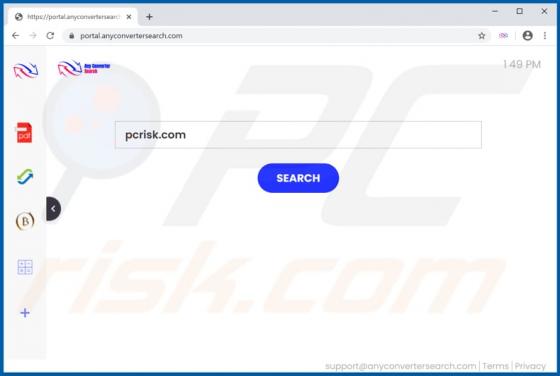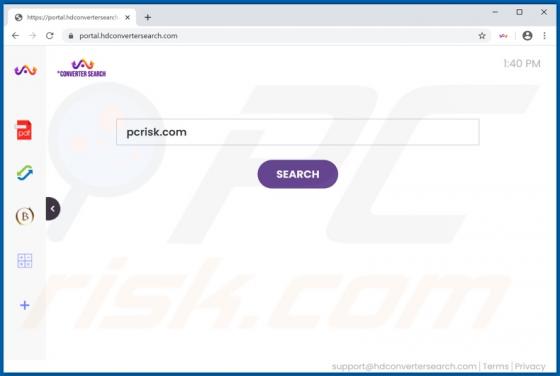
HDConverterSearch Browser Hijacker
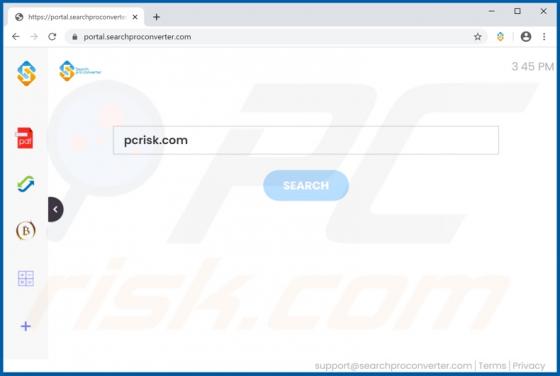
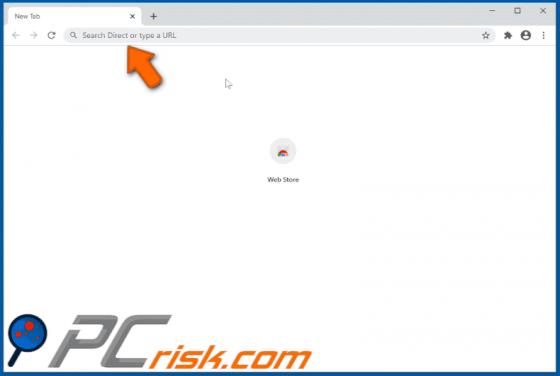
HDConverterSearch is dubious software endorsed as a tool capable of improving web searches. In fact, it operates by making alterations to browser settings to promote hdconvertersearch.com (a bogus search engine). Therefore, HDConverterSearch is categorized as a browser hijacker. Additionally, it