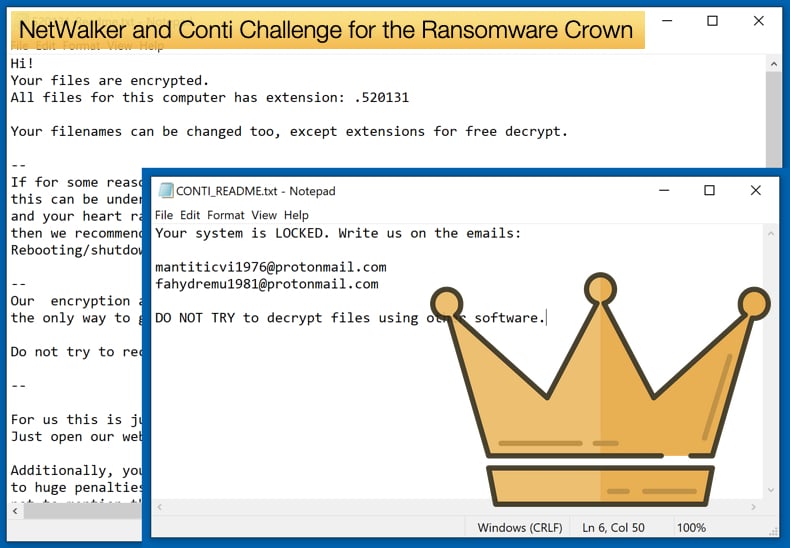
NetWalker and Conti Challenge for the Ransomware Crown
For security researcher’s ransomware has presented an ever-evolving threat readily capable of adapting and changing tactics. This rapid adoption of new tactics is seemingly driven by not only the rich rewards on offer but by competition with the rival ransomware gangs. According to recently published research, it would seem that two relatively new ransomware families are vying to be crowned king of the current ransomware threat. Further, it confirms that the number of ransomware attacks that threaten to release stolen data in the event of non-payment is growing.
The research conducted by Digital Shadows was published on their blog. The key takeaways from it are that a staggering 80% of known attacks were conducted by four ransomware families for the period of July to September. Those infamous four being Maze, Sodinokibi, NetWalker, and Conti. In the three months prior, DoppelPaymer was featured in the top three along with Maze and Sodinokibi. The sudden drop off in DoppelPaymer activity reflects the ever-changing ransomware threat landscape. This may also indicate how saturated the market has become and that to remain competitive tactics need to be continually refined and improved as well as a readiness to adopt new tactics. Maze is widely regarded as the first ransomware family to not only threaten the release of confidential data in the event the ransom is not paid in time but to release said data. Since then we have seen several other ransomware families adopt the tactic and start data release websites used to announce successful attacks and facilitate the release of stolen data.
It was noted that despite the apparent success of these ransomware gangs, NetWalker is believed to have earned 25 million USD during the period of March 2020 to August 2020, many of the gangs are still reliant on attack vectors that can be defended against.
In an interview with ZDNet, Alec Alvarado, cyber threat intelligence analyst at Digital Shadows, noted,
“Phishing is still a favored tactic of ransomware groups, so the common phishing mitigations apply here. Employee awareness and dedicated training around phishing that encapsulates exercises using simulated phishing emails help organizations reduce this threat,”
And summarising the current ransomware climate,
“There is an inherent competitive nature that has befallen the ransomware landscape. The saturated ransomware market pushes ransomware developers to cut through the noise and gain the best ransomware title,”
NetWalker
Taking a deeper dive into the two new rivals to the throne NetWalker presents an interesting case for the current ransomware landscape. Initially called Mailto, the gang has been active since April 2019, however, the gang seemed to refine their tactics and target large organizations to extort more funds in March of this year. This meant that the gang adopted a far more targeted and clinical approach when compared to the mass-distribution methods favored by the gang at its inception. This change has already netted the gang a substantial amount of success, with the first high-profile victim being the Toll group, an Australian logistics company. In June 2020, the FBI issued an alert warning US companies and government organizations that,
“As of June 2020, the FBI has received notifications of Netwalker ransomware attacks on U.S. and foreign government organizations, education entities, private companies, and health agencies by unidentified cyber actors. Netwalker became widely recognized in March 2020, after intrusions on an Australian transportation and logistics company and a U.S. public health organization. Cyber actors using Netwalker have since taken advantage of the COVID-19 pandemic to compromise an increasing number of unsuspecting victims… In April 2020, actors using Netwalker began gaining unauthorized access to victim networks by exploiting unpatched Virtual Private Network (VPN) appliances, vulnerable user interface components in web applications, or weak passwords used for Remote Desktop Protocol connections.”
What makes NetWalker unique amongst the other ransomware families is that the gang is a very closed group. Affiliates are thoroughly vetted before given access to the malware with one of the key requirements to be allowed on board is existing access to large and high-value networks. This provides those with privileged access an opportunity to work with the gang and profit from successful attacks. It is believed that the opportunity is often too sweet to ignore for a class of cybercriminal classified as “initial access brokers”. Typically, these brokers can access to networks via several methods including exploiting vulnerable VPNs and RDP connections, this access is then sold onto other malware operators. The more privileged the access the more they can ask for the pleasure. The NetWalker gang has clearly seen the advantages these brokers can provide to the operation and with the right kind of access, the task of stealing and encrypting data is made infinitely easier. To defend against NetWalker and other ransomware families the FBI advises:
- Back-up critical data offline.
- Ensure copies of critical data are in the cloud or on an external hard drive or storage device.
- Secure your back-ups and ensure data is not accessible for modification or deletion from the system where the data resides.
- Install and regularly update anti-virus or anti-malware software on all hosts.
- Only use secure networks and avoid using public Wi-Fi networks. Consider installing and using a VPN.
- Use two-factor authentication with strong passwords.
- Keep computers, devices, and applications patched and up-to-date.
Conti
Like NetWalker, Conti is a new ransomware family with activity regarding the ransomware starting in the middle of 2020. Conti is interesting in the sense that it is specifically designed to target network assets for encryption. This implies that the ransomware’s operators have set out to target high-value targets from the outset as hitting a few of these network assets can effectively cease operations. Conti has several other features, according to research conducted by Carbon Black that set it above a number of its competitors. The first being that the malware utilizes 32 separate threads when encrypting data improving speed and efficiency. Also, Conti has been developed to make use of several command-line instructions giving the attackers a higher level of control over the ransomware’s actions. It is a higher level of control that is responsible for Conti being able to ignore local files and target network assets directly. Further, the ransomware looks to abuse Windows Restart Manager, with the latter being the application responsible for closing other applications safely upon a reboot. Conti subverts the application to close any application before encryption so that even running applications can be encrypted.
According to several sources including Bleeping Computer and IBM’s Security Intelligence Conti may be the replacement for another heavy hitter amongst ransomware, Ryuk. It is yet to be proven beyond a shadow of a doubt Conti is indeed the direct replacement for Ryuk but there is a significant amount of evidence to link the two variants. Firstly, as Ryuk's activity seemed to decline, Conti activity increased proportionally. Further, there seems to be a strong link between the two party’s codebase. In 2017, a ransomware called Hermes became available for purchase on an underground hacking forum. It is widely believed that Ryuk was developed off Hermes. It is possible that some Ryuk operators split from the gang and developed Conti as the note used by Ryuk has also been seen used by Conti. The code Conti uses seems to be based on the second version of Ryuk sharing several similarities.
Another link has been seen in the triple threat partnership of TrickBot, Emotet, and Ryuk. In several instances, TrickBot would initially compromise a network, when the trojan was done it would create a backdoor onto the network. This backdoor was then used to drop Emotet on the network. Emotet would then drop Ryuk. Some security researchers have reported seeing Conti being distributed via TrickBot’s infrastructure. If there has indeed been a split between Ryuk operators the threat posed by Ryuk may not be lessened as the ransomware may evolve and be used in newer campaigns. This would also mean that Conti would continue to target high-value targets and notch up high-value victims. Those tasked with defending corporate or government networks are advised to follow the FBI’s advice reproduced above.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion