Avoid having your bank account stolen via fake "Novo Banco" emails
Phishing/ScamAlso Known As: Novo Banco spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "Novo Banco email scam"?
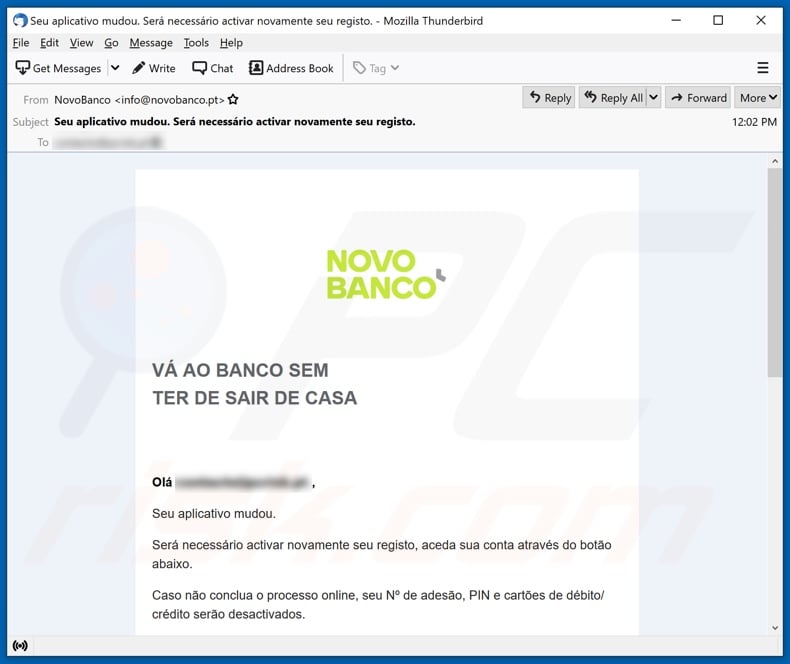
"Novo Banco email scam" is the name of a spam campaign - a large-scale operation during which deceptive emails are sent by the thousand. These letters are disguised notifications from Novo Banco - a legitimate Portuguese bank.
The fake emails request recipients to reactivate and reregister their banking app. This spam campaign aims to promote a phishing website disguised as Novo Banco's sign-in page. Data entered into this site is sent to the scammers, potentially allowing them to take possession of the accounts.
"Novo Banco" scam emails in detail
According to a rough translation, the fake "Novo Banco" emails (subject/title "Seu aplicativo mudou. Será necessário activar novamente seu registo."; may vary) inform recipients that changes have been made to their bank application. The scam letters urge to activate and register the account again.
To access their accounts, recipients are instructed to press the "Aceda sua conta" button presented in the email. The fraudulent letters warn that unless this is done, the recipients' membership and PIN numbers will be disabled, and their debit/credit cards - deactivated.
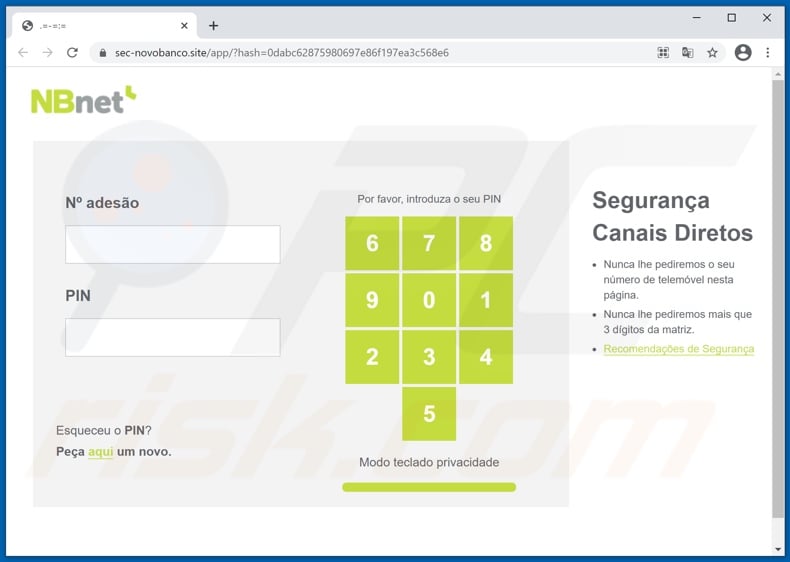
It must be emphasized that these emails are in no way associated with the genuine Novo Banco. Hence, when recipients click the button to access their accounts - they are redirected to a phishing site. This webpage is presented as the sign-in page to Novo Banco.
However, the webpage is illegitimate and operates by recording information provided to it. Therefore, users will inadvertently expose their bank account log-in credentials by attempting to sign in through this phishing website.
To summarize, by trusting these scam letters, users can lose their banking accounts, experience severe privacy issues, financial losses, and identity theft. If attempts to sign in through the phishing page have already been made, users must change the log-in credentials immediately and contact the official support of Novo Banco.
| Name | Novo Banco Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Emails claim recipients must reactivate and reregister their banking apps. |
| Disguise | Scam emails are disguised as letters from the Novo Banco Portuguese bank. |
| Related Domains | sec-novobanco[.]site |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Spam campaigns in general
Phishing spam campaigns target a wide variety of information, including (but not limited to): log-in credentials (e.g., online banks, e-commerce platforms, social networking/media, etc.), personally identifiable details (i.e., names, addresses, contact information. etc.), finance-related data (e.g., credit card numbers, etc.).
"DBS Bank email scam", "UN Covid-19 stimulus package", "Bonifico Effettuato", "Emails Rejected On Admin Server", and "BANCO BPM email scam" are some examples of this type of spam mail. However, these massive operations are not used just for phishing.
Spam campaigns are also employed to facilitate various scams and to proliferate malware (e.g., trojans, ransomware, cryptocurrency miners, etc.). Due to how widespread scam mail is, it is highly recommended to exercise caution with incoming emails.
How do spam campaigns infect computers?
Systems are infected via malicious files distributed through spam campaigns. These files can be attached to and/or linked inside the letters. Infectious files can be in various formats, e.g., Microsoft Office and PDF documents, archives, executables, JavaScript, and so forth.
When the files are executed, run, or otherwise opened - the infection process (i.e., malware download/installation) is initiated. For example, Microsoft Office documents cause infections by executing malicious macro commands.
This process starts the moment a document is opened in Microsoft Office versions released prior to 2010. Later versions have "Protected View" mode that prevents automatic execution of macros. Instead, users can manually enable macro commands (i.e., editing/content).
How to avoid installation of malware?
Dubious and irrelevant emails must not be opened, especially any attachments/links found in them. Aside from spam campaigns, malware is spread via untrustworthy download channels (e.g., unofficial and free file-hosting sites, Peer-to-Peer sharing networks, and other third-party downloaders), illegal activation tools ("cracks"), and fake updates.
Therefore, it is recommended to download only from official and verified sources. Additionally, all programs must be activated and updated with tools/functions provided by legitimate developers.
To ensure device integrity and user privacy, it is paramount to have a dependable anti-virus/anti-spyware suite installed and kept up-to-date. Furthermore, this software has to be used to perform regular system scans and to remove detected/potential threats.
If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "Novo Banco" scam email letter:
Subject: Seu aplicativo mudou. Será necessário activar novamente seu registo.
NOVO BANCO
VÁ AO BANCO SEM TER DE SAIR DE CASA
Olá ******** ,
Seu aplicativo mudou
.
Será necessário activar novamente seu registo, aceda sua conta através do botão abaixo.
Caso não conclua o processo online, seu Nº de adesão, PIN e cartões de débito/ crédito serão desactivados.
Aceda sua conta
Não complicar é o nosso jeito de ser!
Até já, lu
Andreia Teixeira
Diretora de Segurança
O NovoBanco, S.A. é um intermediário financeiro registado na Comissão do Mercado de Valores Mobiliários e encontra-se autorizado a prestar os serviços de investimento de receção e transmissão de ordens por conta de outrem.
© 2021 NOVO BANCO, SA
Appearance of the "Novo Banco" scam email (GIF):
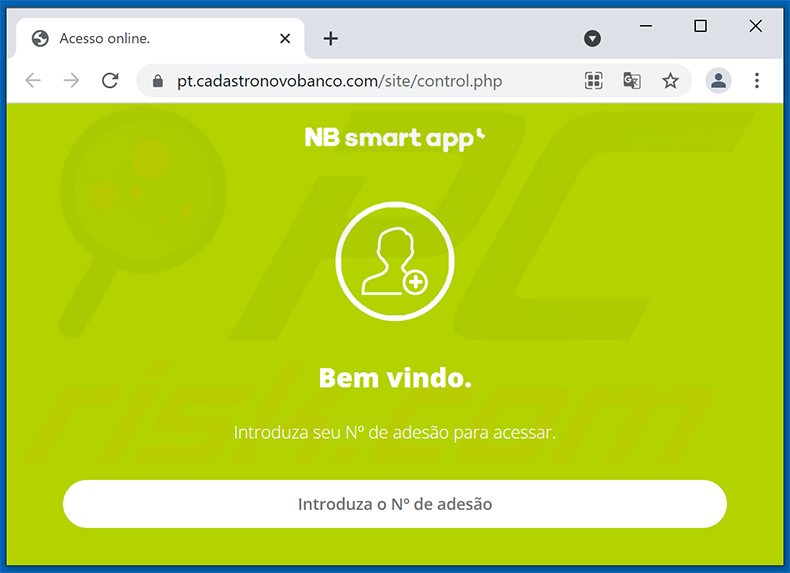
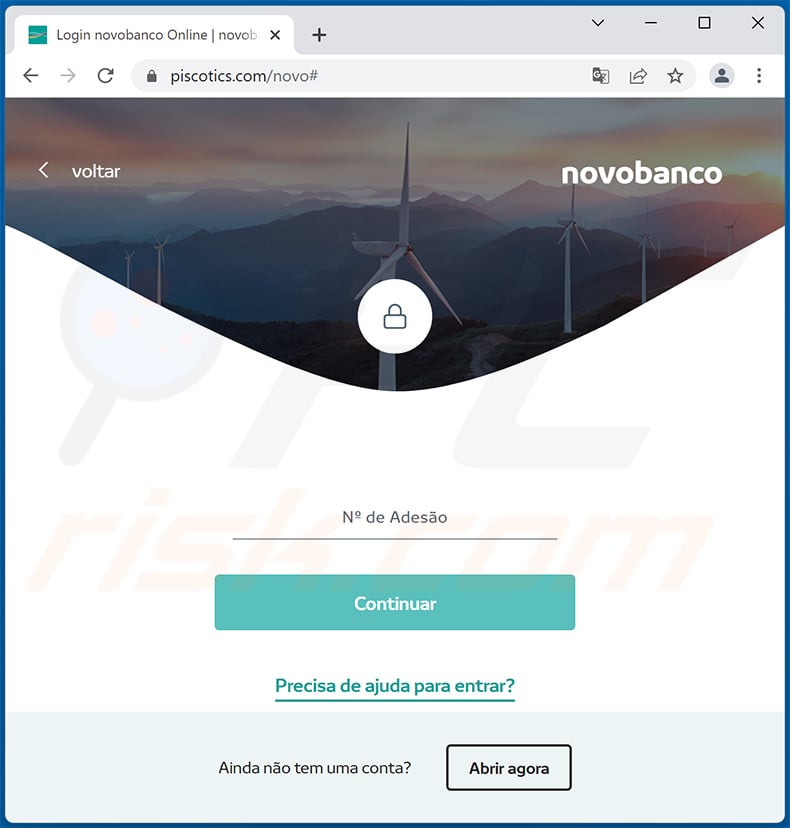
Screenshot of the phishing site disguised as Novo Banco's sign-in page:
Other examples of Novo Banco-themed spam emails used to promote a phishing websites:
Sample 1:
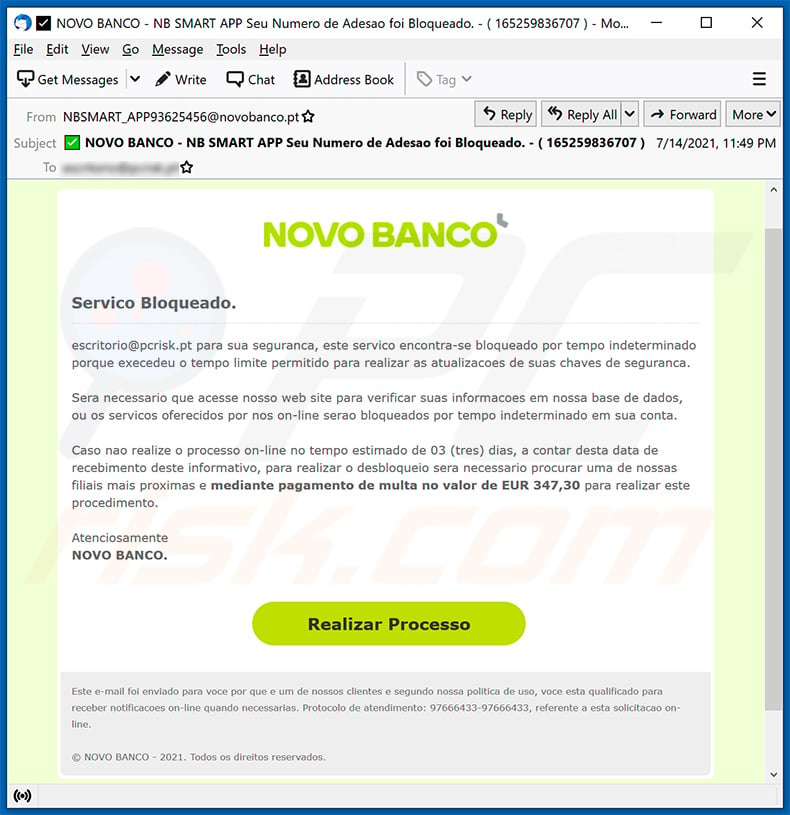
Text presented within:
Subject: NOVO BANCO - NB SMART APP Seu Numero de Adesao foi Bloqueado. - ( 165259836707 )
Servico Bloqueado.******** para sua seguranca, este servico encontra-se bloqueado por tempo indeterminado porque execedeu o tempo limite permitido para realizar as atualizacoes de suas chaves de seguranca.
Sera necessario que acesse nosso web site para verificar suas informacoes em nossa base de dados, ou os servicos oferecidos por nos on-line serao bloqueados por tempo indeterminado em sua conta.
Caso nao realize o processo on-line no tempo estimado de 03 (tres) dias, a contar desta data de recebimento deste informativo, para realizar o desbloqueio sera necessario procurar uma de nossas filiais mais proximas e mediante pagamento de multa no valor de EUR 347,30 para realizar este procedimento.
Atenciosamente
NOVO BANCO.
Realizar ProcessoEste e-mail foi enviado para voce por que e um de nossos clientes e segundo nossa politica de uso, voce esta qualificado para receber notificacoes on-line quando necessarias. Protocolo de atendimento: 97666433-97666433, referente a esta solicitacao on-line.
© NOVO BANCO - 2021. Todos os direitos reservados.
14/07/2021 08:49:15
Screenshot of the promoted phishing site:
Sample 2:
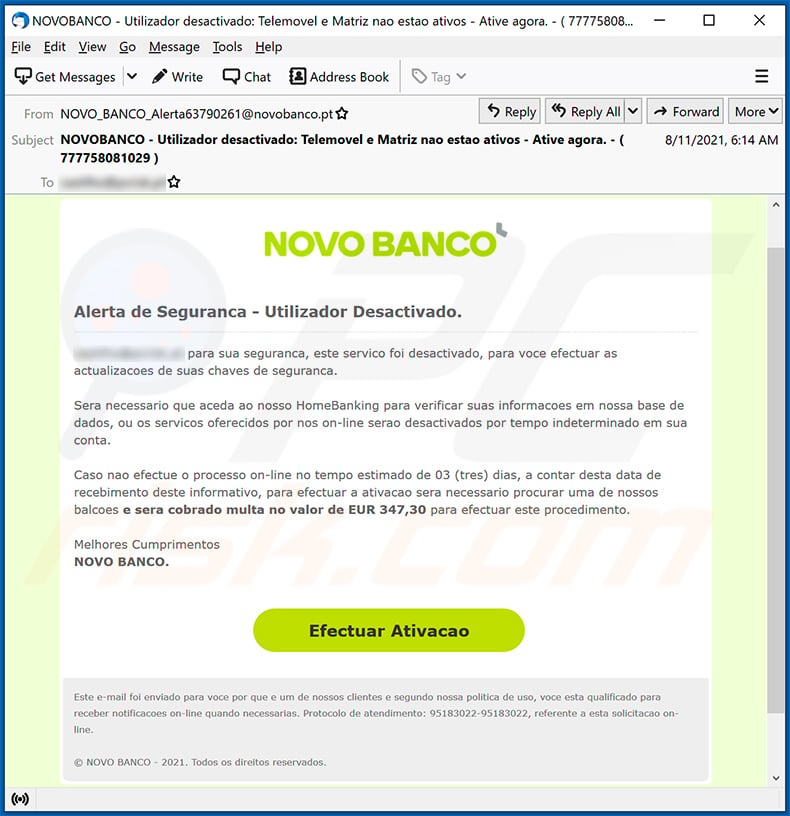
Text presented within:
Subject: NOVOBANCO - Utilizador desactivado: Telemovel e Matriz nao estao ativos - Ative agora. - ( 777758081029 )
Alerta de Seguranca - Utilizador Desactivado.
******** para sua seguranca, este servico foi desactivado, para voce efectuar as actualizacoes de suas chaves de seguranca.
Sera necessario que aceda ao nosso HomeBanking para verificar suas informacoes em nossa base de dados, ou os servicos oferecidos por nos on-line serao desactivados por tempo indeterminado em sua conta.
Caso nao efectue o processo on-line no tempo estimado de 03 (tres) dias, a contar desta data de recebimento deste informativo, para efectuar a ativacao sera necessario procurar uma de nossos balcoes e sera cobrado multa no valor de EUR 347,30 para efectuar este procedimento.
Melhores Cumprimentos
NOVO BANCO.
Efectuar AtivacaoEste e-mail foi enviado para voce por que e um de nossos clientes e segundo nossa politica de uso, voce esta qualificado para receber notificacoes on-line quando necessarias. Protocolo de atendimento: 95183022-95183022, referente a esta solicitacao on-line.
© NOVO BANCO - 2021. Todos os direitos reservados.
10/08/2021 08:14:13
Sample 3:
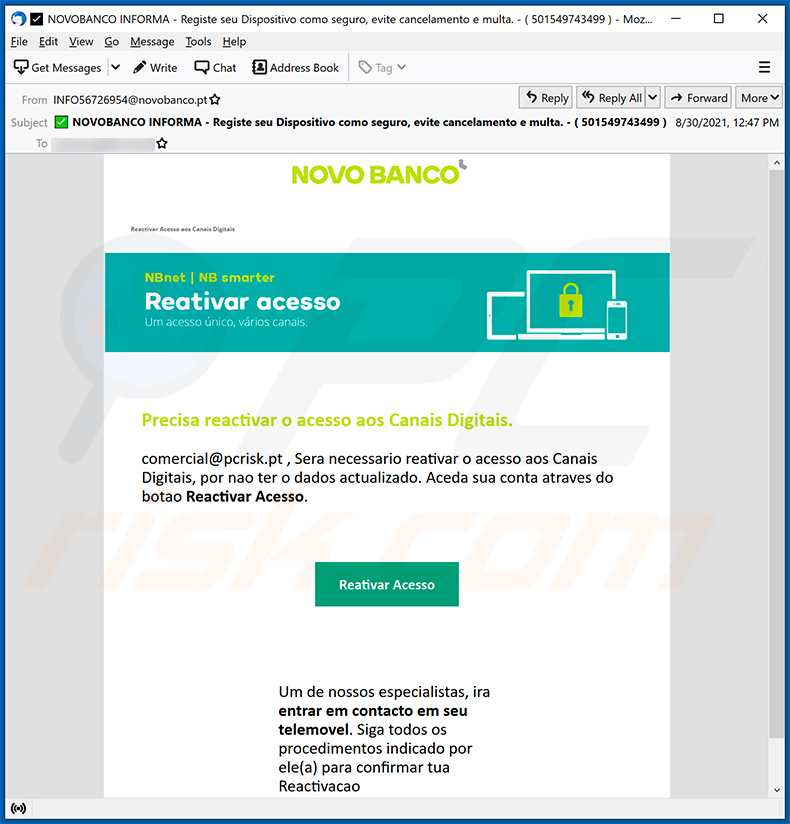
Text presented within:
Subject: NOVOBANCO INFORMA - Registe seu Dispositivo como seguro, evite cancelamento e multa. - ( 501549743499 )
NOVO BANCO
Reactivar Acesso aos Canais Digitais
NBnet | NB smarter
Reativar acesso
Um acesso único, vàrios canais.
Precisa reactivar o acesso aos Canais Digitais.
********* , Sera necessario reativar o acesso aos Canais Digitais, por nao ter o dados actualizado. Aceda sua conta atraves do botao Reactivar Acesso.Reativar Acesso
Um de nossos especialistas, ira entrar em contacto em seu telemovel. Siga todos os procedimentos indicado por ele(a) para confirmar tua Reactivacao
Sample 4:
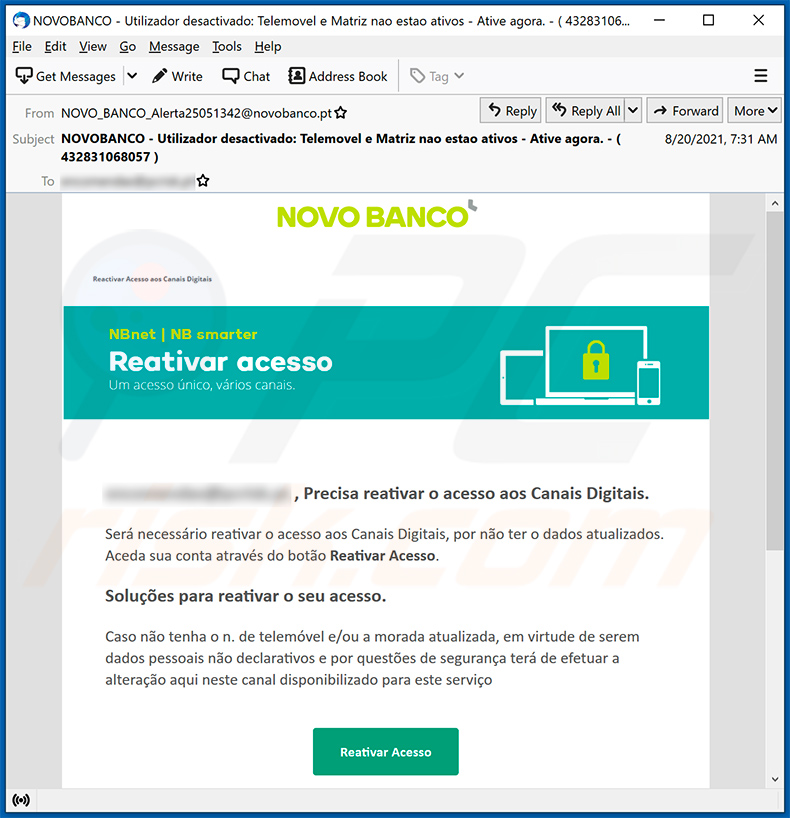
Text presented within:
Subject: NOVOBANCO - Utilizador desactivado: Telemovel e Matriz nao estao ativos - Ative agora. - ( 432831068057 )
NOVO BANCO
Reactivar Acesso aos Canais Digitais
NBnet | NB smarter
Reativar acesso
Um acesso único, vàrios canais.
******** , Precisa reativar o acesso aos Canais Digitais.
Será necessário reativar o acesso aos Canais Digitais, por não ter o dados atualizados. Aceda sua conta através do botão Reativar Acesso.
Soluções para reativar o seu acesso.Caso não tenha o n. de telemóvel e/ou a morada atualizada, em virtude de serem dados pessoais não declarativos e por questões de segurança terá de efetuar a alteração aqui neste canal disponibilizado para este serviço
Reativar Acesso
Sample 5:
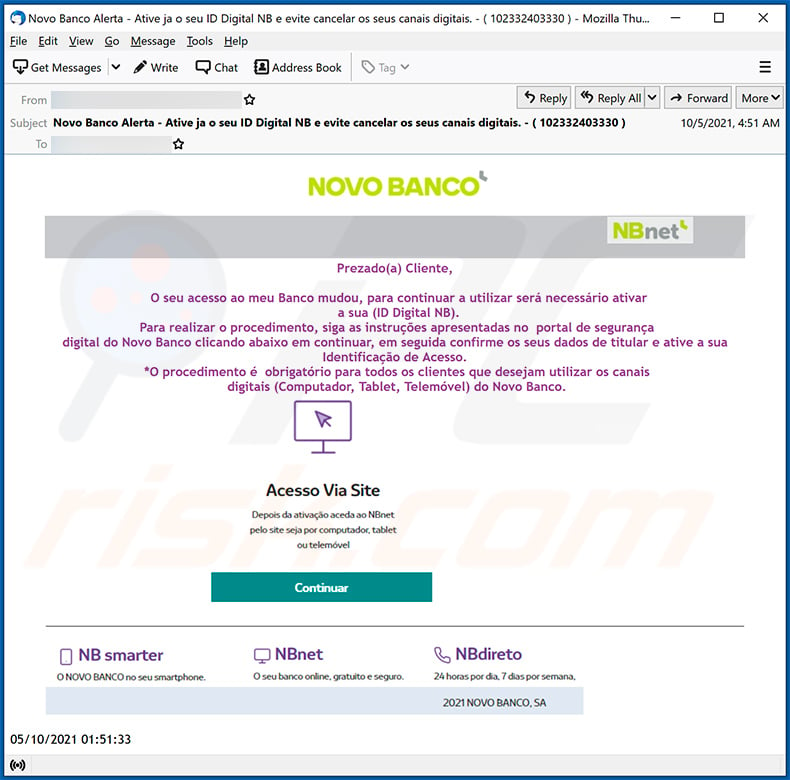
Text presented within:
Subject: Novo Banco Alerta - Ative ja o seu ID Digital NB e evite cancelar os seus canais digitais. - ( 102332403330 )
Prezado(a) Cliente,
O seu acesso ao meu Banco mudou, para continuar a utilizar será necessário ativar
a sua (ID Digital NB).
Para realizar o procedimento, siga as instruções apresentadas no portal de segurança
digital do Novo Banco clicando abaixo em continuar, em seguida confirme os seus dados de titular e ative a sua Identificação de Acesso.
*O procedimento é obrigatório para todos os clientes que desejam utilizar os canais
digitais (Computador, Tablet, Telemóvel) do Novo Banco.
Sample 6:
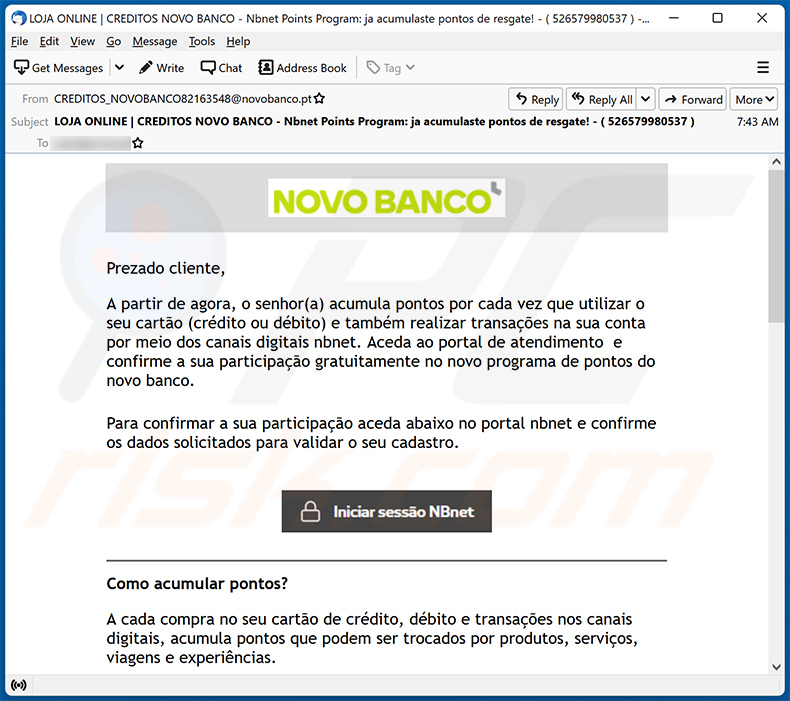
Text presented within:
Subject: LOJA ONLINE | CREDITOS NOVO BANCO - Nbnet Points Program: ja acumulaste pontos de resgate! - ( 526579980537 )
Prezado cliente,
A partir de agora, o senhor(a) acumula pontos por cada vez que utilizar o seu cartão (crédito ou débito) e também realizar transações na sua conta por meio dos canais digitais nbnet. Aceda ao portal de atendimento e confirme a sua participação gratuitamente no novo programa de pontos do novo banco.
Para confirmar a sua participação aceda abaixo no portal nbnet e confirme os dados solicitados para validar o seu cadastro.
Como acumular pontos?
A cada compra no seu cartão de crédito, débito e transações nos canais digitais, acumula pontos que podem ser trocados por produtos, serviços, viagens e experiências.
Fique ligado também nas campanhas para acumular ainda mais pontos conforme a época de uso e as nossas promoções.
Confira algumas ofertas que podem ser trocadas por pontos na loja online:
Iphone 13 Pro Max 256 GB 360.300 Pontos
Samsung Galaxy Z Flip3 256 GB 315.200 Pontos
ACER Portátil Extensa EX215-31 15,6" 256 GB 125.250 Pontos
Apple iMac 24-inch with Retina 4.5K 8GB/256GB 385.500 Pontos
2021 NOVO BANCO, SA 14/10/2021 04:43:14
Sample 7:
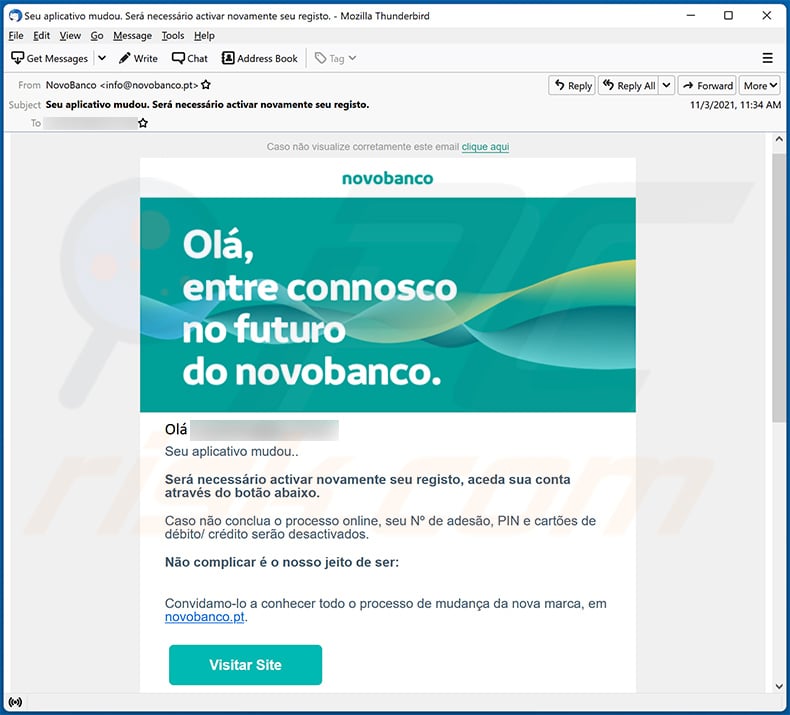
Text presented within:
Subject: Seu aplicativo mudou. Será necessário activar novamente seu registo.
Caso não visualize corretamente este email clique aqui
Olá -Seu aplicativo mudou..
Será necessário activar novamente seu registo, aceda sua conta através do botão abaixo.
Caso não conclua o processo online, seu Nº de adesão, PIN e cartões de débito/ crédito serão desactivados.Não complicar é o nosso jeito de ser:
Convidamo-lo a conhecer todo o processo de mudança da nova marca, em novobanco.pt.
Visitar SiteEm nome do novobanco, da sua administração e de todos os seus colaboradores, agradecemos a sua confiança e prometemos continuar a fazer o futuro consigo.
Cumprimentos,
Juntos fazemos o futuro.Contacte-nos:
Website App novobanco OnlineSiga-nos:
Esta mensagem foi enviada automaticamente pelo que as mensagens enviadas para este endereço de e-mail não serão respondidas.
Os dados pessoais são tratados de acordo com o Regulamento Geral de Proteção de Dados e demais legislação aplicável e nos termos das informações sobre o tratamento de dados pessoais que estão disponíveis a todo o momento em novobanco.pt/politicaprivacidade.
Sample 8:
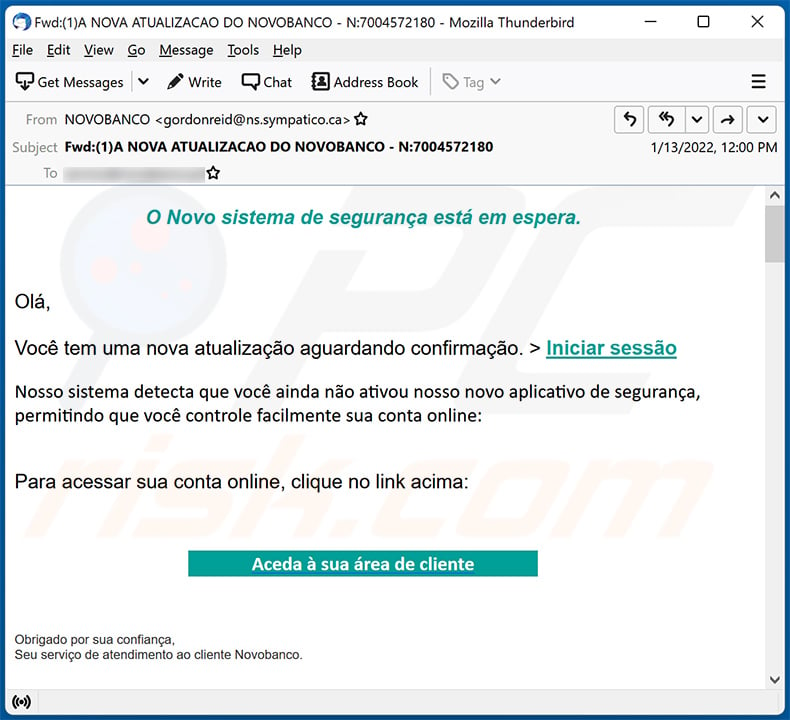
Text presented within:
Subject:Fwd:(1)A NOVA ATUALIZACAO DO NOVOBANCO - N:7004572180
O Novo sistema de segurança está em espera.Olá,
Você tem uma nova atualização aguardando confirmação. > Iniciar sessão
Nosso sistema detecta que você ainda não ativou nosso novo aplicativo de segurança, permitindo que você controle facilmente sua conta online:
Para acessar sua conta online, clique no link acima:
Aceda à sua área de cliente
Obrigado por sua confiança,
Seu serviço de atendimento ao cliente Novobanco.
Sample 9:
Text presented within:
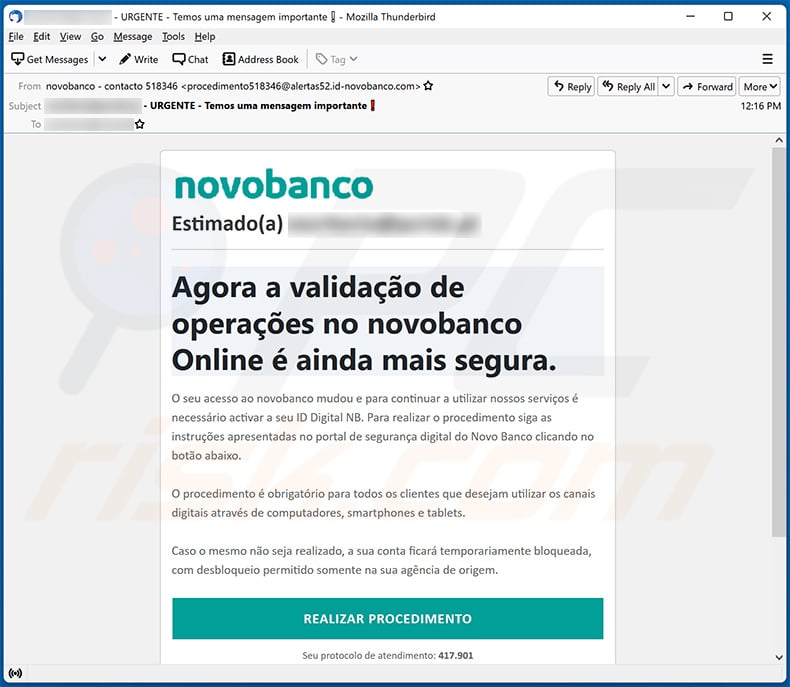
Subject: - URGENTE - Temos uma mensagem importante
Estimado(a) **********
Agora a validação de operações no novobanco Online é ainda mais segura.O seu acesso ao novobanco mudou e para continuar a utilizar nossos serviços é necessário activar a seu ID Digital NB. Para realizar o procedimento siga as instruções apresentadas no portal de segurança digital do Novo Banco clicando no botão abaixo.
O procedimento é obrigatório para todos os clientes que desejam utilizar os canais digitais através de computadores, smartphones e tablets.
Caso o mesmo não seja realizado, a sua conta ficará temporariamente bloqueada, com desbloqueio permitido somente na sua agência de origem.
REALIZAR PROCEDIMENTO
Seu protocolo de atendimento: 417.901ou clique aqui caso o botão acima não funcione.
Sample 10:
Text presented within:
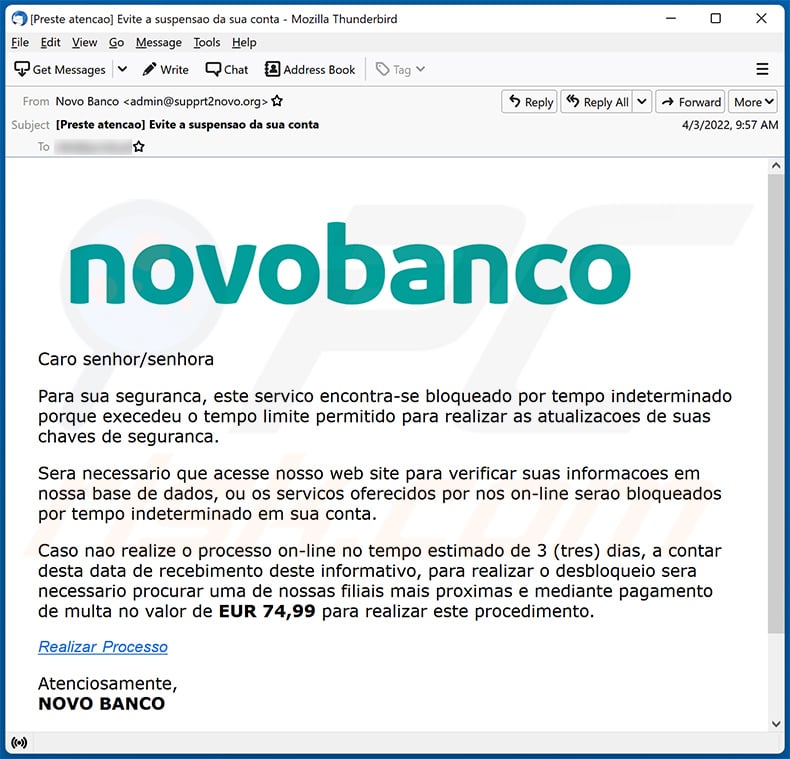
Subject: [Preste atencao] Evite a suspensao da sua conta
novobanco
Caro senhor/senhora
Para sua seguranca, este servico encontra-se bloqueado por tempo indeterminado porque execedeu o tempo limite permitido para realizar as atualizacoes de suas chaves de seguranca.
Sera necessario que acesse nosso web site para verificar suas informacoes em nossa base de dados, ou os servicos oferecidos por nos on-line serao bloqueados por tempo indeterminado em sua conta.
Caso nao realize o processo on-line no tempo estimado de 3 (tres) dias, a contar desta data de recebimento deste informativo, para realizar o desbloqueio sera necessario procurar uma de nossas filiais mais proximas e mediante pagamento de multa no valor de EUR 74,99 para realizar este procedimento.
Realizar Processo
Atenciosamente,
NOVO BANCO
Screenshot of the promoted phishing site:
Sample 11:
Text presented within:
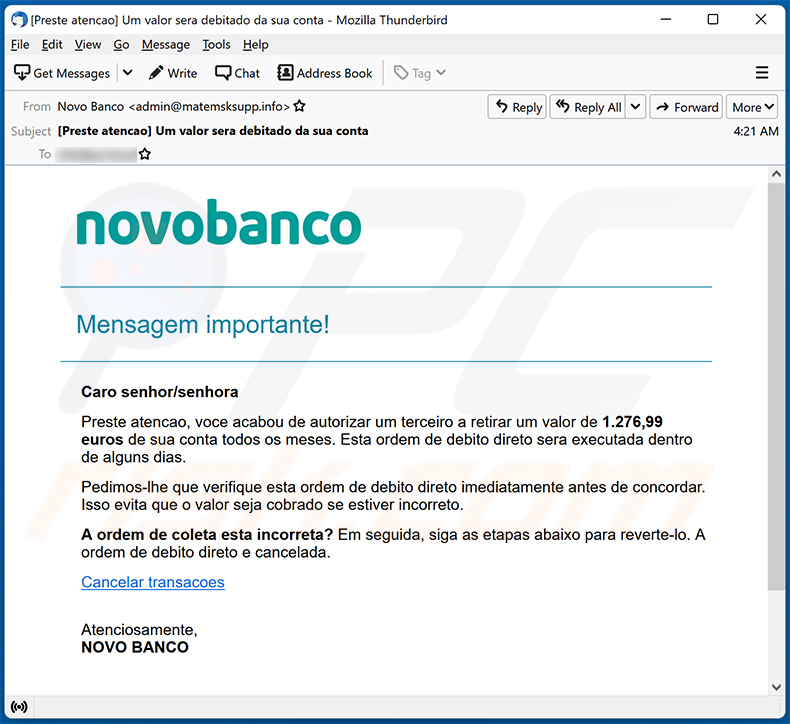
Subject: [Preste atencao] Um valor sera debitado da sua conta
novobanco
Mensagem importante!
Caro senhor/senhora
Preste atencao, voce acabou de autorizar um terceiro a retirar um valor de 1.276,99 euros de sua conta todos os meses. Esta ordem de debito direto sera executada dentro de alguns dias.
Pedimos-lhe que verifique esta ordem de debito direto imediatamente antes de concordar. Isso evita que o valor seja cobrado se estiver incorreto.
A ordem de coleta esta incorreta? Em seguida, siga as etapas abaixo para reverte-lo. A ordem de debito direto e cancelada.
Cancelar transacoes
Atenciosamente,
NOVO BANCO
Sample 12:
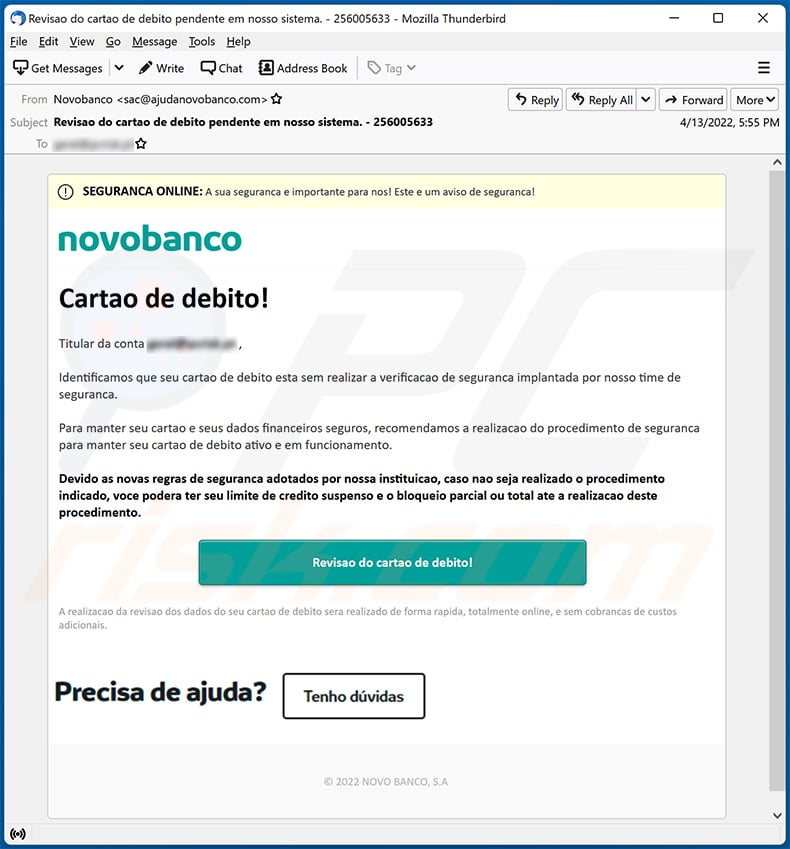
Text presented within:
Subject: Revisao do cartao de debito pendente em nosso sistema. - 256005633
SEGURANCA ONLINE: A sua seguranca e importante para nos! Este e um aviso de seguranca!
Cartao de debito!Titular da conta - ,
Identificamos que seu cartao de debito esta sem realizar a verificacao de seguranca implantada por nosso time de seguranca.
Para manter seu cartao e seus dados financeiros seguros, recomendamos a realizacao do procedimento de seguranca para manter seu cartao de debito ativo e em funcionamento.
Devido as novas regras de seguranca adotados por nossa instituicao, caso nao seja realizado o procedimento indicado, voce podera ter seu limite de credito suspenso e o bloqueio parcial ou total ate a realizacao deste procedimento.
Revisao do cartao de debito!
A realizacao da revisao dos dados do seu cartao de debito sera realizado de forma rapida, totalmente online, e sem cobrancas de custos adicionais.
© 2022 NOVO BANCO, S.A
Sample 13:
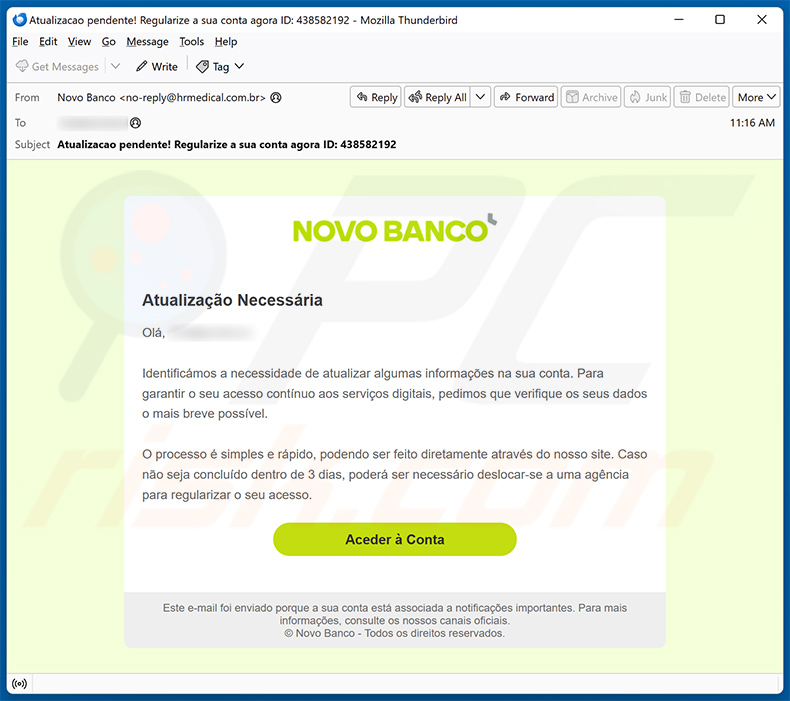
Text presented within:
Subject: Atualizacao pendente! Regularize a sua conta agora ID: 438582192
Novo Banco
Atualização NecessáriaOlá, - ,
Identificámos a necessidade de atualizar algumas informações na sua conta. Para garantir o seu acesso contínuo aos serviços digitais, pedimos que verifique os seus dados o mais breve possível.
O processo é simples e rápido, podendo ser feito diretamente através do nosso site. Caso não seja concluído dentro de 3 dias, poderá ser necessário deslocar-se a uma agência para regularizar o seu acesso.
Aceder à Conta
Este e-mail foi enviado porque a sua conta está associada a notificações importantes. Para mais informações, consulte os nossos canais oficiais.
© Novo Banco - Todos os direitos reservados.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Novo Banco spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal, even if they include information relevant to the recipients. This mail is distributed in large-scale operations – therefore, thousands of users receive identical or incredibly similar messages.
I have provided my personal information when tricked by this spam email, what should I do?
If you have provided your log-in credentials – immediately change the passwords of all potentially exposed accounts and inform their official support. However, if you have disclosed information of a different personal nature (e.g., passport photos/scans, ID card details, credit card numbers, etc.) – contact the appropriate authorities without delay.
I have read a spam email but didn't open the attachment, is my computer infected?
No, reading an email is harmless. Devices are infected when malicious attachments or links are opened/clicked.
I have downloaded and opened a file attached to a spam email, is my computer infected?
File formats can influence infection success rates. Executables (.exe, .run, etc.) cause infections almost without fail once opened. However, some formats – like documents (.doc, .xls, .pdf, .one, etc.) – require additional actions to initiate malware download/installation. Therefore, the infection may only be triggered after macro commands are enabled, embedded content is clicked, or other actions are performed.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is designed to scan systems and remove all kinds of threats. It is capable of detecting and eliminating most of the known malware infections. It must be emphasized that running a full system scan is crucial since sophisticated malicious software usually hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion