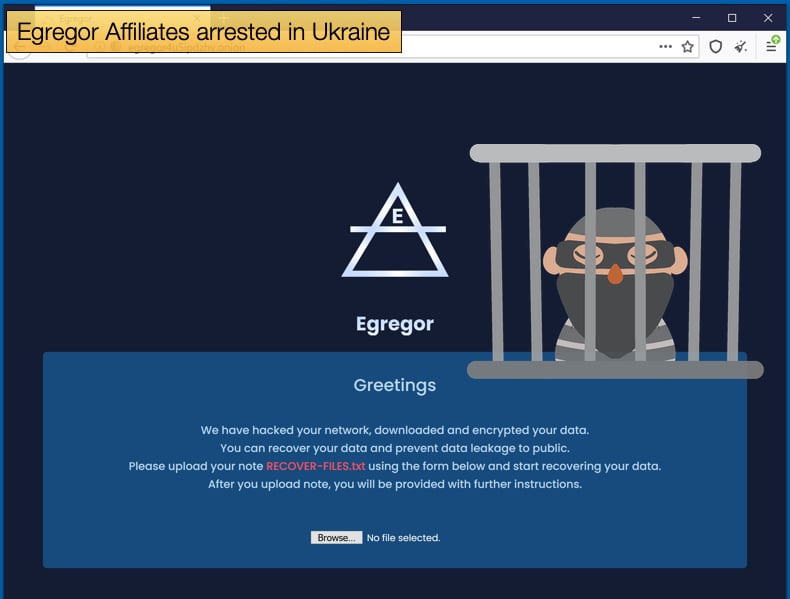
Egregor Affiliates arrested in Ukraine
In terms of law enforcement striking back at cybercriminals, the last few weeks have brought more than a few good stories. From two ransomware gangs ceasing operations in part due to collaborative law enforcement operations spanning several countries and there want to make up for some of the harm, they have caused. The law enforcement operations resulted in Emotet’s infrastructure being seized and the arrest of a Netwalker ransomware affiliate being arrested. Now, in a combined effort between French and Ukrainian law enforcement agencies, several affiliates of the Egregor have been arrested.
The news was initially broken by France Inter, with journalist Emmanuel Leclère noting that law enforcement made the arrests after French authorities could trace ransom payments to individuals located in Ukraine. The individuals arrested are believed to be hackers working in partnership with the creators of the ransomware to hack into corporate networks and deploy the ransomware. The InfoSec community refers to these individuals as affiliates.
A recent analysis of cryptocurrency transactions between affiliates and the creators, or admins, revealed that affiliates get the highest share of the earning as they take on the most risk. The most recent arrests of both Netwalker and Egregor affiliates prove the risks they take may not be worth it in the long run.
The Egregor ransomware gang seemed to draw the ire of French officials when several French organizations including Ubisoft, Ouest France, and, most recently Gefko fall victim to the ransomware. This prompted an investigation to be opened last fall by the Tribunal de Grande instance de Paris after receiving several complaints about the ransomware gang.
At the time of writing Bleeping Computer reported that Egregor's Tor websites are offline, including the payment site and the operation's data leak site. For those victims looking to pay the ransom, this may come as bad news as victims will be unable to contact ransomware operators, pay the ransom, and receive the decryption key necessary to decrypt data. Currently, it is not known if the website being offline as a result of law enforcement operations, however, the coincidences between both events will certainly lead to questions about a connection being asked.
Meteoric Rise
To say this is the last we will see of Egregor maybe a prediction made far too soon. As has been seen with TrickBot malware developers have proved difficult to pin down and bring a complete end to operations. That is not to say that the above arrests will have little to no impact. More information garnered from the arrests can lead to more and law enforcement agencies over the last several years have proved that they are willing to work across borders to help bring the victims of cybercrimes some justice. Further, by targeting the affiliates the distribution of the ransomware can be severely limited and some may refrain from spreading the ransomware knowing that they can be found and arrested.
Egregor’s rise is something of a fairy tale story. Ransomware operation began in earnest in September 2020, just as the Maze admins announced they were ceasing operations. The timing of both events led to researchers seeing if there is some kind of a connection between the ransomware strains and those behind them. Recent analysis, mentioned above, by Chainalysis, strengthens the case of a connection but definitive proof is needed to say for certain. At the time when Maze left stage left and Egregor entered stage right, there were whisperings that Maze affiliates had migrated to Egregor’s infrastructure. Then came the news that Egregor had partnered with the botnet QBot to further help distribute the ransomware to a new spectrum of victims.
This resulted in the number of victims being too large to handle for the ransomware's admins, and victims being placed in a queuing system by December 2020, just to speak with the party responsible for encrypting large portions of their corporate network. However, soon it began to become clear that this meteoric rise was having some unpredictable consequences. Also, in December researchers noticed that there was a steep drop off in Egregor detections and activity. This was followed by the Tor website being offline for two weeks in January.
When the site was returned online, several threat actors noticed several issues with the website and suspected the site was either hacked or breached by law enforcement. Despite the struggles according to security firm Kivu, in a newly published report, Egregor has amassed over 200 victims since it launched and is comprised of 10-12 core members and 20-25 semi-exclusively vetted members. Kivu’s researchers concluded that,
“Kivu’sThreat Intelligence team assesses Egregor’s Ransomware as a Service group alludes to international violations of organized crime by scaling at a contractual level based on the size of the attack. The economics of using contracted affiliates and time spent within a victim’s network directly affects the size of the extortion demands sought by the group. While these variables are two driving vectors of rising extortion demands, an attackers’ perception of the victim’s ability to pay continues to exhibit significance.”
Kivu’s conclusion mirrors that of tactics shared by the major ransomware gangs currently making up the threat landscape. However, if law enforcement operations are indeed increasing as the increase in new articles may suggest the Ransomware as a Service business model may need to adapt or die.
US Government looks to Boost Cyber Crime Enforcement
Both the dismantling of Emotet and the arrest of a Netwalker affiliate involved US law enforcement and the Department of Justice. Legal experts are suggesting that this comes in the wake of the US government realizing ransomware needs to be combated. In 2020, ransomware attacks on US businesses increased by 311%. Officials have established a two-prong attack methodology. The first prong involves the searching for and seizing of servers. As these are often outside of the US operations will need to involve a strong collaborative effort with international law enforcement agencies as well as those of independent nations.
This has been seen to be the case regarding both Egregor and Emotet, the latter was used to spread ransomware. The seizing of infrastructure severely limits the ransomware’s admins to receive ransom payments and send decryption keys. Going after the affiliates will hopefully limit how the ransomware is distributed and victims created.
The second prong involves warning US businesses that there may be legal repercussions to paying the ransom. As experts pointed out,
“In October, the Financial Crimes Enforcement Network (FinCEN) released an advisory “to alert financial institutions to predominant trends, typologies, and potential indicators,” specifically as it pertains to ransomware payments processed through these businesses. As FinCEN noted, financial institutions play a “critical role” in the collection of ransom payments in that the victim typically transmits ransom payments via wire transfer or credit card payment processed by financial institutions that are then sent to a convertible virtual currency exchange before being deposited in the perpetrator’s account. FinCEN has reminded these entities that they are required to register with FinCEN, are subject to the monitoring and reporting requirements of the Bank Secrecy Act, and are required to file suspicious activity reports should they observe conduct consistent with ransomware payments. Likewise, the Office of Foreign Assets Control (OFAC) recently advised financial institutions that they could be subject to sanctions if they facilitate ransomware payments. Therefore, to both satisfy their legal obligations and to avoid the possibility that the U.S. government could find that a financial institution’s failure to adequately monitor and report such conduct gives rise to criminal or civil liability on behalf of the financial institution, all financial institutions should ensure that their AML programs are designed to identify the red flags evincing potential ransomware attacks and that there are sufficient controls in place to stop the payment of a ransom demand when detected.”
It is sincerely hoped that these developments are followed by further law enforcement operations looking to bring some of ransomware’s other big names into line.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion