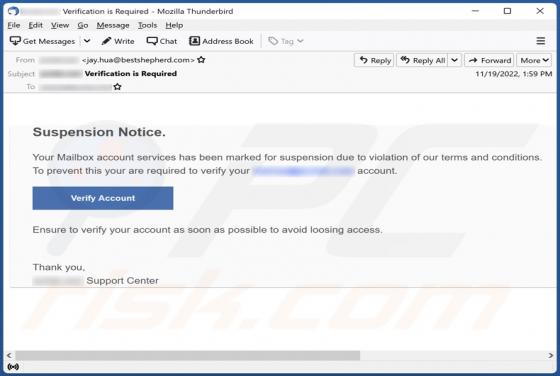
Large File Send Email Scam
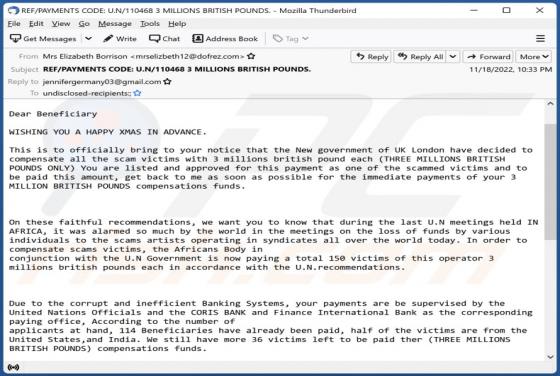
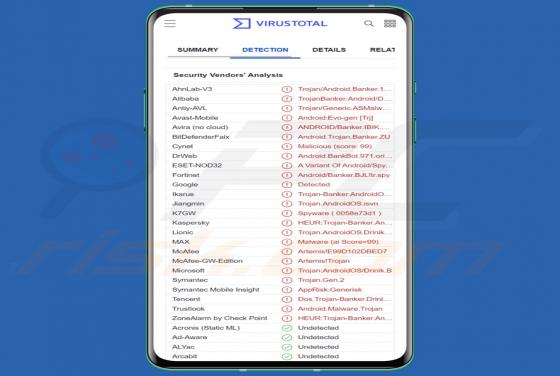
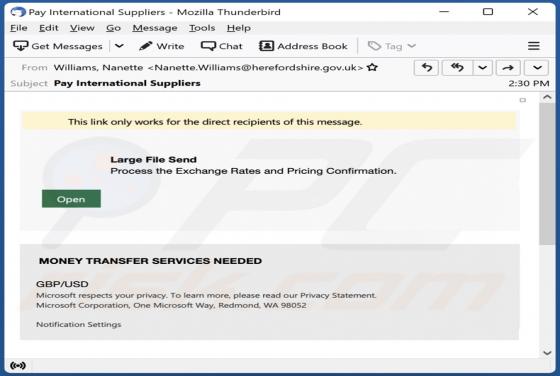
"Large File Send" is an email that our research revealed to be spam. This fake letter operates as a phishing scam targeting email account log-in credentials. It does so by claiming that a file sent to the recipient can only be accessed by following the provided link. The spam email with th