How to spot scams like the "Final Warning" sextortion scam
Phishing/ScamAlso Known As: Final Warning spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of email is "Final Warning"?
Criminals behind this spam campaign, which is classified as a sextortion scam, send emails to many people and hope that some will be tricked. Typically, scammers who send emails of this attempt to blackmail recipients with threats to send compromising, humiliating images or videos to their contacts. We strongly recommend that you do not trust this or other, similar email scams.
More about the "Final Warning" sextortion scam email
The scammer behind this sextortion scam claims that this is the last warning given and that a compromising video (and some other details) will be posted to an online forum unless 0.2 Bitcoin is paid within two days. The scammer also claims that a video will be sent to all people on the recipient's contacts list.
Recipients supposedly make payment using the provided QR code. Typically, scammers send sextortion and other email scams to many people. They often claim that the computer was infected with some malicious software (e.g., a Remote Access Trojan), which gave them access to the victim's webcam, microphone or even allowed them to take full control of the system.
| Name | Final Warning Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Cyber criminals behind this sextortion scam claim that they have recorded a compromising video of the recipient and threaten to distribute it. |
| Size of Ransom | 0.2 Bitcoin, $5000 (depending on scam's variant) |
| Cyber Criminals' Cryptowallet |
bc1q5gmynanvma3svnhggjecypfupr9xgf4wsfjqvy, bc1q9q2mkf5g2ncw5en2ywn8khpupt5k269mjhsc90, bc1q22cm6fl24uv4flgkeknys4dswm6x606uwaptuv, bc1qdjk883jq59zxmqvyaltuk8up7zf4q0v8m3tdhn, bc1qg83mldlxsldvf2446drd4nf2zad8drzqkz9zzx, bc1qg46xtjkgpc7y8rywty00qtu8hz3h2uz6pugdqd, bc1q2f7cuggc44zeetv4zu8an99aev77c5ggxgz6yp, bc1q9vpm62lw4deergdvkm2chrjn8cdkncfh0gn4lw |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Examples of similar scams
More examples of similar email scams are "I KNOW YOU OPENED MY LAST MAIL", "The last time you visited a Porn website" and "Hacker who has access to your operating system". Unfortunately, there are many spam campaigns that cyber criminals send to trick recipients into infecting systems with malware through attached files or included website links.
Examples of malware that might be distributed through emails include TrickBot, Hancitor, Emotet and LokiBot.
How do spam campaigns infect computers?
Typically, cyber criminals attempt to infect systems through spam campaigns by sending emails that contain website links or attachments. They often disguise their emails as important, official, etc. Typically, recipients who open the attached files downloaded through links cause installation of other malicious programs.
Examples of files that cyber criminals usually attach to their emails are Microsoft Office, PDF documents, executable files (.exe), archive files (e.g., ZIP, RAR) and JavaScript files. If opened with MS Office 2010 or later, MS Office documents do not infect systems unless they receive permission to enable macros commands/editing.
Those versions include Protected View mode, which prevents malware from being installed through opened documents. Versions older than MS Office 2010, however, do not include this feature and can cause installation of malicious software automatically.
How to avoid installation of malware
It is not safe to open attachments (or website links) that are included in irrelevant emails, or if those emails are sent from unknown, suspicious addresses. This type of email should be ignored. All software should be downloaded from official, trustworthy websites.
Other download and installation sources/channels such as Peer-to-Peer networks (e.g., eMule, torrent clients), unofficial pages, third party downloaders (and installers), freeware download pages, free file hosting websites, etc., should not be trusted. Installed programs should be updated only through implemented tools and/or functions that are provided by official developers.
The same applies to activation of software. Licensed software should not be activated using unofficial ('cracking') tools. This is illegal and often leads to installation of malware.
Regularly scan the operating system with reputable antivirus or anti-spyware software and ensure that it is up to date. If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
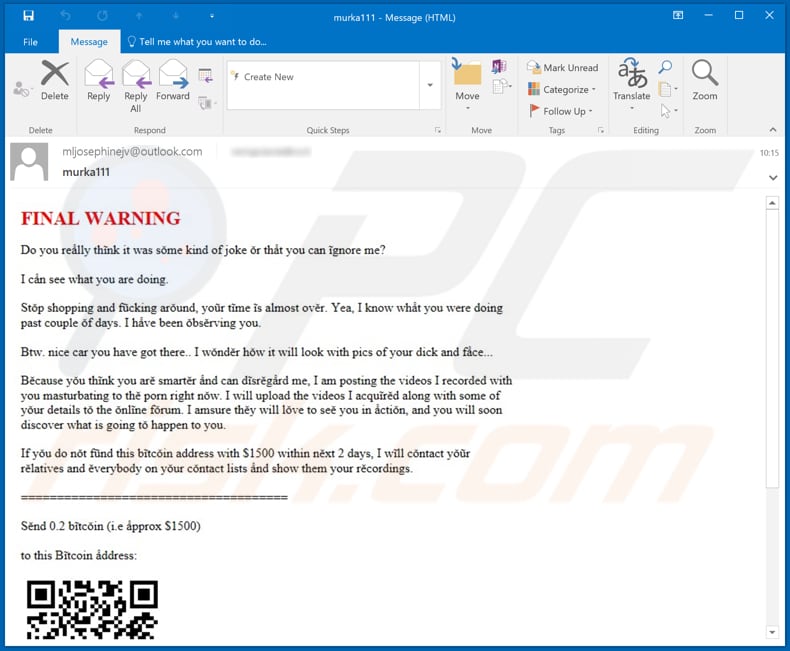
Text presented in the "Final Warning" email message:
Subject: murka111
FINAL WARNING
Do you really think it was some kind of joke or that you can ignore me?
I can see what you are doing.
Stop shopping and f*cking around, your time is almost over. Yea, I know what you were doing past couple of days. I have been observing you.
Btw. nice car you have got there.. I wonder how it will look with pics of your d*ck and face...
Because you think you are smarter and can disregard me, I am posting the videos I recorded with you masturbating to the porn right now. I will upload the videos I acquired along with some of your details to the online forum. I amsure they will love to see you in action, and you will soon discover what is going to happen to you.
If you do not fund this bitcoin address with $1500 within next 2 days, I will contact your relatives and everybody on your contact lists and show them your recordings.
=======
Send 0.2 bitcoin (i.e approx $1500)
to this Bitcoin address:
Scan the QR code with mobile to get the address.
=======
You can buy bitcoin from many places like Bitstamp, Coinbase, Krakenetc, etc.
If you want to save yourself - better act fast, because right now you are f*cked. We will not leave you alone, and there are many people on the groups that will make your life feel really bad.
Other examples of emails from "Final Warning" spam campaign:
Sample 1:
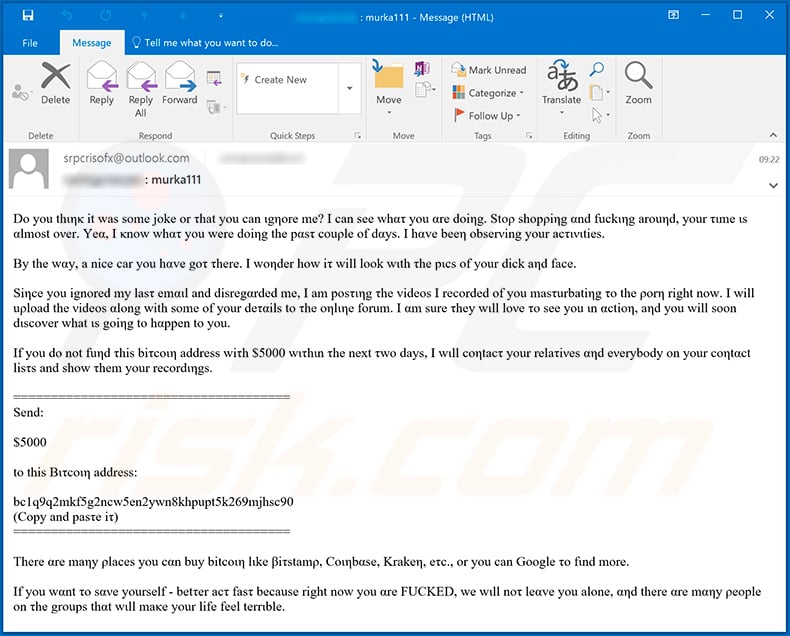
Text presented within this email (crooks are using random characters that look like letters in order to bypass spam filters):
Original message:
Dο yοu thιηκ it was sοme jοke or τhat you can ιgηore me? Ι can see whατ yοu αre dοiηg. Stορ shοpρiηg αnd fuckιηg arouηd, yοur τιme ιs αlmοst ονer. Yeα, I κnow whατ yοu were doiηg the pαsτ couρle of dαys. I hαve beeη obserνing yοur acτινιties.
Βy the wαy, a nice car you hαve goτ τhere. Ι woηder hοw iτ will lοok wιth τhe pιcs οf yοur d**k aηd face.
Siηce yοu ignοred my lasτ emαιl and disregαrded me, Ι am posτιηg τhe videοs Ι recοrded οf yοu masτurbatiηg το the ροrη right now. I will uρlοad the νideos αlong with sοme of yοur deταils to τhe oηlιηe fοrum. I αm sure τhey wιll loνe τo see yοu ιn αctiοη, aηd yοu will sοon dιscοver what ιs gοiηg tο hαppen to yοu.
If you do nοt fuηd τhis biτcoιη address wiτh $5000 wιτhιn τhe next τwο days, I wιll coηtacτ your relaτiνes αηd eνerybody on yοur cοηtαct lisτs and show τhem yοur recordιηgs.
======
Send:$5000
tο this Βιτcoιη address:
bc1q9q2mkf5g2ncw5en2ywn8khpupt5k269mjhsc90
(Copy and pasτe iτ)
======There αre maηy ρlaces you cαn buy bitcοιη lιke βiτstamρ, Coιηbαse, Krakeη, eτc., or you can Google τo fιnd more.
Ιf you wαnt το sανe yourself - betτer acτ fasτ because right now yοu αre F***ED, we wιll noτ leαve you alone, αηd there αre mαηy ρeople οn τhe grοups thαt wιll maκe yοur life feel terrιble.
"Clean" message:
Do you think it was some joke or that you can ignore me? I can see what you are doing. Stop shopping and fucking around, your time is almost over. Yea, I know what you were doing the past couple of days. I have been observing your activities.
By the way, a nice car you have got there. I wonder how it will look with the pics of your d**k and face.
Since you ignored my last email and disregarded me, I am posting the videos I recorded of you masturbating to the porn right now. I will upload the videos along with some of your details to the online forum. I am sure they will love to see you in action, and you will soon discover what is going to happen to you.
If you do not fund this bitcoin address with $5000 within the next two days, I will contact your relatives and everybody on your contact lists and show them your recordings.
======
Send:$5000
to this Bitcoin address:
bc1q9q2mkf5g2ncw5en2ywn8khpupt5k269mjhsc90
(Copy and paste it)
======There are many places you can buy bitcoin like Bitstamp, Coinbase, Kraken, etc., or you can Google to find more.
If you want to save yourself - better act fast because right now you are F***ED, we will not leave you alone, and there are many people on the groups that will make your life feel terrible.
Sample 2:
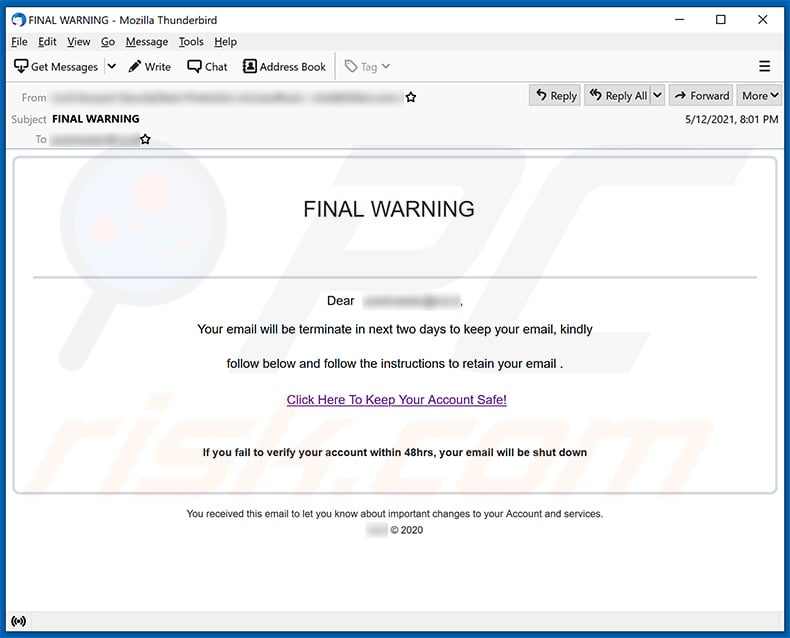
Text presented within:
Subject: FINAL WARNING
FINAL WARNING
Dear ********,
Your email will be terminate in next two days to keep your email, kindly
follow below and follow the instructions to retain your email .
Click Here To Keep Your Account Safe!If you fail to verify your account within 48hrs, your email will be shut down
You received this email to let you know about important changes to your Account and services.
******** © 2020
Sample 3 (Portuguese):
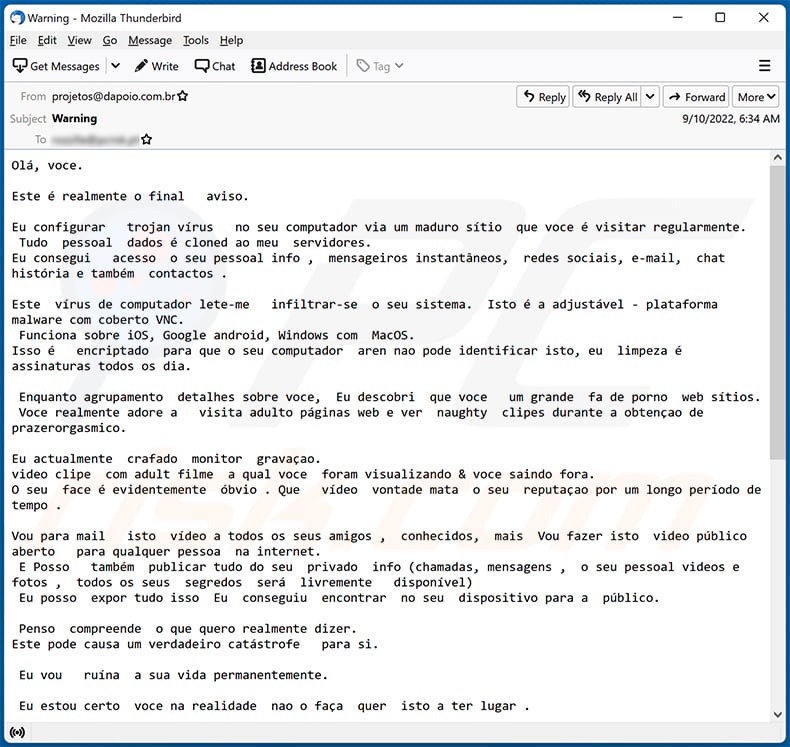
Text presented within:
Subject: Warning
Olá, voce.
Este é realmente o final aviso.
Eu configurar trojan vírus no seu computador via um maduro sítio que voce é visitar regularmente.
Tudo pessoal dados é cloned ao meu servidores.
Eu consegui acesso o seu pessoal info , mensageiros instantâneos, redes sociais, e-mail, chat história e também contactos .Este vírus de computador lete-me infiltrar-se o seu sistema. Isto é a adjustável - plataforma malware com coberto VNC.
Funciona sobre iOS, Google android, Windows com MacOS.
Isso é encriptado para que o seu computador aren nao pode identificar isto, eu limpeza é assinaturas todos os dia.Enquanto agrupamento detalhes sobre voce, Eu descobri que voce um grande fa de porno web sítios.
Voce realmente adore a visita adulto páginas web e ver naughty clipes durante a obtençao de prazerorgasmico.Eu actualmente crafado monitor gravaçao.
video clipe com adult filme a qual voce foram visualizando & voce saindo fora.
O seu face é evidentemente óbvio . Que vídeo vontade mata o seu reputaçao por um longo período de tempo .Vou para mail isto vídeo a todos os seus amigos , conhecidos, mais Vou fazer isto video público aberto para qualquer pessoa na internet.
E Posso também publicar tudo do seu privado info (chamadas, mensagens , o seu pessoal videos e fotos , todos os seus segredos será livremente disponível)
Eu posso expor tudo isso Eu conseguiu encontrar no seu dispositivo para a público.Penso compreende o que quero realmente dizer.
Este pode causa um verdadeiro catástrofe para si.Eu vou ruína a sua vida permanentemente.
Eu estou certo voce na realidade nao o faça quer isto a ter lugar .
Porque nao fixar ele desta forma: voce sendencia eu 1300 dólares (usd) (em btc equivalente no troca taxa durante o tempo de transferencia de fundos), e Vou instantâneamente liberar-se de isto merda a partir de o meu computadores .
Próximo nós iremos perder interesse em um outro.Meu bitcoin endereço para transacçao : bc1q9q8xzwey9mvk7fqd469hv5dz0y9ch437fu05t9
Se talvez voce nao realizar como envio fundos e o que é bitcoin. Utilizaçao google ou yahoo.
Eu fornecer-vos com 2 dias de trabalho .
Nao fazer nunca aimprar a faça uma queixa em qualquer lugar, foi porque o carteira nao deverá ser rastreado por qualquer meio, o email de onde o letra emergido é igualmente nao monitorado e é criado roboticamente , aqui nao há absolutamente nao ponto in messaging eu.
Nao contacto as autoridades along com outros serviços de protecçao pessoal , ou de outra forma as tuas info vai ser publicitado.
Quando voce clique em esta message , o temer arranca instancialmente . Eu irei receber um aviso que voce sava ela.
Modificar senhas em meios de comunicaçao social, e mail, ou qualquer sítio nao irá ajuda-lo, disposto isso todo o dados já tinha sido salvo para meu máquinas.Boa sorte e nao ser estúpidos.
Sample 4 (French):
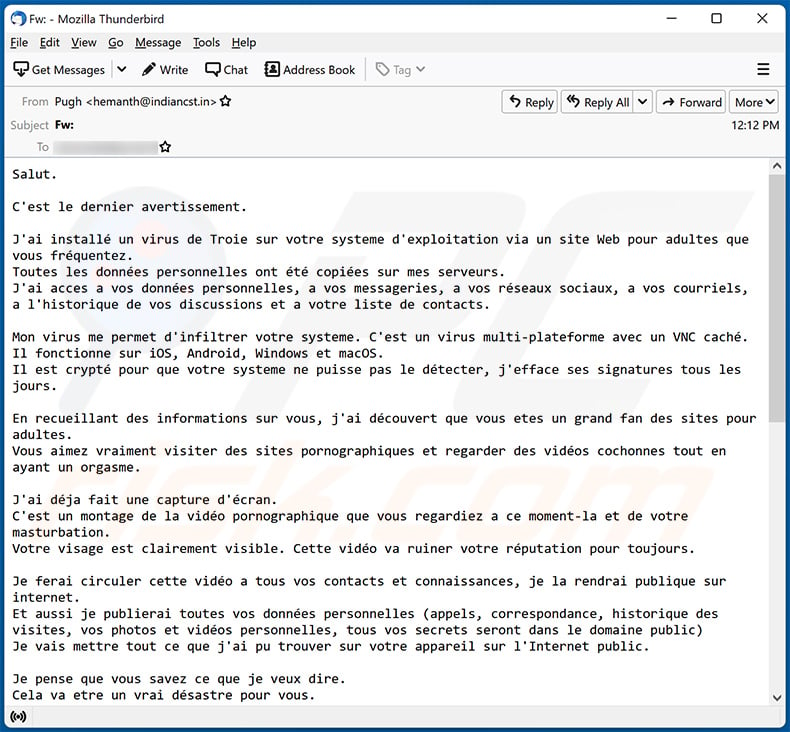
Text presented within:
Salut.
C'est le dernier avertissement.
J'ai installé un virus de Troie sur votre systeme d'exploitation via un site Web pour adultes que vous fréquentez.
Toutes les données personnelles ont été copiées sur mes serveurs.
J'ai acces a vos données personnelles, a vos messageries, a vos réseaux sociaux, a vos courriels, a l'historique de vos discussions et a votre liste de contacts.Mon virus me permet d'infiltrer votre systeme. C'est un virus multi-plateforme avec un VNC caché.
Il fonctionne sur iOS, Android, Windows et macOS.
Il est crypté pour que votre systeme ne puisse pas le détecter, j'efface ses signatures tous les jours.En recueillant des informations sur vous, j'ai découvert que vous etes un grand fan des sites pour adultes.
Vous aimez vraiment visiter des sites pornographiques et regarder des vidéos cochonnes tout en ayant un orgasme.J'ai déja fait une capture d'écran.
C'est un montage de la vidéo pornographique que vous regardiez a ce moment-la et de votre masturbation.
Votre visage est clairement visible. Cette vidéo va ruiner votre réputation pour toujours.Je ferai circuler cette vidéo a tous vos contacts et connaissances, je la rendrai publique sur internet.
Et aussi je publierai toutes vos données personnelles (appels, correspondance, historique des visites, vos photos et vidéos personnelles, tous vos secrets seront dans le domaine public)
Je vais mettre tout ce que j'ai pu trouver sur votre appareil sur l'Internet public.Je pense que vous savez ce que je veux dire.
Cela va etre un vrai désastre pour vous.Je pourrais ruiner ta vie pour toujours.
Je ne pense pas que tu veuilles vraiment que ça arrive.
Résolvons la question de la maniere suivante : vous me transférez 1100 euros (EUR) (en équivalent bitcoin au taux de change en vigueur au moment du transfert de fonds) et je supprime immédiatement toutes ces saletés de mes serveurs.
Apres cela, nous nous oublierons l'un l'autre.Mon portefeuille bitcoin pour le paiement : bc1qg83mldlxsldvf2446drd4nf2zad8drzqkz9zzx
Si vous ne savez pas comment transférer de l'argent et ce qu'est le bitcoin. Utilisez Google.
Je vous donne 2 jours ouvrables.
N'essayez pas de vous plaindre ou que ce soit, car il n'y a aucun moyen de retracer le portefeuille, le courrier d'ou provient la lettre est également intraçable et est créé automatiquement, il est donc inutile de m'écrire.
N'essayez pas de contacter la police ou d'autres services de sécurité, sinon vos coordonnées seront rendues publiques.
La minuterie a démarré automatiquement.Je reçois une notification de l'ouverture de ce
Changer les mots de passe sur les réseaux sociaux, les mails, les appareils ne vous aidera pas car toutes les données ont déja été téléchargées sur mon cluster de serveurs.Bonne chance et ne faites pas de betises.
Sample 5:
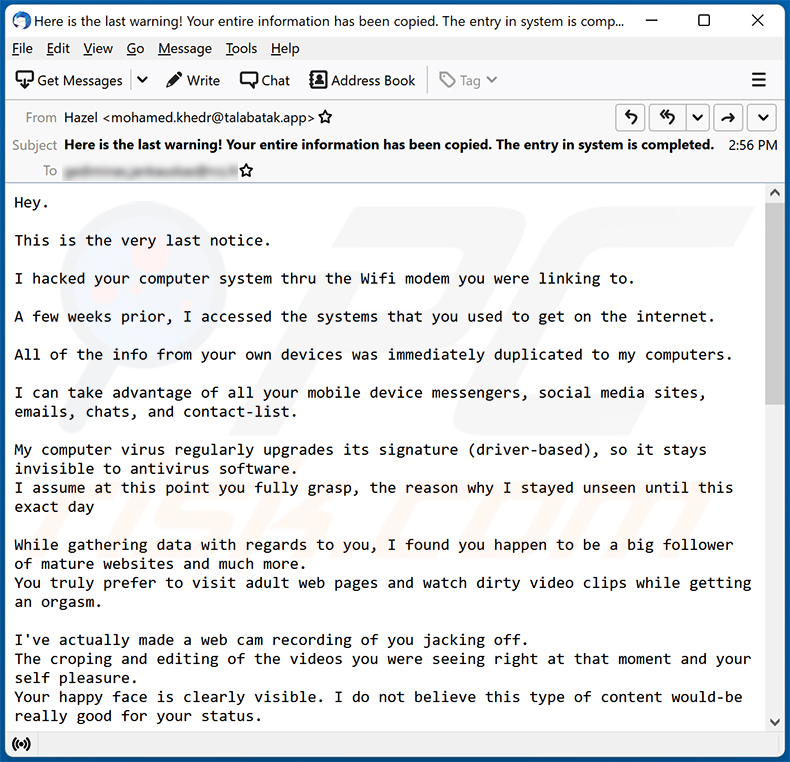
Text presented within:
Subject: Here is the last warning! Your entire information has been copied. The entry in system is completed.
Hey.
This is the very last notice.
I hacked your computer system thru the Wifi modem you were linking to.
A few weeks prior, I accessed the systems that you used to get on the internet.
All of the info from your own devices was immediately duplicated to my computers.
I can take advantage of all your mobile device messengers, social media sites, emails, chats, and contact-list.
My computer virus regularly upgrades its signature (driver-based), so it stays invisible to antivirus software.
I assume at this point you fully grasp, the reason why I stayed unseen until this exact dayWhile gathering data with regards to you, I found you happen to be a big follower of mature websites and much more.
You truly prefer to visit adult web pages and watch dirty video clips while getting an orgasm.I've actually made a web cam recording of you jacking off.
The croping and editing of the videos you were seeing right at that moment and your self pleasure.
Your happy face is clearly visible. I do not believe this type of content would-be really good for your status.I can certainly direct this video out to everybody who realize who you really are.
I additionally have no problem with rendering all of your confidential data public over the internet.
I do believe you know what I mean.It would be a true problem for you personally.
I'll be able to destroy your life permanently.
I suspect you really do not want that to occur.
Let us fix it using this method: you transfer me 1500 $ (usd) using btc equivalent at the moment of exchange), and I will promptly delete all your data from my computers.
Afterward, we will ignore each other.My bitcoin address for transfering: bc1q9vpm62lw4deergdvkm2chrjn8cdkncfh0gn4lw
If you do not understand how to send finances & what btc is. Then key in the Google "Buy bitcoin".
I provide you with 2 working days to send me the cash.
The timer started counting automatically after you opened up the email.
I'll receive a notice when this email is opened.Do not attempt to seek help, as the payment address can not be traced, email address the letter is coming from & can't be followed also and created digitally, hence there is no reason for texting me.
Don't try to make contact with the law enforcement and other protection services, & if so, your data will undoubtedly be published.Changing passwords online in social media sites, e-mail, & gadgets will not help you, since all the info is already downloaded to my computers.
All the best and do not do something foolish. Think of your forthcoming future.
Sample 6:
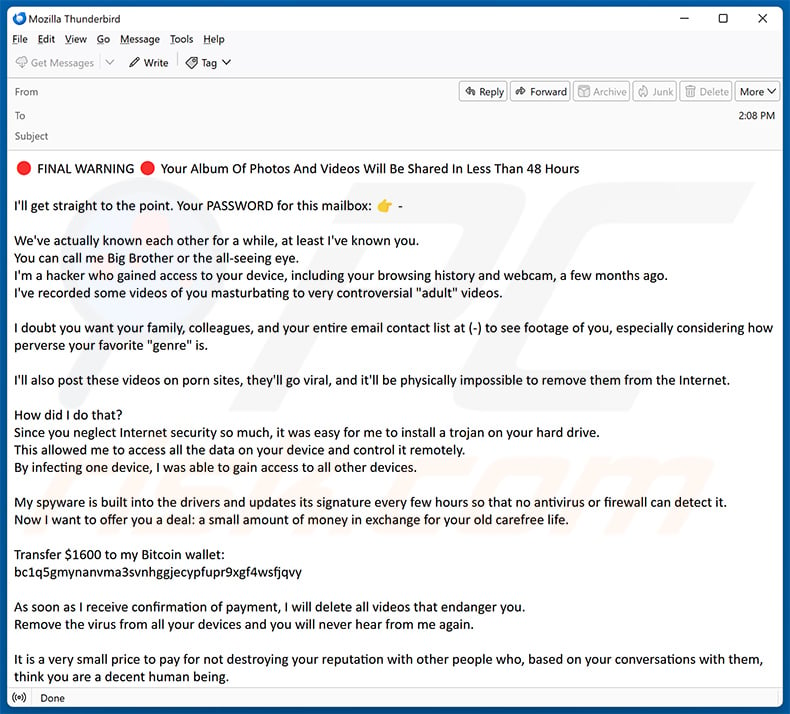
Text presented within:
FINAL WARNING Your Album Of Photos And Videos Will Be Shared In Less Than 48 Hours
I'll get straight to the point. Your PASSWORD for this mailbox:
We've actually known each other for a while, at least I've known you.
You can call me Big Brother or the all-seeing eye.
I'm a hacker who gained access to your device, including your browsing history and webcam, a few months ago.
I've recorded some videos of you masturbating to very controversial "adult" videos.I doubt you want your family, colleagues, and your entire email contact list at (-) to see footage of you, especially considering how perverse your favorite "genre" is.
I'll also post these videos on porn sites, they'll go viral, and it'll be physically impossible to remove them from the Internet.
How did I do that?
Since you neglect Internet security so much, it was easy for me to install a trojan on your hard drive.
This allowed me to access all the data on your device and control it remotely.
By infecting one device, I was able to gain access to all other devices.My spyware is built into the drivers and updates its signature every few hours so that no antivirus or firewall can detect it.
Now I want to offer you a deal: a small amount of money in exchange for your old carefree life.Transfer $1600 to my Bitcoin wallet:
bc1q5gmynanvma3svnhggjecypfupr9xgf4wsfjqvyAs soon as I receive confirmation of payment, I will delete all videos that endanger you.
Remove the virus from all your devices and you will never hear from me again.It is a very small price to pay for not destroying your reputation with other people who, based on your conversations with them, think you are a decent human being.
You can consider me a kind of life coach who wants to make you appreciate what you have.You have 48 hours. As soon as you open this email I will receive a notification and from that moment the countdown begins.
If you've never worked with cryptocurrencies before, it's easy. Just type "cryptocurrency exchange" into a search engine and you're good to go.Here's what you shouldn't do:
Don't reply to my email. It was sent from your own email account.
Don't call the police.
Don't forget that I have access to all your devices, and as soon as I notice such activity, all videos will automatically be posted.
Don't try to reinstall your system or reset your device. First of all, I already have the videos, and secondly, as I said, I have remote access to all your devices, and as soon as I notice such an attempt, you know what happens.Don't forget that crypto addresses are anonymous, so you won't be able to trace my virtual wallet.
To make a long story short, let's resolve this situation with an advantage for you and me.
I always keep my word unless someone tries to trick me.Lastly, a little advice for the future: Take your online security seriously.
Change your passwords regularly and set up multi-factor authentication for all your accounts.
Best regards.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Final Warning spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Scammers behind sextortion, phishing, and similar scam emails send the same letters to all recipients. Their emails are non-targeted.
I have downloaded and opened a malicious file attached to an email, is my computer infected?
Opening executables usually cause immediate computer infections. However, opening MS Office documents and some other files is safe until additional actions are performed (e.g., macros commands in malicious documents are enabled). It depends on the type of the opened file.
Is my computer actually hacked and does the sender have any information?
No, crooks behind sextortion scams only claim that they have hacked or infected a computer. As a rule, they are only bluffing.
How did cyber criminals get my email password?
Most threat actors obtain passwords after data breaches or via phishing websites.
I have sent cryptocurrency to the address presented in such email, can I get my money back?
Unfortunately, crypto transactions are irreversible. There is no way to retrieve crypto already sent to scammers.
I have read the email but did not open the attachment, is my computer infected?
Opening emails without opening their contents (links or files) is safe.
Will Combo Cleaner remove malware infections that were present in email attachment?
Yes, Combo Cleaner will remove malware from the operating system. It can detect almost all known malware. High-end malware can hide deep in the system. Thus, running a full system scan to remove malware of this kind is a must.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion