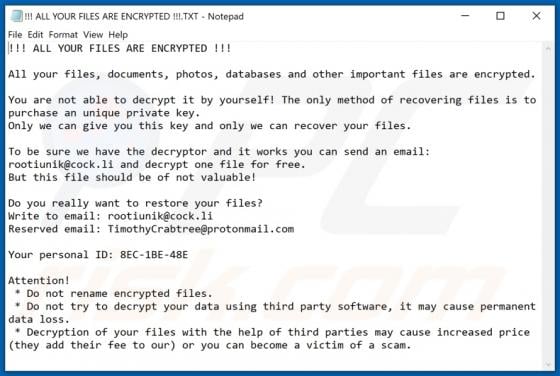
Rootiunik Ransomware
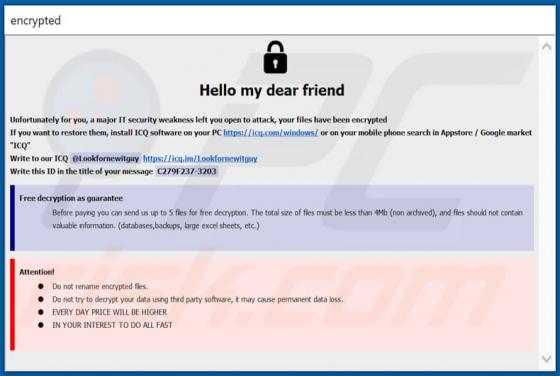
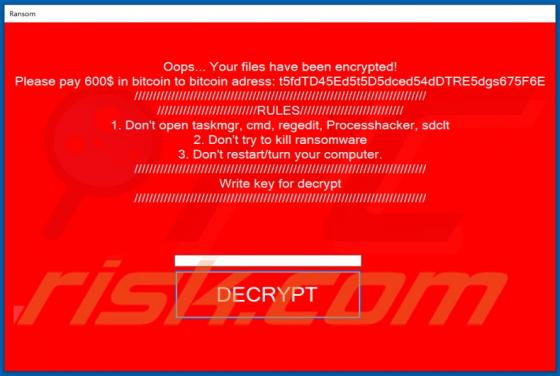
Rootiunik is a variant of the ZEPPELIN ransomware. Systems infected with this malware experience data encryption and receive ransom demands for the decryption. In other words, victims cannot use the files affected by Rootiunik, and are asked to pay - to recover access to them. During the encrypti