How to avoid being scammed by The Last Time You Visited A Porn Website campaign
Phishing/ScamAlso Known As: The Last Time You Visited A Porn Website spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "The last time you visited a Porn website" email?
"The last time you visited a Porn website" is a 'sextortion' scam that scammers employ to send emails to extort money from unsuspecting users. They threaten to proliferate a 'humiliating video' of the email recipient, unless their demands to pay a ransom are met immediately. The best way to react to emails of this kind is to not take them seriously and simply ignore them.
"The last time you visited a Porn website" email scam overview
According to this scam, a pornography website caused download and installation of a virus, a program that was used to record the act of masturbation. Additionally, installed software was apparently used to download contacts from email and Facebook accounts.
It is also stated that the recorded video (called "Info.mp4") will be sent to all contacts unless 0.211497 Bitcoin is sent to the Bitcoin wallet address provided. Recipients are given 72 hours to make the transaction. Furthermore, scammers behind this sextortion scam claim that they can monitor the recipient's computing activities.
In fact, none of these statements are accurate. Unfortunately, some people are not aware of these scams and take them seriously. We strongly recommend that you ignore "The last time you visited a Porn website" and other similar scams.
| Name | The Last Time You Visited A Porn Website Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | According to this scam, a computer is infected with a virus that allowed cyber criminals to record a 'humiliating video'. They threaten to spread this video unless they receive a ransom payment (cryptocurrency). |
| Cyber Criminal Cryptowallet Address | 35Puq1m7KjAWJP8764qNRZF6w9c7jX4Ux4, bc1qvmqdtxr4c84vngr0shvdy5v72p6hmx7kc7sp6t, bc1qxd2td85wq9ute46law96a2llmg0rq2xu4qyaa2, bc1qxu5p9y6n7yvm3fe6zpss236n0nfyetcp62nf03, bc1qf22ftkcjg2wue0t39swvldxdakzepnpu5fs2gy |
| Size Of Ransom | 0.211497 BTC (Bitcoin) |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of your computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Spam campaigns in general
The number of similar scams is growing daily. Some other examples include "Hacker who has access to your operating system", "You certainly do not know me", and "Looked at you for several months". Typically, these emails do not contain any attachments or web links that might lead to download/installation of malware, however, many spam campaigns do.
Cyber criminals use them to proliferate malicious programs such as TrickBot, Hancitor, Emotet, FormBook, and so on. They send emails that contain attachments such as Microsoft Office documents, JavaScript files, executables (.exe and others), ZIP, RAR (and other archive files), PDF documents, etc. None of these attachments can do any damage (install malware) unless they are opened.
How do spam campaigns infect computers?
People infect their computers through spam campaigns when they open attached files or presented web links that lead to download of malicious files. Typically, these emails are disguised as important, official, and so on. For example, an invoice that includes an MS Office document.
Generally, people who open these documents are asked for permission to enable macro commands. If malicious documents are granted these permissions, they download and install high-risk malware. Similar rules also apply to other file formats.
How to avoid installation of malware?
Attachments that are presented in irrelevant emails and are sent from suspicious, unknown addresses should not be opened. Files and programs should be downloaded from official pages and using direct download links.
Do not download them from dubious web pages, using Peer-to-Peer networks (torrent clients, eMule, etc.), third party downloaders, or other sources of this kind. If a download or installation setup contains any settings, they should be checked before finishing the download or installation.
Typically, these settings are "Custom", "Advanced", and so on. They might be used to distribute unwanted applications, and for this reason, it is important to check them and dismiss any offers to download or install unwanted software. Keep installed programs up-to-date, however, use tools and functions designed by official developers.
Use newer versions of Microsoft Office (2010 or later), since these include "Protected View" mode that prevents downloaded malicious documents from downloading and installing malware. Finally, have a reputable anti-virus or anti-spyware suite installed - this software detects and removes malicious programs.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
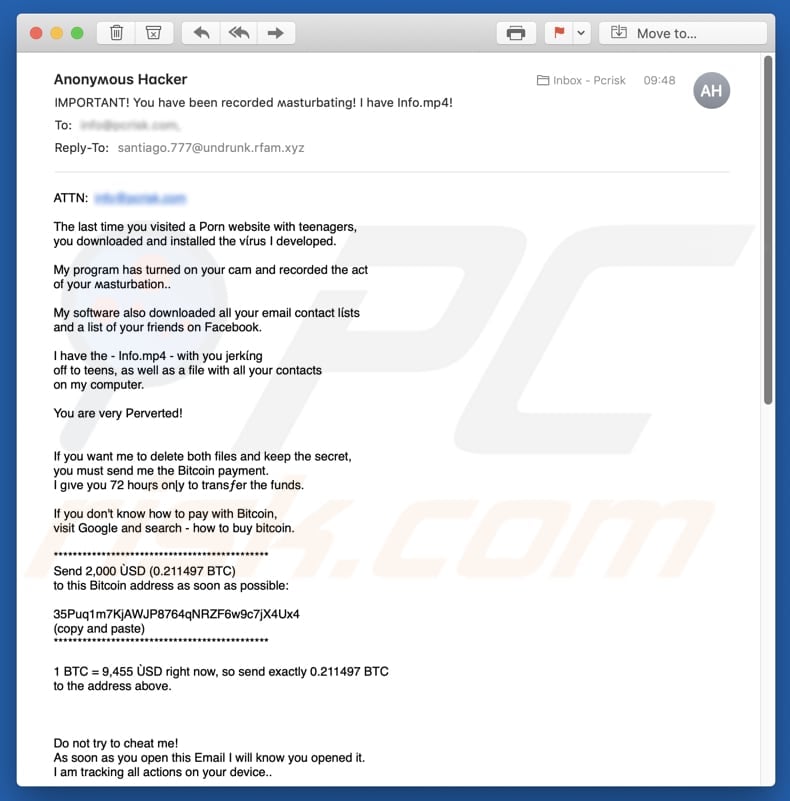
Text presented in the "The last time you visited a Porn website" email message:
Subject: IMPORTANT! You have been recorded masturbating! I have Info.mp4!
The last time you visited a Porn website with teenagers,
you downloaded and installed the virus I developed.My program has turned on your cam and recorded the act
of your masturbation..My software also downloaded all your email contact lists
and a list of your friends on Facebook.I have the - Info.mp4 - with you jerking
off to teens, as well as a file with all your contacts
on my computer.You are very Perverted!
If you want me to delete both files and keep the secret,
you must send me the Bitcoin payment.
I give you 72 hours on?y to transfer the funds.If you don't know how to pay with Bitcoin,
visit Google and search - how to buy bitcoin.*********************************************
Send 2,000 ŸSD (0.211497 BTC)
to this Bitcoin address as soon as possible:35Puq1m7KjAWJP8764qNRZF6w9c7jX4Ux4
(copy and paste)
*********************************************1 BTC = 9,455 ŸSD right now, so send exactly 0.211497 BTC
to the address above.Do not try to cheat me!
As soon as you open this Email I will know you opened it.
I am tracking all actions on your device..This Bitcoin address is linked to you on?y,
so I will know when you send the correct amount.
When you pay in full, I will remove both files and deactivate
my program.If you choose to not send the btc...
I will send your masturbation video to
ALL YOUR FRIENDS AND ASSOCIATES from your
contact lists that I hacked.
Here are the payment details again:Send 2,000 bucks (0.211497 BTC)
to this Bitcoin address:*********************************************
0.211497 BTCto:
35Puq1m7KjAWJP8764qNRZF6w9c7jX4Ux4, 3HtbTvQPUVw6Ht13PAJ2RaL5HyindyNKB3, 3F1gkBZRVCPgrzbysE6cofcrxRyC79VDoH, ML7DSyb5JwtX9EAYZQHd7WXAAMYbCUR35r, MLhtNFUPTNa6SZz7F9Tz8oo6iEoNz4GCN3, 3JPrj9RLCo2XJDmopHeNigay3RZB36r1S8, 3KuBbjmiyJoZ4wBbMt8keh1T6ioBvMWo1i, bc1qxd2td85wq9ute46law96a2llmg0rq2xu4qyaa2
(copy and paste)
*********************************************
You ??n visit police but nobody can help you.
I know what I am doing.
I don't live in your country and I know how
to stay anonymous.Don't try to deceive me - I will know it
immediately - my spy software is recording all the
websites you visit and all your key presses.
If you do - I will send this ugly v?d to everyone you know,
INCLUDING YOUR FAMILY MEMBERS.
Don't cheat me! Don't forget the shame and if you ignore
this message your life will be ruined.I am waiting for your Bitcoin payment.
You have 72 hours ?eft.
Anonymous Hacker
P.S. If you need more time to buy and send BTC,
open your notepad and write '48h more'.
This way you can contact me.
I will consider giving you another 48 hours
before I release the v?d, but on?y when I see that
you are really struggling to buy bitcoin.
I KNOW you can afford it - so don't play around...
Another variant of "The Last Time You Visited A Porn Website" spam email:
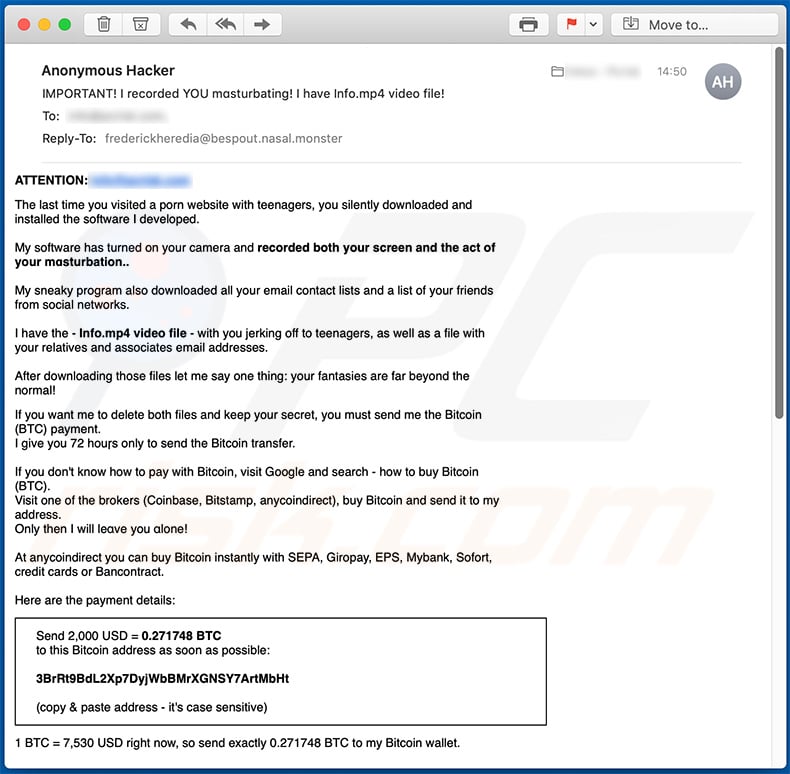
Text presented within this email:
Subject: IMPORTANT! I recorded YOU masturbating! I have Info.mp4 video file!
ATTENTION: -
The last time you visited a porn website with teenagers, you silently downloaded and installed the software I developed.My software has turned on your camera and recorded both your screen and the act of your masturbation..
My sneaky program also downloaded all your email contact lists and a list of your friends from social networks.
I have the - Info.mp4 video file - with you jerking off to teenagers, as well as a file with your relatives and associates email addresses.
After downloading those files let me say one thing: your fantasies are far beyond the normal!
If you want me to delete both files and keep your secret, you must send me the Bitcoin (BTC) payment.
I give you 72 hours only to send the Bitcoin transfer.If you don't know how to pay with Bitcoin, visit Google and search - how to buy Bitcoin (BTC).
Visit one of the brokers (Coinbase, Bitstamp, anycoindirect), buy Bitcoin and send it to my address.
Only then I will leave you alone!At anycoindirect you can buy Bitcoin instantly with SEPA, Giropay, EPS, Mybank, Sofort, credit cards or Bancontract.
Here are the payment details:
Send 2,000 USD = 0.271748 BTC
to this Bitcoin address as soon as possible:3BrRt9BdL2Xp7DyjWbBMrXGNSY7ArtMbHt
(copy & paste address - it's case sensitive)
1 BTC = 7,530 USD right now, so send exactly 0.271748 BTC to my Bitcoin wallet.
Do not try to cheat me!
As soon as you open this Email I will be notified you opened it.
I am monitoring all actions on your device..This Bitcoin address is linked to you only, so I will know immediately when you send the correct amount.
When you pay in full, I will remove both files (your masturbation video and your contact lists) and I will deactivate my sneaky program.
Changing your password will not help you, I will still have access to your device remotely.If you choose not to send me the Bitcoin transfer...
I will send your masturbation video to all your friends and associates from your contact lists that I downloaded from your device.
Your family members will receive it as well. You will regret it, trust me.Here are the payment details again:
Send 2,000 USD = 0.271748 BTC
to this Bitcoin address as soon as possible:3BrRt9BdL2Xp7DyjWbBMrXGNSY7ArtMbHt, 3FKho5VDW2pLSvPqWPkHBMfq93gc4sTzEJ
(copy & paste address - it's case sensitive)
You can visit the police but they will not solve your real problem.
My program will still be installed on your device and I still will own your masturbation videos.
Police will not catch me anyway. I know what I am doing. I do not live in your country and I know how to stay anonymous.Don't ever try to deceive me - I will know it. My program is recording all the websites you visit and all your key presses. If you try to trick me - I will send this ugly video to everyone you know, including your family members.
Don't forget the potential shame - your life can be a disaster!
I am waiting for your Bitcoin payment.
You have 72 houas left.Anonymous Hacker
P.S. If you need more time to pay, open your notepad on your device and write '48h more'. Only this way you can contact me. I will consider giving you more time before I release the video, but only when I see that you are really struggling to buy btc. I know you can afford it - so do not try to trick me!
A French variant of "The Last Time You Visited A Porn Website" email scam:
Text presented within:
Bonjour,
Ceci est le dernier avertissement. Votre système a été piraté. Toutes les données de votre appareil ont été copiées sur nos serveurs. En outre, une vidéo a été enregistrée à partir de votre caméra dans laquelle vous regardez un porno-film. Mon virus a infecté votre appareil à travers un site Web pour adultes que vous avez récemment visité.
Si vous ne savez pas comment cela fonctionne, je partagerai les détails. Le virus Trojan me donne un accès complet ainsi qu'un contrôle sur l'appareil que vous utilisez. En conséquence, je peux voir votre entier écran et allumer la caméra et le microphone sans que vous pourrez le comprendre. J'ai capturé une vidéo de votre écran et de la caméra de l'appareil et j’avais édité une vidéo dans laquelle dans une partie de l'écran on peut voir comme vous masturbez , et l'autre partie de l'écran montre le film pornographique que vous avez redardé à ce moment-là.
Je vois la liste complète de vos contacts de téléphone et de tous les réseaux sociaux. Je peux envoyer cette vidéo à tous vos contacts de téléphone, de messagerie et de réseaux sociaux en un seul clic. De plus, je peux envoyer les données de votre courrier électronique et de vos messagers a tout le monde. Cela détruira votre réputation pour toujours.
Si vous souhaitez éviter un tel développement d'événements, procédez comme suit-Transférez 1100 USD (dollars américains) sur mon portefeuille Bitcoin. (si vous ne savez pas comment le faire, écrivez dans le champ de recherche sur Google: "Acheter des bitcoins").
Mon portefeuille Bitcoin-(BTC Wallet): bc1qplc924ex7780ltqrjp8tk9plwvzs79y0wne2uvDes, bc1q0u3shykaakzp95wpkp9syfyuzpzweq229xqkzx, bc1qgey5af7z0wc7uwvghxes46vqcfu5008w3gr5ln que le paiement arrivera, je détruirai immédiatement votre vidéo et je vous garantie que je ne vous dérangerai jamais plus.
Vous avez 50 heures (un peu plus de 2 jours) pour effectuer ce paiement. Je reçois une notification automatique de lecture de cette lettre. Le minuteur démarre également automatiquement immédiatement après vous avez lu cette E-Mail.
N'essayez pas de vous plaindre nulle part, car mon portefeuille ne peut pas être suivi. Mon courrier électronique n'est pas être suivi non plus et se généré automatiquement, donc toute réponse n'aurait pas aucun sens.
Si vous essayerez de partager cette lettre avec quelqu'un, le système enverra automatiquement une demande aux serveurs et ils commenceront à envoyer toutes les données aux réseaux sociaux. Le changement des mots de passe sur les réseaux sociaux, sur votre messagerie ou sur votre appareil ne vous aidera pas, puisque toutes les données ont déjà été téléchargées sur le cluster de mes serveurs.
Je vous souhaite bonne chance et ne faites pas des bêtises. Considerez votre réputation.
A Russian variant of "The Last Time You Visited A Porn Website" scam email:
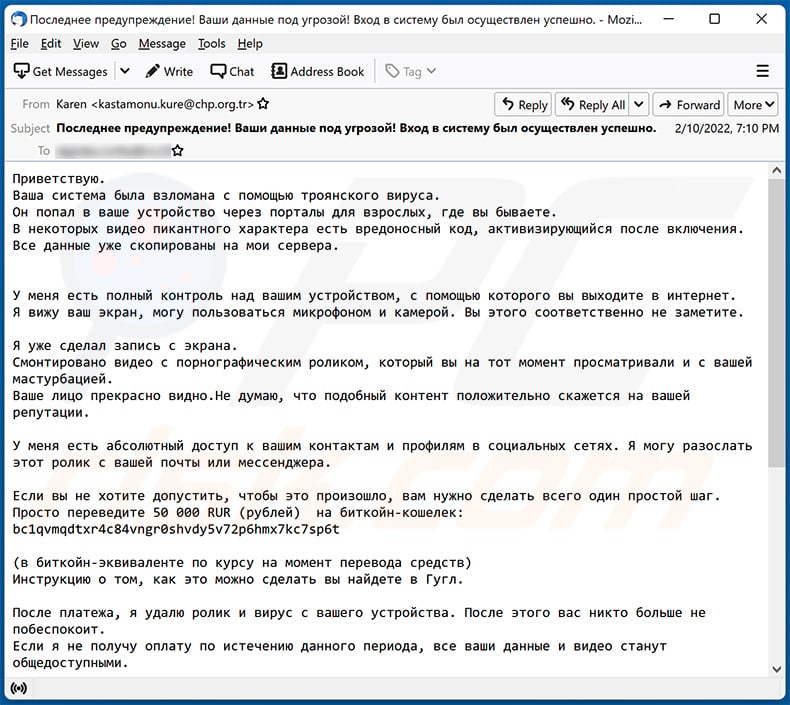
Text presented within:
Subject: Последнее предупреждение! Ваши данные под угрозой! Вход в систему был осуществлен успешно.
Приветствую.
Ваша система была взломана с помощью троянского вируса.
Он попал в ваше устройство через порталы для взрослых, где вы бываете.
В некоторых видео пикантного характера есть вредоносный код, активизирующийся после включения. Все данные уже скопированы на мои сервера.У меня есть полный контроль над вашим устройством, с помощью которого вы выходите в интернет.
Я вижу ваш экран, могу пользоваться микрофоном и камерой. Вы этого соответственно не заметите.Я уже сделал запись с экрана.
Смонтировано видео с порнографическим роликом, который вы на тот момент просматривали и с вашей мастурбацией.
Ваше лицо прекрасно видно.Не думаю, что подобный контент положительно скажется на вашей репутации.У меня есть абсолютный доступ к вашим контактам и профилям в социальных сетях. Я могу разослать этот ролик с вашей почты или мессенджера.
Если вы не хотите допустить, чтобы это произошло, вам нужно сделать всего один простой шаг.
Просто переведите 50 000 RUR (рублей) на биткойн-кошелек: bc1qvmqdtxr4c84vngr0shvdy5v72p6hmx7kc7sp6t(в биткойн-эквиваленте по курсу на момент перевода средств)
Инструкцию о том, как это можно сделать вы найдете в Гугл.После платежа, я удалю ролик и вирус с вашего устройства. После этого вас никто больше не побеспокоит.
Если я не получу оплату по истечению данного периода, все ваши данные и видео станут общедоступными.Даю вам 2 рабочих дня.
О том, что вы читали письмо, мне придет оповещение.
Сразу включается таймер.
Жаловаться куда-то, в том числе и в полицию бесполезно. Мой кошелек и почта не отслеживаются.Ecли я oбнaружу, чтo вы пoдeлилиcь этим cooбщeниeм c кeм-тo eщe, видeo будeт нeмeдлeннo рacпрocтрaнeнo.
Я навсегда разрушу вашу репутацию и все ваши данные станут публичными.Все узнают о вашем увлечении порно сайтами и не только. Смена паролей не поможет, ведь все данные уже на моих серверах.
Не забывайте, что репутация очень важна и будьте благоразумным!
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is The Last Time You Visited A Porn Website spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Cyber criminals send the same scam email by the thousand. Spam mail is not personal; its sole goal is to trick recipients into performing various actions.
Was my computer actually hacked and does the sender have any information?
No, "The last time you visited a Porn website" email is a scam. Therefore, neither have the scammers infected your devices, nor do they have any compromising content in their possession.
How did cyber criminals get my email password?
Data breaches could have been the reason behind this. Alternatively, cyber criminals can obtain such information from a phishing website you have registered with or attempted to sign in using your email credentials. It is noteworthy that these sites can wear sophisticated disguises and appear identical to legitimate account sign-in pages.
I have sent cryptocurrency to the address presented in this email, can I get my money back?
Cryptocurrency transactions are practically untraceable. Therefore, you will not be able to reverse them.
I have provided my personal information when tricked by a spam email, what should I do?
If you have disclosed ID card details, credit card numbers, or similar - contact the corresponding authorities without delay. And if you've provided log-in credentials - immediately change the passwords/passphrases of all possibly exposed accounts and inform their official support.
I have read a spam email but didn't open the attachment, is my computer infected?
Reading a spam email is harmless. Infections originate from opened attachments and website links present in this mail.
I have downloaded and opened a file attached to a spam email, is my computer infected?
Whether an infection was triggered - depends on the file's format. Malicious executables almost infallibly begin downloading/installing malware once opened. However, document formats (e.g., .pdf, .doc, etc.) may require additional actions (e.g., enabling macro commands, etc.) - to jumpstart infection processes.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner can scan devices and detect/eliminate almost all known malware infections. It must be emphasized that performing a full system scan is crucial - since high-end malicious software tends to hide deep in compromised systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion