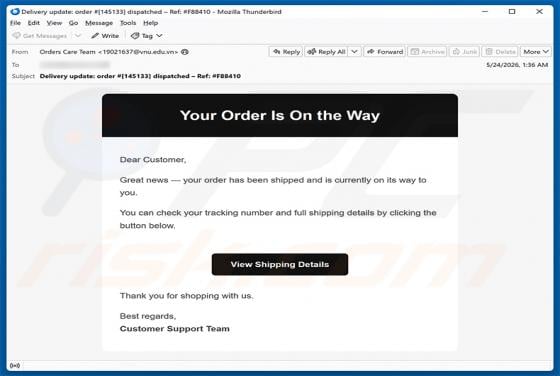
Your Order Is On The Way Email Virus
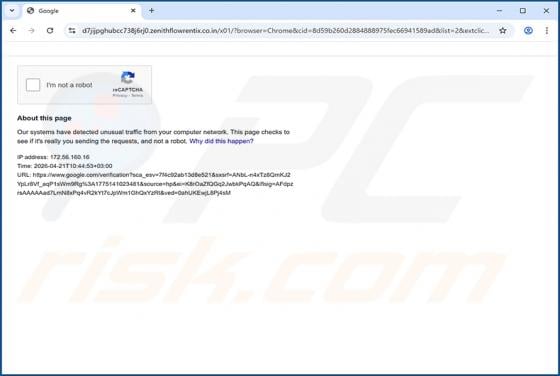
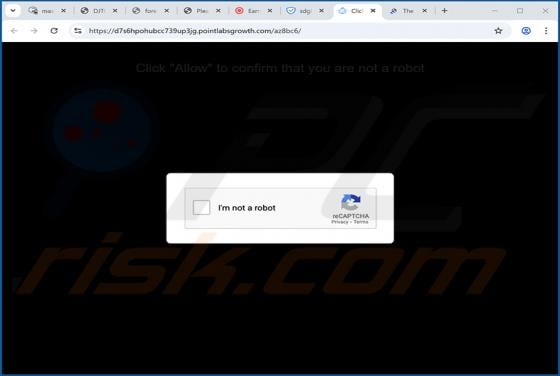
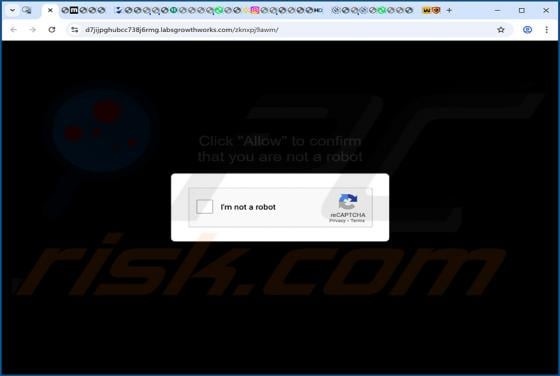
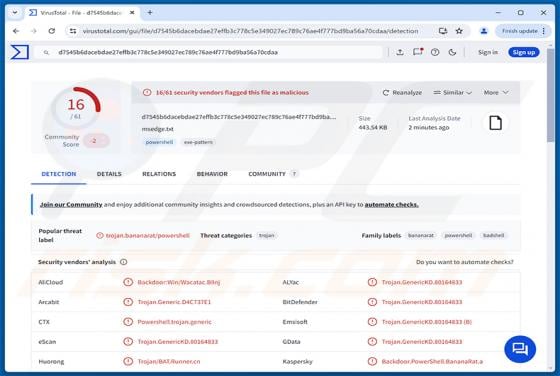
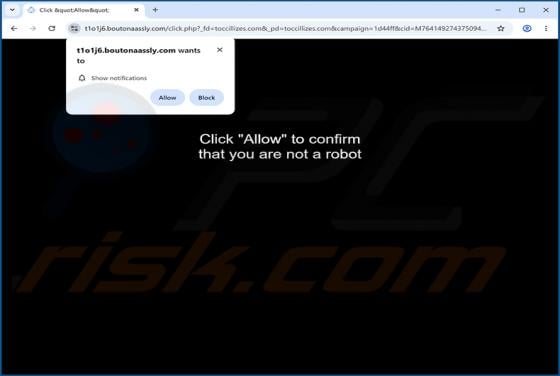
We analyzed this email and found it to be malspam. The message poses as a shipping notification, urging recipients to click a link to check their order and tracking details. The link leads to a fraudulent website that silently downloads a trojanized remote access tool onto the visitor's device. Th