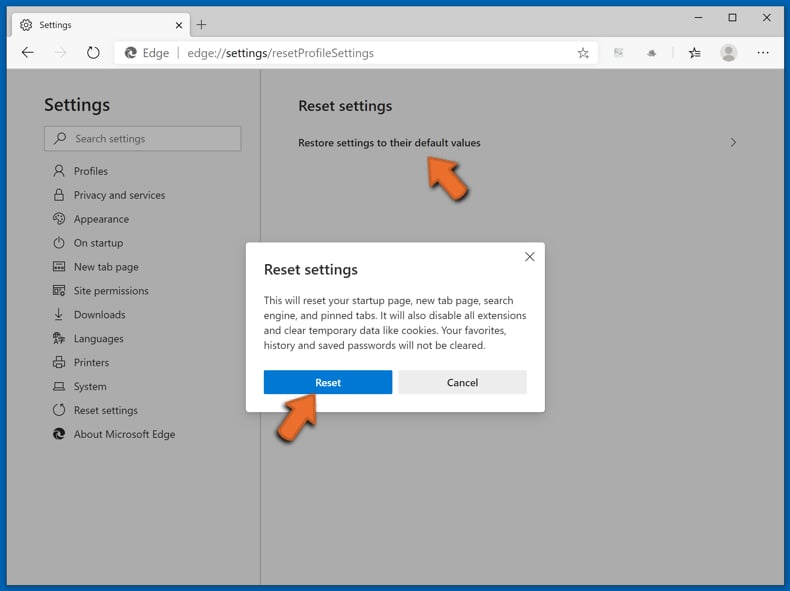
In the opened settings menu select Reset settings.
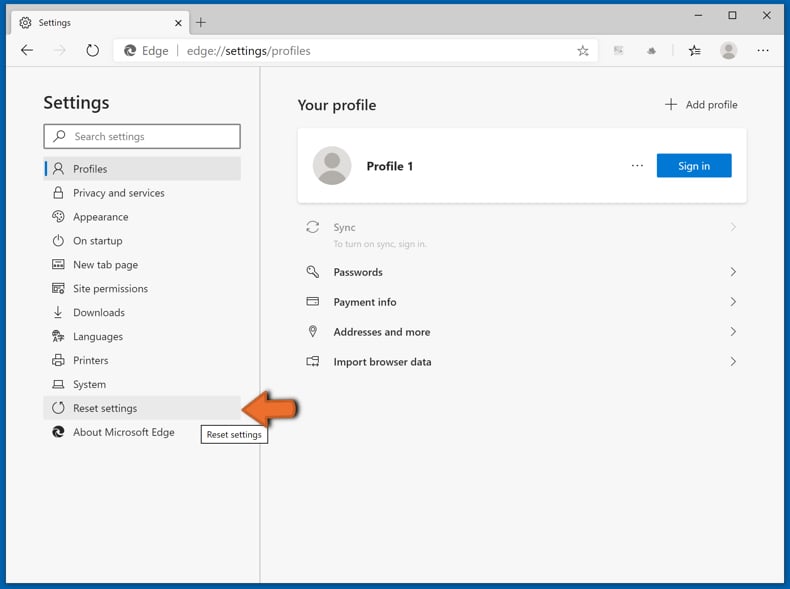
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
 Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Post a comment:
If you have additional information on unicom malicious application or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
What is the purpose of an unwanted application?
The purpose of an unwanted application, often malicious or unreliable, can vary, but common goals include unauthorized data harvesting, compromising user privacy, engaging in fraudulent activities, or exploiting the computational resources of devices for tasks such as cryptocurrency mining.
Is an unwanted application legal?
Unwanted applications are generally deemed legal because their End User License Agreements (EULA) usually inform users about their potential behaviors.
Is having Unicom installed on my computer dangerous?
If you have Unicom installed on your computer, there is a potential risk of unauthorized data harvesting, privacy infringements, or even cryptocurrency mining. Additionally, the inclusion of unwanted components and the application's elusive nature could pose security threats.
Will Combo Cleaner help me remove Unicom unwanted application?
Combo Cleaner will conduct an in-depth scan of your computer to identify and eliminate any rogue applications that may be installed. Using dedicated software is advised for removing unwanted apps, as manual removal may not be effective.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion