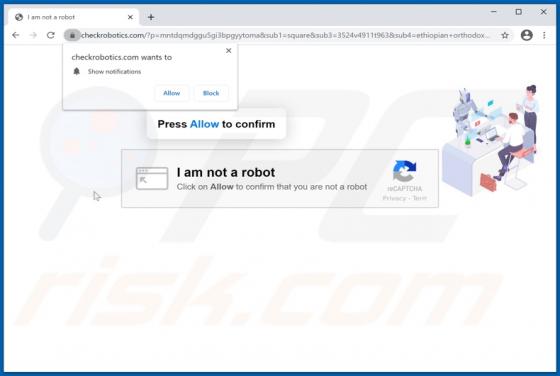
Checkrobotics.com Ads
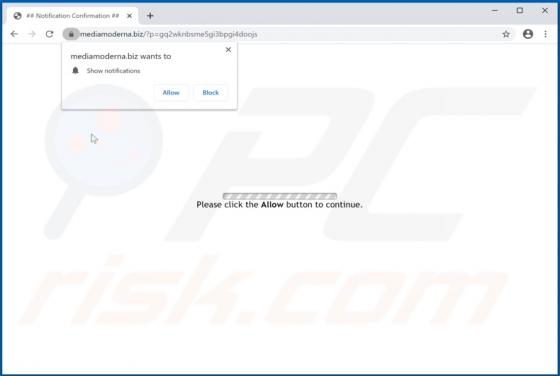
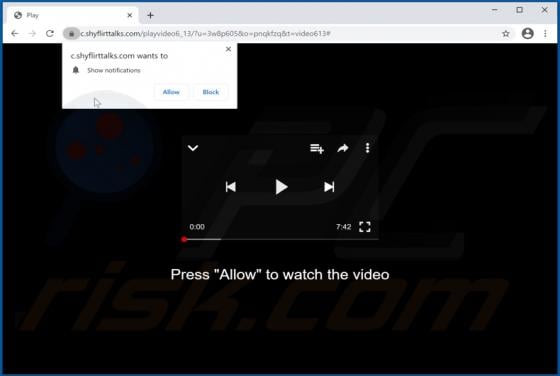
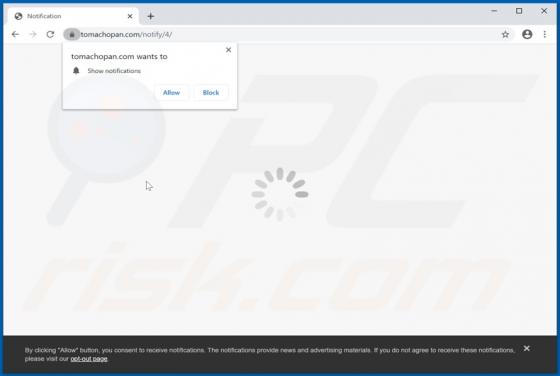
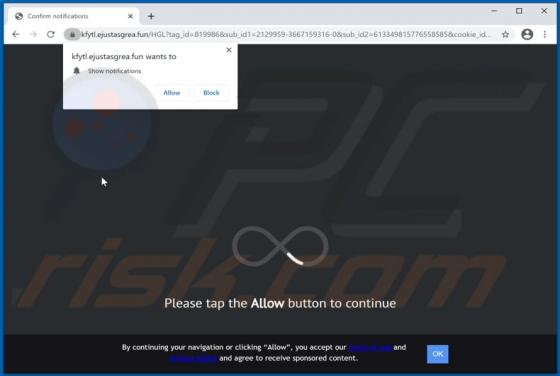
Sharing similarities with shyflirttalks.com, ejustasgrea.fun, saiwhute.com, sitioninindi.club, and many others, checkrobotics[.]com is a rogue website. Visitors to this page are presented with dubious material and/or redirected to untrustworthy or possibly malicious sites. Users seldom enter webp