How to recognize phshing scams like INTERNATIONAL MONETARY FUND (IMF)?
Phishing/ScamAlso Known As: INTERNATIONAL MONETARY FUND (IMF) spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is INTERNATIONAL MONETARY FUND (IMF) email scam?
The International Monetary Fund (IMF) is a legitimate financial institution, an international organization that promotes global economic growth, reduces poverty, encourages international trade. There is more than one email scam variant claiming to be authored by IMF officials.
Typically, scammers behind these bogus emails attempt to trick recipients into contacting the IMF for issuance of some form of approval, to receive a donation, or for other matters. In any case, the purpose of these emails is to deceive recipients into providing personal information or transferring money.
INTERNATIONAL MONETARY FUND (IMF) scam in detail
Scammers often use the names of real people, use actual company logos, addresses, etc., to make their hoaxes seem real. This is an email scam claiming to be a message from Kristalina Georgieva, the managing director of the International Monetary Fund.
Scammers behind it attempt to trick recipients into believing that they were selected to receive a donation from the IMF and into contacting them for more information. It is likely that after contacting the scammers, recipients will be asked to send personal banking details (such as credit card details), or make a small payment like a "transaction fee".
Typically, when scammers successfully obtain credit card details and other personal information, they use it to make fraudulent purchases and transactions, steal identities, hijack personal accounts, etc., or sell it to third parties (other cyber criminals).
Therefore, recipients who fall for these scams suffer monetary loss, cannot access their personal accounts, become victims of identity theft, and encounter other serious problems. This and other similar emails are simply scams - they should be ignored and reported.
| Name | INTERNATIONAL MONETARY FUND (IMF) Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Recipient has been selected to receive a donation |
| Disguise | A letter from the managing director of the International Monetary Fund (IMF) |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Phishing scams in general
Plentu of email scams are circulating the internet. Some examples are "U.S Army Special Operations Command Consignment Email Scam", "EMPLOYEE BENEFITS Email Scam", and "Synchronize Mail Error Email Scam". They are often disguised as official messages from existing, legitimate companies or other entities, and ask for personal information, payments.
In fact, the emails can be used to deliver malware. In such cases, emails contain malicious links or attachments. Their main purpose is to deceive recipients into opening malicious files.
How do spam campaigns infect computers?
Malware (including ransomware) is usually distributed via malspam campaigns, unofficial software activation ('cracking') tools, Trojans, dubious file/software download sources, and fake software updating tools.
When cyber criminals attempt to distribute malware via malspam campaigns, they send emails that contain malicious attachments or download links for malicious files. Typically, they disguise their emails as official and important. If recipients open the attached file (or a file downloaded via a website link), they cause installation of malicious software.
Cyber criminals commonly attach executable files (.exe), archive files such as RAR, ZIP, PDF documents, JavaScript files and Microsoft Office documents to their emails. Software 'cracking' tools supposedly activate licensed software illegally (bypass activation), however, they often install malicious programs and do not activate any legitimate installed software.
Trojans are other rogue programs that can cause chain infections. I.e., when a Trojan is installed on the operating system, it can install additional malware.
Free file hosting websites, freeware download websites, Peer-to-Peer networks (e.g., torrent clients, eMule), unofficial websites, and third party downloaders are examples of other sources that are used to distribute malware. Cyber criminals disguise malicious files as legitimate and regular. When users download and open them, they inadvertently infect their computers with malware.
Fake software updating tools install malicious software rather than updates/fixes for installed programs, or they exploit bugs/flaws of outdated software that is installed on the operating system.
How to avoid installation of malware
Download software and files from official websites and via direct links. It is not safe to use torrent clients, eMule (or other Peer-to-Peer networks), third party downloaders, unofficial websites or other sources of this kind.
Avoid third party installers. Check "Advanced", "Custom" and other settings, and decline offers to download or install unwanted software. Do not click ads that are displayed on dubious websites, since they can open other untrusted websites or even cause unwanted downloads and installations.
Remove any unwanted, suspicious applications (extensions, add-ons, and plug-ins) that are installed on the browser. The same should be applied to programs of this kind that are installed on the operating system.
Regularly scan your computer with reputable antivirus or anti-spyware software and keep this software up to date.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
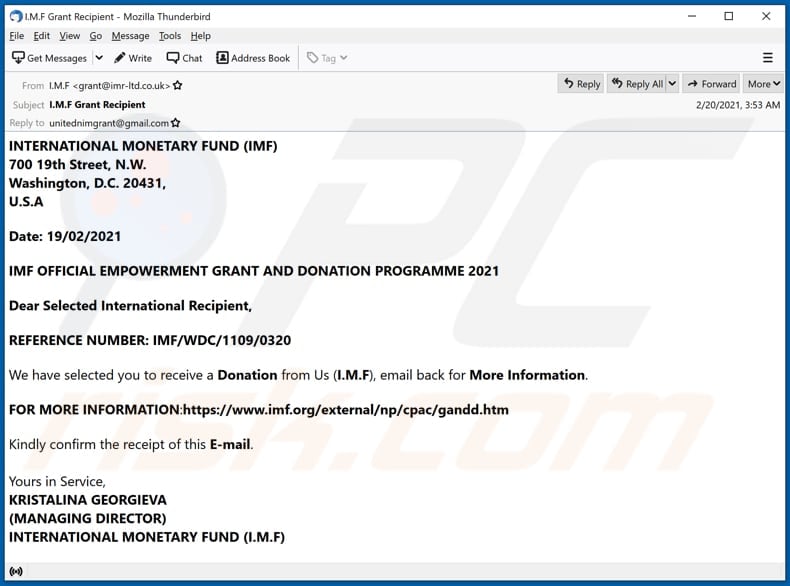
Text presented in the email:
Subject: I.M.F Grant Recipient
INTERNATIONAL MONETARY FUND (IMF)
700 19th Street, N.W.
Washington, D.C. 20431,
U.S.A
Date: 19/02/2021
IMF OFFICIAL EMPOWERMENT GRANT AND DONATION PROGRAMME 2021
Dear Selected International Recipient,
REFERENCE NUMBER: IMF/WDC/1109/0320
We have selected you to receive a Donation from Us (I.M.F), email back for More Information.
FOR MORE INFORMATION:hxxps://www.imf.org/external/np/cpac/gandd.htm
Kindly confirm the receipt of this E-mail.
Yours in Service,
KRISTALINA GEORGIEVA
(MANAGING DIRECTOR)
INTERNATIONAL MONETARY FUND (I.M.F)
Other examples of INTERNATIONAL MONETARY FUND-themed spam emails:
Sample 1:
Text presented within:
Subject: Directive from Dr Kristalina Georgieva the M D IMF, Please Contact Mr. Wilbur Autry for further Directives on your fund payment.
INTERNATIONAL MONETARY FUND (HQ1)
700 19th Street, N.W., Washington, D.C.
20431.
Email: wilburautry.imf@aol.com
Date: 4/5/2021To the knowledge of the Beneficiary.
Re Payment of $5.2m
2021 UNPAID FUND RECOVERED LETTER
In our efforts to foster global monetary cooperation secures financial
stability and facilitates individual company economic growth.The IMF through our international monitoring network has recovered
your UNPAID FUND $5.2m that has been on hold.We hereby advise you to reconfirm to this office officially if you are
the person that instructed Mr. RAVIS RAY LUNN of America to claim and
receive the payment on your behalf before we send your fund transfer
instruction to one of our approved paying banks to contact you for the
release of your fund.For your information we have the following banks as our
nominated/approved payment banks, Lloyd’s Bank London, Citibank New
York and CMB WING LUNG Bank Hong Kong.Please, Re-confirm as follows
(1) Your Full Name........?
(2) Full Residential Address: (P.O.BOX NOT ALLOWED)?
(3) Country/State..........?
(4) Beneficiary Amount?
(5) Direct and Current Phone?
(6) Passport identification?Please you are also required to clarify the following immediately:
1. IS Williams Rogers your local representative?
2. Did you broker your fund to one Mr. TRAVIS RAY LUNN of America to claim?
And receive the payment on your behalf?3. Did you sign any “Deed of Assignment” in his favor, thereby making
him the current beneficiary with the following account details to
receive your fund?Mr. TRAVIS RAY LUNN
Address 55601 SWAN RD.SUNRIVER BEND, OREGON 97707
USA
Account Name: TRAVIS RAY LUNN
Bank Name: WELLS FARGO
Bank Address: 450 NE WINDY KNOLLS DR BEND,OR,97701
Beneficiary Account Number: 8210526748
Swift Code:WFBIUS6S
Routing Number for wire Transfer: 12100024Please confirm so that we can proceed with your fund payment as we
don’t anticipate any further delay.Contact Mr. Wilbur Autry.
Operation department for further Directive.
Email: wilburautry.imf@aol.comThank you and have a nice day.
Regards
Dr Ms. Kristalina Georgieva
Managing Director
IMF
Sample 2:
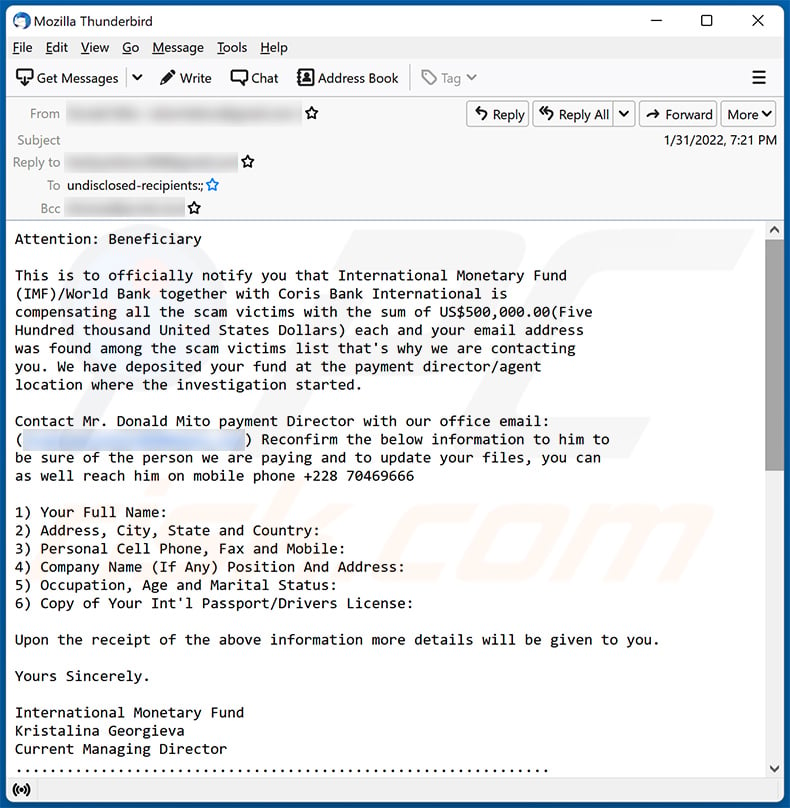
Text presented within:
Attention: Beneficiary
This is to officially notify you that International Monetary Fund
(IMF)/World Bank together with Coris Bank International is
compensating all the scam victims with the sum of US$500,000.00(Five
Hundred thousand United States Dollars) each and your email address
was found among the scam victims list that's why we are contacting
you. We have deposited your fund at the payment director/agent
location where the investigation started.Contact Mr. Donald Mito payment Director with our office email:
(**********) Reconfirm the below information to him to
be sure of the person we are paying and to update your files, you can
as well reach him on mobile phone +228 704696661) Your Full Name:
2) Address, City, State and Country:
3) Personal Cell Phone, Fax and Mobile:
4) Company Name (If Any) Position And Address:
5) Occupation, Age and Marital Status:
6) Copy of Your Int'l Passport/Drivers License:Upon the receipt of the above information more details will be given to you.
Yours Sincerely.
International Monetary Fund
Kristalina Georgieva
Current Managing Director
...............................................................Attenzione: Beneficiario
Questo per informarti ufficialmente che il Fondo Monetario
Internazionale (FMI)/Banca Mondiale insieme a Coris Bank International
sta risarcindo tutte le vittime della truffa con la somma di US $
500.000,00 (cinquecentomila dollari statunitensi) ciascuna e il tuo
indirizzo email è stato trovato tra i elenco delle vittime della
truffa ecco perché ti stiamo contattando. Abbiamo depositato il tuo
fondo presso il direttore dei pagamenti/la sede dell'agente in cui è
iniziata l'indagine.Contatta il Direttore dei pagamenti Mr. Donald Mito con la nostra
email di ufficio: (**********) Riconfermagli le
informazioni di seguito per essere sicuro della persona che stiamo
pagando e per aggiornare i tuoi file, puoi anche raggiungerlo sul
cellulare + 228 704696661) Il tuo nome completo:
2) Indirizzo, Città, Stato e Paese:
3) Cellulare personale, Fax e Mobile:
4) Nome dell'azienda (se presente) Posizione e indirizzo:
5) Professione, età e stato civile:
6) Copia del tuo passaporto internazionale/patente di guida:Al ricevimento delle informazioni di cui sopra ti verranno forniti
maggiori dettagli.Cordiali saluti.
Fondo monetario internazionale
Kristalina Georgieva
Attuale amministratore delegato
Sample 3:
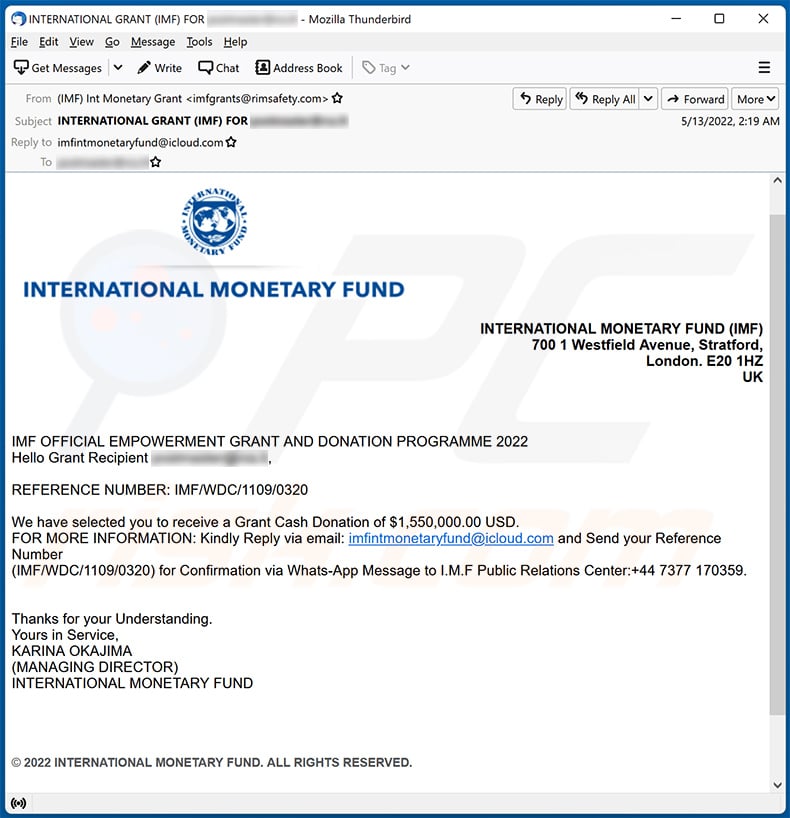
Text presented within:
Subject: INTERNATIONAL GRANT (IMF) FOR -
INTERNATIONAL MONETARY FUND (IMF)
700 1 Westfield Avenue, Stratford,
London. E20 1HZ
UK
IMF OFFICIAL EMPOWERMENT GRANT AND DONATION PROGRAMME 2022
Hello Grant Recipient -,
REFERENCE NUMBER: IMF/WDC/1109/0320
We have selected you to receive a Grant Cash Donation of $1,550,000.00 USD.
FOR MORE INFORMATION: Kindly Reply via email: imfintmonetaryfund@icloud.com and Send your Reference Number
(IMF/WDC/1109/0320) for Confirmation via Whats-App Message to I.M.F Public Relations Center:+44 7377 170359.
Thanks for your Understanding.
Yours in Service,
KARINA OKAJIMA
(MANAGING DIRECTOR)
INTERNATIONAL MONETARY FUND© 2022 INTERNATIONAL MONETARY FUND. ALL RIGHTS RESERVED.
Sample 4:
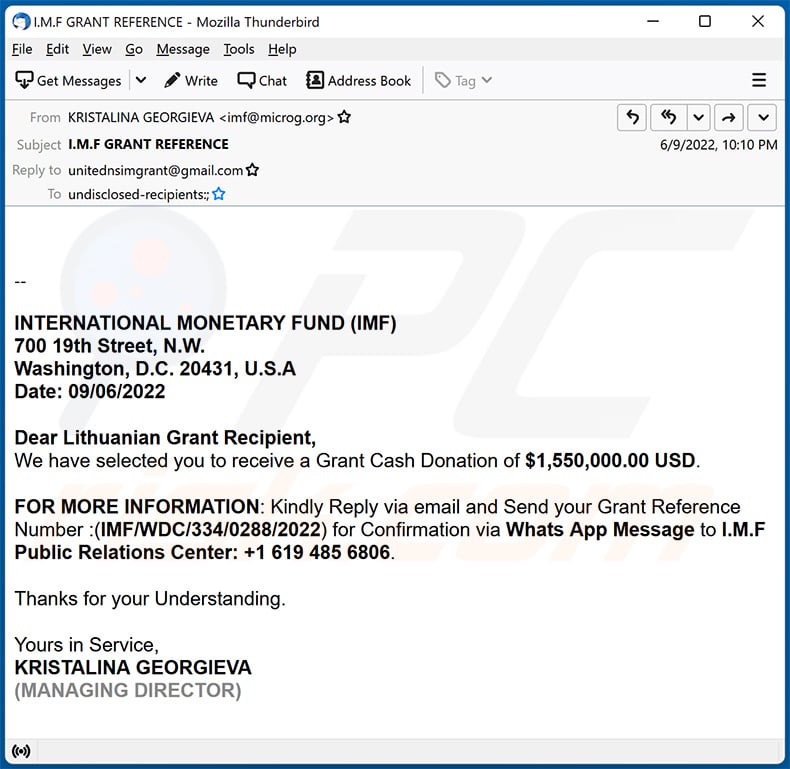
Text presented within:
Subject: I.M.F GRANT REFERENCE
--INTERNATIONAL MONETARY FUND (IMF)
700 19th Street, N.W.
Washington, D.C. 20431, U.S.A
Date: 09/06/2022Dear Lithuanian Grant Recipient,
We have selected you to receive a Grant Cash Donation of $1,550,000.00 USD.FOR MORE INFORMATION: Kindly Reply via email and Send your Grant Reference Number :(IMF/WDC/334/0288/2022) for Confirmation via Whats App Message to I.M.F Public Relations Center: +1 619 485 6806.
Thanks for your Understanding.
Yours in Service,
KRISTALINA GEORGIEVA
(MANAGING DIRECTOR)
Sample 5:
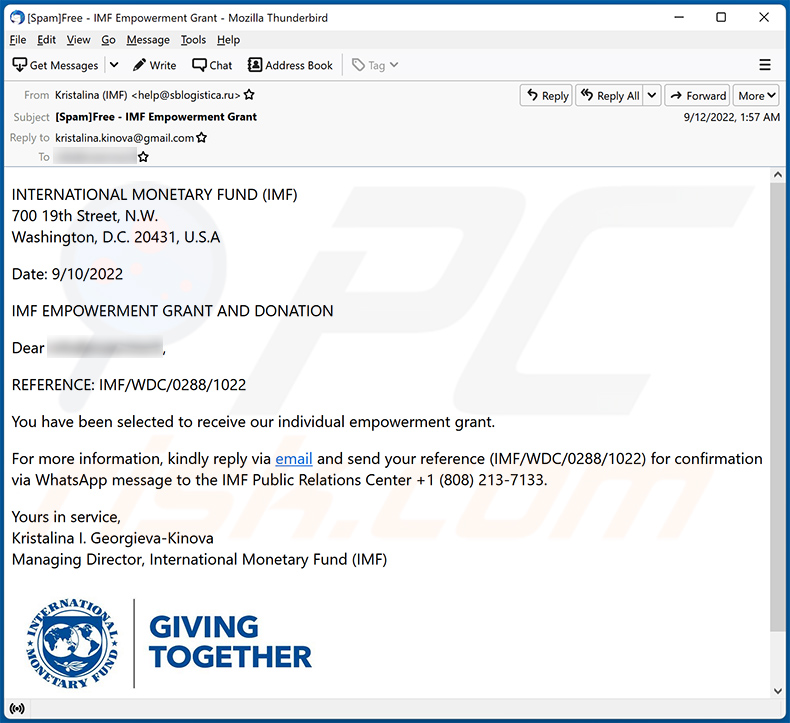
Text presented within:
Subject: [Spam]Free - IMF Empowerment Grant
INTERNATIONAL MONETARY FUND (IMF)
700 19th Street, N.W.
Washington, D.C. 20431, U.S.ADate: 9/10/2022
IMF EMPOWERMENT GRANT AND DONATION
Dear -,
REFERENCE: IMF/WDC/0288/1022
You have been selected to receive our individual empowerment grant.
For more information, kindly reply via email and send your reference (IMF/WDC/0288/1022) for confirmation via WhatsApp message to the IMF Public Relations Center +1 (808) 213-7133.
Yours in service,
Kristalina I. Georgieva-Kinova
Managing Director, International Monetary Fund (IMF)
Sample 6:
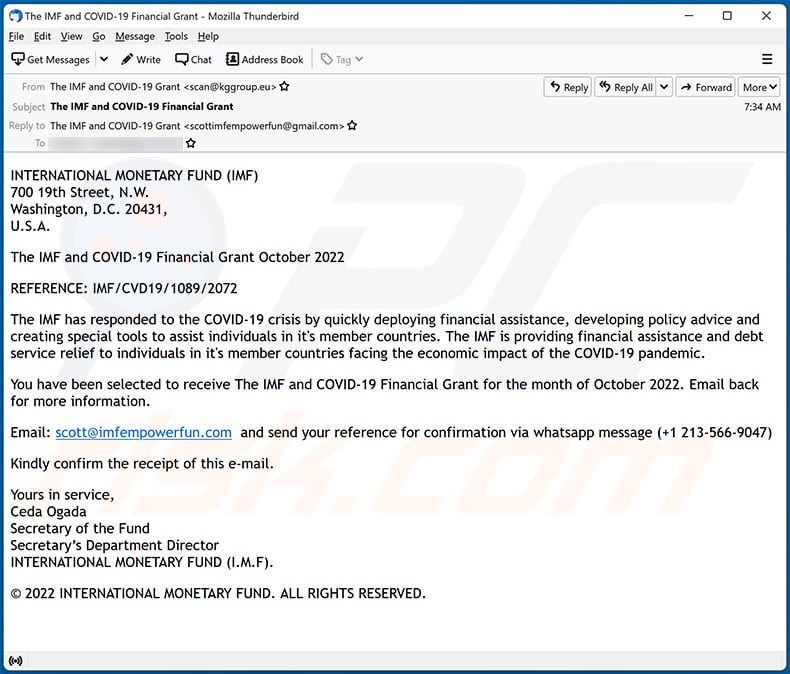
Text presented within:
INTERNATIONAL MONETARY FUND (IMF)
700 19th Street, N.W.
Washington, D.C. 20431,
U.S.A.The IMF and COVID-19 Financial Grant October 2022
REFERENCE: IMF/CVD19/1089/2072
The IMF has responded to the COVID-19 crisis by quickly deploying financial assistance, developing policy advice and creating special tools to assist individuals in it's member countries. The IMF is providing financial assistance and debt service relief to individuals in it's member countries facing the economic impact of the COVID-19 pandemic.
You have been selected to receive The IMF and COVID-19 Financial Grant for the month of October 2022. Email back for more information.
Email: scott@imfempowerfun.com and send your reference for confirmation via whatsapp message (+1 213-566-9047)
Kindly confirm the receipt of this e-mail.
Yours in service,
Ceda Ogada
Secretary of the Fund
Secretary’s Department Director
INTERNATIONAL MONETARY FUND (I.M.F).© 2022 INTERNATIONAL MONETARY FUND. ALL RIGHTS RESERVED.
Sample 7:
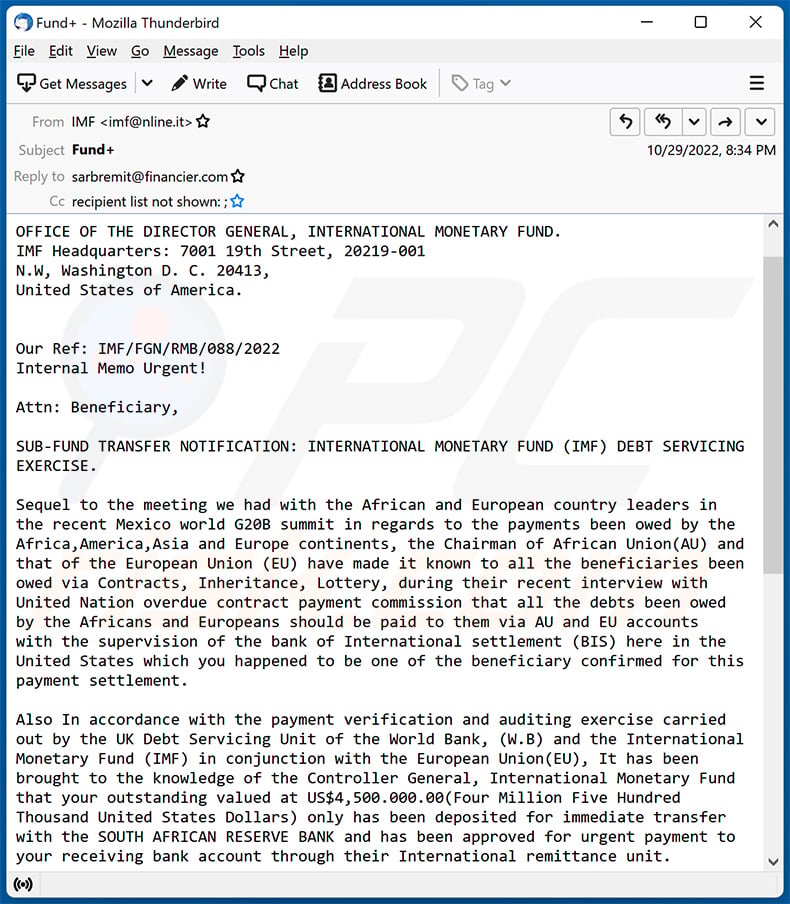
Text presented within:
Subject: Fund+
OFFICE OF THE DIRECTOR GENERAL, INTERNATIONAL MONETARY FUND.
IMF Headquarters: 7001 19th Street, 20219-001
N.W, Washington D. C. 20413,
United States of America.
Our Ref: IMF/FGN/RMB/088/2022
Internal Memo Urgent!Attn: Beneficiary,
SUB-FUND TRANSFER NOTIFICATION: INTERNATIONAL MONETARY FUND (IMF) DEBT SERVICING
EXERCISE.Sequel to the meeting we had with the African and European country leaders in
the recent Mexico world G20B summit in regards to the payments been owed by the
Africa,America,Asia and Europe continents, the Chairman of African Union(AU) and
that of the European Union (EU) have made it known to all the beneficiaries been
owed via Contracts, Inheritance, Lottery, during their recent interview with
United Nation overdue contract payment commission that all the debts been owed
by the Africans and Europeans should be paid to them via AU and EU accounts
with the supervision of the bank of International settlement (BIS) here in the
United States which you happened to be one of the beneficiary confirmed for this
payment settlement.Also In accordance with the payment verification and auditing exercise carried
out by the UK Debt Servicing Unit of the World Bank, (W.B) and the International
Monetary Fund (IMF) in conjunction with the European Union(EU), It has been
brought to the knowledge of the Controller General, International Monetary Fund
that your outstanding valued at US$4,500.000.00(Four Million Five Hundred
Thousand United States Dollars) only has been deposited for immediate transfer
with the SOUTH AFRICAN RESERVE BANK and has been approved for urgent payment to
your receiving bank account through their International remittance unit.We issue this last notification to you on this development since we were unable
to reach you with the payment Details, as you are advised to contact the SOUTH
AFRICAN RESERVE BANK, International Remittance Unit.Attn: Mr. Fred Malusi on Direct Tel: +27 748476701 Email:
fredmalusi@executivemail.co.za, with this payment Ref N0:BBYUK/REG1958755 for
the transfer conclusion.This avenue has been created by the United Nations (EU) & (AU) on
Foreign debt Reconciliation Commission to offset all the outstanding foreign
payments on-hold in order to rehabilitate the lost dignity of the EU, AU &
Others.The international Monetary Fund (IMF) remains communicated to our
financial principles through the above contact details. We hope you will benefit
from our team of experts. We assure you the best of our services at all times
assuring you of this payment transfer legitimacy.Congratulation,
Yours Faithfully,
Kristalina Georgieva(Managing Director (IMF).
Sample 8:
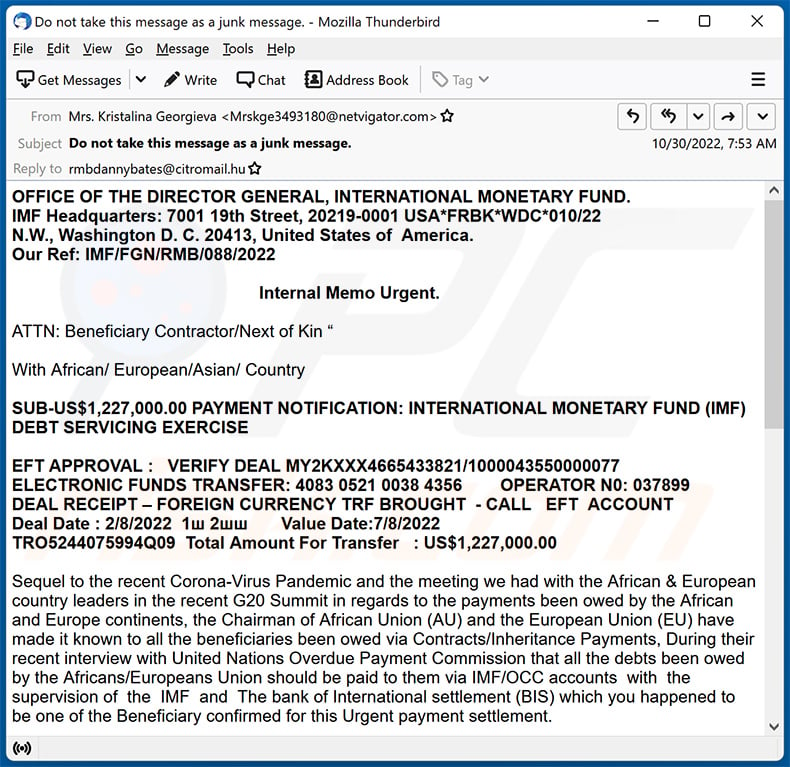
Text presented within:
Subject: Do not take this message as a junk message.
OFFICE OF THE DIRECTOR GENERAL, INTERNATIONAL MONETARY FUND.
IMF Headquarters: 7001 19th Street, 20219-0001 USA*FRBK*WDC*010/22
N.W., Washington D. C. 20413, United States of America.
Our Ref: IMF/FGN/RMB/088/2022
Internal Memo Urgent.
ATTN: Beneficiary Contractor/Next of Kin “
With African/ European/Asian/ Country
SUB-US$1,227,000.00 PAYMENT NOTIFICATION: INTERNATIONAL MONETARY FUND (IMF) DEBT SERVICING EXERCISE
EFT APPROVAL : VERIFY DEAL MY2KXXX4665433821/1000043550000077
ELECTRONIC FUNDS TRANSFER: 4083 0521 0038 4356 OPERATOR N0: 037899
DEAL RECEIPT – FOREIGN CURRENCY TRF BROUGHT - CALL EFT ACCOUNT
Deal Date : 2/8/2022 1ш 2шш Value Date:7/8/2022
TRO5244075994Q09 Total Amount For Transfer : US$1,227,000.00
Sequel to the recent Corona-Virus Pandemic and the meeting we had with the African & European country leaders in the recent G20 Summit in regards to the payments been owed by the African and Europe continents, the Chairman of African Union (AU) and the European Union (EU) have made it known to all the beneficiaries been owed via Contracts/Inheritance Payments, During their recent interview with United Nations Overdue Payment Commission that all the debts been owed by the Africans/Europeans Union should be paid to them via IMF/OCC accounts with the supervision of the IMF and The bank of International settlement (BIS) which you happened to be one of the Beneficiary confirmed for this Urgent payment settlement.
Also In accordance with the payment verifications and auditing exercise carried out by the African Debt Servicing Unit and the International Monetary Fund (IMF) in conjunction with the African and European Union (EU), it has been brought to the knowledge of the Comptroller General, International Monetary Fund that your outstanding payment Compensation valid US$1,227,000.00 (One Million, Two Hundred & Twenty Seven Thousand United States Dollars) only has been deposited for immediate Payment with the South African Rand Merchant Bank and has been approved for urgent Online payment transfer in your name immediately.
We issue this last notification to you on this development Since We Were Unable To Reach You With The Payment Details, you are advised to contact the Rand Merchant Bank south Africa, International Remittance Unit, 'Attn: Mr. James Formby on Direct Tel:+27-710927585 email: ( rmbdannybates@citromail.hu ) with payment Ref: MY2KXX4665433821/1000043550000077 for the Payment conclusion.
This avenue has been created by the United Nations (EU) & (AU) on Foreign debt Reconciliation Commission to offset all the outstanding foreign payments on-hold in order to rehabilitate the lost dignity of the EU & AU African states.
The international Monetary Funds (IMF) remains communicated to our financial principles through the above contact details. We hope you will benefit from our team of experts. We assure you the best of our services at all times assuring you of this payment transfer conclusion.
PAYMENT REFN0 : YUK/REG1958755Yours Faithfully,
Mrs. Kristalina Georgieva
Managing Director
International Monetary Fund
Washington, D.C. 20431, U.S.A
Sample 9:
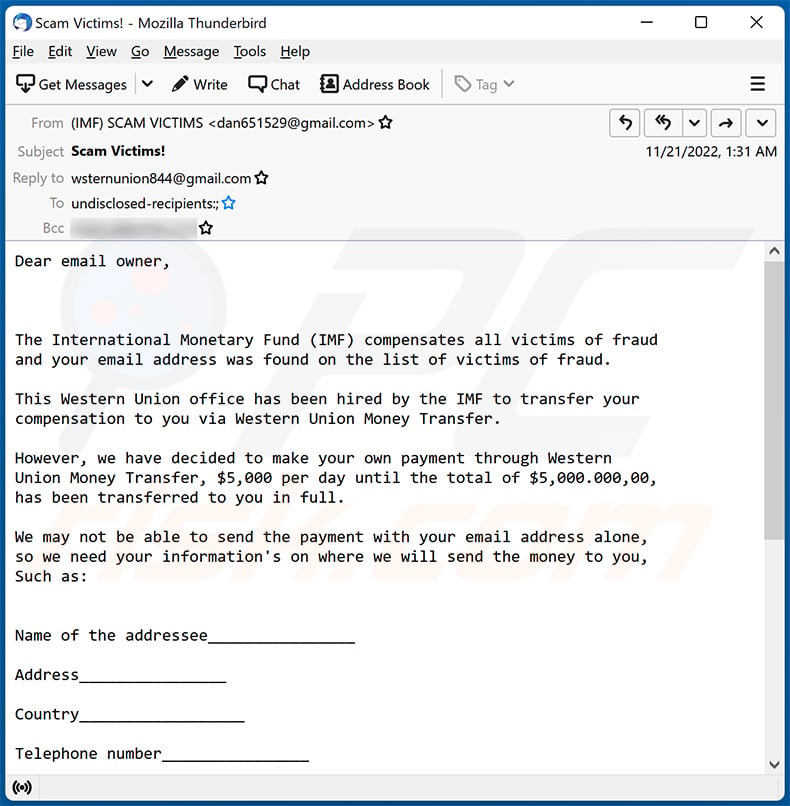
Text presented within:
Subject: Scam Victims!
Dear email owner,
The International Monetary Fund (IMF) compensates all victims of fraud
and your email address was found on the list of victims of fraud.This Western Union office has been hired by the IMF to transfer your
compensation to you via Western Union Money Transfer.However, we have decided to make your own payment through Western
Union Money Transfer, $5,000 per day until the total of $5,000.000,00,
has been transferred to you in full.We may not be able to send the payment with your email address alone,
so we need your information's on where we will send the money to you,
Such as:Name of the addressee________________
Address________________
Country__________________
Telephone number________________
Attached copy of your ID_____________
Age ________________________
We will start the transfer once we have received your Information:
Contact E-mail: (wsternunion844@gmail.com)Faithfully,
Mr. Anthony Duru1 (605) 453-2941
Director of Western Union Money Transfer
Sample 10:
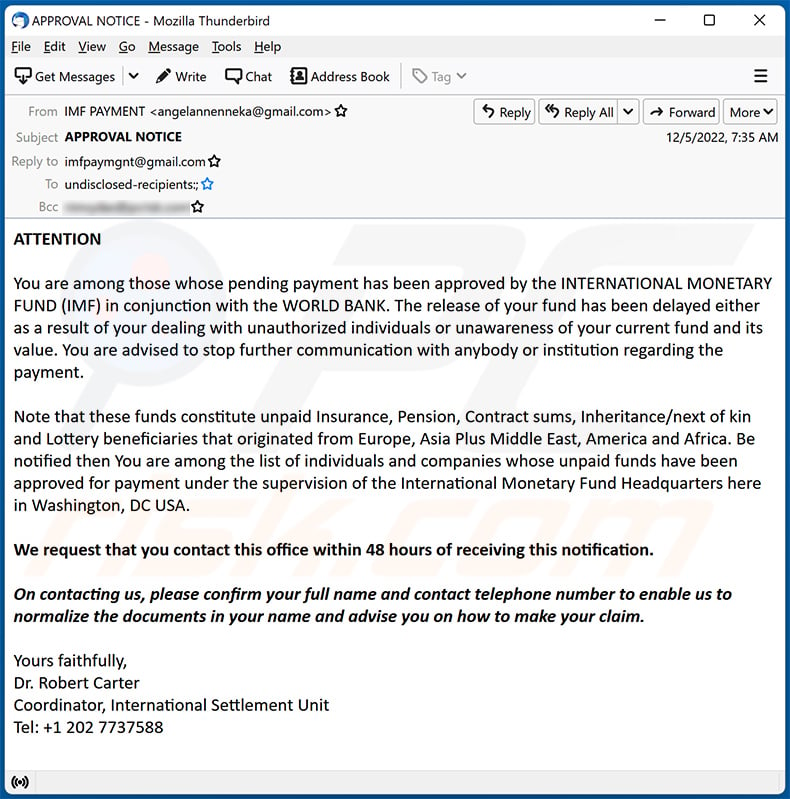
Text presented within:
Subject: APPROVAL NOTICE
ATTENTIONYou are among those whose pending payment has been approved by the INTERNATIONAL MONETARY FUND (IMF) in conjunction with the WORLD BANK. The release of your fund has been delayed either as a result of your dealing with unauthorized individuals or unawareness of your current fund and its value. You are advised to stop further communication with anybody or institution regarding the payment.
Note that these funds constitute unpaid Insurance, Pension, Contract sums, Inheritance/next of kin and Lottery beneficiaries that originated from Europe, Asia Plus Middle East, America and Africa. Be notified then You are among the list of individuals and companies whose unpaid funds have been approved for payment under the supervision of the International Monetary Fund Headquarters here in Washington, DC USA.
We request that you contact this office within 48 hours of receiving this notification.
On contacting us, please confirm your full name and contact telephone number to enable us to normalize the documents in your name and advise you on how to make your claim.
Yours faithfully,
Dr. Robert Carter
Coordinator, International Settlement Unit
Tel: +1 202 7737588
Sample 11:
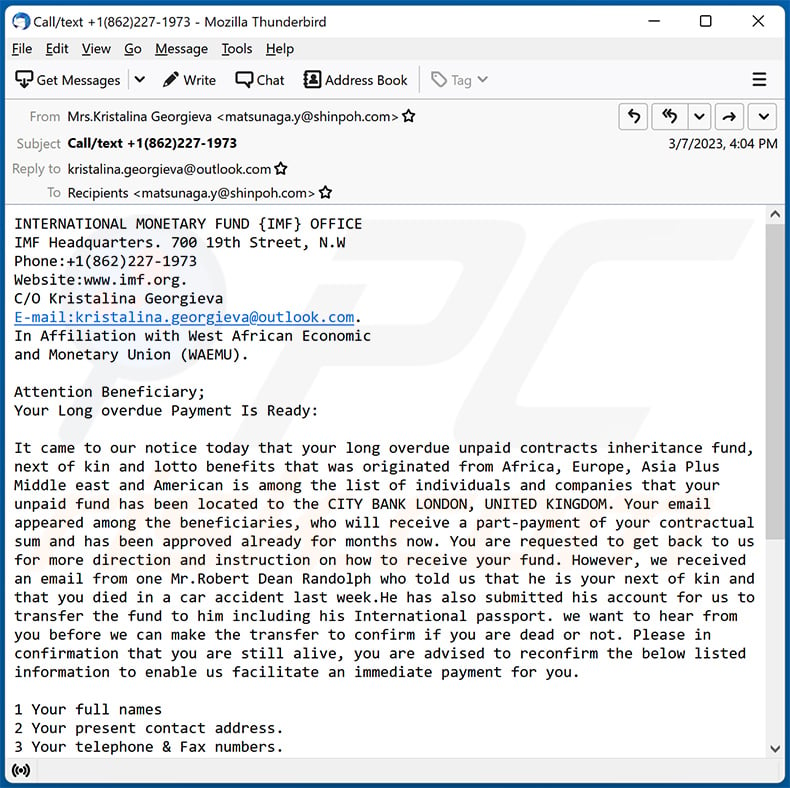
Text presented within:
Subject: Call/text +1(862)227-1973
INTERNATIONAL MONETARY FUND {IMF} OFFICE
IMF Headquarters. 700 19th Street, N.W
Phone:+1(862)227-1973
Website:www.imf.org.
C/O Kristalina Georgieva
E-mail:kristalina.georgieva@outlook.com.
In Affiliation with West African Economic
and Monetary Union (WAEMU).Attention Beneficiary;
Your Long overdue Payment Is Ready:It came to our notice today that your long overdue unpaid contracts inheritance fund, next of kin and lotto benefits that was originated from Africa, Europe, Asia Plus Middle east and American is among the list of individuals and companies that your unpaid fund has been located to the CITY BANK LONDON, UNITED KINGDOM. Your email appeared among the beneficiaries, who will receive a part-payment of your contractual sum and has been approved already for months now. You are requested to get back to us for more direction and instruction on how to receive your fund. However, we received an email from one Mr.Robert Dean Randolph who told us that he is your next of kin and that you died in a car accident last week.He has also submitted his account for us to transfer the fund to him including his International passport. we want to hear from you before we can make the transfer to confirm if you are dead or not. Please in
confirmation that you are still alive, you are advised to reconfirm the below listed information to enable us facilitate an immediate payment for you.1 Your full names
2 Your present contact address.
3 Your telephone & Fax numbers.
4 Your Occupations/age/sex.
5 Your Private Email Address.
6 Home Equity (Yes or No)
Once again, We apologize to you on behalf Of IMF (International Monetary Fund) for the delays on paying your funds, which according to records in the system had been long overdue. You can contact the IMF director/chairperson Ms. Kristalina Georgieva on her E-mail:(kristalina.georgieva@outlook.com).Yours Sincerely,
Kristalina Georgieva
Chairperson/Director IMF,
IMF Headquarters.700 19th Street, N.W
+1(862)227-1973
www.imf.org.
Sample 12:
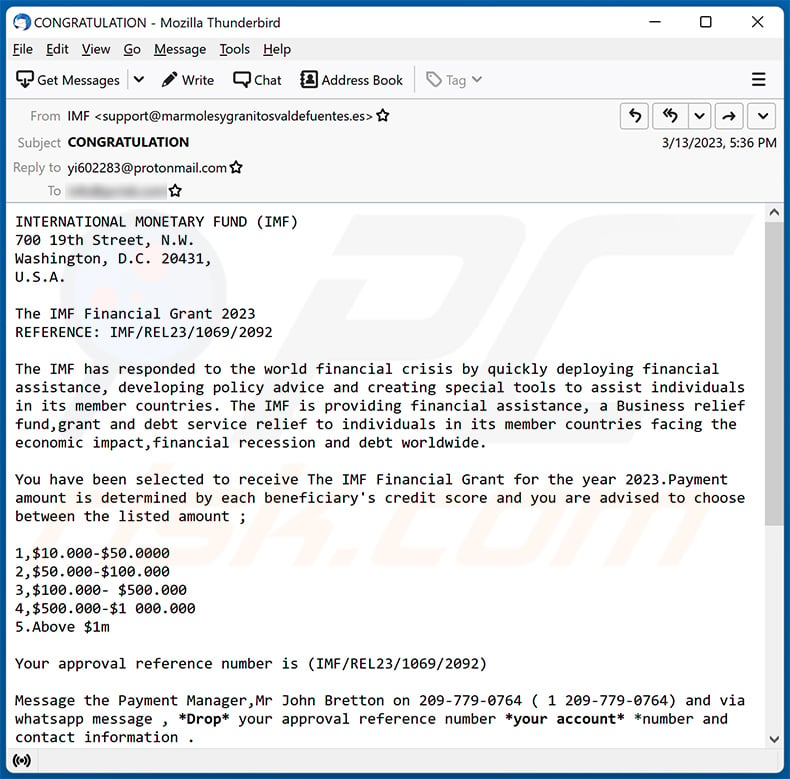
Text presented within:
Subject: CONGRATULATION
INTERNATIONAL MONETARY FUND (IMF)
700 19th Street, N.W.
Washington, D.C. 20431,
U.S.A.The IMF Financial Grant 2023
REFERENCE: IMF/REL23/1069/2092The IMF has responded to the world financial crisis by quickly deploying financial assistance, developing policy advice and creating special tools to assist individuals in its member countries. The IMF is providing financial assistance, a Business relief fund,grant and debt service relief to individuals in its member countries facing the economic impact,financial recession and debt worldwide.
You have been selected to receive The IMF Financial Grant for the year 2023.Payment amount is determined by each beneficiary's credit score and you are advised to choose between the listed amount ;
1,$10.000-$50.0000
2,$50.000-$100.000
3,$100.000- $500.000
4,$500.000-$1 000.000
5.Above $1mYour approval reference number is (IMF/REL23/1069/2092)
Message the Payment Manager,Mr John Bretton on 209-779-0764 ( 1 209-779-0764) and via whatsapp message , *Drop* your approval reference number *your account* *number and contact information .
Send your reference for confirmation via whatsapp message 209-779-0764 ( 1 209-779-0764) with chosen amount and follow winning instructions to receive your fund.
Congratulations.
Yours in service,
Ceda Ogada
Secretary of the Fund
Secretary’s Department Director
INTERNATIONAL MONETARY FUND (I.M.F).© 2023 INTERNATIONAL MONETARY FUND. ALL RIGHTS RESERVED.
Sample 13:
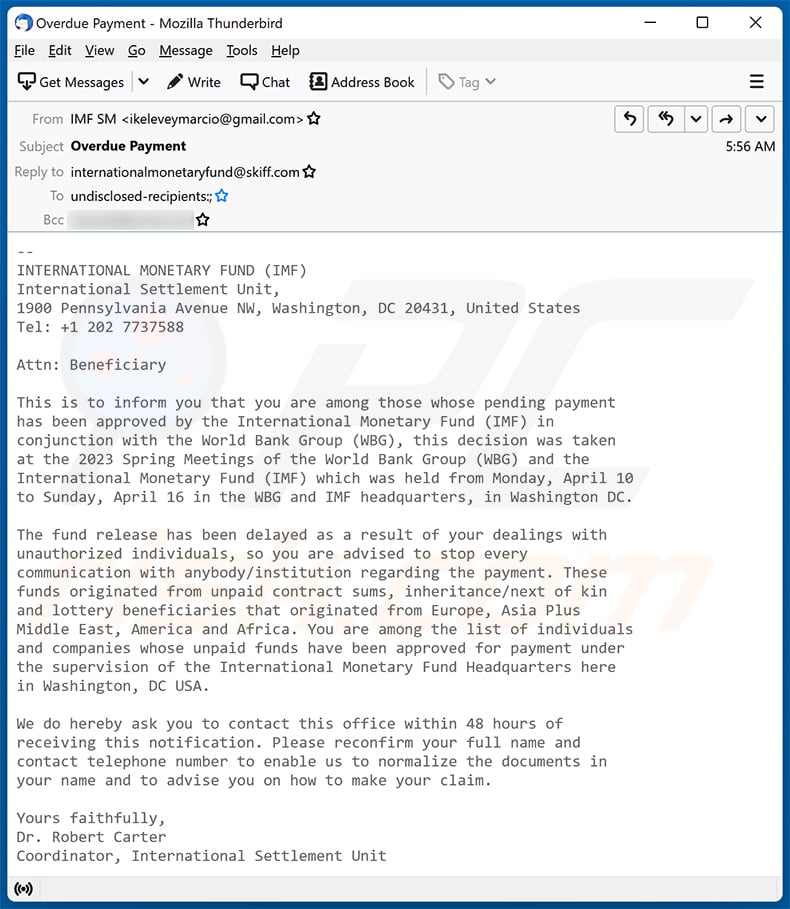
Text presented within:
Subject: Overdue Payment
--
INTERNATIONAL MONETARY FUND (IMF)
International Settlement Unit,
1900 Pennsylvania Avenue NW, Washington, DC 20431, United States
Tel: +1 202 7737588Attn: Beneficiary
This is to inform you that you are among those whose pending payment
has been approved by the International Monetary Fund (IMF) in
conjunction with the World Bank Group (WBG), this decision was taken
at the 2023 Spring Meetings of the World Bank Group (WBG) and the
International Monetary Fund (IMF) which was held from Monday, April 10
to Sunday, April 16 in the WBG and IMF headquarters, in Washington DC.The fund release has been delayed as a result of your dealings with
unauthorized individuals, so you are advised to stop every
communication with anybody/institution regarding the payment. These
funds originated from unpaid contract sums, inheritance/next of kin
and lottery beneficiaries that originated from Europe, Asia Plus
Middle East, America and Africa. You are among the list of individuals
and companies whose unpaid funds have been approved for payment under
the supervision of the International Monetary Fund Headquarters here
in Washington, DC USA.We do hereby ask you to contact this office within 48 hours of
receiving this notification. Please reconfirm your full name and
contact telephone number to enable us to normalize the documents in
your name and to advise you on how to make your claim.Yours faithfully,
Dr. Robert Carter
Coordinator, International Settlement Unit
Sample 14:
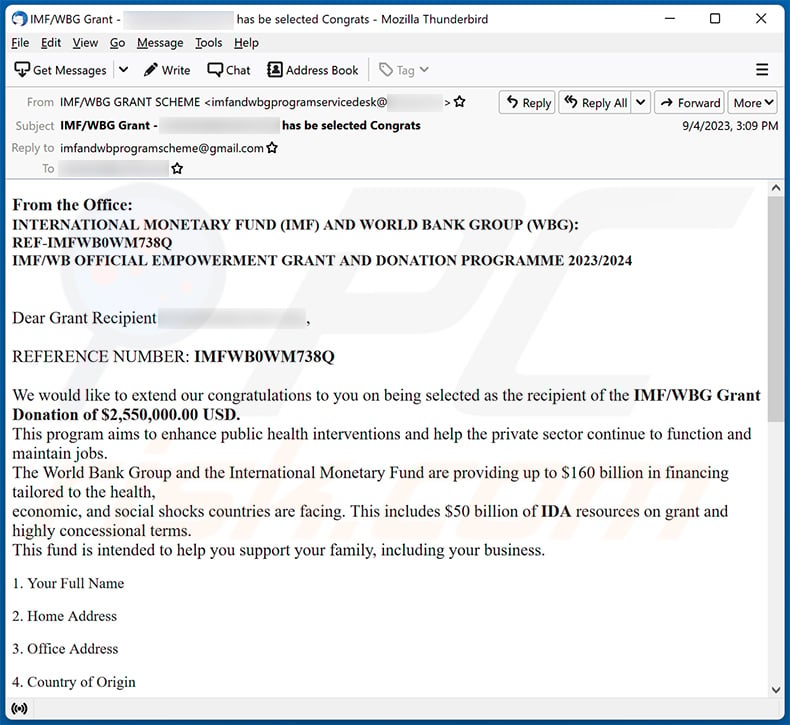
Text presented within:
Subject: IMF/WBG Grant - ******** has be selected Congrats
Dear Grant Recipient ********,
REFERENCE NUMBER: IMFWB0WM738QWe would like to extend our congratulations to you on being selected as the recipient of the IMF/WBG Grant Donation of $2,550,000.00 USD.
This program aims to enhance public health interventions and help the private sector continue to function and maintain jobs.
The World Bank Group and the International Monetary Fund are providing up to $160 billion in financing tailored to the health,
economic, and social shocks countries are facing. This includes $50 billion of IDA resources on grant and highly concessional terms.
This fund is intended to help you support your family, including your business.1. Your Full Name
2. Home Address
3. Office Address
4. Country of Origin
5. Age6. Occupation.
Please if you have received any WORLD BANK GROUP AND INTERNATIONAL MONETARY FUND Intervention fund previously kindly indicate and state the amount.
FOR MORE INFORMATION:
Kindly Reply with Your above Ref No. via email imfandwbprogramscheme@gmail.com.Regards
Yours in Service,
JOSE VELILLA
(GRANT OFFICER)
WORLD BANK GROUP AND INTERNATIONAL MONETARY FUND
Sample 15:
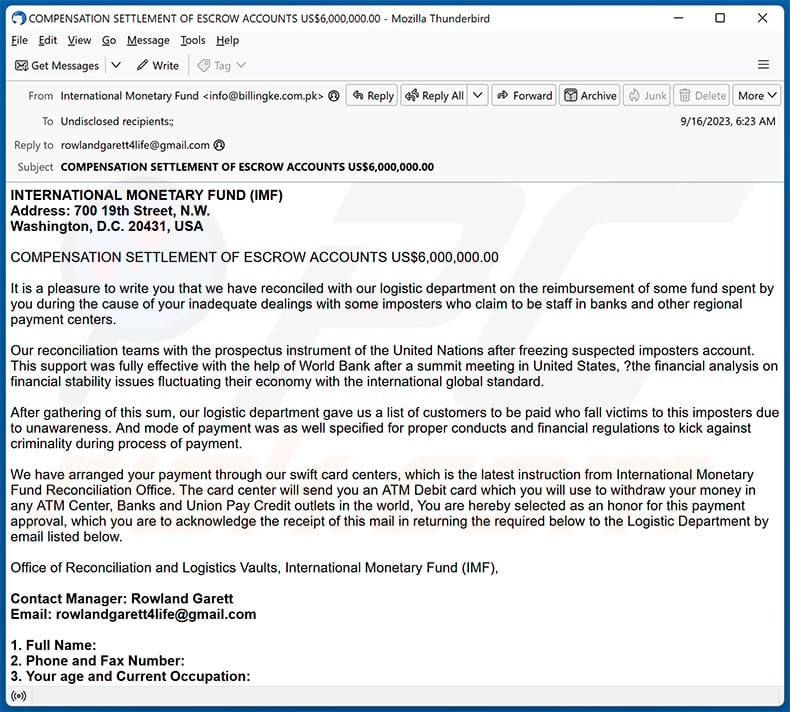
Text presented within:
Subject: COMPENSATION SETTLEMENT OF ESCROW ACCOUNTS US$6,000,000.00
INTERNATIONAL MONETARY FUND (IMF)
Address: 700 19th Street, N.W.
Washington, D.C. 20431, USA
COMPENSATION SETTLEMENT OF ESCROW ACCOUNTS US$6,000,000.00
It is a pleasure to write you that we have reconciled with our logistic department on the reimbursement of some fund spent by you during the cause of your inadequate dealings with some imposters who claim to be staff in banks and other regional payment centers.
Our reconciliation teams with the prospectus instrument of the United Nations after freezing suspected imposters account. This support was fully effective with the help of World Bank after a summit meeting in United States, ?the financial analysis on financial stability issues fluctuating their economy with the international global standard.
After gathering of this sum, our logistic department gave us a list of customers to be paid who fall victims to this imposters due to unawareness. And mode of payment was as well specified for proper conducts and financial regulations to kick against criminality during process of payment.
We have arranged your payment through our swift card centers, which is the latest instruction from International Monetary Fund Reconciliation Office. The card center will send you an ATM Debit card which you will use to withdraw your money in any ATM Center, Banks and Union Pay Credit outlets in the world, You are hereby selected as an honor for this payment approval, which you are to acknowledge the receipt of this mail in returning the required below to the Logistic Department by email listed below.
Office of Reconciliation and Logistics Vaults, International Monetary Fund (IMF),
Contact Manager: Rowland Garett
Email: rowlandgarett4life@gmail.com
1. Full Name:
2. Phone and Fax Number:
3. Your age and Current Occupation:
4. Contact Address where you want your ATM Card to be delivered to (P.O Box Not Acceptable):
For your information, you have to stop any further communication with any other person (s) or office (s) to avoid any hitches in receiving your payment.
Because of Impostors, we hereby issued you our code of conduct, which is (ATM-745) so you have to indicate this code when contacting the Card Center by using it as your subject.
Yours in Service,
Kristalina Georgieva,
Director of the Finance Department
International Monetary Fund
Sample 16:
Text presented within:
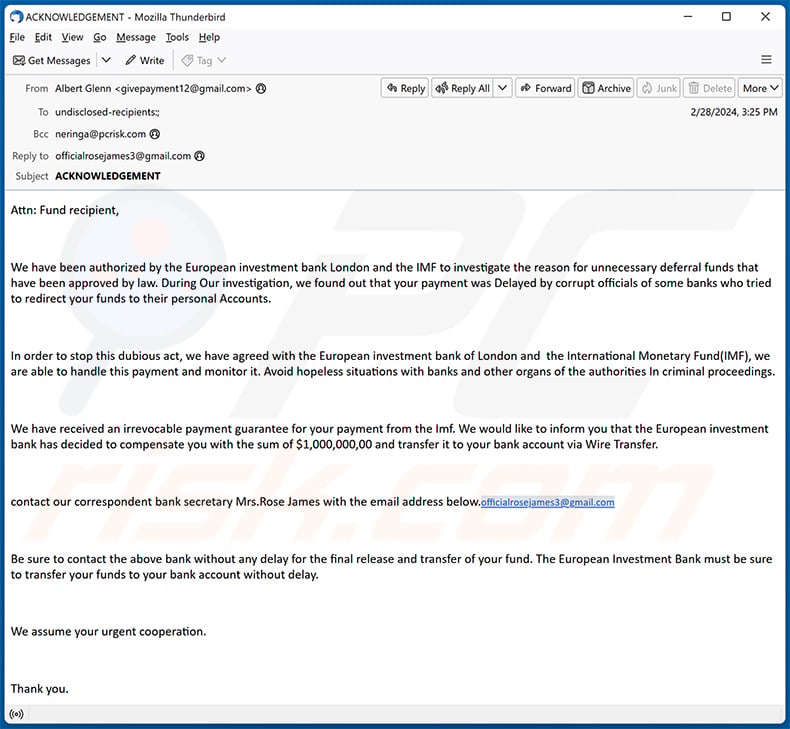
Subject: ACKNOWLEDGEMENT
Attn: Fund recipient,
We have been authorized by the European investment bank London and the IMF to investigate the reason for unnecessary deferral funds that have been approved by law. During Our investigation, we found out that your payment was Delayed by corrupt officials of some banks who tried to redirect your funds to their personal Accounts.
In order to stop this dubious act, we have agreed with the European investment bank of London and the International Monetary Fund(IMF), we are able to handle this payment and monitor it. Avoid hopeless situations with banks and other organs of the authorities In criminal proceedings.
We have received an irrevocable payment guarantee for your payment from the Imf. We would like to inform you that the European investment bank has decided to compensate you with the sum of $1,000,000,00 and transfer it to your bank account via Wire Transfer.
contact our correspondent bank secretary Mrs.Rose James with the email address below.officialrosejames3@gmail.com
Be sure to contact the above bank without any delay for the final release and transfer of your fund. The European Investment Bank must be sure to transfer your funds to your bank account without delay.
We assume your urgent cooperation.
Thank you.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is INTERNATIONAL MONETARY FUND (IMF) spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Usually, cybercriminals use obtained email databases to spread their scams. They send the same email (or emails) to many people - these emails are never personal.
I have provided my personal information when tricked by this email, what should I do?
Victims who have fallen for such scams (have provided account credentials) should change all passwords immediately. In other cases (for example, when the provided information is credit card details, ID card information etc.), users should contact corresponding authorities.
Can emails be used to distribute malware?
Emails can be used as tools to trick recipients into infecting their computers. Such emails contain malicious attachments or links. Recipients infect computers by opening/executing malicious files.
Will Combo Cleaner remove malware infections that were present in email attachment?
Yes, Combo Cleaner will detect and eliminate almost all known malware infections. It is recommended to scan the operating system using the full scan feature. Certain types of malware are capable of hiding deep in the system.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion