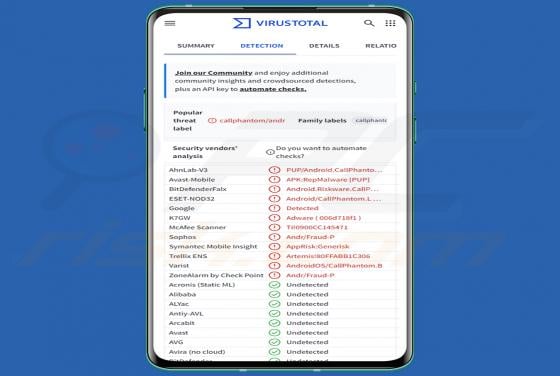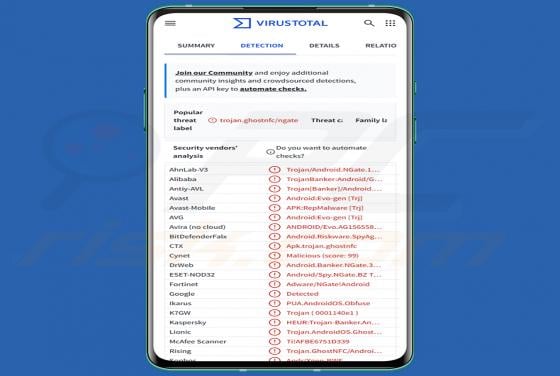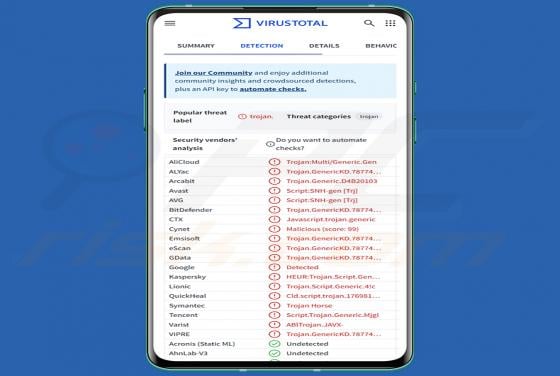
Mirax RAT (Android)
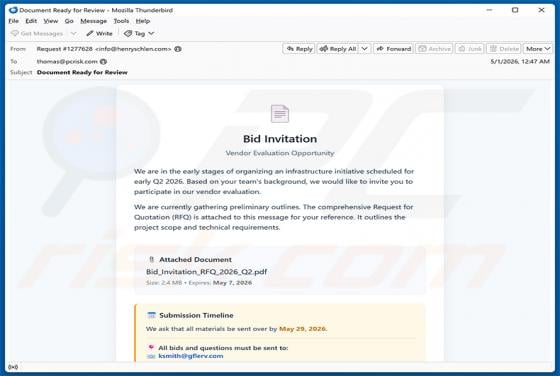
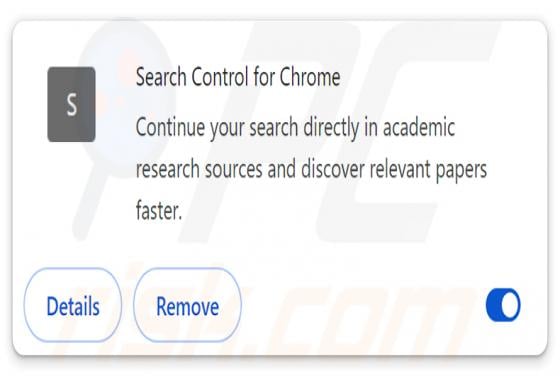
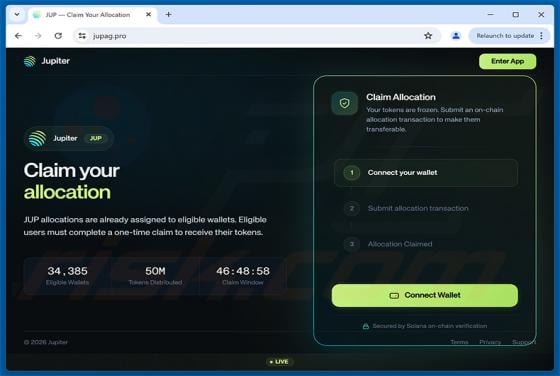
Mirax RAT is a Remote Access Trojan targeting Android devices. First analyzed by the Cleafy Threat Intelligence Team in March 2026, it primarily focuses on Spanish-speaking users and is designed to spy on victims, steal sensitive data, and silently route internet traffic through infected phones.