How to remove Grand Explorer from computers
AdwareAlso Known As: Grand Explorer cryptocurrency miner
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of program is Grand Explorer?
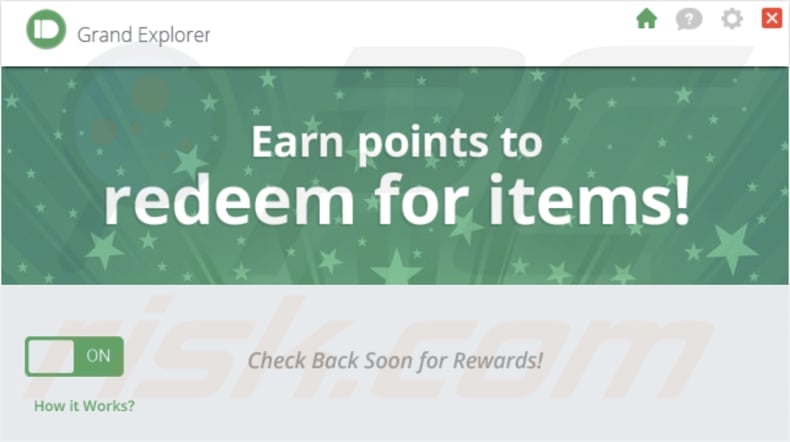
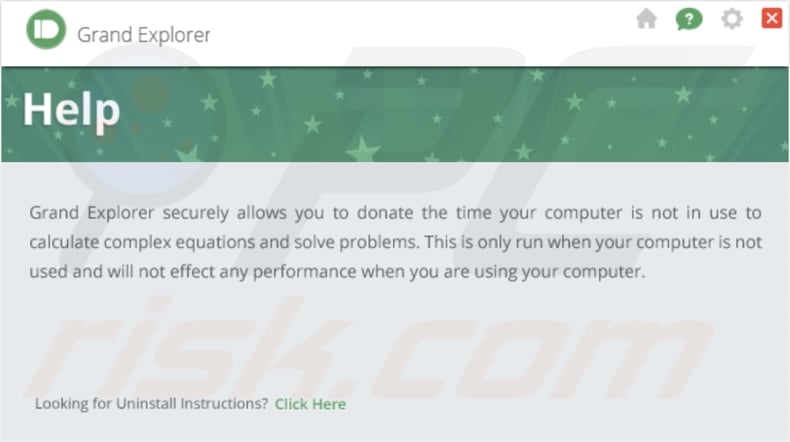
The Grand Explorer app is marketed as a tool that enables users to securely contribute their computer's idle time to perform complex calculations and problem-solving tasks. According to its description, the app operates exclusively during periods of computer inactivity and has no impact on performance when users are actively using their computers.
In essence, Grand Explorer operates as a cryptocurrency miner. Moreover, it is distributed alongside other unwanted apps.
Grand Explorer in detail
As a cryptocurrency miner, Grand Explorer utilizes computer resources to perform complex mathematical calculations, a process known as mining, to validate transactions on a blockchain network and generate new units of cryptocurrency as a reward.
The app might strain system resources excessively, particularly during active computer usage. This could result in a notable decline in overall system performance, causing delays and inefficiencies in tasks unrelated to the application. Users may find their computers responding more slowly, affecting their experience and productivity.
Also, the operation of Grand Explorer might lead to increased power consumption, which can result in higher energy bills. There is also a risk that Grand Explorer could conflict with other software or processes running on a user's computer.
It is known that Grand Explorer is distributed with other shady apps. This raises concerns about potential security risks for users. These bundled apps could include malicious software, adware, browser hijackers, or other unwanted programs that may compromise the user's privacy and system integrity.
Shady apps often engage in practices such as intrusive advertising, data tracking, or even more severe actions like installing malware. Therefore, it is highly advisable to uninstall Grand Explorer from compromised computers and thoroughly examine the system for any additional components that may have been installed alongside it.
| Name | Grand Explorer cryptocurrency miner |
| Threat Type | Cryptocurrency Miner |
| Detection Names | Avira (ADWARE/Opesup.Gen), Cynet (Malicious (score: 99)), DeepInstinct (MALICIOUS), F-Secure (Adware.ADWARE/Opesup.Gen), Full List (VirusTotal) |
| Symptoms | Your computer becomes slower than normal, some programs stop working, computer freezes, and similar issues. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), torrent file downloads, P2P networks, dubious pages, etc. |
| Damage | Increased energy consumption, higher electricity bills, hardware wear and tear, internet bandwidth usage, performance issues. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
Cryptocurrency miners often raise concerns about potential security risks, and users should be wary of the possibility of additional components bundled with Grand Explorer. It is recommended to evaluate the implications of such applications, considering factors like increased power consumption, potential conflicts with other software, and the risk of installing unwanted or malicious programs.
More examples of cryptocurrency miners are Altruistics, Kratos Silent Miner, and Sapphire Miner.
How did unwanted software install on my computer?
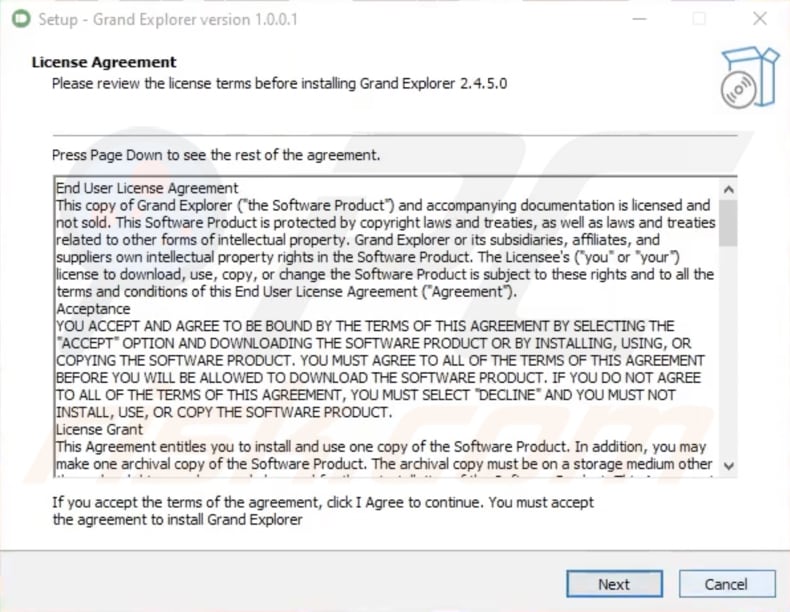
Unintentional installations of undesirable software can occur when users download or install applications from untrustworthy sources. Frequently, users hastily navigate through installation procedures, neglecting to thoroughly examine the provided options and inadvertently agreeing to install bundled applications.
Moreover, users might come across undesired downloads and installations due to deceptive tactics, including misleading advertisements, false download links, or deceptive software updates on untrustworthy websites. Engaging in the downloading of pirated software can similarly result in unintended installations.
How to avoid installation of unwanted applications?
Adhere to reliable websites and official app stores when obtaining software. Before initiating a download, evaluate user reviews and ratings for the application. When installing, choose custom or advanced settings, and be sure to deselect any pre-selected checkboxes for bundled apps. Avoid misleading advertisements or pop-ups, especially those enticing with promises of free software or services.
Make sure to consistently update your antivirus and anti-malware tools. Routinely review the list of installed applications on your device and remove any unfamiliar or unnecessary apps. If your computer is already infected with rogue applications, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Grand Explorer's description:
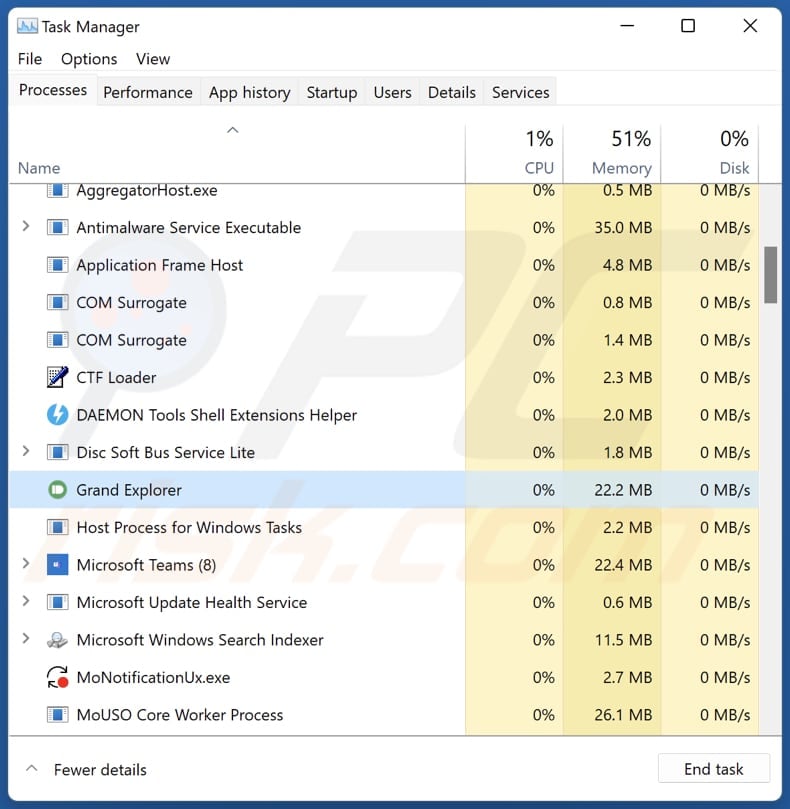
Grand Explorer running in the Task Manager:
The installer used to distribute Grand Explorer:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Grand Explorer?
- STEP 1. Uninstall adware applications using Control Panel.
- STEP 2. Remove rogue plug-ins from Google Chrome.
- STEP 3. Remove adware-type extensions from Mozilla Firefox.
- STEP 4. Remove malicious extensions from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
Unwanted software removal:
Windows 11 users:
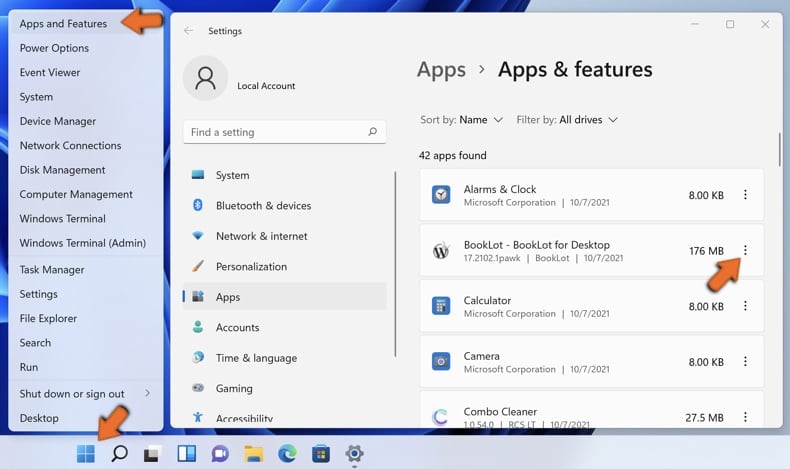
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
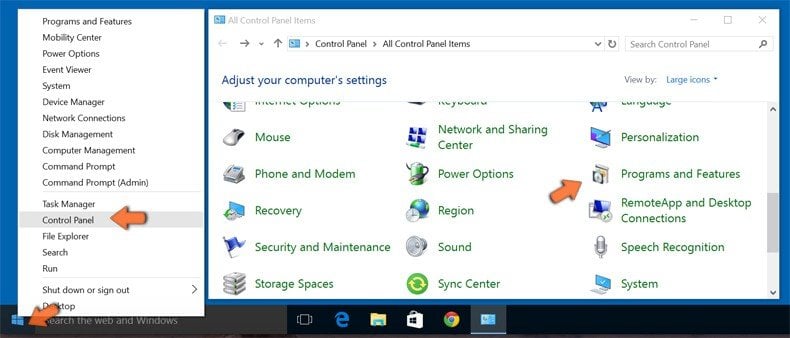
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.
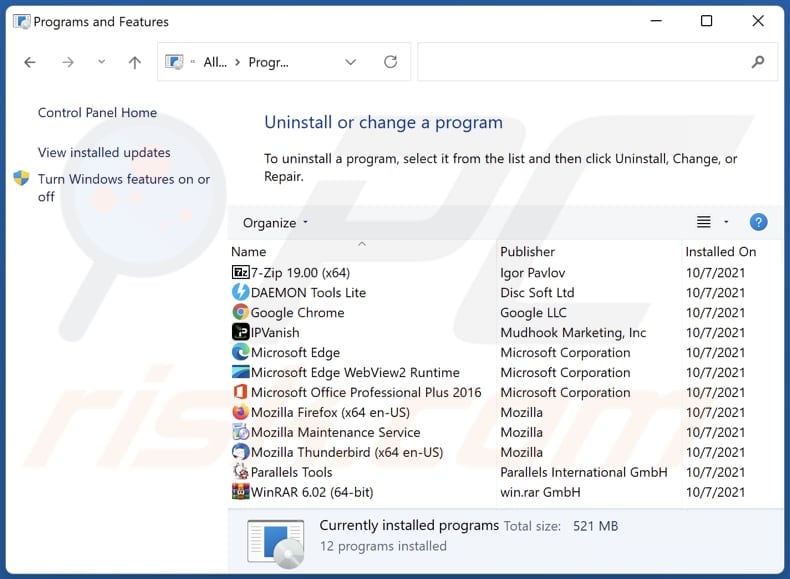
In the uninstall programs window, look for any unwanted applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the unwanted application, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove unwanted apps from Internet browsers:
Video showing how to remove unwanted browser add-ons:
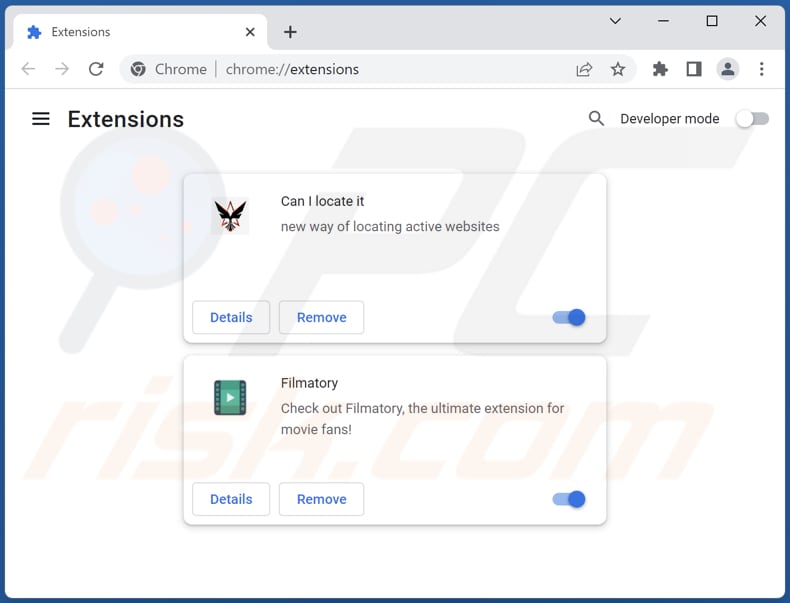
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
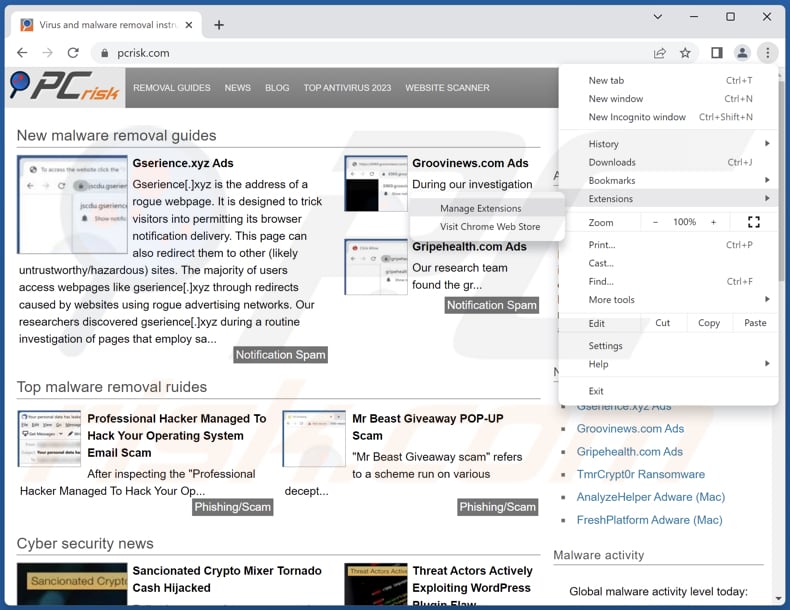
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
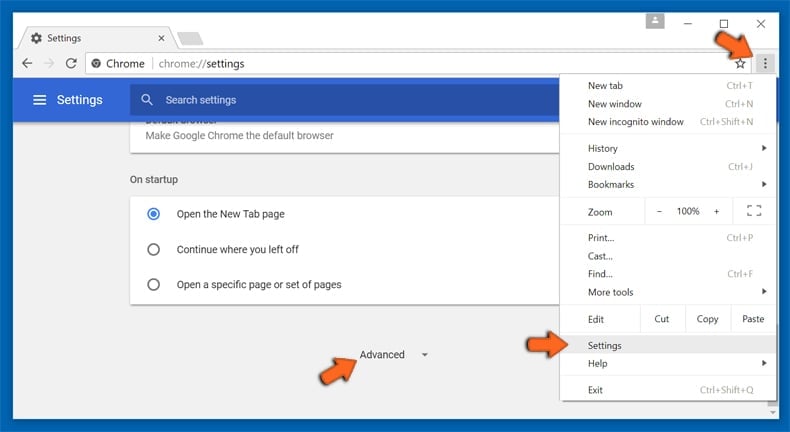
Optional method:
If you continue to have problems with removal of the grand explorer cryptocurrency miner, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
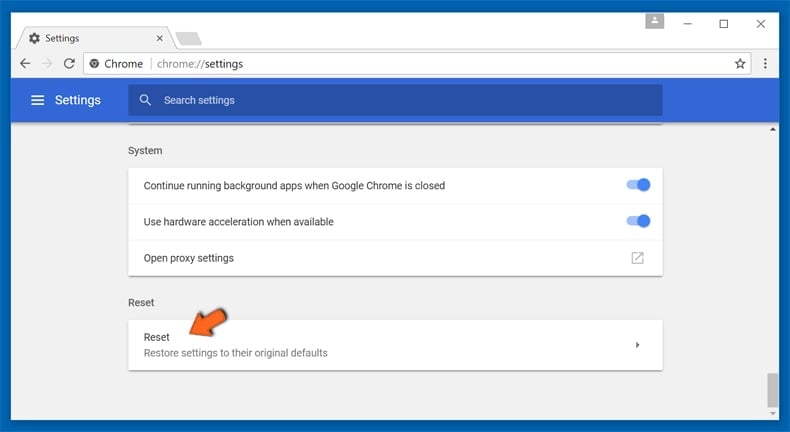
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
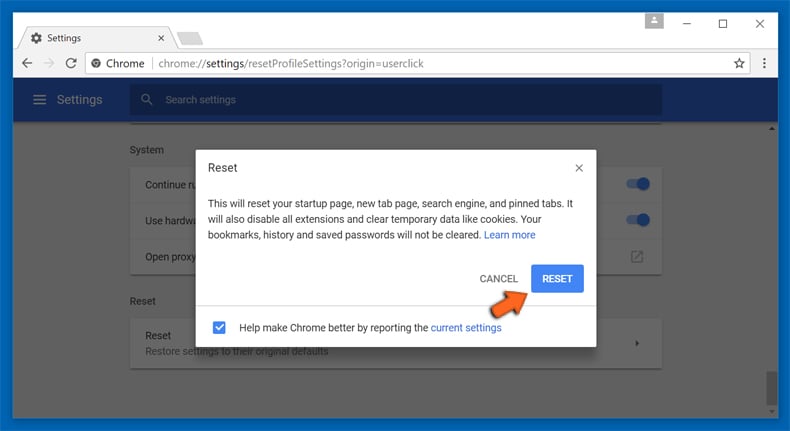
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious plug-ins from Mozilla Firefox:
Remove malicious plug-ins from Mozilla Firefox:
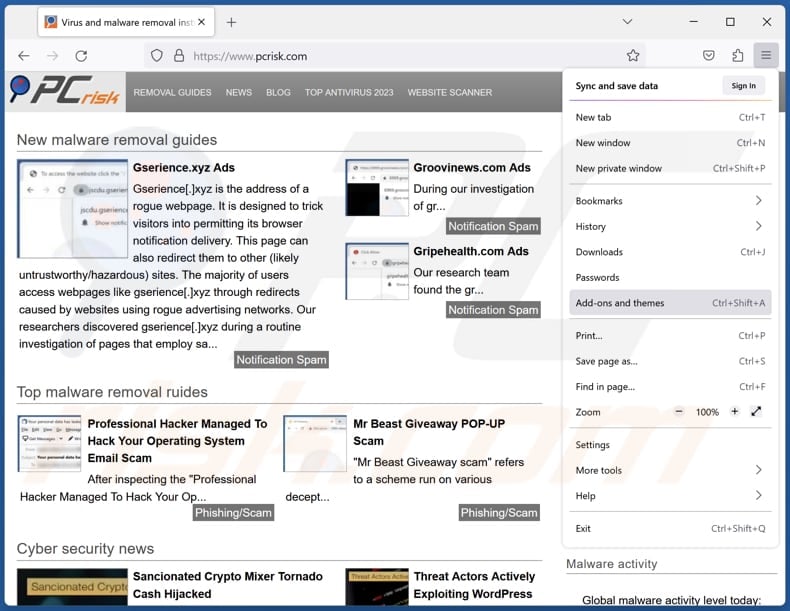
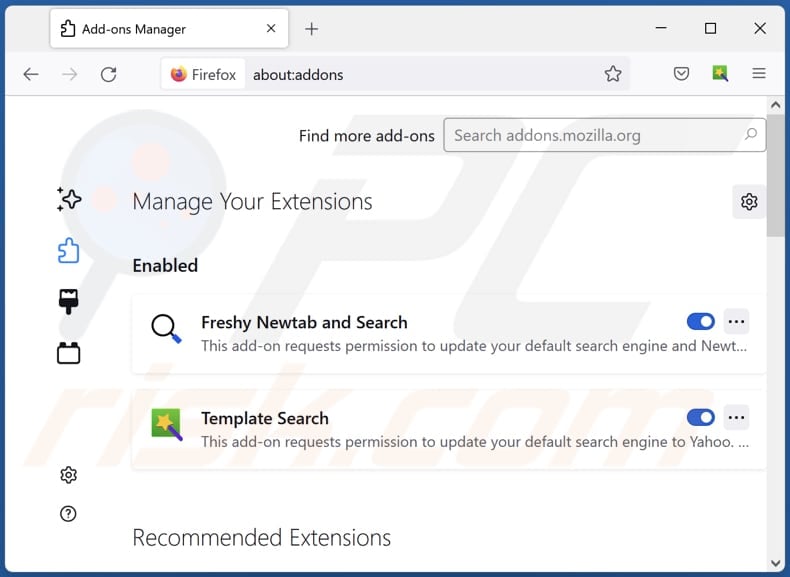
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
Optional method:
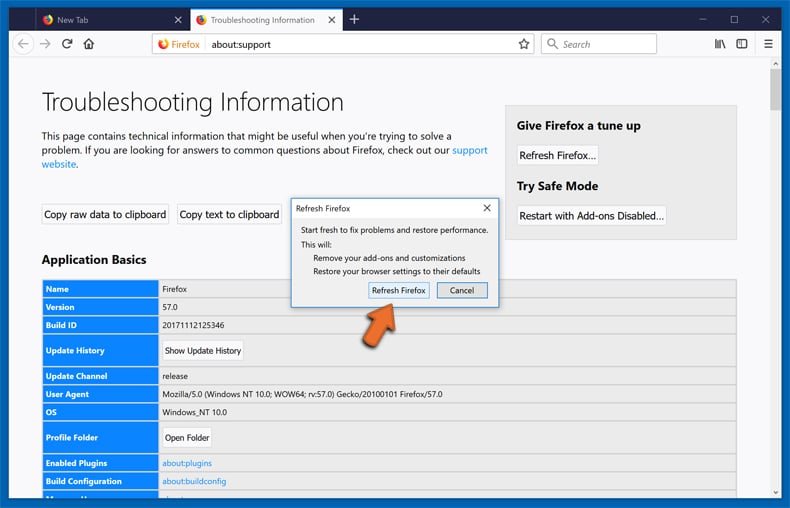
Computer users who have problems with grand explorer cryptocurrency miner removal can reset their Mozilla Firefox settings.
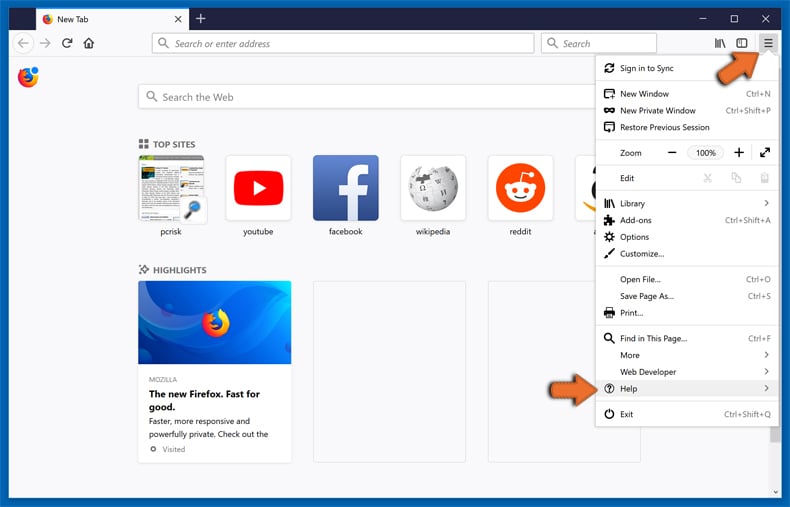
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
Select Troubleshooting Information.
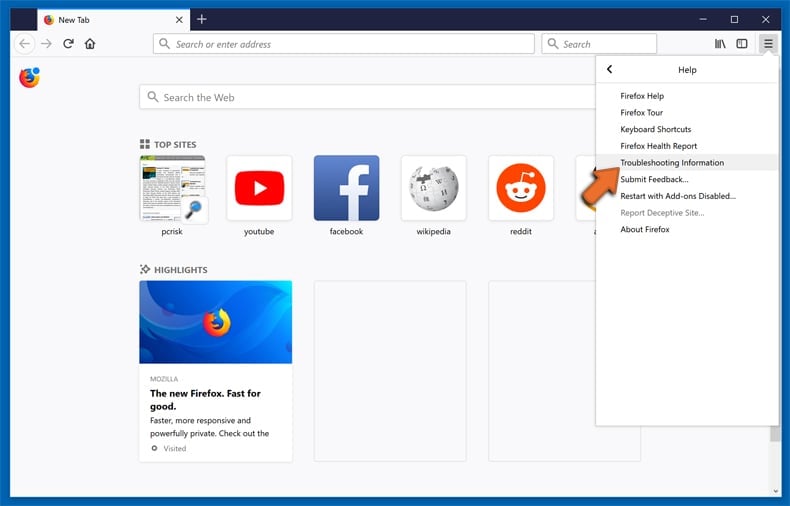
In the opened window, click the Refresh Firefox button.
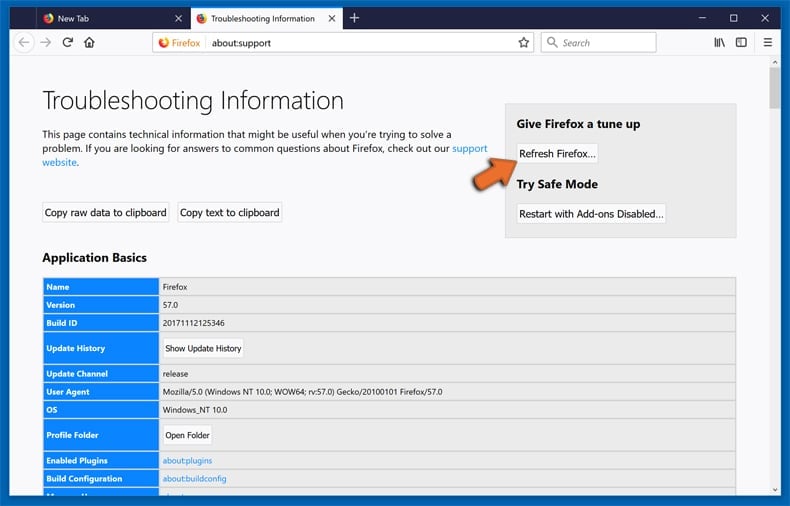
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
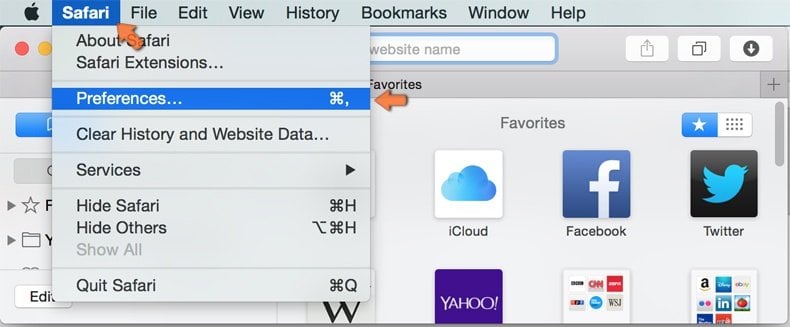
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
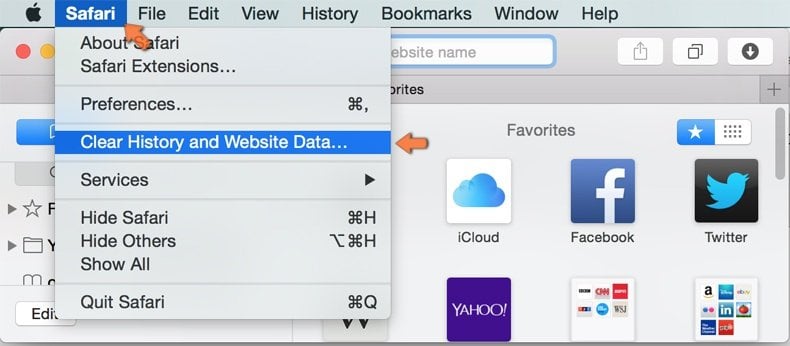
In the opened window select all history and click the Clear History button.

 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
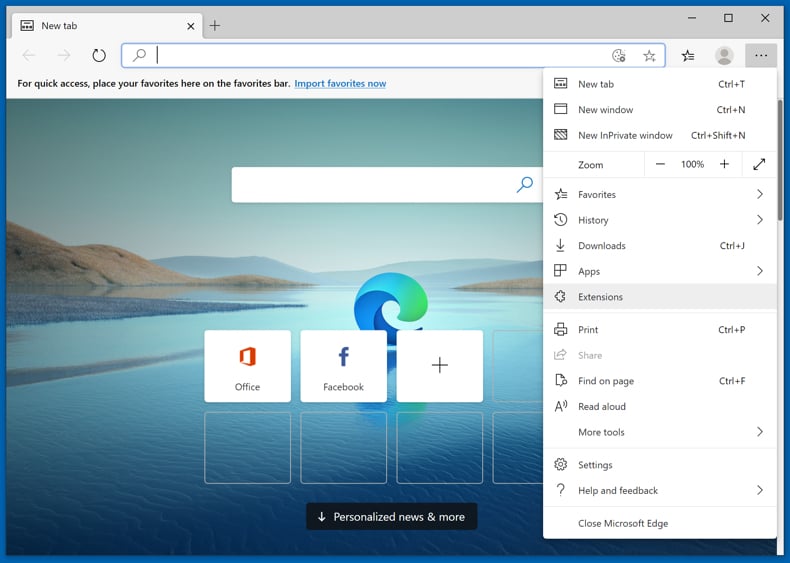
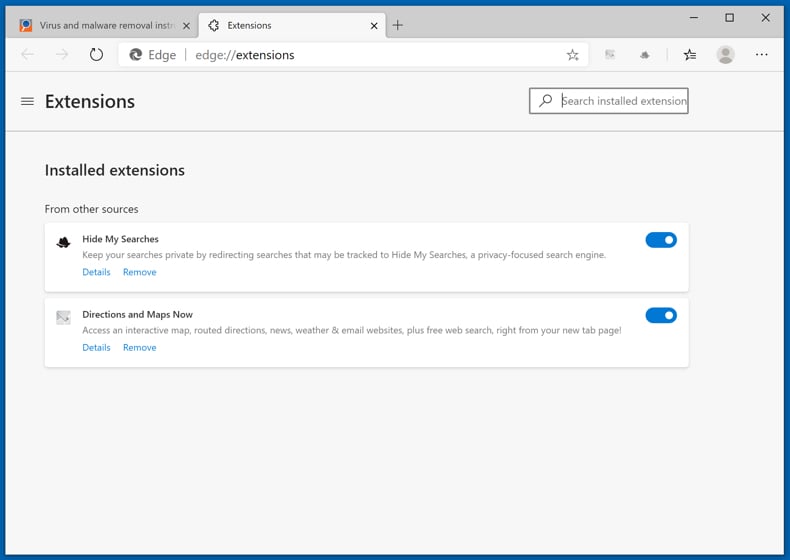
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
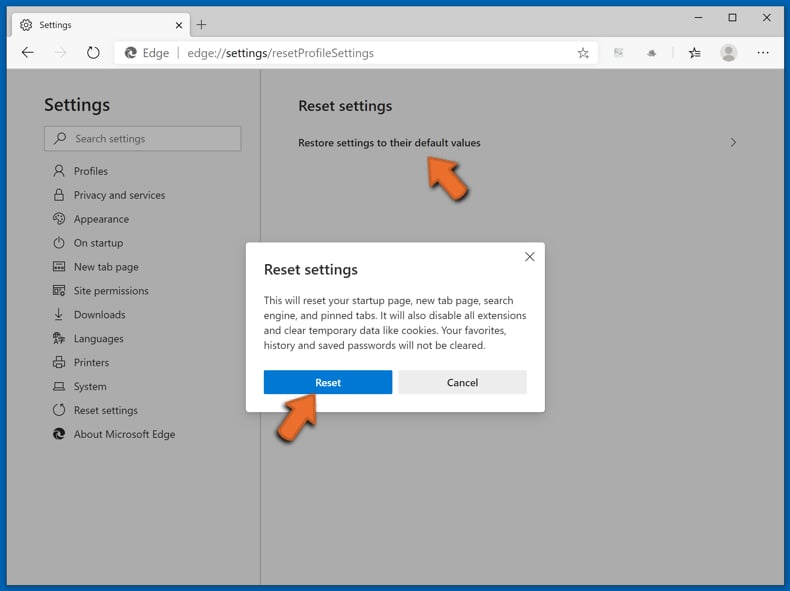
Optional method:
If you continue to have problems with removal of the grand explorer cryptocurrency miner, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
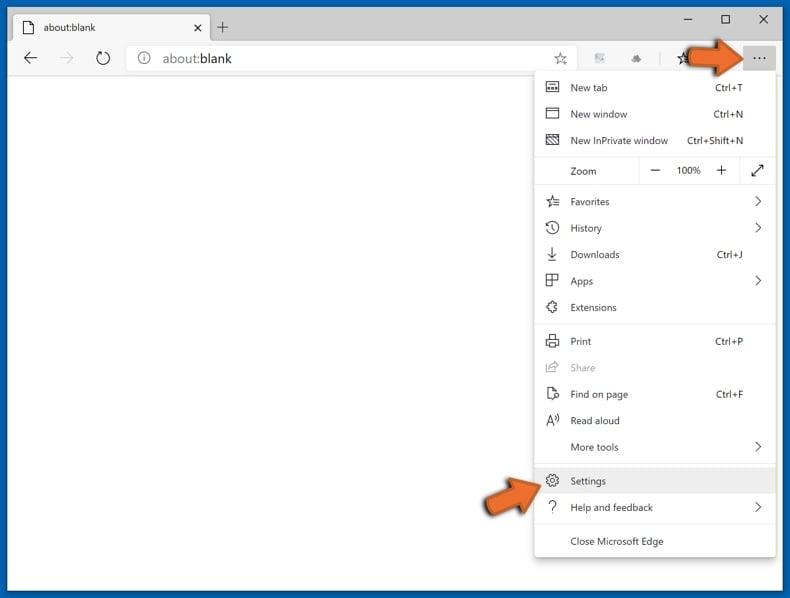
In the opened settings menu select Reset settings.
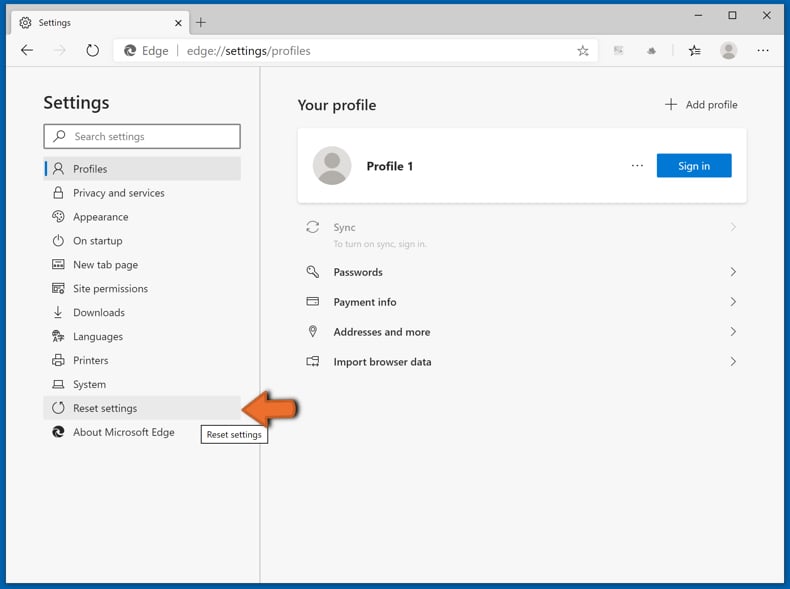
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
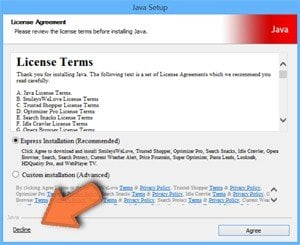 Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Post a comment:
If you have additional information on grand explorer cryptocurrency miner or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
What is the purpose of Grand Explorer?
The Grand Explorer app is presented as a tool designed to contribute to charitable causes by utilizing the idle time of a user's Windows computer. Specifically, it operates as a cryptocurrency miner, using the computer's hardware to solve equations and mathematical problems.
Is Grand Explorer application legal?
These applications are commonly considered lawful, as their End User License Agreements (EULA) usually reveal potential behaviors to users.
Is having Grand Explorer installed on my computer dangerous?
The installation of Grand Explorer on a computer may result in increased electricity costs, system crashes, diminished performance, and more. Additionally, the program has raised concerns for being bundled with other undesirable components, which could introduce security risks and trigger other undesirable consequences.
Will Combo Cleaner help me remove unwanted applications?
Combo Cleaner will scan your computer and eliminate malicious and unwanted applications. Manual removal may not always be exhaustive, as residual files can linger within the system. Thus, it is advisable to use a tool like Combo Cleaner for a more comprehensive solution.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion