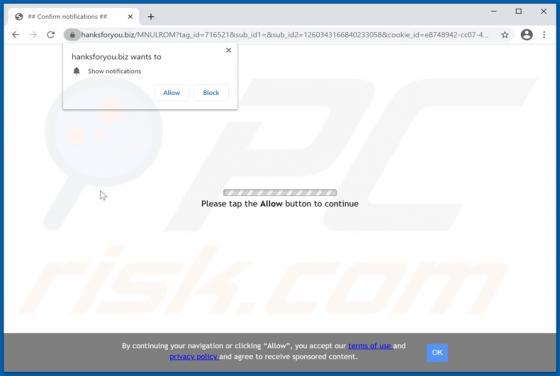
Hanksforyou.biz Ads
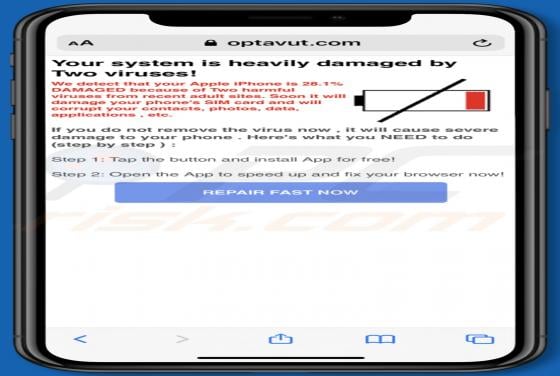
hanksforyou[.]biz is a rogue website designed to deliver dubious content and redirect visitors to other untrusted, possibly malicious web pages. Users rarely access hanksforyou[.]biz and similar sites intentionally - most are redirected to them by intrusive advertisements or installed Potentially