How to remove Grandoreiro trojan from your computer
TrojanAlso Known As: Grandoreiro banking trojan
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Grandoreiro?
Grandoreiro is the name of malicious software, a banking Trojan written in the Delphi programming language. It targets users in Brazil, Mexico, Spain and Peru. Cyber criminals attempt to infect computers with software of this type to generate revenue by misusing information stolen by programs such as Grandoreiro.
These Trojans steal banking-related information, and thus victims are exposed to risk of monetary loss. If your computer is infected with Grandoreiro (or other malicious programs), uninstall/remove it immediately.
Grandoreiro overview
Typically, banking Trojans steal information such as login credentials (logins, passwords), account numbers, credit card details, and other confidential information stored or processed through various online banking systems. Cyber criminals misuse stolen information to generate revenue by making fraudulent purchases and transactions, selling it to third parties and in other ways.
They misuse the details specifically for financial gain and attempt to generate as much revenue as possible. In most cases, victims of banking Trojans such as Grandoreiro suffer a monetary loss, experience problems relating to online privacy, become victims of identity theft and are at risk of other serious problems.
If you believe that Grandoreiro is already installed on the operating system, remove this malicious software immediately.
| Name | Grandoreiro banking trojan |
| Threat Type | Trojan, password-stealing virus, banking malware. |
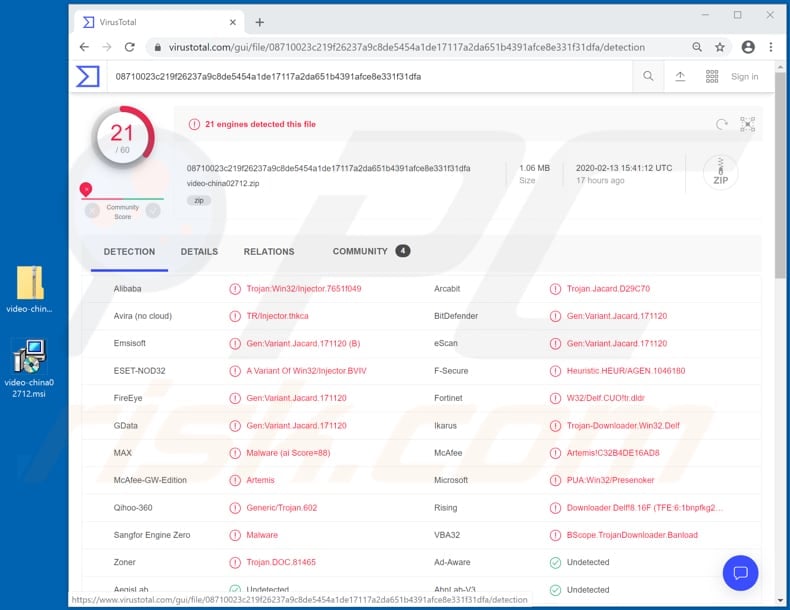
| Detection Names (video-china02712.zip) | Arcabit (Trojan.Jacard.D29C70), Emsisoft (Gen:Variant.Jacard.171120 (B)), ESET-NOD32 (A Variant Of Win32/Injector.BVIV), Microsoft (PUA:Win32/Presenoker), Full List (VirusTotal) |
| Detection Names (video-china02712.msi) | Arcabit (Trojan.Jacard.D29C70), BitDefender (Gen:Variant.Jacard.171120), ESET-NOD32 (A Variant Of Win32/Injector.BVIV), Microsoft (Trojan:Win32/Grandoreiro!MTB), Full List (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Malicious websites, infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Data-stealing malware examples
Other examples of Trojans that are designed to steal confidential information and perform other actions include KBOT, Lampion and CryptBot.
In most cases, Trojans steal information and infect operating systems with other malware (e.g., ransomware). In any case, cyber criminals proliferate programs of this type simply to generate. We strongly recommend that you take all necessary precautions to prevent installation of these programs.
How did Grandoreiro infiltrate my computer?
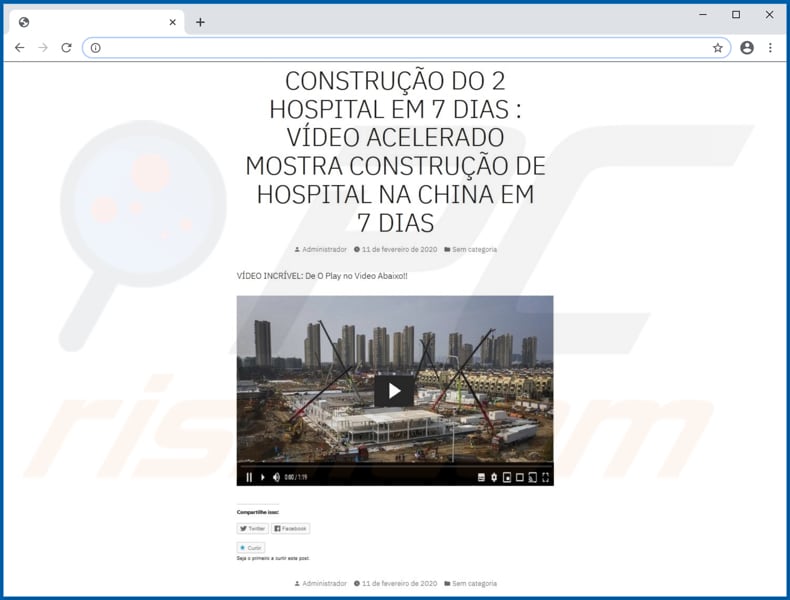
Cyber criminals proliferate Grandoreiro through malicious websites that offer fake Java, Flash updates or contain videos supposedly relating to the coronavirus, however, if a visitor clicks the "Play" button, the websites download an archive file named "video-china02712.zip" (the downloaded file might be named differently), which contains a malicious executable (.exe) file.
If opened/executed, this file installs Grandoreiro and allows it to steal personal data. Peer-to-Peer networks (e.g., torrent clients, eMule), free file hosting, freeware download websites, third party downloaders are examples of other file or software download channels, sources that can be used by cyber criminals to host malicious files.
Unfortunately, there are more ways to proliferate malware. For example, emails (spam campaigns), fake software updating tools, and unofficial activation ('cracking') tools. Cyber criminals employ spam campaigns to proliferate viruses by sending malicious attachments via email.
They send emails that include infected Microsoft Office documents, archive files, PDF files, executables, JavaScript files and so on, hoping that people will open them. If opened, these attachments or links download and install malware.
Fake software updating tools infect operating systems by installing malware rather than updates or by exploiting bugs/flaws of any outdated software that is installed on the operating system. Software 'cracking' tools are designed activate licensed programs free of charge (bypass paid activation), however, they often install malicious programs.
How to avoid installation of malware
If a received email is irrelevant, is sent from unknown address or contains an attachment (or website link), ignore it. Do not open files or web links that are presented in these emails without being sure that it is safe to do so. Software should be downloaded from official websites and direct download links.
Other sources (such as Peer-to-Peer networks, third party downloaders, unofficial pages, etc.) could be used to proliferate malware. Installed programs should be updated through implemented functions or tools that are provided by official software developers. The same applies to activation.
It is illegal to use third party tools to activate licensed programs, and this can lead to system infections with malware.
Regularly scan the operating system for threats with a reputable antivirus or anti-spyware suite and keep this software up to date. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Malicious website designed to trick visitors into downloading a file that contains a malicious executable:
Update 29 April 2020 - The newest version of Grandoreiro can update itself, log (capture) keystrokes, simulate mouse and keyboard, force browsers to open chosen addresses or block access to them, restart the computer and log victims out of the Windows operating system.
It can also collect data such as username, operating system version, computer name, list of installed programs, and check if Diebold's GAS Technologia (online payment and mobile banking security app) is installed on the victim's computer.
Research shows that some Grandoreiro versions are capable of stealing credentials stored in Google Chrome and data stored in Microsoft Outlook. Additionally, Grandoreiro includes a tool that can be used to spread spam email campaigns - the tools allows cyber criminals to create and send the spam messages through utilized EASendMail SDK.
This banking Trojan is also capable of blocking banking access protection programs such as Trusteer and GAS Technologia by changing Trusteer's file system path and killing GAS Technologia's running processes.
Update 26 June 2020 - The new Grandoreiro variant has some improvements in its communication with the C2 (Command and Control) server, it now uses Latenbot botnet modules to communicate between C2 and infected computers. In other words, Grandoneiro creates a sort of a botnet. Also, it now targets not only users in Brazil, Mexico, Spain and Peru, but also in Portugal.
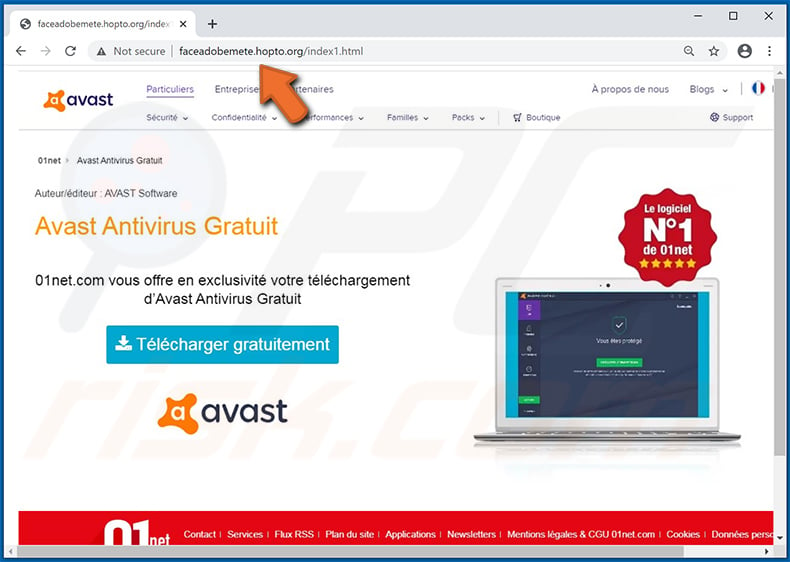
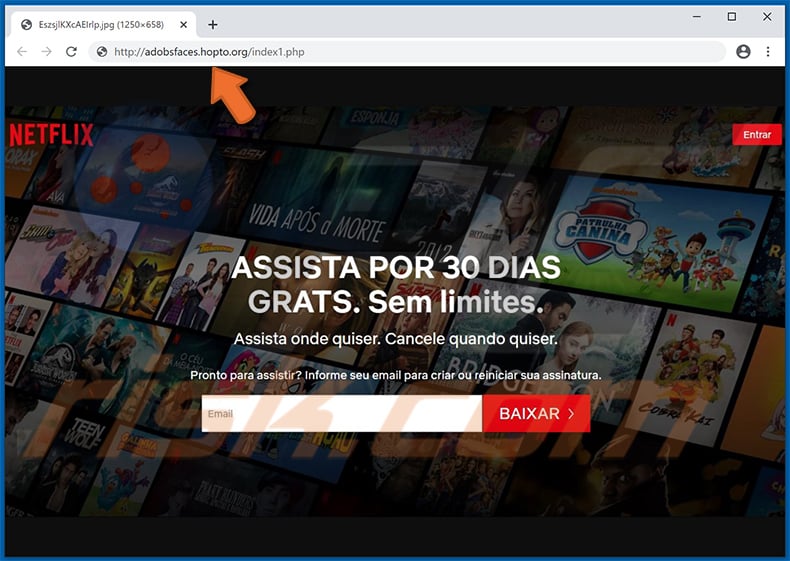
Cyber criminals have recently developed two fake websites targeting France users in order to spread Grandoreiro. One of the sites offers a download of the Avast anti-virus suite and the other one supposedly provides access to Netflix.
Screenshot of the fake Avast download website (faceadobemete.hopto[.]org):
Screenshot of the fake Netflix website (adobsfaces.hopto[.]org):
Update 25 August 2022 - The most recent Grandoreiro variant includes several new features. In now uses domain generation algorithm to communicate with Command and Control (C2) sever. Also, it can log keystrokes (record keyboard input), automatically update itself (if newer versions and modules are created), perform web injection and restrict access to specific web pages.
Moreover, Grandoreiro can execute commands, manipulate windows, imitate mouse and keyboard movements, and open websites using the victim's browser.
Screenshots of Grandoreiro trojan's admin panel:
Screenshot of ÉSECÈ Group-themed spam email spreading Grandoreiro trojan:
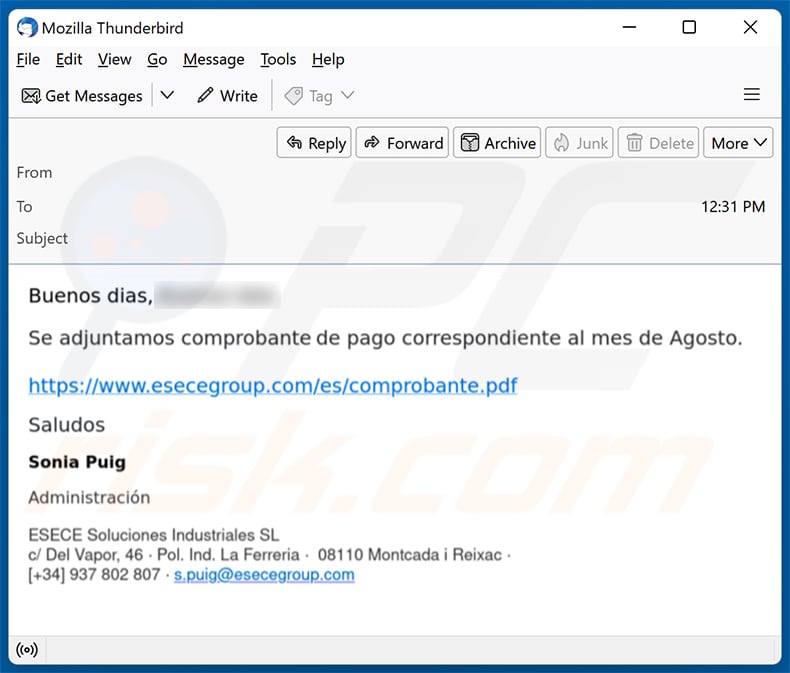
Text presented within:
Buenos dias, -
Se adjuntamos comprobante de pago correspondiente al mes de Agosto.
-
Saludos
Sonia Puig
Administración
ESECE Soluciones Industriales SL
c/ Vel Vapor, 46 Pol. Ind. La Ferreria 08110 Montcada i Reixac
+[34] 937 802 807 s.puig@esecegroup.com
Screenshot of Claro telecommunications-themed spam email spreading Grandoreiro trojan:
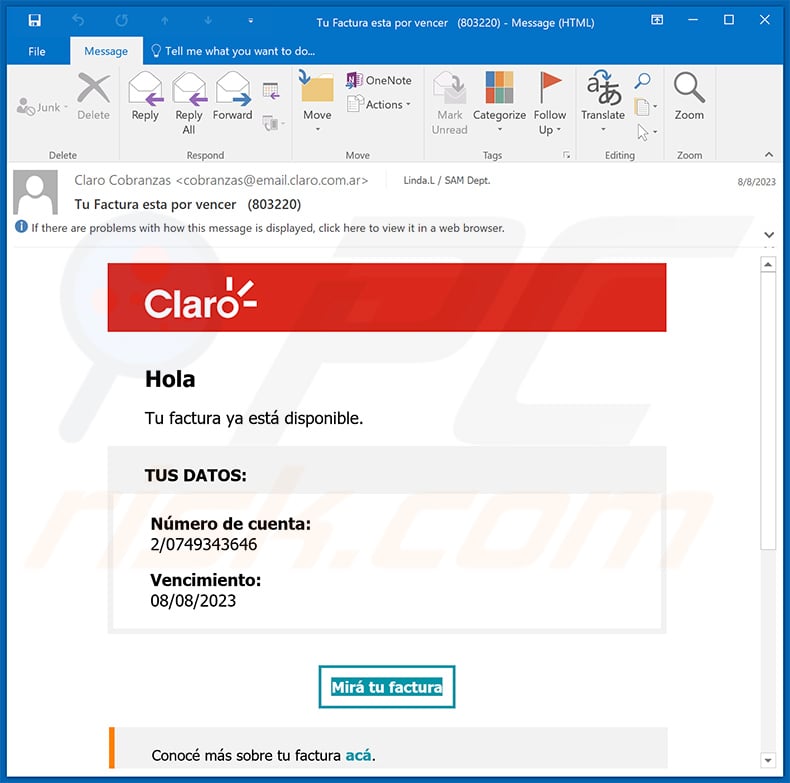
Text presented within:
Subject: Tu Factura esta por vencer (803220)
Hola
Tu factura ya está disponible.
TUS DATOS:
Número de cuenta:
2/0749343646Vencimiento:
08/08/2023Mirá tu factura
Conocé más sobre tu factura acá.
Ante las estafas, estemos alerta! Conocé los tips para cuidarte de los perfiles falsos y las estafas telefónicas acá.
Update February 8, 2024 – threat actors linked to the Grandoreiro banking trojan have been arrested. The Federal Police of Brazil relied on key information provided by and cooperation from the Spanish National Police, Interpol, ESET, and Caixa Bank for the investigation. This resulted in thirteen acts of search and seizure and five arrests in five Brazilian states. More information on these developments can be found in an article by Bill Toulas on the Bleeping Computer website.
Update May 21, 2024 - Grandoreiro has reappeared in a phishing campaign spanning over 60 countries. It now targets accounts from approximately 1,500 banks and is probably being sold as Malware-as-a-service to other cybercriminals. It is known that Grandoreiro is now targeting not only Spanish-speaking regions but also English-speaking countries.
Also, the malware has various improvements, such as an updated string decryption algorithm, updates to the domain generation algorithm, and new features targeting Microsoft Outlook clients and establishing persistence via registry keys.
Moreover, Grandoreiro currently has enhanced capabilities, such as targeting bank applications, cryptocurrency wallets, remote control, file manipulation, keylogging, and browser manipulation via JavaScript commands. Also, Grandoreiro can profile victims to decide whether to execute and avoid specific countries and system configurations.
Threat actors have been observed delivering Grandoreiro via phishing emails posing as government entities, mainly tax agencies and revenue services. These emails, tailored to the recipient's language, urge recipients to click links to view invoices or perform other actions.
In these campaigns, clicking the provided links leads to an image of a PDF designed to initiate the download of a ZIP file containing an executable file that functions as the loader for Grandoreiro.
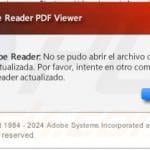
Update March 13, 2025 - Cyber criminals have been recently spreading Grandoreiro trojan via malicious sites presenting users with a PDF file download. In reality, the download link leads to a ZIP file with a VBS script within. Once executed, the script shows a fake Adobe Reader/Acrobat window and injects malware.
Screenshots of the websites as well as fake Adobe Reader/Acrobat pop-ups:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Grandoreiro?
- STEP 1. Manual removal of Grandoreiro malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Grandoreiro malware, should I format my storage device to get rid of it?
No, Grandoreiro's removal does not necessitate such drastic measures.
What are the biggest issues that Grandoreiro malware can cause?
Grandoreiro is classified as a banking trojan. Hence, this malware primarily targets information relating to online banking. However, it can also extract other sensitive data and add the victims' computers to a botnet. Therefore, this trojan can cause decreased system performance, severe privacy issues, significant financial losses, and identity theft.
What is the purpose of Grandoreiro malware?
Since Grandoreiro is a banking trojan - it is likely used to generate revenue, which is the purpose of most malicious programs. However, malware can also be used to amuse cyber criminals, disrupt processes (e.g., websites, services, companies, institutions, etc.), carry out personal vendettas, launch politically/geopolitically motivated attacks, and so on.
How did Grandoreiro malware infiltrate my computer?
Malware is primarily spread through drive-by (stealthy and deceptive) downloads, malicious attachments and links in spam emails/messages, online scams, untrustworthy download sources (e.g., unofficial and freeware sites, Peer-to-Peer sharing networks, etc.), illegal program activation tools ("cracks"), and fake updates. Some malicious programs are also capable of self-proliferating via local networks and removable storage devices (e.g., external hard drives, USB flash drives, etc.).
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is designed to detect and eliminate threats. It is capable of removing nearly all known malware infections. It must be mentioned that high-end malicious software typically hides deep within systems - therefore, running a complete system scan is crucial.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate





▼ Show Discussion