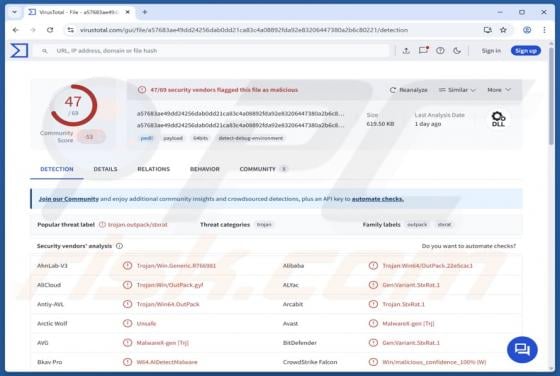
Net Ransomware
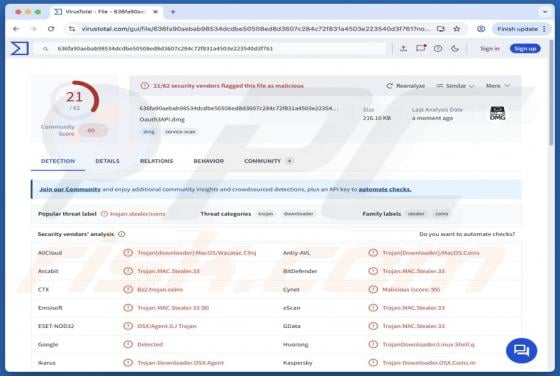
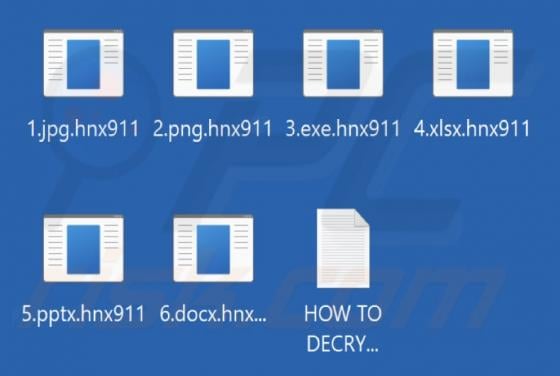
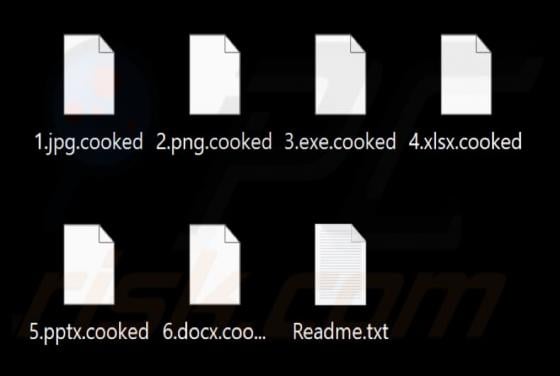
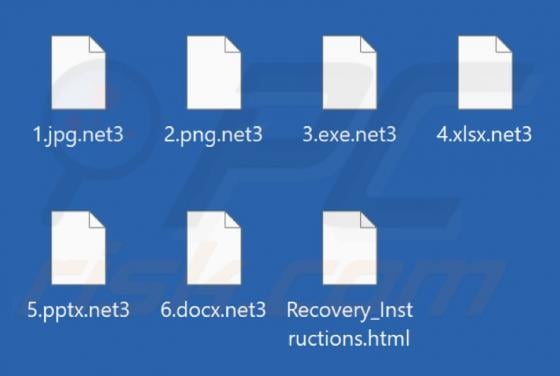
Net is ransomware that we uncovered while examining malware samples submitted to VirusTotal. After execution, Net makes files inaccessible by encrypting them. Also, the ransomware appends the ".net6" extension to files (the number in it may vary) and provides a ransom note ("Recovery_Instructions.