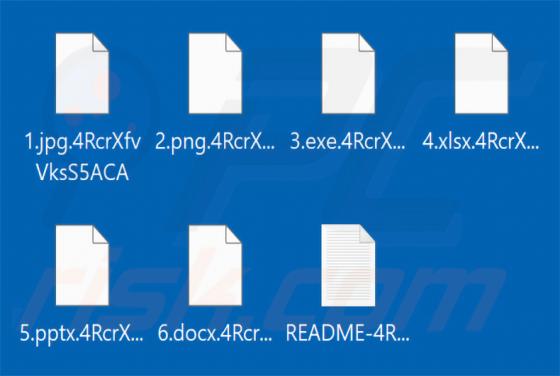
MORTAR Ransomware
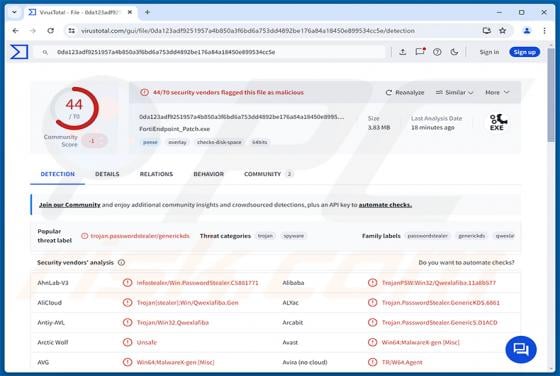
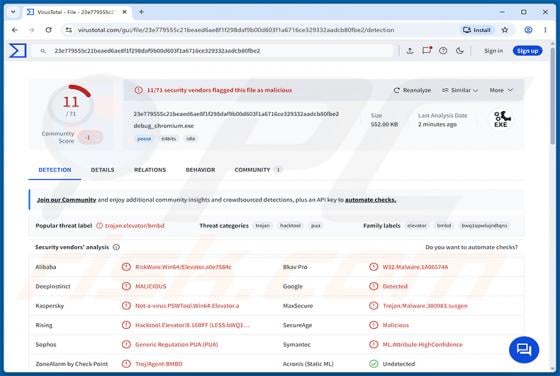
MORTAR is ransomware we discovered during a routine inspection of new submissions to the VirusTotal website. It targets corporate networks, encrypts files, and drops a ransom note named README-[victim's ID].txt. On our test machine, MORTAR appended a unique victim ID as the extension to each encr