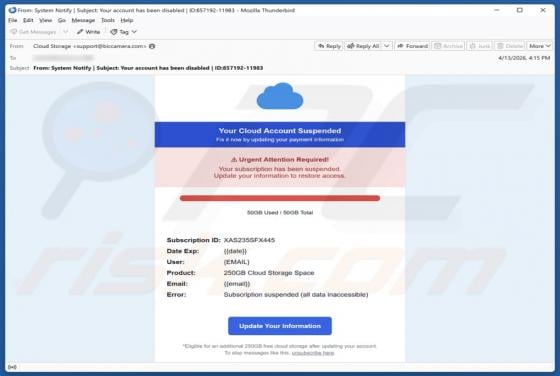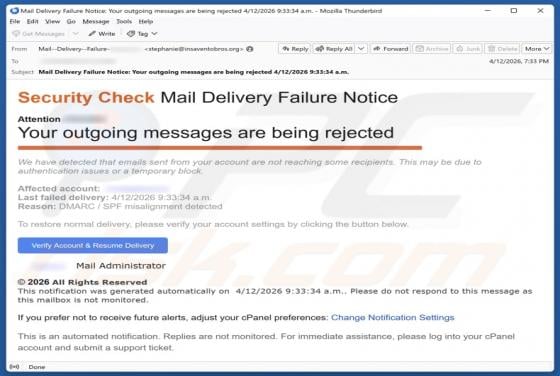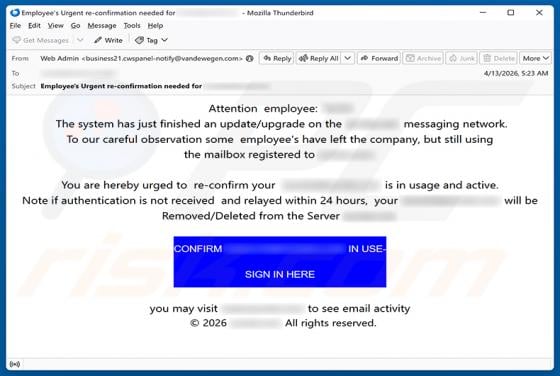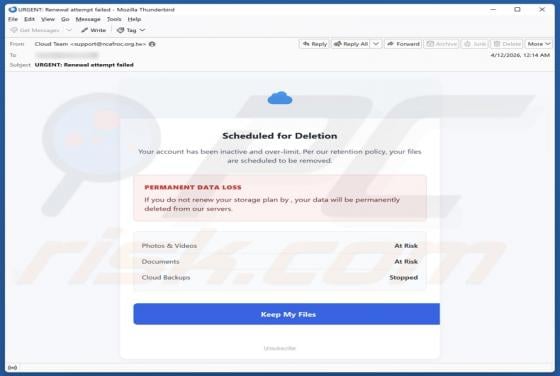
Cloud Account Scheduled For Deletion Email Scam
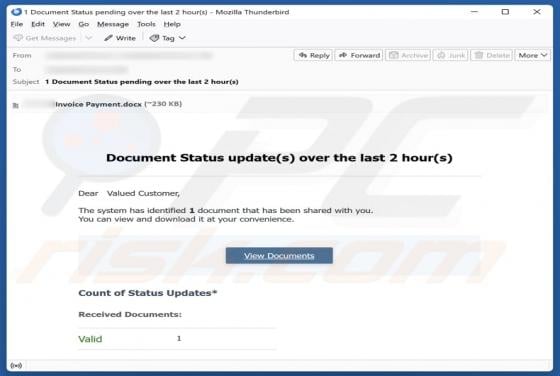
Our analysis indicates that this is a scam email intended to deceive recipients into thinking their cloud account has been scheduled for deletion. It directs users to fraudulent websites. All claims made in the email and on the linked sites are false and should not be trusted. If you receive this