Avoid infecting your device with malware via fake "DHL Express" emails
Phishing/ScamAlso Known As: DHL Express spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "DHL Express" email virus?
"DHL Express Email Virus" is a spam email campaign used to proliferate a high-risk trojan called LokiBot. Cyber criminals send thousands of deceptive emails encouraging users to open attached Microsoft Office documents. This leads to infiltration of the LokiBot trojan.

"DHL Express" email virus overview
"DHL Express Email Virus" campaign emails are essentially notifications of received packages. The messages state that users have received packages and encourage them to read attached documents for detailed information. This is a scam. The attached document infects the system.
Be aware that DHL is a legitimate delivery company and has nothing to do with this spam campaign. Cyber criminals often hide behind names of popular companies and governmental agencies. They do this to increase the number of infections, since users are much more likely to open files when they are received from familiar names.
LokiBot is a high-risk trojan designed to record personal data, such as logins/passwords, web browsing data, and so on. Therefore, LokiBot's developers might gain access to users' personal accounts on social networks, banks, etc. These people aim to generate as much revenue as possible and there is a high probability that hacked accounts will be misused.
The presence of an information-tracking virus such as LokiBot can lead to significant financial loss and even identity theft. If you have already opened "DHL Express Email Virus" campaign attachments, there is a high probability that your computer is infected. Therefore, scan it with a legitimate anti-virus/anti-spyware suite and eliminate all threats.
| Name | DHL Express spam |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Malware-proliferating spam campaigns in general
"Apple Recent Purchase Email Virus", "Payroll Timetable Email Virus", and "Companies House Email Virus", are a few examples of malware-spreading spam campaigns.
LokiBot shares many similarities with dozens of other trojans that are also proliferated using spam emails. The list of examples includes (but is not limited to) TrickBot, Adwind, Emotet, and FormBook.
Behavior might slightly differ (some track information, others proliferate malware, and so on), but all of these viruses have one thing in common - they pose a significant threat to your privacy and computer safety. Therefore, eliminate trojan-type viruses immediately.
How did DHL Express Email Virus infect my computer?
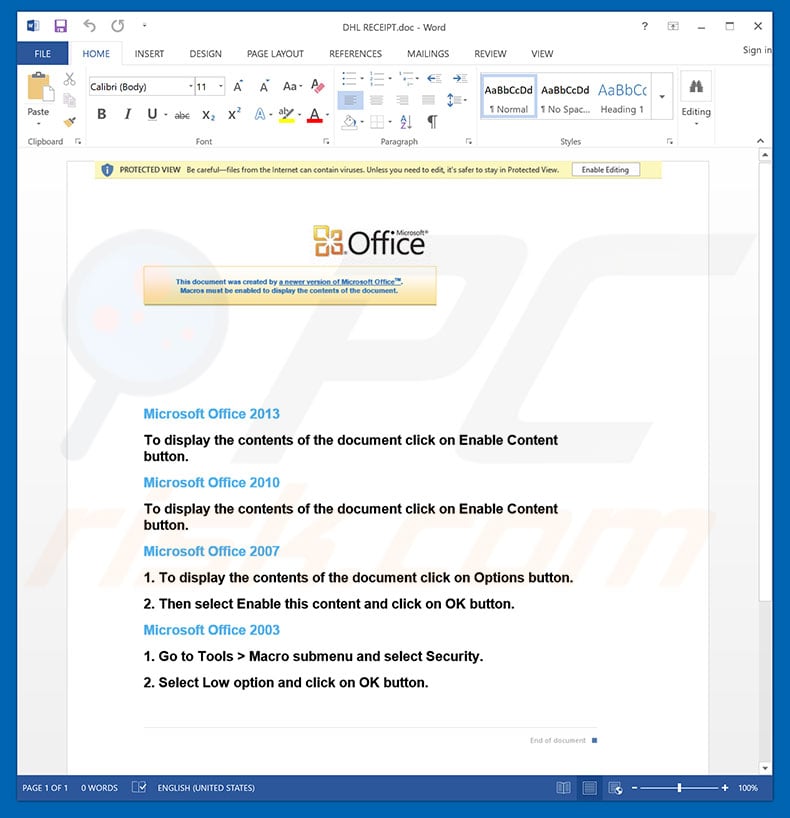
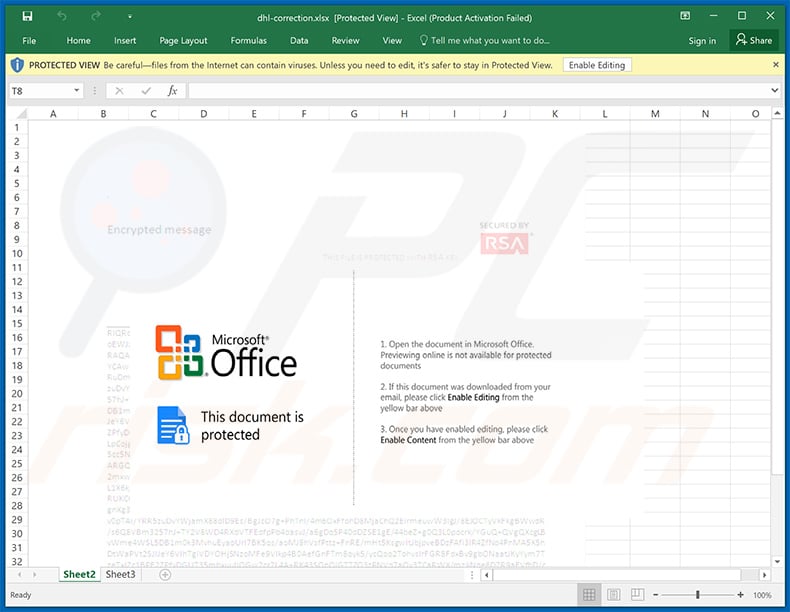
As mentioned above, the "DHL Express Email Virus" campaign proliferates an infectious MS Office attachment. The document immediately asks victims to enable macro commands, otherwise content will not be displayed properly. In doing so, however, users inadvertently grant attachments permission to execute commands that download and install LokiBot onto the system.
This malware distribution method is simple and extremely effective. Note, however, is that it works only if the user opens the document using tools from MS Office. For example, if a .doc file is opened using any application other than MS Word, the malware will not be downloaded.
Furthermore, LokiBot works on Microsoft Windows and Google Android operating systems only. Users of other platforms are safe.
How to avoid installation of malware?
To prevent this situation, be very cautious when browsing the Internet. Think twice before opening email attachments. Files that seem irrelevant and those received from suspicious/unfamiliar email addresses should never be opened.
Furthermore, have a reputable anti-virus/anti-spyware suite installed and running, since these tools are very likely to detect and terminate malicious files before they harm the system. 2010 and newer versions of MS Office open newly-downloaded documents in "Protected View" mode. This prevents malicious attachments from infecting the system.
Therefore, using older versions is risky. The main reasons for computer infections are poor knowledge and careless behavior. The key to safety is caution. If you have already opened "DHL Express Email Virus" attachment, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "DHL Express Email Virus" email message:
Subject: ARRIVAL NOTICE
Dear Customer
Your shipment has arrived!
Arrival Information
Your package has been arrived to your local DHL office and it’s ready for pick up.
——————————————
ARRIVAL NOTICE
——————————————
DATE & TIME : 2018-09-14 at 4:15
STATUS : Shipment arrived
CLASS: Package services
************************
Please print the receipt that is attached to this email and visit DHL location indicated in the receipt
DHL WorldWide Delivery
Malicious attachment distributed via "DHL Express Email Virus" spam campaign:
Example of yet another DHL Express spam email distributing a malicious .iso file ("gskfyc.iso"):
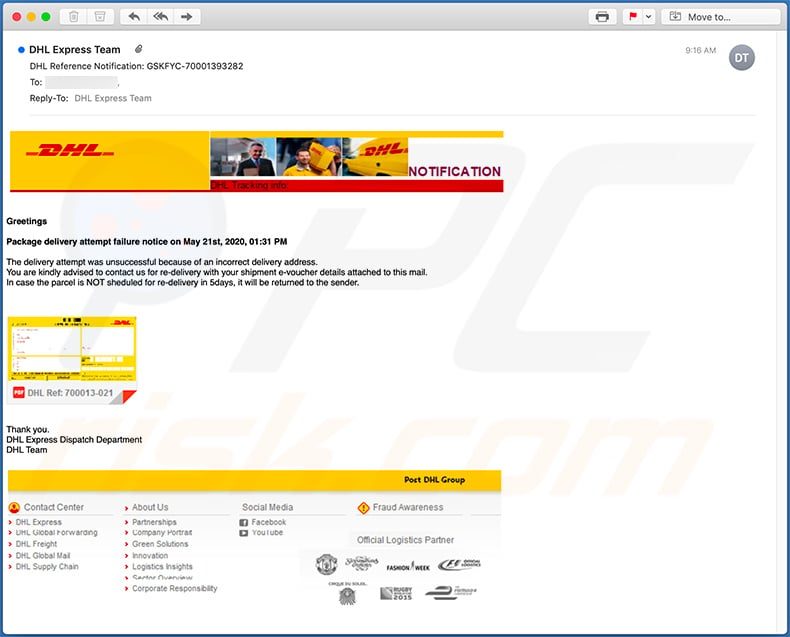
Text presented within:
Subject: DHL Reference Notification: GSKFYC-70001393282
Greetings
Package delivery attempt failure notice on May 21st, 2020, 01:31 PM
The delivery attempt was unsuccessful because of an incorrect delivery address.
You are kindly advised to contact us for re-delivery with your shipment e-voucher details attached to this mail.
In case the parcel is NOT sheduled for re-delivery in 5days, it will be returned to the sender.Thank you.
DHL Express Dispatch Department
DHL Team
Example of a DHL Express-themed spam email which is used to spread AgentTesla malware:
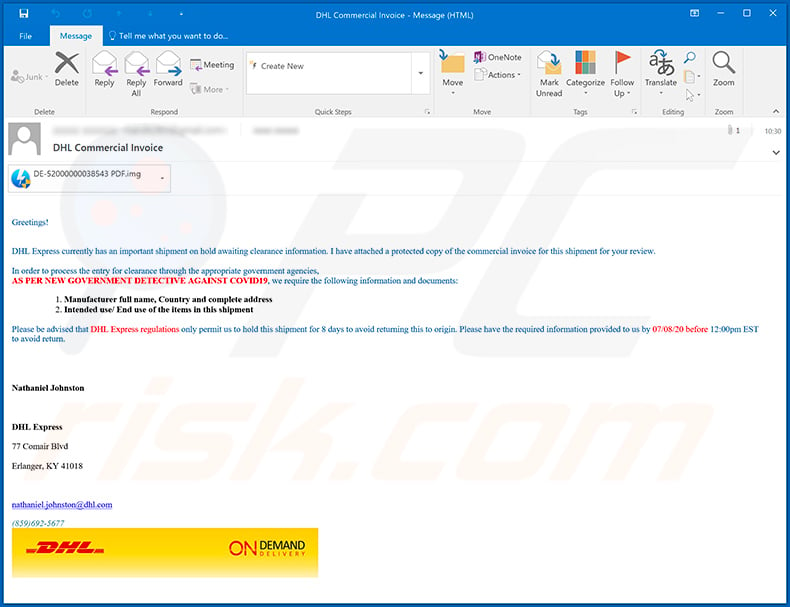
Text presented within:
Subject: DHL Commercial Invoice
Greetings!
DHL Express currently has an important shipment on hold awaiting clearance information. I have attached a protected copy of the commercial invoice for this shipment for your review.In order to process the entry for clearance through the appropriate government agencies,
AS PER NEW GOVERNMENT DETECTIVE AGAINST COVID19, we require the following information and documents:1. Manufacturer full name, Country and complete address
2. Intended use/ End use of the items in this shipmentPlease be advised that DHL Express regulations only permit us to hold this shipment for 8 days to avoid returning this to origin. Please have the required information provided to us by 07/08/20 before 12:00pm EST to avoid return.
Nathaniel JohnstonDHL Express
77 Comair Blvd
Erlanger, KY 41018
nathaniel.johnston@dhl.com
(859)692-5677
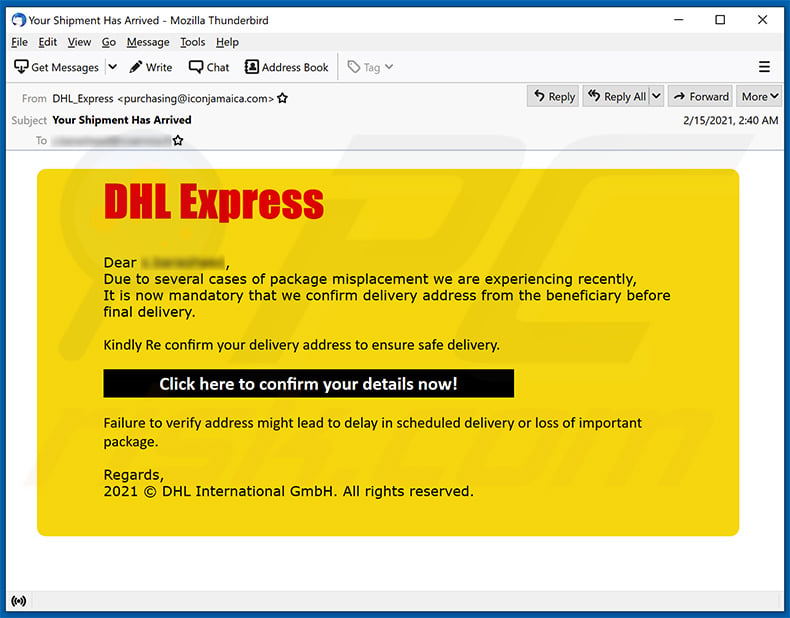
A variant of DHL Express-themed spam email used to promote a phishing website:
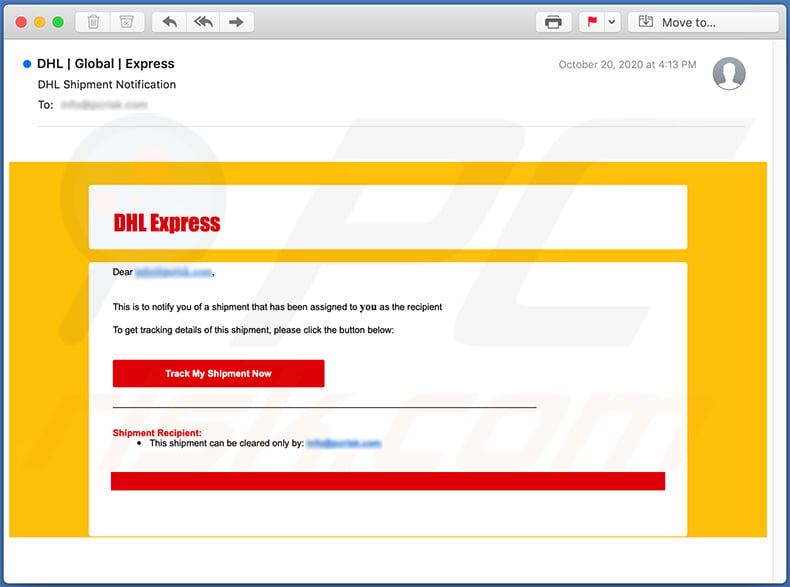
Text presented within:
Subject: DHL Shipment Notification
DHL Express
Dear -,
This is to notify you of a shipment that has been assigned to you as the recipient
To get tracking details of this shipment, please click the button below:
Track My Shipment Now
Shipment Recipient:
This shipment can be cleared only by: -DHL Express Worldwide 2020.
Screenshot of the promoted phishing site:
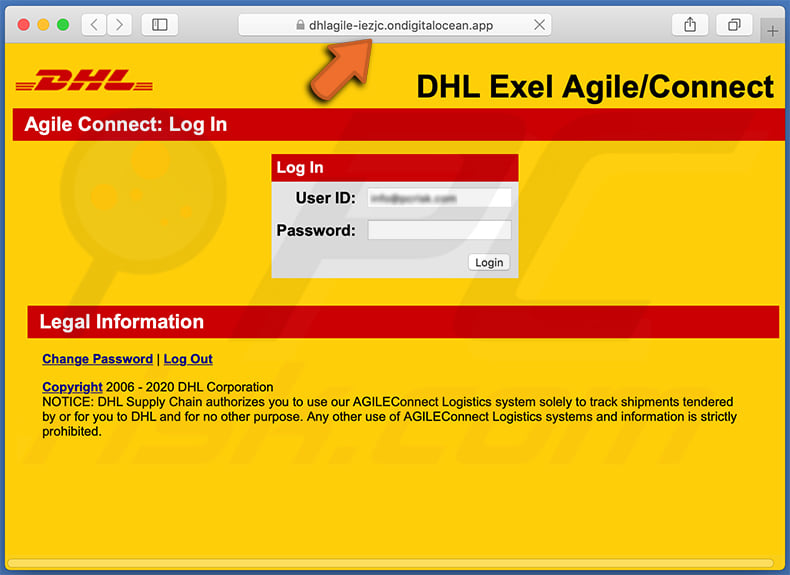
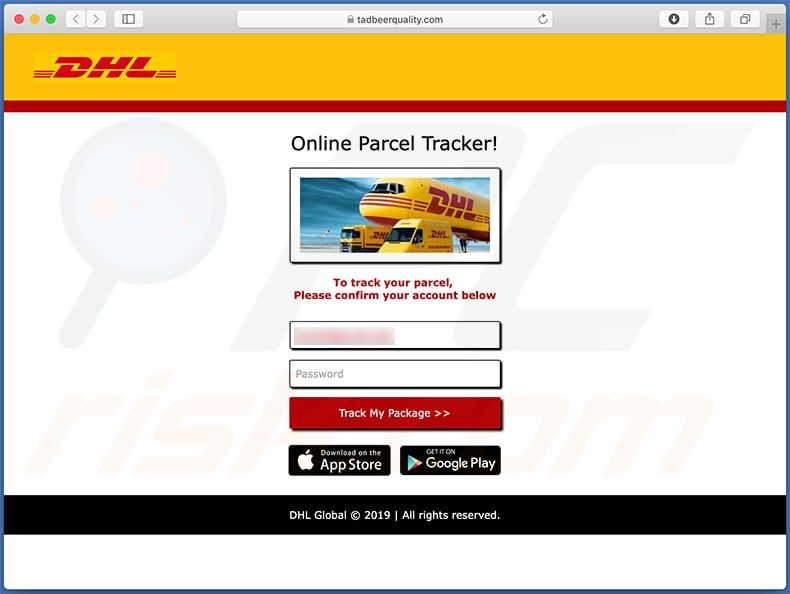
Another phishing website promoted via an identical spam email:
An Italian variant of DHL Express spam email used to promote a phishing website:
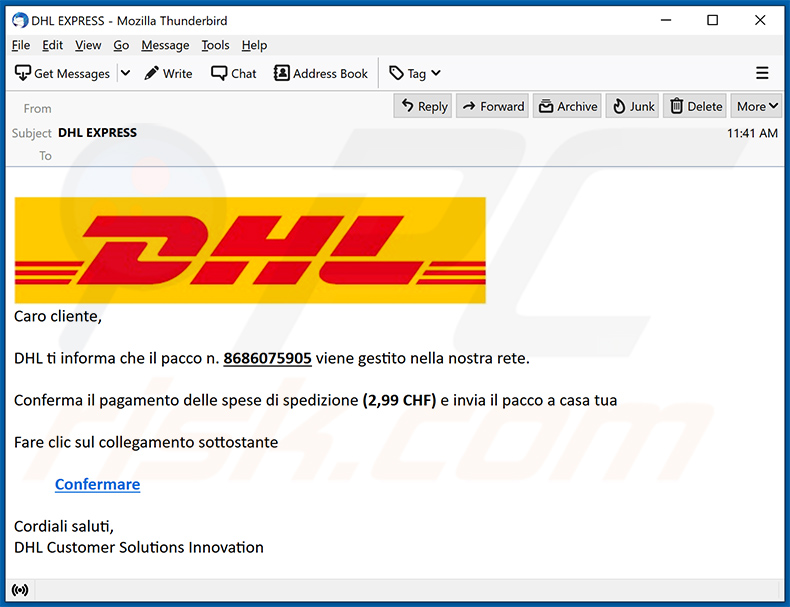
Text presented within:
Subject: DHL EXPRESS
Caro cliente,
DHL ti informa che il pacco n. 8686075905 viene gestito nella nostra rete.
Conferma il pagamento delle spese di spedizione (2,99 CHF) e invia il pacco a casa tua
Fare clic sul collegamento sottostante
Confermare
Cordiali saluti,
DHL Customer Solutions Innovation
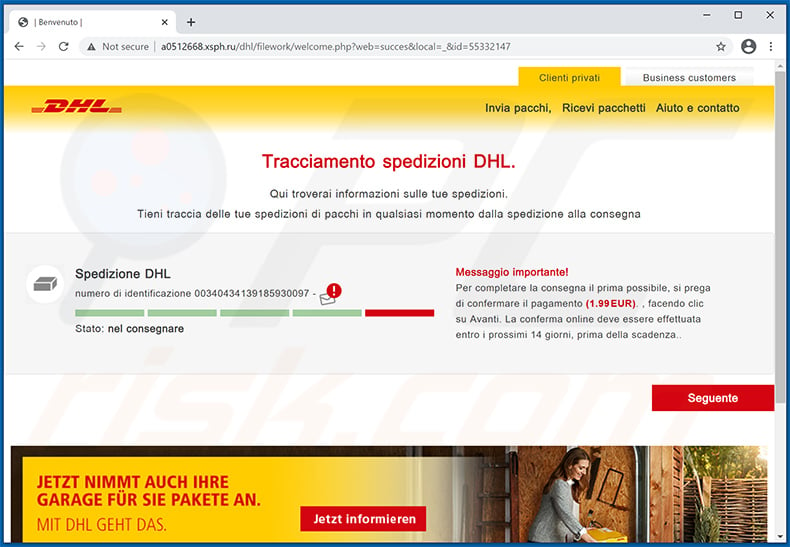
Screenshot of the promoted phishing site:
An example of DHL Express-themed spam email used to spread a malicious MS Excel document (the link within this email downloads the document):
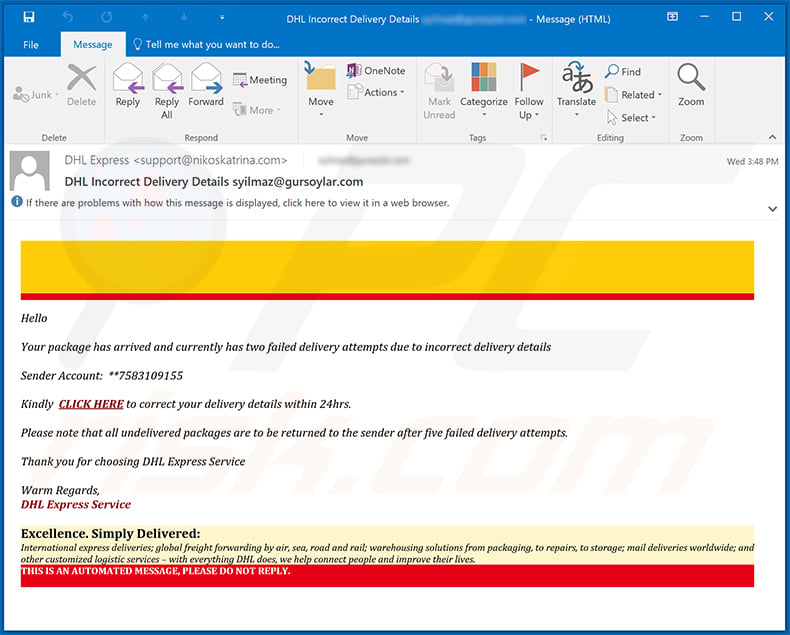
Text presented within:
Subject: DHL Incorrect Delivery Details
Hello
Your package has arrived and currently has two failed delivery attempts due to incorrect delivery details
Sender Account: **7583109155
Kindly CLICK HERE to correct your delivery details within 24hrs.
Please note that all undelivered packages are to be returned to the sender after five failed delivery attempts.
Thank you for choosing DHL Express ServiceWarm Regards,
DHL Express Service
Excellence. Simply Delivered:
International express deliveries; global freight forwarding by air, sea, road and rail; warehousing solutions from packaging, to repairs, to storage; mail deliveries worldwide; and other customized logistic services – with everything DHL does, we help connect people and improve their lives.
THIS IS AN AUTOMATED MESSAGE, PLEASE DO NOT REPLY.
Screenshot of the malicious Excel document:
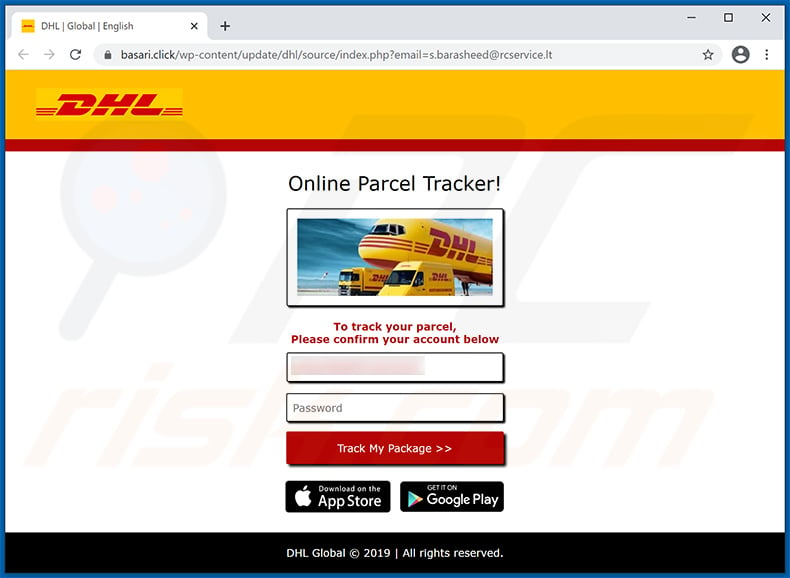
Another example of DHL Express-themed spam email used to promote a phishing website:
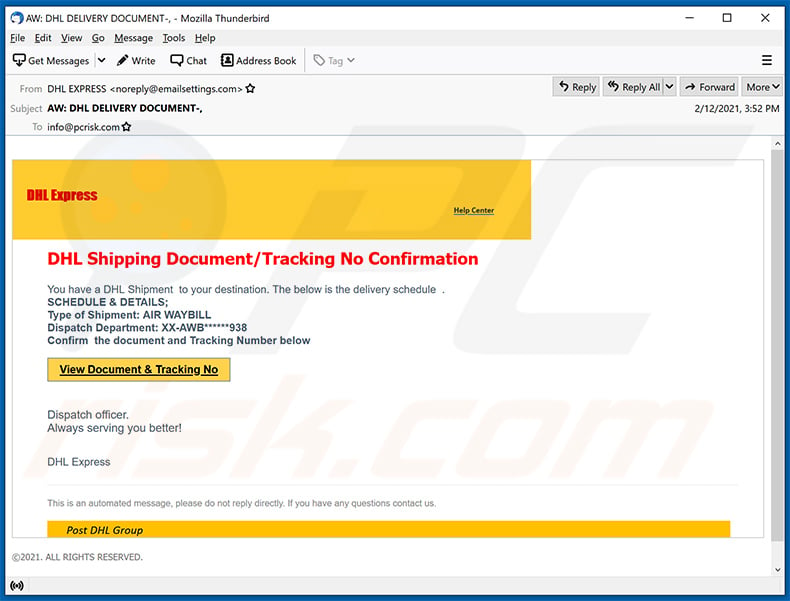
Text presented within:
Subject: AW: DHL DELIVERY DOCUMENT
DHL Express
Help Center
DHL Shipping Document/Tracking No Confirmation
You have a DHL Shipment to your destination. The below is the delivery schedule .
SCHEDULE & DETAILS;
Type of Shipment: AIR WAYBILL
Dispatch Department: XX-AWB******938
Confirm the document and Tracking Number below
View Document & Tracking No
Dispatch officer.
Always serving you better!DHL Express
This is an automated message, please do not reply directly. If you have any questions contact us.
Post DHL Group©2021. ALL RIGHTS RESERVED.
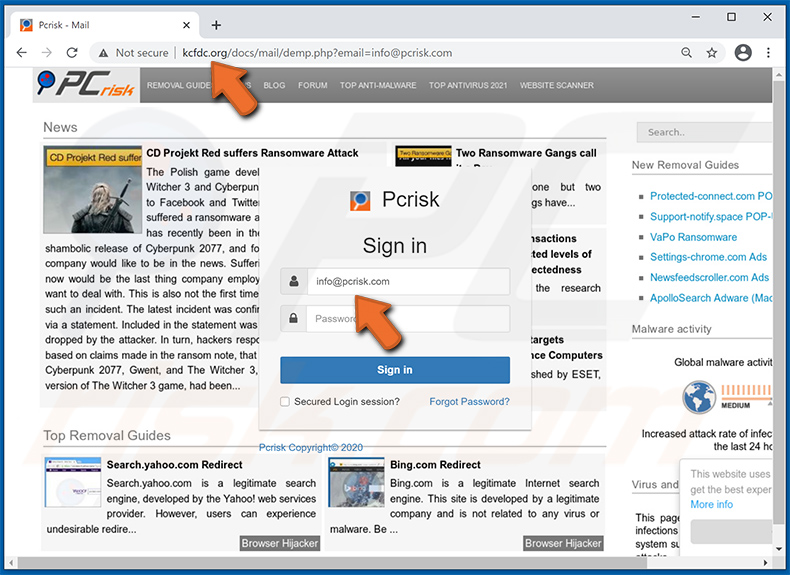
Screenshot of the promoted phishing website - notice that the site is designed to check recipient's email address and set its background accordingly. For example, if victim's email is @yahoo.com, the site will have yahoo.com website picture as background and so forth. In this example, the recipient's email is @pcrisk.com, therefore, the phishing website's background is a picture of pcrisk.com:
Another example of DHL Express-themed spam email used for phishing purposes (the attached HTML document imitates DHL website and sends all the user input into a remote server):
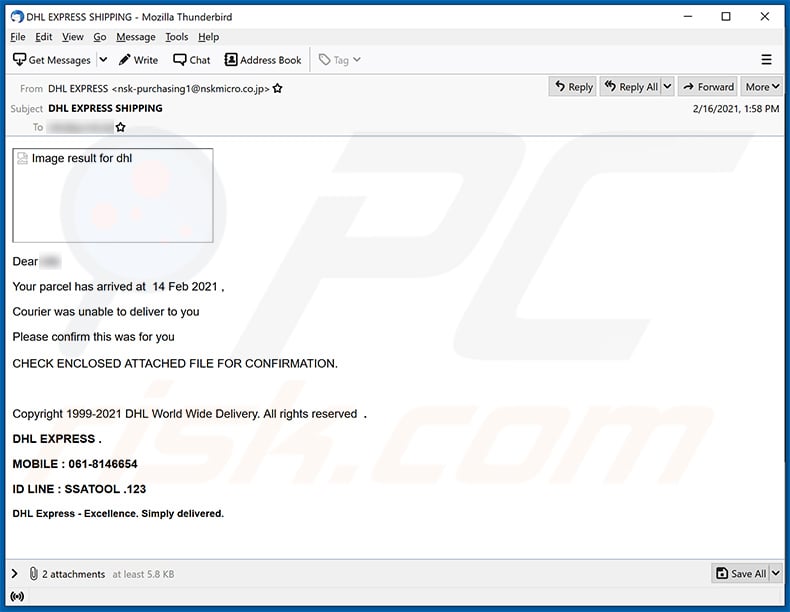
Text presented within:
Subject: DHL EXPRESS SHIPPING
Dear -
Your parcel has arrived at 14 Feb 2021 ,
Courier was unable to deliver to you
Please confirm this was for you
CHECK ENCLOSED ATTACHED FILE FOR CONFIRMATION.
Copyright 1999-2021 DHL World Wide Delivery. All rights reserved .
DHL EXPRESS .
MOBILE : 061-8146654
ID LINE : SSATOOL .123
DHL Express - Excellence. Simply delivered.
Screenshot of the attached HTML document ("INVOICE.html"):
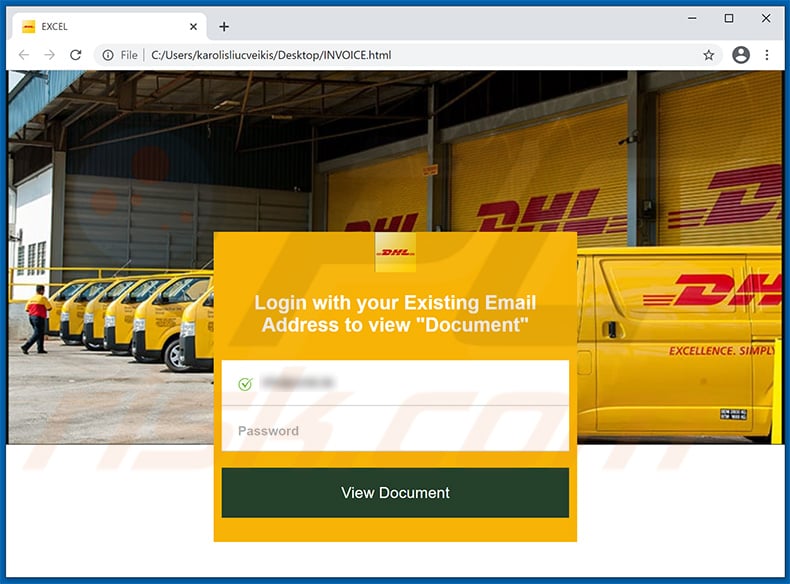
Another example of DHL Express-themed spam email used to promote a phishing website:
Text presented within:
Subject: Your Shipment Has Arrived
DHL ExpressDear -,
Due to several cases of package misplacement we are experiencing recently,
It is now mandatory that we confirm delivery address from the beneficiary before final delivery.Kindly Re confirm your delivery address to ensure safe delivery.
Click here to confirm your details now!Failure to verify address might lead to delay in scheduled delivery or loss of important package.
Regards,
2021 © DHL International GmbH. All rights reserved.
Screenshot of the promoted phishing site:
Another DHL Express-themed spam email used to promote an identical phishing website:
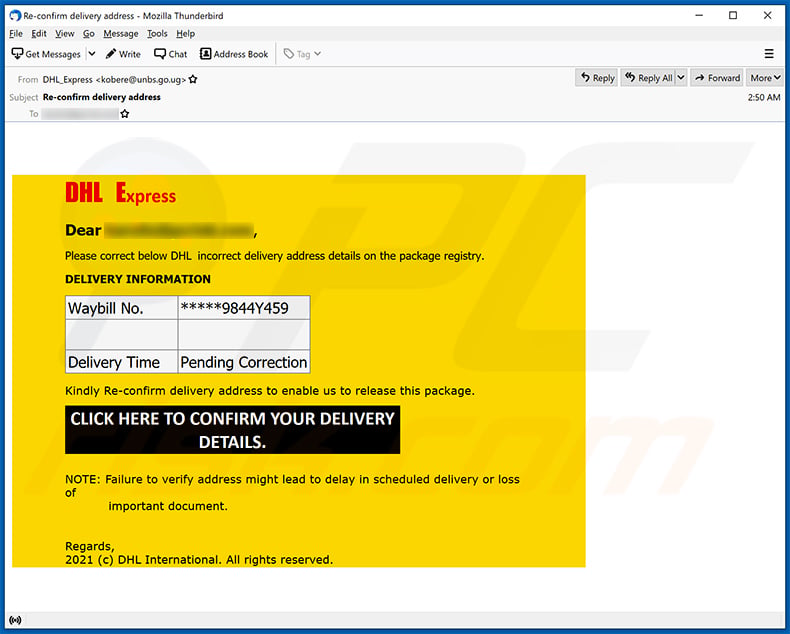
Text presented within:
Subject: Re-confirm delivery address
DHL Express
Dear ******,
Please correct below DHL incorrect delivery address details on the package registry.
DELIVERY INFORMATION
Waybill No.
*****9844Y459Delivery Time
Pending Correction
Kindly Re-confirm delivery address to enable us to release this package.
CLICK HERE TO CONFIRM YOUR DELIVERY DETAILS.
NOTE: Failure to verify address might lead to delay in scheduled delivery or loss of
important document.Regards,
2021 (c) DHL International. All rights reserved.
Yet another example of DHL Express-themed spam email used to promote a phishing website:
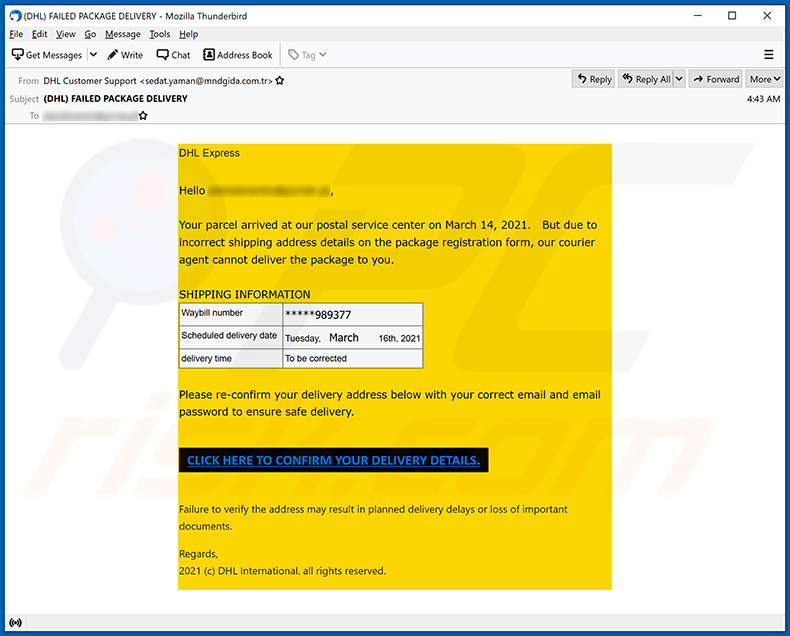
Text presented within:
Subject: (DHL) FAILED PACKAGE DELIVERY
DHL Express
Hello ********,Your parcel arrived at our postal service center on March 14, 2021. But due to incorrect shipping address details on the package registration form, our courier agent cannot deliver the package to you.
SHIPPING INFORMATION
Waybill number
*****989377
Scheduled delivery date
Tuesday, March 16th, 2021
delivery time
To be correctedPlease re-confirm your delivery address below with your correct email and email password to ensure safe delivery.
CLICK HERE TO CONFIRM YOUR DELIVERY DETAILS.
Failure to verify the address may result in planned delivery delays or loss of important documents.Regards,
2021 (c) DHL International. all rights reserved.
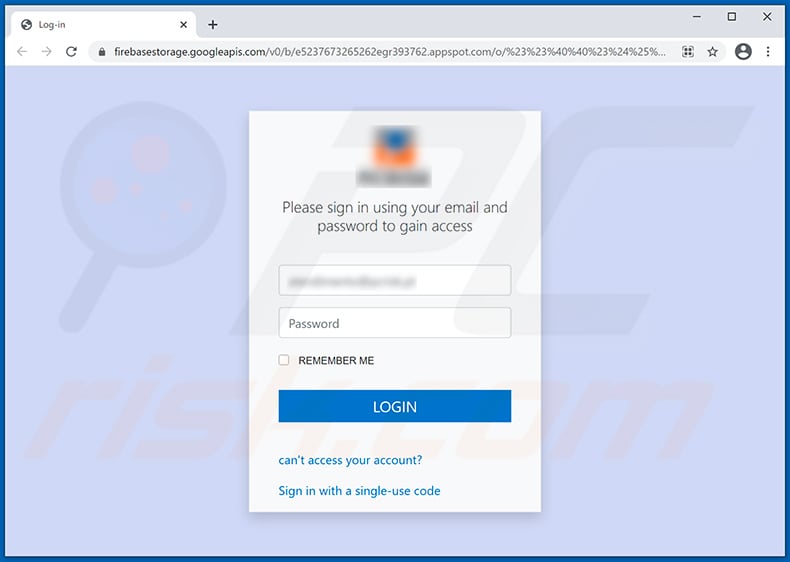
Screenshot of the promoted phishing site:
Another example of DHL Express-themed spam email used to spread Agent Tesla RAT:
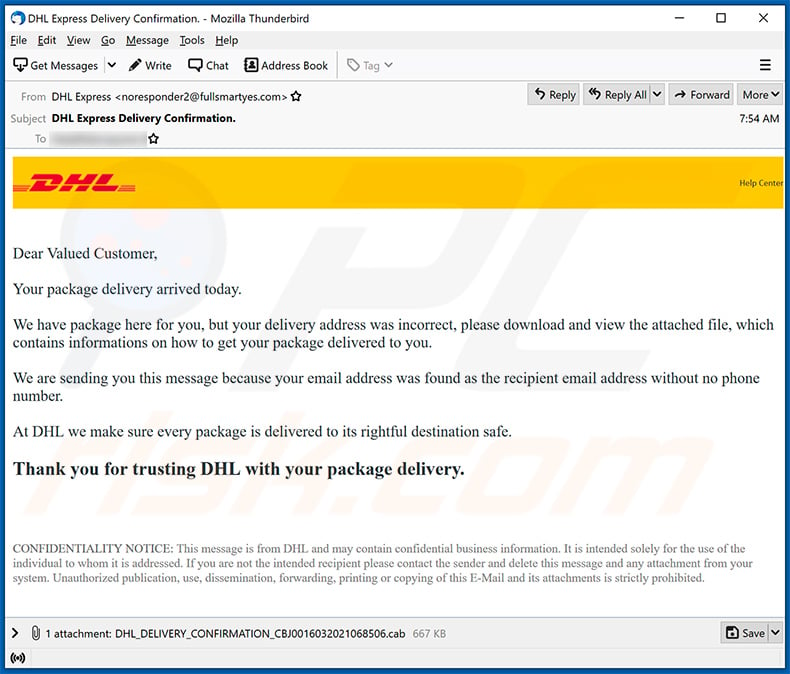
Text presented within:
Subject: DHL Express Delivery Confirmation.
Help Center
Dear Valued Customer,
Your package delivery arrived today.
We have package here for you, but your delivery address was incorrect, please download and view the attached file, which contains informations on how to get your package delivered to you.
We are sending you this message because your email address was found as the recipient email address without no phone number.
At DHL we make sure every package is delivered to its rightful destination safe.
Thank you for trusting DHL with your package delivery.
CONFIDENTIALITY NOTICE: This message is from DHL and may contain confidential business information. It is intended solely for the use of the individual to whom it is addressed. If you are not the intended recipient please contact the sender and delete this message and any attachment from your system. Unauthorized publication, use, dissemination, forwarding, printing or copying of this E-Mail and its attachments is strictly prohibited.
Another example of DHL Express-themed spam email promoting a phishing website:
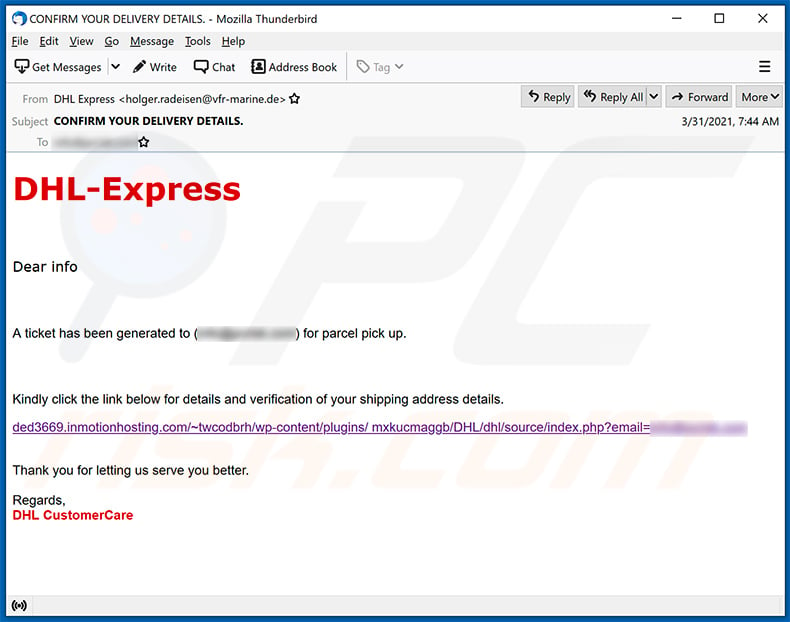
Text presented within:
Subject: CONFIRM YOUR DELIVERY DETAILS.
DHL-Express
Dear info
A ticket has been generated to (********) for parcel pick up.
Kindly click the link below for details and verification of your shipping address details.-
Thank you for letting us serve you better.
Regards,
DHL CustomerCare
Yet another example of DHL Express-themed spam email used to spread Agent Tesla RAT:
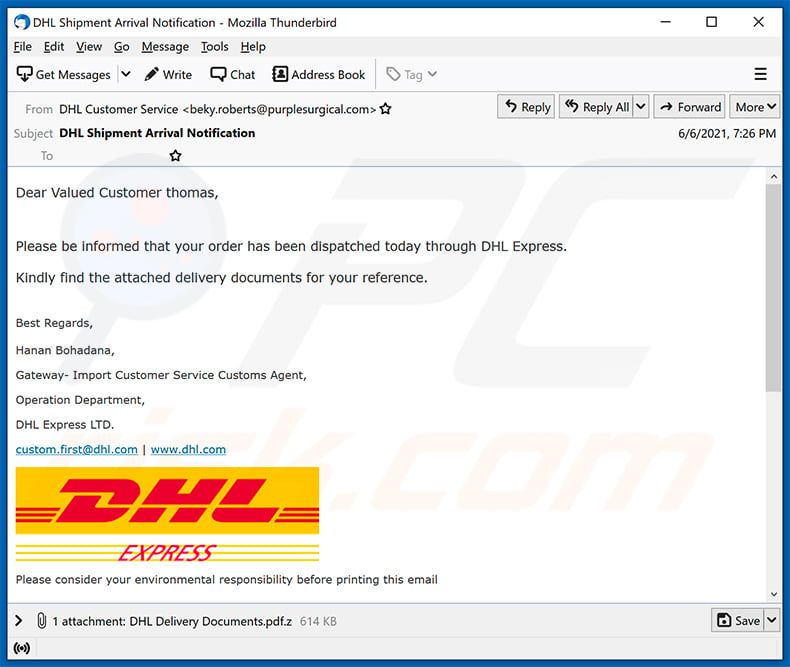
Text presented within:
Subject: DHL Shipment Arrival Notification
Dear Valued Customer ********,
Please be informed that your order has been dispatched today through DHL Express.Kindly find the attached delivery documents for your reference.
Best Regards,Hanan Bohadana,
Gateway- Import Customer Service Customs Agent,
Operation Department,
DHL Express LTD.
custom.first@dhl.com | www.dhl.com
Please consider your environmental responsibility before printing this email
Another example of DHL Express-themed spam email promoting a HTML file designed for phishing purposes:
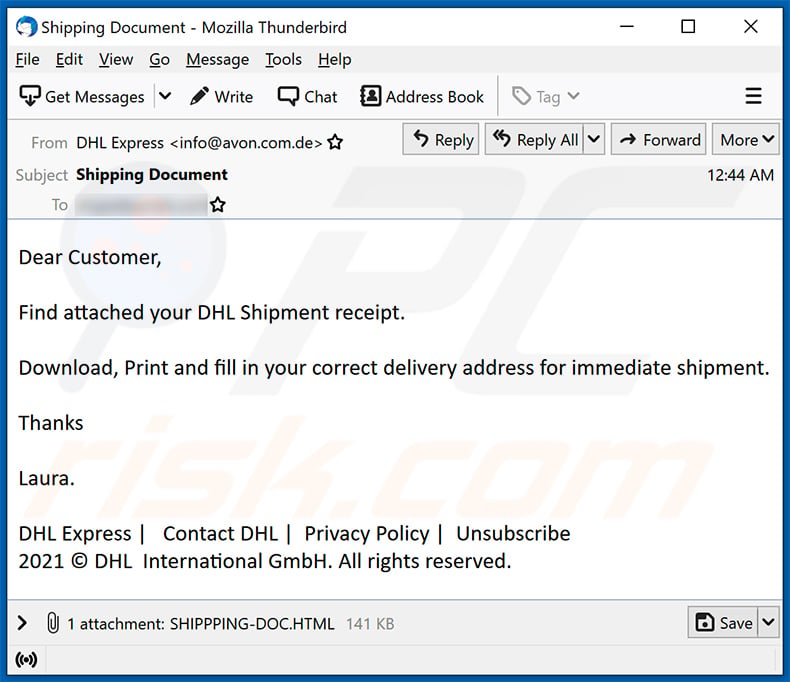
Text presented within:
Subject: Shipping Document
Dear Customer,
Find attached your DHL Shipment receipt.
Download, Print and fill in your correct delivery address for immediate shipment.
Thanks
Laura.
DHL Express | Contact DHL | Privacy Policy | Unsubscribe
2021 © DHL International GmbH. All rights reserved.
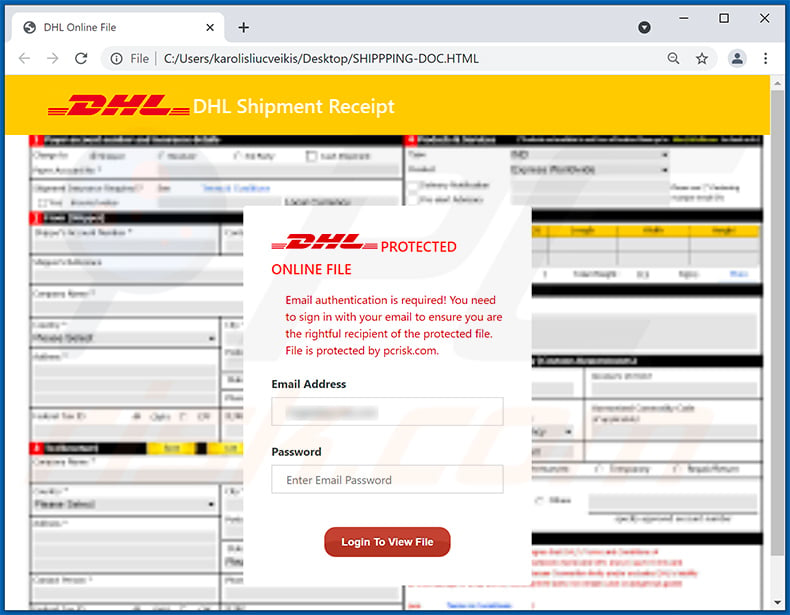
Screenshot of the promoted HTML file:
Another DHL Express-themed spam email promoting a phishing site:
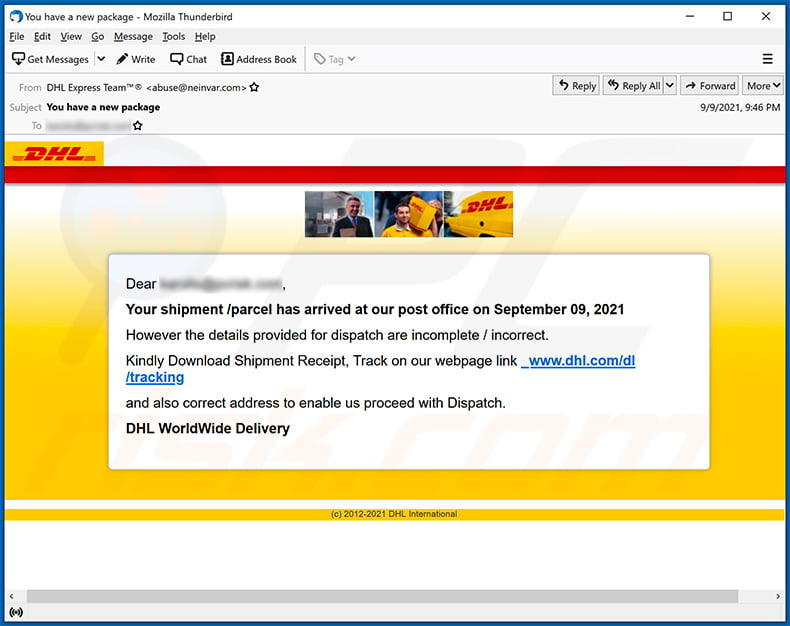
Text presented within:
Subject: You have a new package
Dear ********,Your shipment /parcel has arrived at our post office on September 09, 2021
However the details provided for dispatch are incomplete / incorrect.
Kindly Download Shipment Receipt, Track on our webpage link _www.dhl.com/dl/tracking
and also correct address to enable us proceed with Dispatch.
DHL WorldWide Delivery
(c) 2012-2021 DHL International
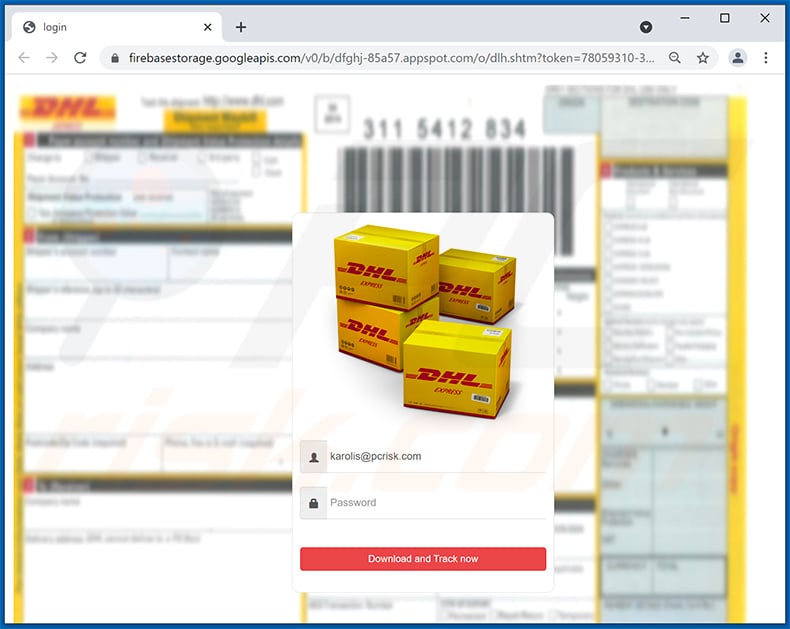
Screenshot of the promoted phishing site:
A Lithuanian variant of DHL Express-themed spam email spreading malware:
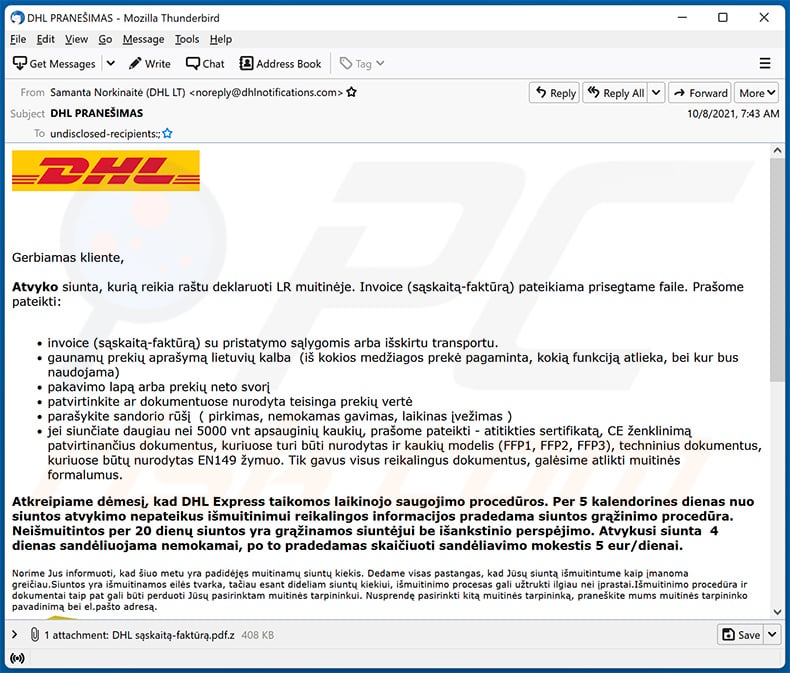
Text presented within:
Subject: DHL PRANEŠIMAS
Gerbiamas kliente,
Atvyko siunta, kurią reikia raštu deklaruoti LR muitinėje. Invoice (sąskaitą-faktūrą) pateikiama prisegtame faile. Prašome pateikti:
invoice (sąskaitą-faktūrą) su pristatymo sąlygomis arba išskirtu transportu.
gaunamų prekių aprašymą lietuvių kalba (iš kokios medžiagos prekė pagaminta, kokią funkciją atlieka, bei kur bus naudojama)
pakavimo lapą arba prekių neto svorį
patvirtinkite ar dokumentuose nurodyta teisinga prekių vertė
parašykite sandorio rūšį ( pirkimas, nemokamas gavimas, laikinas įvežimas )
jei siunčiate daugiau nei 5000 vnt apsauginių kaukių, prašome pateikti - atitikties sertifikatą, CE ženklinimą patvirtinančius dokumentus, kuriuose turi būti nurodytas ir kaukių modelis (FFP1, FFP2, FFP3), techninius dokumentus, kuriuose būtų nurodytas EN149 žymuo. Tik gavus visus reikalingus dokumentus, galėsime atlikti muitinės formalumus.Atkreipiame dėmesį, kad DHL Express taikomos laikinojo saugojimo procedūros. Per 5 kalendorines dienas nuo siuntos atvykimo nepateikus išmuitinimui reikalingos informacijos pradedama siuntos grąžinimo procedūra. Neišmuitintos per 20 dienų siuntos yra grąžinamos siuntėjui be išankstinio perspėjimo. Atvykusi siunta 4 dienas sandėliuojama nemokamai, po to pradedamas skaičiuoti sandėliavimo mokestis 5 eur/dienai.
Norime Jus informuoti, kad šiuo metu yra padidėjęs muitinamų siuntų kiekis. Dedame visas pastangas, kad Jūsų siuntą išmuitintume kaip įmanoma greičiau.Siuntos yra išmuitinamos eilės tvarka, tačiau esant dideliam siuntų kiekiui, išmuitinimo procesas gali užtrukti ilgiau nei įprastai.Išmuitinimo procedūra ir dokumentai taip pat gali būti perduoti Jūsų pasirinktam muitinės tarpininkui. Nusprendę pasirinkti kitą muitinės tarpininką, praneškite mums muitinės tarpininko pavadinimą bei el.pašto adresą.
Pagarbiai / Kind regards,
Samanta NorkinaitėMuitinės tarpininkų asistentė/ Customs Broker Assistant
Darbo laikas: 7.00-16.00
Tel.: 870077060
DHL Lietuva, UAB
Dariaus ir Girėno g. 81
LT - 02189 Vilnius
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is DHL Express spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are sent in mass-scale campaigns; hence, thousands of users receive the same letter.
I have read the "DHL Express" spam email but didn't open the attachment, is my computer infected?
No, simply opening a spam email will not initiate malware download/installation. These processes begin when the attachments or links found in these emails are opened.
I have downloaded and opened the file attached to the "DHL Express" spam email, is my computer infected?
Whether an infection was triggered - depends on the file's format. If it was an executable - most likely, yes. On the other hand, document files (e.g., .pdf, .doc, etc.) may require additional actions (e.g., macro commands enablement, etc.) to jumpstart infection processes.
My computer is infected with LokiBot malware, should I format my storage device to get rid of it?
No, formatting is unnecessary for LokiBot's removal.
What are the biggest issues that malware can cause?
The threats posed by a malicious program depend on its abilities and how the cyber criminals use it. Since LokiBot malware is designed to steal information, it mainly endangers user privacy and financial integrity. In general, system infections can compromise its operation and cause hardware damage or permanent loss.
What is the purpose of malware?
Malware is mainly used by cyber criminals to generate profit. However, this software might be because of other reasons like criminals' amusement, political/geopolitical motivations, targeting specific victims (personal reasons), process (e.g., website, service, company, etc.) disruption, and so on.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is capable of detecting and eliminating practically all known malware infections. It must be stressed that running a full system is a must - as sophisticated malware typically hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion