Do not trust the "Synchronize Mail Error" scam emails
Phishing/ScamAlso Known As: Synchronize Mail Error spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the "Synchronize Mail Error" scam email?
"Synchronize Mail Error" refers to an email spam campaign. This term refers to a large-scale operation during which deceptive emails are sent by the thousand. The letters distributed through this campaign notify recipients that they have a number of pending emails.
The messages are supposedly withheld and require to be released or deleted. It must be emphasized that this information is false, and recipients have no mail that has failed to arrive into their email inbox. The purpose of the "Synchronize Mail Error" scam letters is to promote a phishing website, which is disguised as the email account sign-in page.
Any data entered into this site is disclosed to the scammers behind the spam campaign.
The "Synchronize Mail Error" scam emails (subject/title "Synchronize Mail Error: [13] messages to ******** is delayed for 48 hours"; may vary) inform recipients that they have thirteen incoming messages. The letters allegedly failed to arrive into the inbox due to a security level lift on the email server.
Recipients are reassured that the nonexistent emails are currently stored on a backup server. The scam letters instruct to either release the messages into the inbox or discard them if they are irrelevant. By clicking the "Release all Pending" link in the emails, recipients are redirected to the phishing webpage.
This site is presented as the sign-in page to the recipients' email accounts. Log-in credentials (i.e., passwords) provided to the website are revealed to the scammers. If attempts to sign-in through this webpage have already been made, it is advised to immediately change the emails' passwords (and those of other potentially affected accounts).
Additionally, it is recommended to contact the official support of all possibly compromised accounts/services. Email accounts are of particular interest to scammers as they are often associated with other accounts/services. Hence, through hijacked mails - it may be possible to gain access to connected content/platforms.
To elaborate on how this can be misused via stolen communicating accounts (e.g., emails, social networking, social media, messengers, etc.), scammers can assume the owner's identity and ask contacts/friends for loans. Alternatively, by sharing infectious files through such accounts - cyber criminals can proliferate malware (e.g., trojans, ransomware, cryptominers, etc.).
Accounts that directly or indirectly deal with finances or financial information (e.g., store credit card details) can be used to make fraudulent transactions and/or online purchases.
To summarize, by trusting the "Synchronize Mail Error" scam letters, recipients can lose their emails and associated accounts/services, experience severe privacy issues, financial losses, and even identity theft.
| Name | Synchronize Mail Error Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Scam emails claim recipients have messages pending arrival into their email inbox. |
| Related Domains | airus.co[.]uk, laptopspot[.]co |
| Serving IP Address (airus.co[.]uk) | 50.116.93.215 |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
"New sign-in on", "Order Error", "N26 email scam", and "Email Disabling Service" are a few examples of phishing spam campaigns. The letters distributed through these mass-scale operations are usually disguised as "official", "urgent", "important", and similar.
This mail may even be presented as messages from genuine institutions, organizations, companies, service providers, and other entities. Spam mail is used for phishing and various other scams, but most importantly - to spread malware. Due to the relative prevalence of deceptive emails, it is strongly advised to exercise caution with incoming letters.
How do spam campaigns infect computers?
Spam campaigns infect systems via virulent files distributed through them. The scam emails contain download links of malicious files, and/or the files are simply attached to the letters. Infectious files can be in various formats (e.g., archives, executables, Microsoft Office and PDF documents, JavaScript, etc.), and when they are opened - malware download/installation is triggered.
For example, Microsoft Office documents cause infections by executing malicious macro commands. In Microsoft Office versions released before 2010, this process begins the moment a document is opened. Newer versions have "Protected View" mode that prevents automatic execution of macros.
Instead, users are asked to enable macro commands (i.e., to enable editing/content) and are warned of the risks.
How to avoid installation of malware?
Suspect and/or irrelevant emails must not be opened, especially any attachments or links present in them - as they are origins of potential system infections.
Additionally, it is recommended to use Microsoft Office versions released after 2010. Aside from spam campaigns, malware is also spread through untrustworthy download channels (e.g., unofficial and free file-hosting websites, Peer-to-Peer sharing networks, etc.), illegal software activation tools ("cracks"), and fake updates.
Therefore, all downloads must be done from official and verified sources. It is just as important to activate and update programs with tools/functions provided by legitimate developers. To ensure device and user safety, it is crucial to have a reputable anti-virus/anti-spyware installed and kept updated.
This software is to be used to perform regular system scans and remove detected/potential threats. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
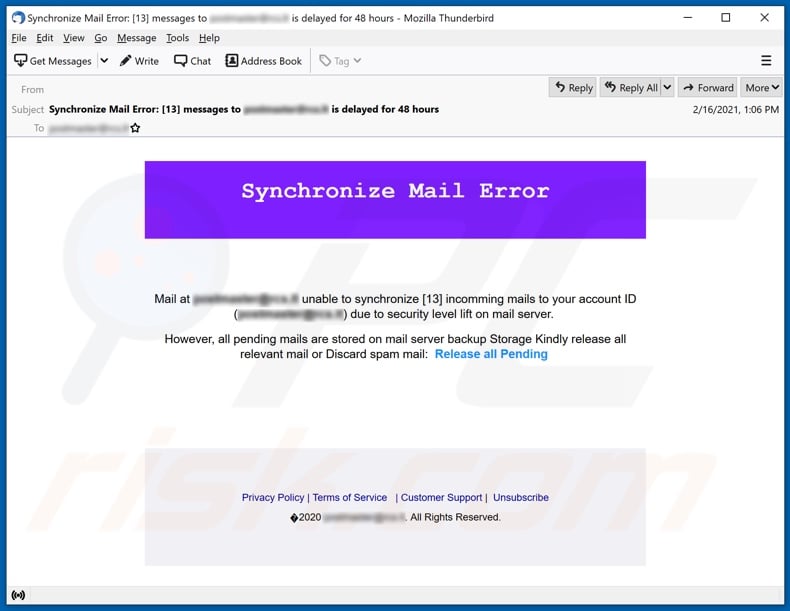
Text presented in the "Synchronize Mail Error" scam email letter:
Subject: Synchronize Mail Error: [13] messages to ******** is delayed for 48 hours
Synchronize Mail Error
Mail at ********* unable to synchronize [13] incomming mails to your account ID (********) due to security level lift on mail server.
However, all pending mails are stored on mail server backup Storage Kindly release all relevant mail or Discard spam mail: Release all Pending
Privacy Policy | Terms of Service | Customer Support | Unsubscribe
2020 ********. All Rights Reserved.
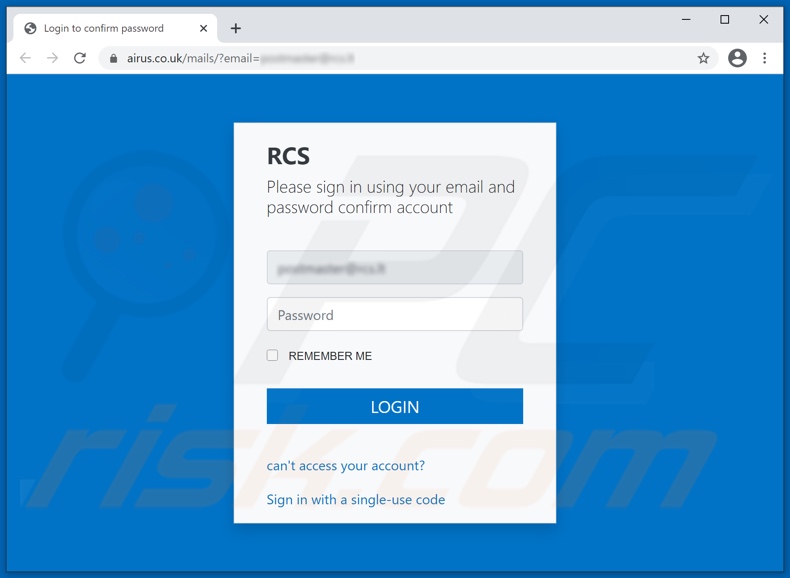
Screenshot of the phishing website promoted by the "Synchronize Mail Error" spam campaign:
Another example of email synchronization-themed spam email used to promote an identical phishing website:
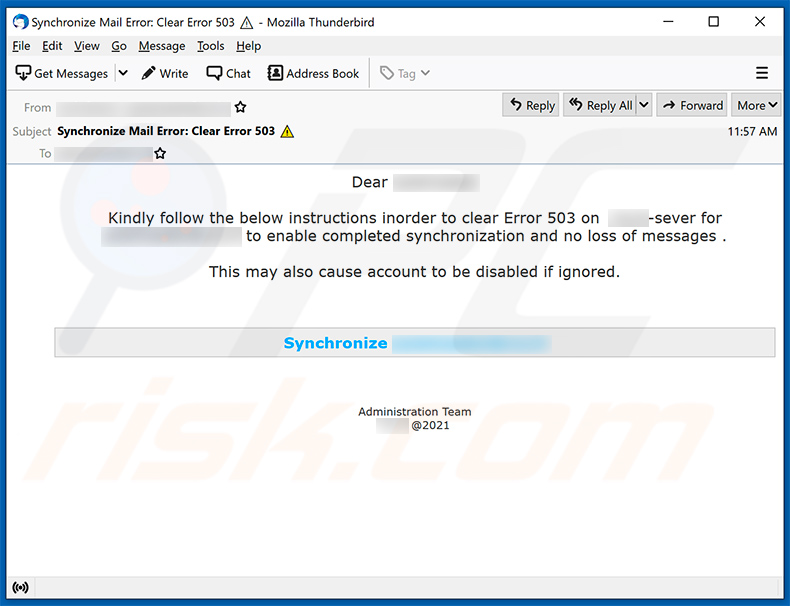
Text presented within:
Dear ********
Kindly follow the below instructions inorder to clear Error 503 on ********-sever for ******** to enable completed synchronization and no loss of messages .
This may also cause account to be disabled if ignored.
Synchronize ********
Administration Team
******** @2021
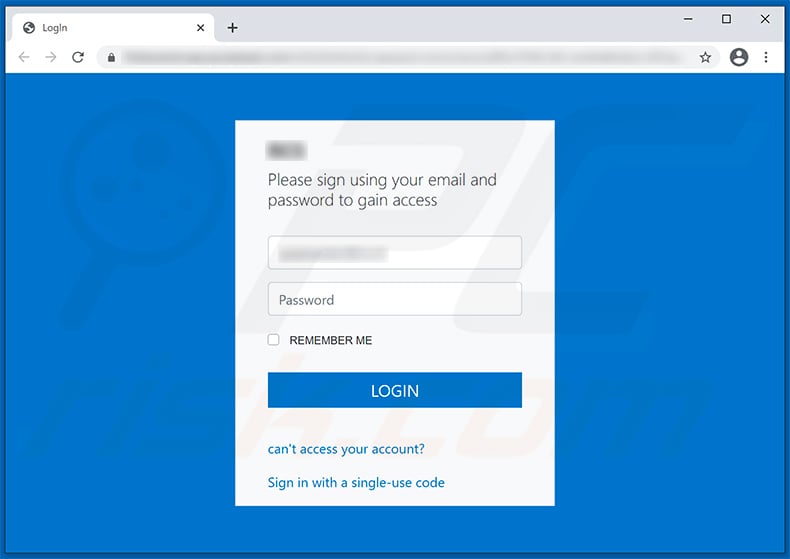
Screenshot of a phishing website promoted via this spam email:
Yet another variant of mail synchronization-themed spam:
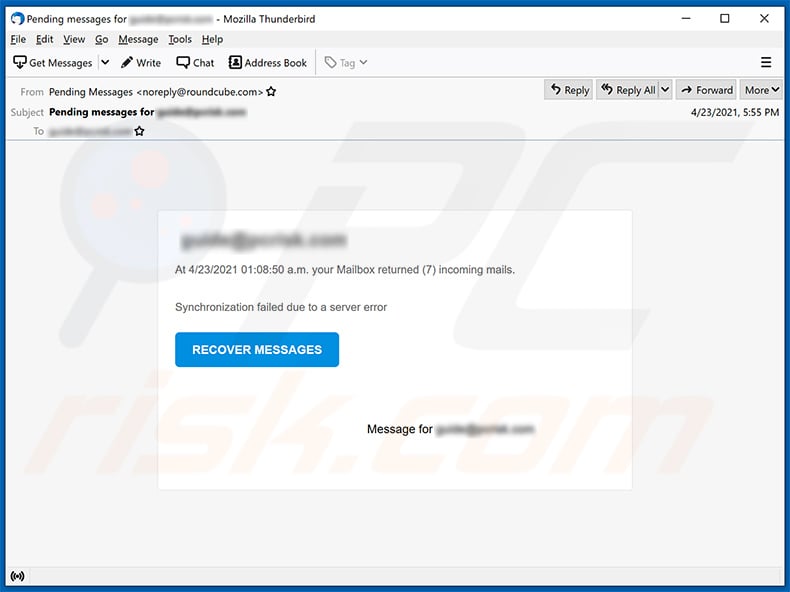
Tet presented within:
Subject: Pending messages for ********
********
At 4/23/2021 01:08:50 a.m. your Mailbox returned (7) incoming mails.
Synchronization failed due to a server error
RECOVER MESSAGES
Message for ********
Another example of email synchronization-themed spam email promoting a phishing website:
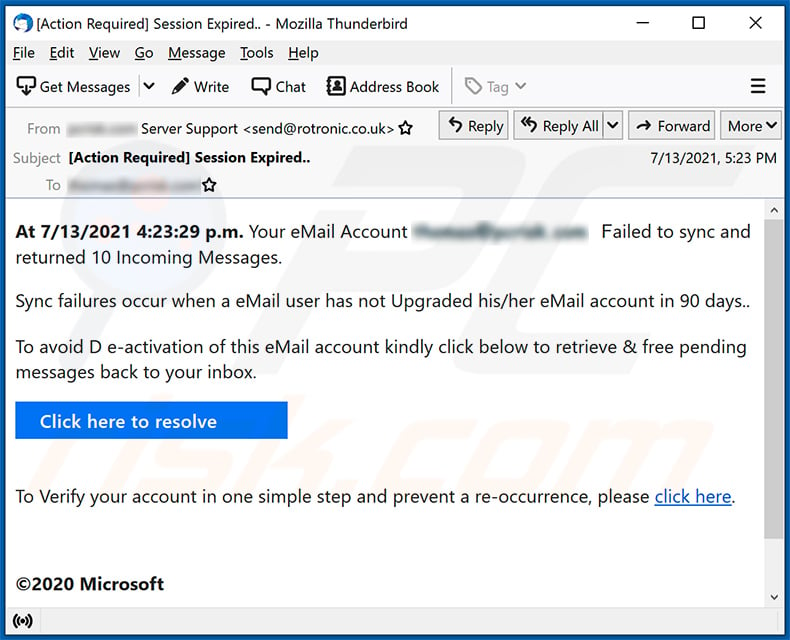
Text presented within:
Subject: [Action Required] Session Expired..
At 7/13/2021 4:23:29 p.m. Your eMail Account ******** Failed to sync and returned 10 Incoming Messages.
Sync failures occur when a eMail user has not Upgraded his/her eMail account in 90 days..
To avoid D e-activation of this eMail account kindly click below to retrieve & free pending messages back to your inbox.
Click here to resolveTo Verify your account in one simple step and prevent a re-occurrence, please click here.
©2020 Microsoft
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Synchronize Mail Error spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion