How to remove searchtosearch.com and associated programs
Browser HijackerAlso Known As: searchtosearch.com browser hijacker
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of website is searchtosearch.com?
During the examination of deceptive websites, our investigators discovered an installation package harboring a questionable application that forces users to visit searchtosearch.com, and address operating as a component within a redirection chain.
Ordinarily, browser-hijacking programs promote such sites by adjusting browser settings. Although, the aforementioned app refrained from making any modifications to the browser on our test system. Additionally, it employed a persistence mechanism to hinder its removal process.
Searchtosearch.com overview
While the undesired application promoting searchtosearch.com is present on the operating system, inputting search queries into the URL bar directs users to visit searchtosearch.com. As previously highlighted, searchtosearch.com plays a role in a redirection chain.
In the course of our investigation, entering search queries through a compromised browser led to redirections from searches-world.com to searchtosearch.com, ultimately leading to bing.com (a legitimate search engine owned by Microsoft). It is essential to note that searchtosearch.com might feature in other redirect chains.
As stated earlier, the browser hijacker responsible for promoting searchtosearch.com employs a technique to ensure persistence, hindering users from restoring their browsers.
The redirections are managed through processes named "IdealWeightOptimizer" and "IdealWeightService". However, removing them proves challenging. The hijacker utilizes a legitimate Windows tool from Microsoft's Deployment ToolKit, known as "ServiceUI", to ensure the reactivation of "IdealWeightOptimizer" and "IdealWeightService" after their processes are terminated via Task Manager and system restarts.
Hence, a particular sequence is required for eliminating the browser hijacker that promotes searchtosearch.com. You can find the removal steps outlined below.
| Name | searchtosearch.com |
| Threat Type | Browser Hijacker, Redirect, Search Hijacker, Toolbar, Unwanted New Tab |
| Detection Names (Installer) | N/A (VirusTotal) |
| Detection Names (searchtosearch.com) | N/A (VirusTotal) |
| Detection Names (IdealWeightService.exe) | Arcabit (Trojan.Zusy.D82966), Combo Cleaner (Gen:Variant.Zusy.534886), Emsisoft (Gen:Variant.Zusy.534886 (B)), MAX (Malware (ai Score=83)), Symantec (Trojan.Gen.MBT), Full List Of Detections (VirusTotal) |
| Detection Names (IdealWeightOperator.exe) | ALYac (Gen:Variant.Zusy.534884), Combo Cleaner (Gen:Variant.Zusy.534884), Cylance (Unsafe), Fortinet (PossibleThreat), VIPRE (Gen:Variant.Zusy.534884), Full List Of Detections (VirusTotal) |
| Promoted URL | searchtosearch.com |
| Affected Browser Settings | Homepage, new tab URL, default search engine |
| Symptoms | Users are forced to visit the hijacker's website and search the Internet using their search engines. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling). |
| Damage | Internet browser tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Browser hijackers in general
Browser hijackers are unwanted apps designed to alter the settings of a web browser without the user's knowledge, often redirecting their searches and homepage to a predetermined website. Once infiltrated, browser hijackers may manipulate search results, inject unwanted advertisements, and track users' online activities.
They not only compromise the user's online privacy but also degrade the overall browsing experience. Removal of browser hijackers often requires specialized anti-malware tools or manual intervention to restore the browser settings to their original state.
Users are advised to be careful when downloading software to minimize the risk of encountering such threats.
Examples of browser-hijacking apps are Mycool Search, Your Search Bar, and Extreme New Tab.
How did searchtosearch.com promoting software install on my computer?
Users may find their browsers hijacked through various means, often unwittingly downloading malicious software or browser extensions. One common method involves users unintentionally installing bundled software that includes browser hijackers.
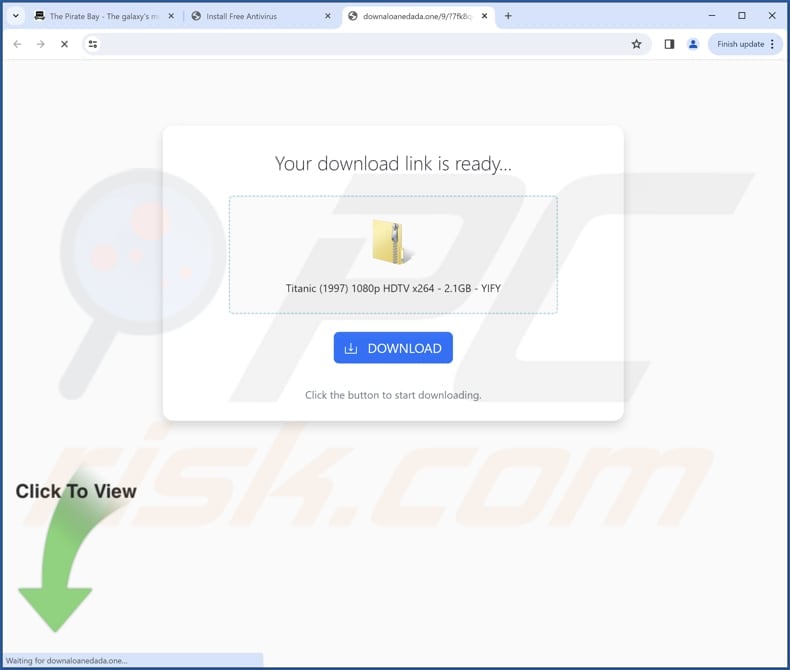
These may come from seemingly legitimate sources, such as free software downloads or file-sharing platforms, where the additional unwanted software is included in the installation package. Additionally, users can be tricked into downloading browser hijackers through deceptive email attachments, misleading advertisements, or compromised websites.
How to avoid installation of browser hijackers?
To avoid browser hijackers, users should exercise caution when downloading software, opting for reputable sources, and avoid dubious websites or third-party app providers. It is essential to carefully read installation prompts and uncheck any boxes or change settings (like "Advanced" or "Custom") that indicate additional software installations.
Additionally, users should keep their browsers and security software up to date, avoid clicking dubious ads and pop-ups while browsing the web, and employ reliable antivirus and anti-malware tools. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate this browser hijacker.
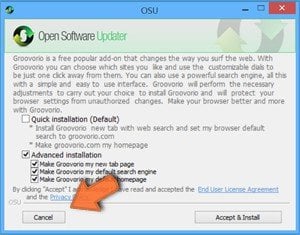
Screenshot of deceptive website promoting an installer containing this browser hijacker:
Removal steps for this browser hijacker:
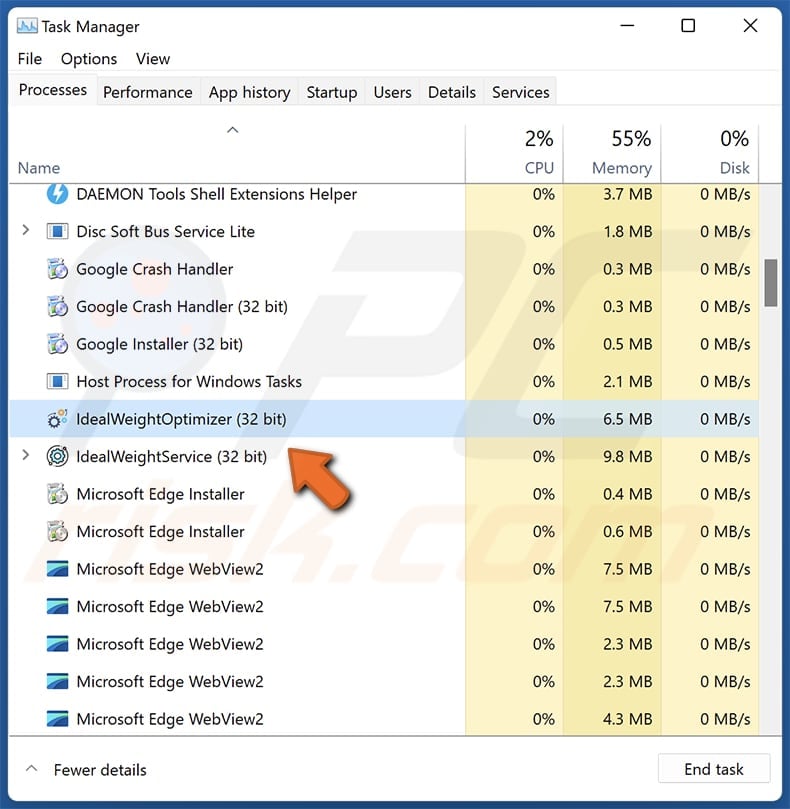
Open Windows Task Manager, locate the "IdealWeightOptimizer" and "IdealWeightService" processes, and terminate them by clicking "End task".
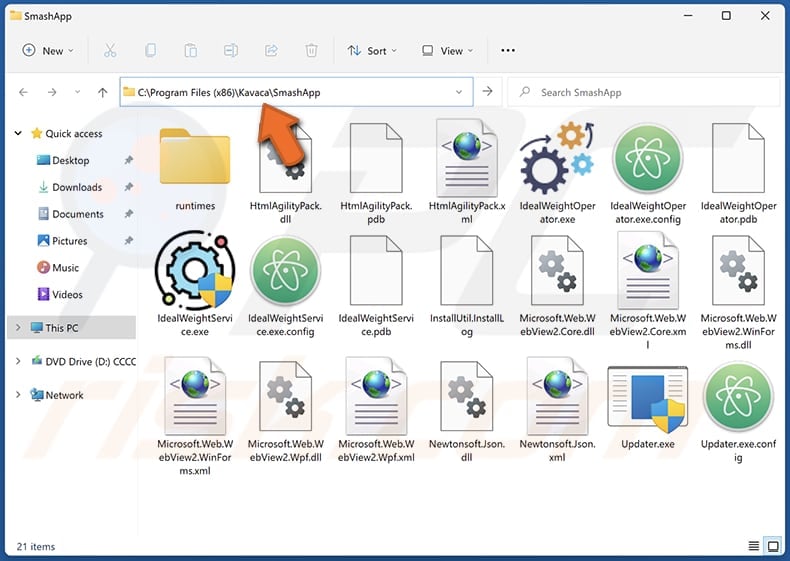
Open the "SmashApp" folder (C:\Program Files (x86)\Kavaca\SmashApp), and delete its contents.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
Summary:
 A browser hijacker is a type of adware infection that modifies Internet browser settings by assigning the homepage and default Internet search engine settings to some other (unwanted) website URL. Commonly, this type of adware infiltrates operating systems through free software downloads. If your download is managed by a download client, ensure that you decline offers to install advertised toolbars or applications that seek to change your homepage and default Internet search engine settings.
A browser hijacker is a type of adware infection that modifies Internet browser settings by assigning the homepage and default Internet search engine settings to some other (unwanted) website URL. Commonly, this type of adware infiltrates operating systems through free software downloads. If your download is managed by a download client, ensure that you decline offers to install advertised toolbars or applications that seek to change your homepage and default Internet search engine settings.
Post a comment:
If you have additional information on searchtosearch.com browser hijacker or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
What is the purpose of forcing users to visit searchtosearch.com website?
It is part of a browser hijacking scheme aimed at promoting a particular search engine. Additionally, the redirection to searchtosearch.com might be a step in a larger strategy to expose users to deceptive advertising, phishing attempts, or other malicious content.
Is visiting searchtosearch.com a threat to my privacy?
Yes, visiting searchtosearch.com can pose a threat to your privacy, especially if it is associated with malicious activities such as unauthorized data collection or redirecting to deceptive websites.
How did a browser hijacker infiltrate my computer?
A browser hijacker may have infiltrated your computer through deceptive downloads, malicious ads, bundled software installations, malicious email attachments, or while visiting compromised websites.
Will Combo Cleaner help me remove browser hijackers?
Combo Cleaner conducts a comprehensive scan to remove unwanted applications from your computer. Relying solely on manual removal may not ensure complete eradication, as residual files could persist. Unlike manual methods, Combo Cleaner guarantees the absence of lingering traces of unwanted apps in the system.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion