Removal instructions for Agent Tesla RAT (Remote Access Trojan) malware
TrojanAlso Known As: AgentTesla remote access trojan
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Agent Tesla?
Agent Tesla (AgentTesla) is a remote access tool (RAT) that allows users to control computers remotely. This tool can be purchased from its official website and developers present it as a legitimate program. In fact, cyber criminals use Agent Tesla to steal various personal data.
Agent Tesla RAT overview
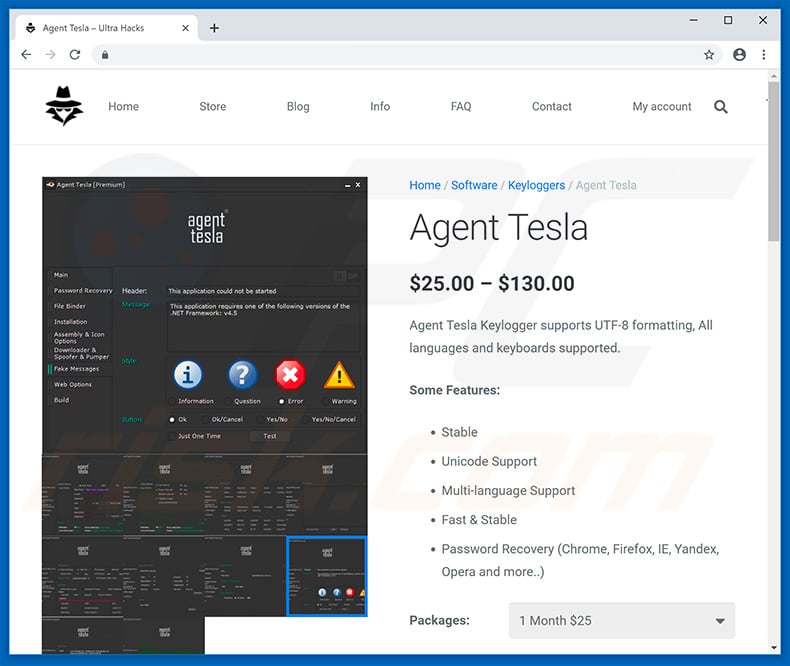
Anyone can purchase an Agent Tesla subscription (monthly/yearly) and use it for various purposes. The website claims that this tool should not be used for malicious purposes, and the subscriptions of users who do so will be suspended. In fact, research shows that these claims are false and the developers attempt to give the impression of legitimacy.
Be aware that subscribers can get 24/7 support on a Discord chatting program. Developers provide a wide range of support, including tips about how to proliferate Agent Tesla in malicious ways (e.g., spam email campaigns, misusing software bugs, etc.).
Therefore, it is safe to assume that claims regarding the suspension of subscriptions are false and that developers condone employing this tool to illegally monitor/control other people's computers to generate revenue in malicious ways. One of the main Agent Tesla features is keylogging - it can be used to record system keystrokes.
Therefore, criminals can gain access to victims' accounts. They aim to generate as much revenue as possible and will probably misuse hijacked accounts in various ways. For example, bank accounts can be used to transfer money, purchase items online, and so on.
Other personal accounts (e.g., social networks, emails, etc.) can be used to steal a victim's identity to borrow even more money and send malicious files to people on the contacts list, thus proliferating this RAT (or other malware) even further.
Cyber criminals often improve and update their malicious programs, and Agent Tesla is not an exception. Its full list of functionalities can be found below.
Therefore, the presence of a remote access tool on your system might cause various issues, financial loss, and victims can even get into debt. Therefore, you should eliminate these threats immediately.
| Name | AgentTesla remote access trojan |
| Threat Type | Trojan, remote access trojan, RAT. |
| Detection Names | Avast (AutoIt:Injector-JF [Trj]), BitDefender (Trojan.GenericKD.31825418), ESET-NOD32 (MSIL/Spy.Agent.AES), Kaspersky (Trojan-Dropper.Win32.Scrop.uod), Full List (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
RAT examples
There are hundreds of remote access tools online. For example, Imminent Monitor, H-Worm, CrimsonRAT, and Nymeria.
Some are malicious, others are legitimate, however, if misused, they all pose threats to users' privacy and computer safety (remote access tools are often used to download and install additional applications that are often malicious). Therefore, removing remote access tools is extremely important.
How did Agent Tesla infiltrate my computer?
Anyone can purchase and start proliferating Agent Tesla using many available distribution tools/methods. In most cases, RATs are proliferated using trojans, spam email campaigns, fake software updaters/cracks and unofficial software download sources. Trojans are essentially malicious applications that stealthily infiltrate computers and continually inject additional malware.
Spam email campaigns are used to proliferate malicious attachments together with deceptive messages encouraging users to open the files. These attachments are often presented as invoices, bills, receipts, and so on. Opening them usually leads to system infections.
Fake updaters infect computers by exploiting outdated software bugs/flaws or simply downloading and installing malware rather than updates. The idea behind software cracks is to bypass paid software activation, however, since they are often used to proliferate malware, users commonly end up infecting their computers rather than activating software free of charge.
Unofficial software download sources are also an issue. Developers present malicious executables/apps as legitimate software, thereby tricking users into downloading and installing malware. In summary, the main reasons for computer infections are poor knowledge of these threats and careless behavior.
How to avoid installation of malware?
To prevent this situation, be very cautious when browsing the internet and downloading/installing software. Think twice before opening email attachments. Files/links that do not concern you, and those received from suspicious/unrecognizable email addresses, should not be opened. Software should be downloaded from official sources only, using direct download/links.
Third party downloaders/installers often include rogue apps, and thus such tools should never be used. Similar rules apply to software updates. Keeping installed applications and operating systems up-to-date is important, however, use tools provided by the official developer or implemented functions only.
Never use software cracking tools since software piracy is a cyber crime and the risk of infections is extremely high. Use a reputable anti-virus/anti-spyware suite - these tools commonly detect and eliminate malware before the system is harmed. The key to computer safety is caution.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Hacking website promoting Agent Tesla RAT:
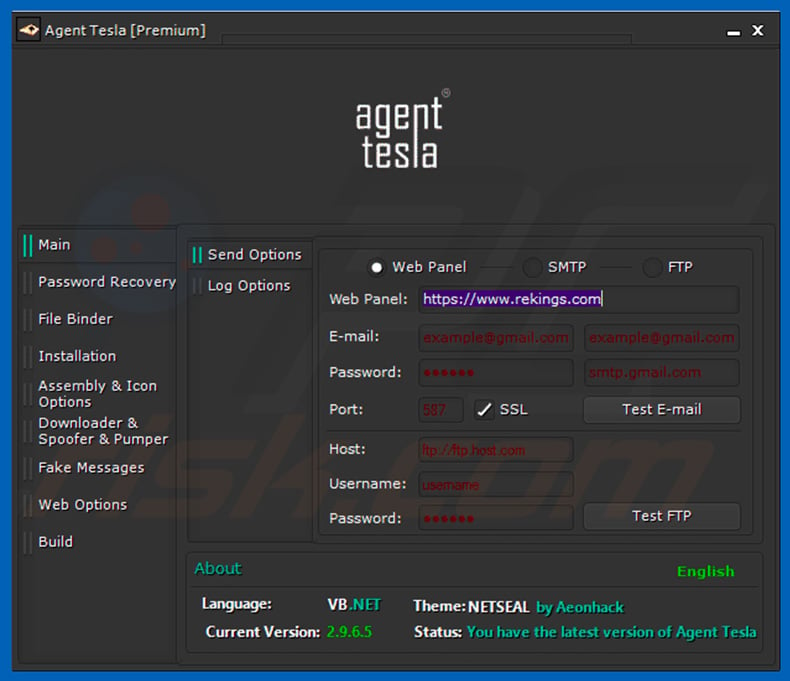
Agent Tesla dashboard used to control this RAT:
Deceptive email promoting a malicious attachment that injects Agent Tesla:
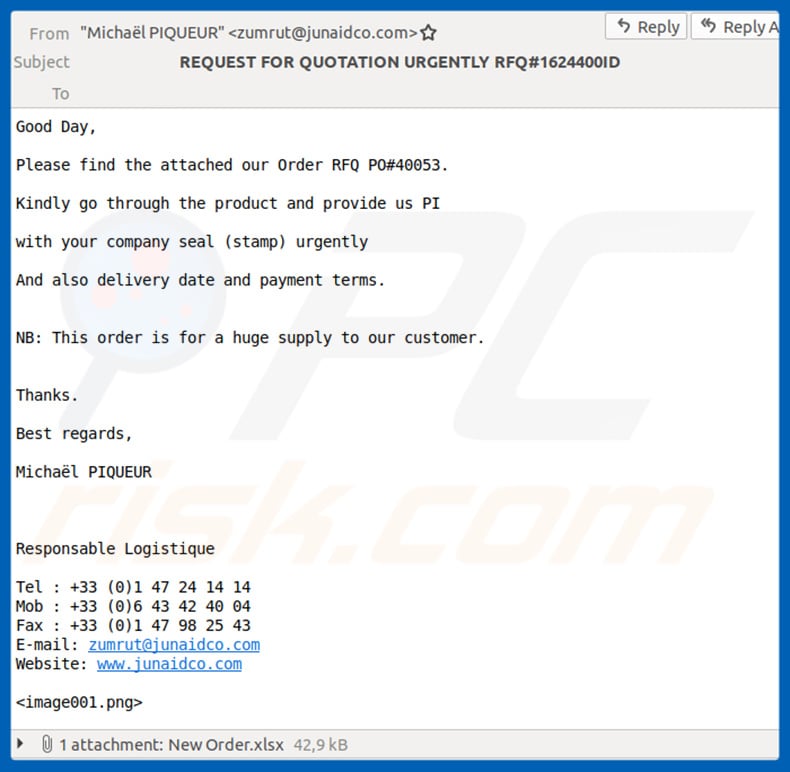
Text presented within this email:
Subject REQUEST FOR QUOTATION URGENTLY RFQ#1624400ID
Good Day,
Please find the attached our Order RFQ PO#40053.
Kindly go through the product and provide us PI
with your company seal (stamp) urgently
And also delivery date and payment terms.
NB: This order is for a huge supply to our customer.
Thanks.
Best regards,
Michael PIQUEUR
Responsable Logistique
Tel : +33 (0)1 47 24 14 14
Mob : +33 (0)6 43 42 40 04
Fax : +33 (0)1 47 98 25 43
E-mail: zumrut@junaidco.com
Website: www.junaidco.com
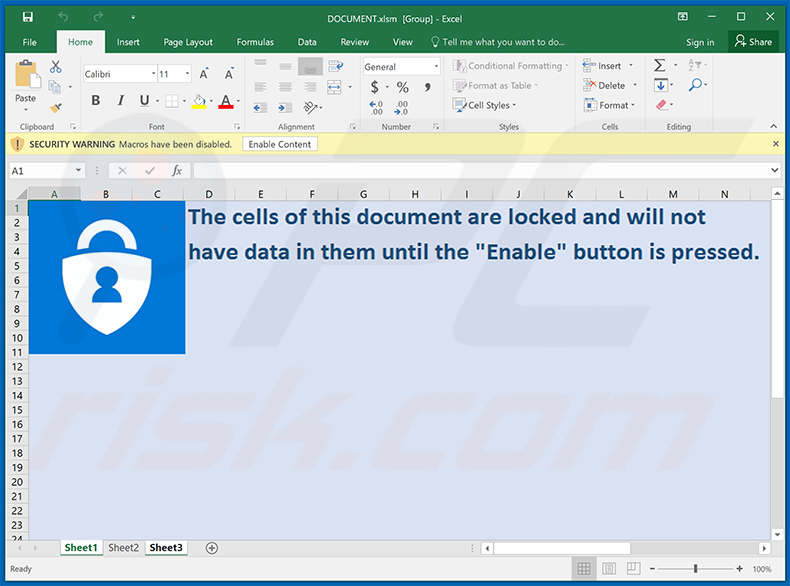
Malicious attachment (Microsoft Excel document) distributing Agent Tesla:
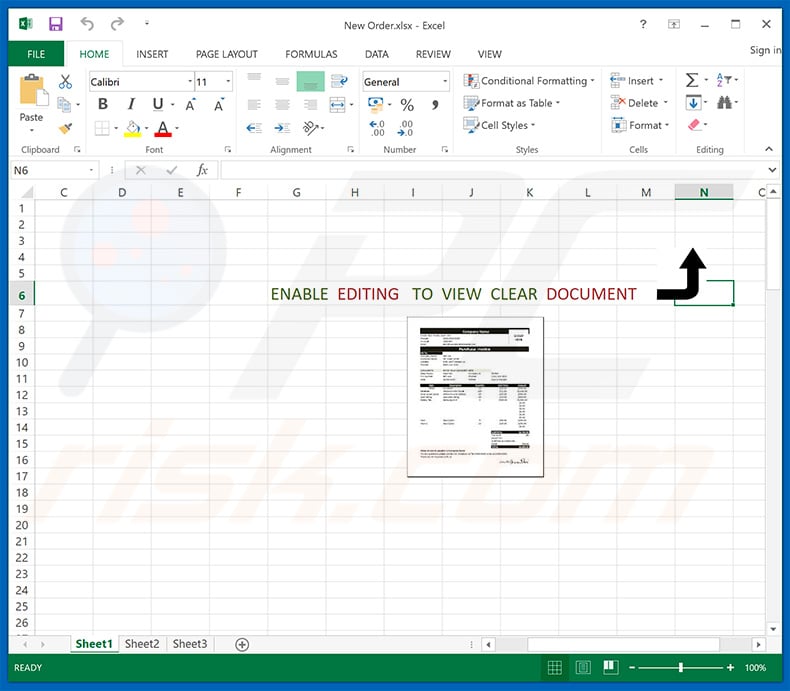
Another email spam campaign ("TNT Express") used to spread Agent Tesla RAT:
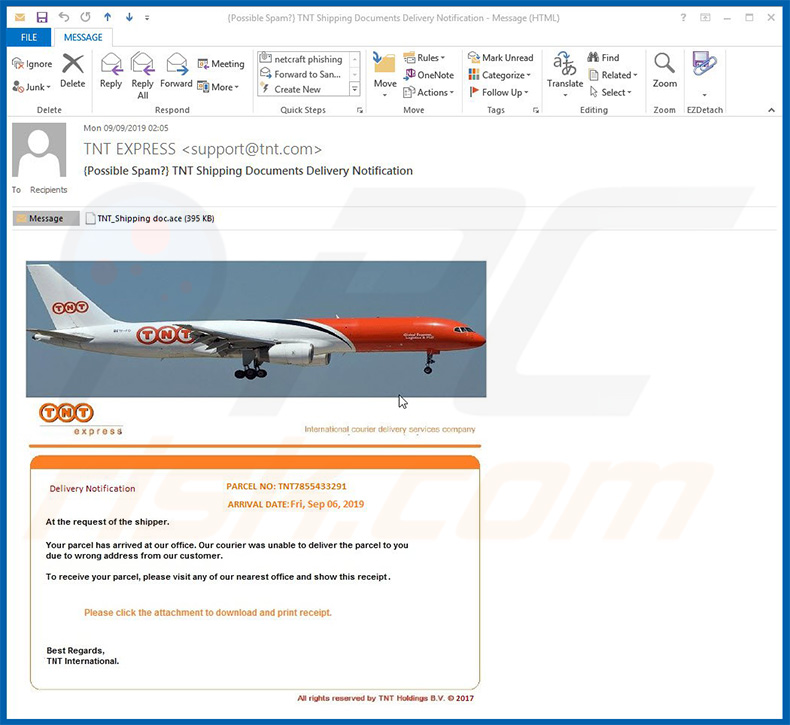
Text presented within this email:
Subject: TNT Shipping Documents Delivery Notification
Attachment: TNT_Shipping
TNT express
International courier delivery services company
Delivery Notification
PARCEL NO: TNT7855433291
ARRIVAL DATE:Fri, Sep 06, 2019
At the request of the shipper.
Your parcel has arrived at our office. Our courier was unable to deliver the parcel to you due to wrong address from our customer.
To receive your parcel, please visit any of our nearest office and show this receipt.
Please click the attachment to download and print receipt.
Best regards,
TNT International
All rights reserved by TNT Holdings B.V. © 2017
Yet another email spam campaign ("DHL Express") used to distribute Agent Tesla RAT:
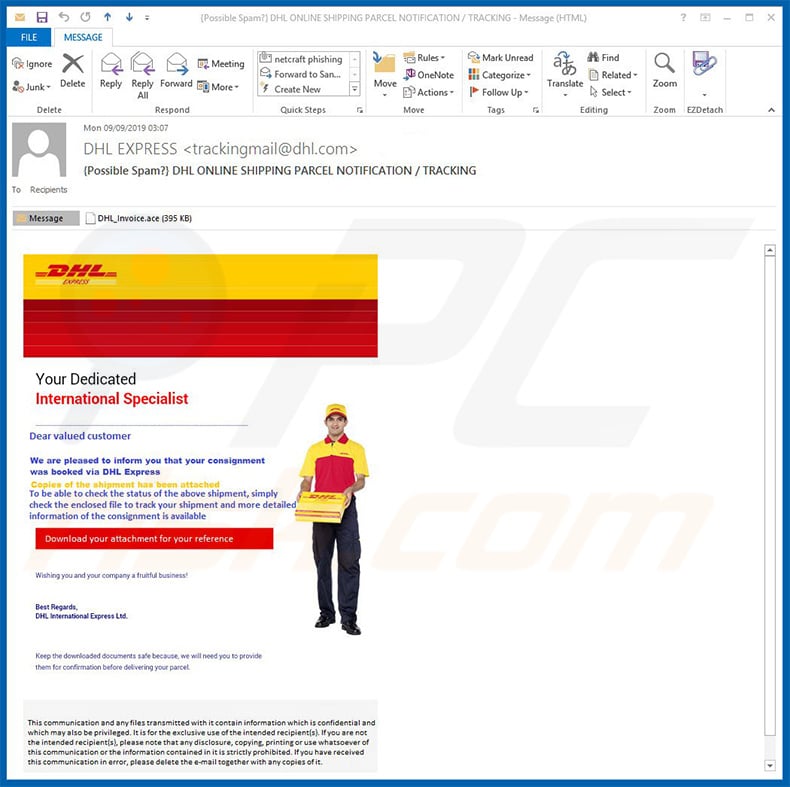
Text presented within this email:
Subject: DHL ONLINE SHIPPING PARCEL NOTIFICATION / TRACKING
Attachment: DHL_Invoice.ace
Your Dedicated
International SpecialistDear Valued customer
We are pleased to inform you that your consignment was booked via DHL Express
Copies of the shipment has been attached
To be able to check the status of the above shipment, simply check the enclosed file to track your shipment and more detailed information of the consignment is available
Download your attachment for your reference
Wishing you and your company a fruitful business!Best Regards,
DHL International Express Ltd.Keep the downloaded documents safe because, we will need you to provide them for confirmation before delivering your parcel.
Yet another email spam campaign (crooks pretend to be employees of Pricol company) used to spread Agent Tesla RAT:
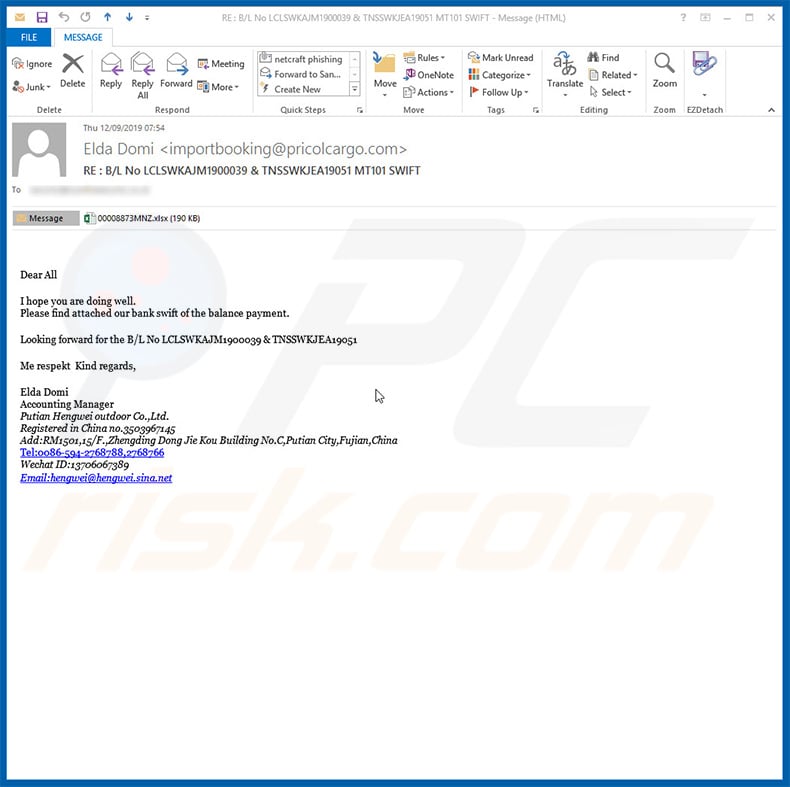
Text presented within this email:
Subject: RE : B/L No LCLSWKAJM1900039 & TNSSWKJEA19051 MT101 SWIFT
Attachment: 00008873MNZ.xlsx
Dear AllI hope you are doing well.
Please find attached our bank swift of the balance payment.
Looking forward for the B/L No LCLSWKAJM1900039 & TNSSWKJEA19051
Me respekt Kind regards,
Elda Domi
Accounting Manager
Putian Hengwei outdoor Co.,Ltd.
Registered in China no.3503967145
Add:RM1501,15/F.,Zhengding Dong Jie Kou Building No.C,Putian City,Fujian,China
Tel:0086-594-2768788,2768766
Wechat ID:13706067389
Email:hengwei@hengwei.sina.net
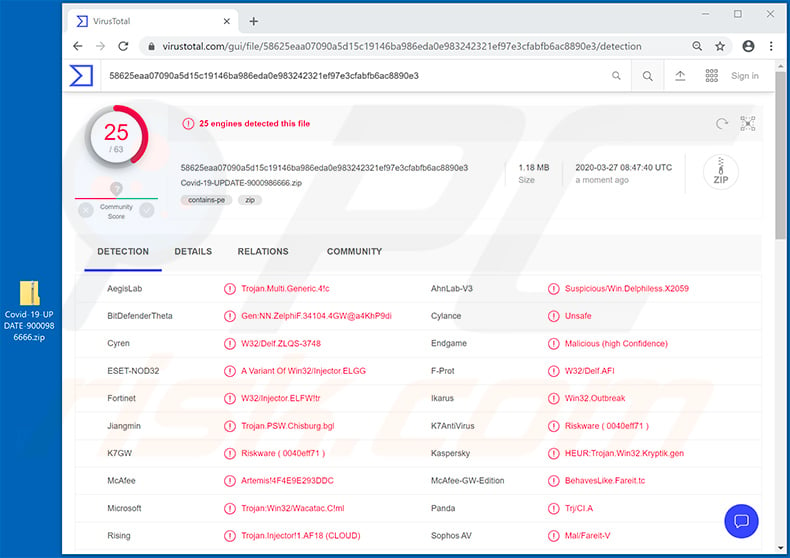
Update March 27, 2020 - Due to the recent outbreak of Coronavirus (COVID-19) cyber criminals have started hundreds of email spam campaigns relating to this topic.
They send various emails encouraging users to open attached files which are presented as documents relating to the current situation (e.g., list of infected people, safety instructions, etc.) The attachments, as usual, inject various malware into the system.
Here's an example of a malicious attachment ("Covid-19-UPDATE-9000986666.zip") which is supposedly sent by World Health Organization (WHO). The attachment injects Agent Tesla:
Yet another phishing email used to spread Agent Tesla RAT (the malicious attachment is an executable named "**** Delivery Express.exe"):
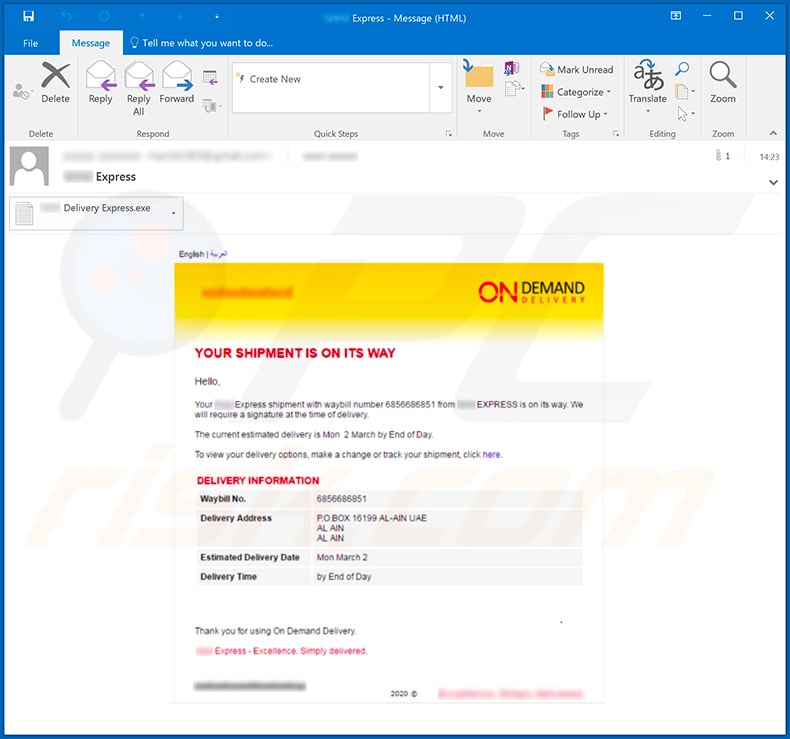
Text presented within this email:
ON DEMAND DELIVERY
YOUR SHIPMENT IS ON ITS WAYHello,
Your *** Express shipment with waybill number 6856686851 *** EXPRESS is on its way. We will require a signature at the same time of delivery.
The current estimated delivery is Mon 2 March by End of Day.
To view your delivery options, make a change or track your shipment, click here.
DELIVERY INFORMATION
Waybill No
Delivery Address P.O.BOX 16199 AL-AIN UAE
AL AIN
AL AIN
Estimated Delivery Date Mon March 2
Delivery Time by End of Day
Thank you for using On Demand Delivery
*** Express - Excellence. Simply delivered.
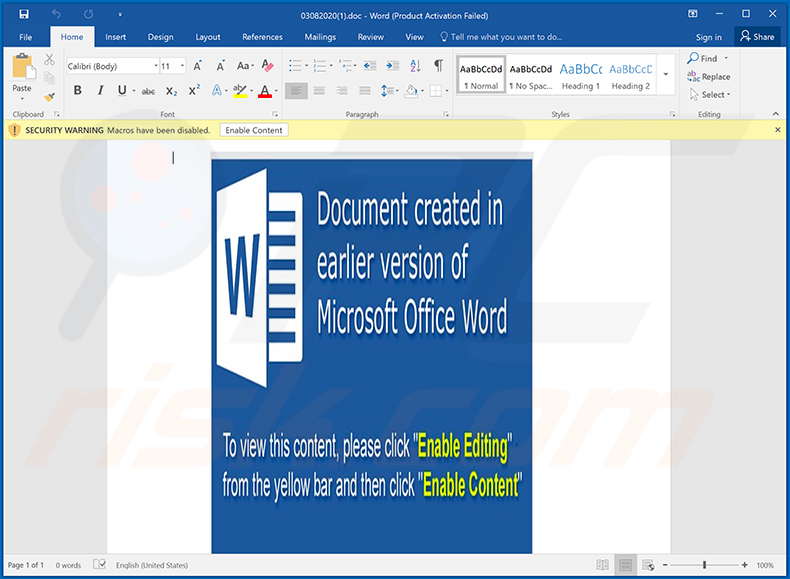
Example of a Coronavirus-related spam email spreading Agent Tesla RAT via attached Microsoft Word document:
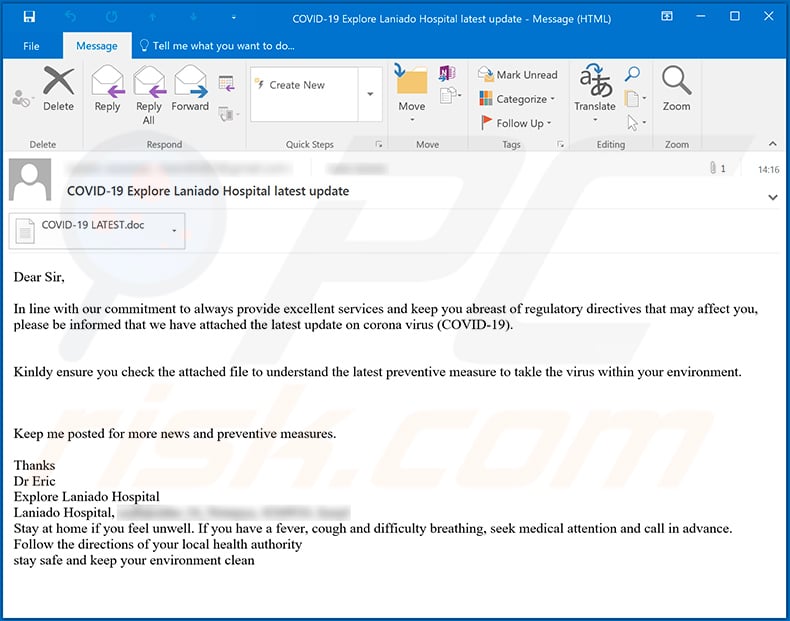
Text presented within this email:
Subject: COVID-19 Explore Laniado Hospital latest update
Dear Sir,
In line with our commitment to always provide excellent services and keep you abreast of regulatory directives that may affect you, please be informed that we have attached the latest update on corona virus (COVID-19).
Kinldy ensure you check the attached file to understand the latest preventive measure to takle the virus within your environment.
Keep me posted for more news and preventive measures.Thanks
Dr Eric
Explore Laniado Hospital
Laniado Hospital, -
Stay at home if you feel unwell. If you have a fever, cough and difficulty breathing, seek medical attention and call in advance. Follow the directions of your local health authority
stay safe and keep your environment clean
Screenshot of the attached malicious MS Word document:
Update April 2, 2020 - Agent Tesla targets web browsers such as:
- 360
- 7 Star
- Amigo
- Apple Safari
- BlackHawk
- Brave
- Cent
- Chedot
- Citrio
- Chromium
- Coccoc
- Comodo Dragon
- CoolNovo
- Coowon
- CyberFox
- Elements
- Epic Privacy
- Falkon
- Flock
- Google Chrome
- IceCat
- IceDragon
- Iridium
- KMeleon
- Kometa
- Liebao
- Microsoft IE & Edge
- Mozilla Firefox
- Opera
- Orbitum
- PaleMoon
- QIP Surf
- SeaMonkey
- Sleipnir 6
- Sputnik
- Tencent
- QQBrowser
- Torch
- UCBrowser
- Uran
- Vivaldi
- WaterFox
- Yandex
List of targeted email clients and messaging clients:
- Aerofox Foxmail
- Becky! Internet Mail
- Claws Mail
- ICQ Transport
- IncrediMail
- Microsoft Outlook
- Mozilla Thunderbird
- Opera Mail
- Pocomail
- Postbox
- Qualcomm Eudora
- The Bat! Email
- Trillian Messenger
List of targeted VPN, FTP clients and download managers:
- CFTP
- CoreFTP
- Coowon jDownloader
- DownloadManager
- FTP Navigator
- FTPGetter
- FileZilla
- FlashFXP
- Ipswitch WS_FTP
- OpenVPN
- SmartFTP
- WinSCP
Agent Tesla collects credentials from files in VPN, FTP clients and download managers, also, it collects credentials from the system registry and sends them to a C&C server controlled by cyber criminals.
New Agent Tesla version is capable of starting every time the operating system starts, also, it can disable various operating system's features or prevent victims from using them. It can:
- Disable Windows User Account Controls
- Prevent victims from opening Task Manager
- Prevent victims from launching Command Prompt (cmd.exe)
- Disable Control Panel, run various items from the Start menu and start new tasks from Task Manager
- Prevent victims from accessing the System Registry
- Prevent victims from restoring Windows
- Disable Folder Options in Windows Explorer
- Prevent victims from running msconfig.exe
Additionally, Agent Tesla can restart a computer, take screenshots of victims screen and send them to attackers email address.
Update April 17, 2020 - New variants of Agent Tesla RAT have been observed targeting Wi-Fi credentials. It attempts to steal Wi-Fi profiles and passwords. This data may be used to spread the infection to other devices, using the same wireless network.
An example of Facebook-related spam campaign used to spread Agent Tesla RAT (the attachment is a compressed malicious executable):
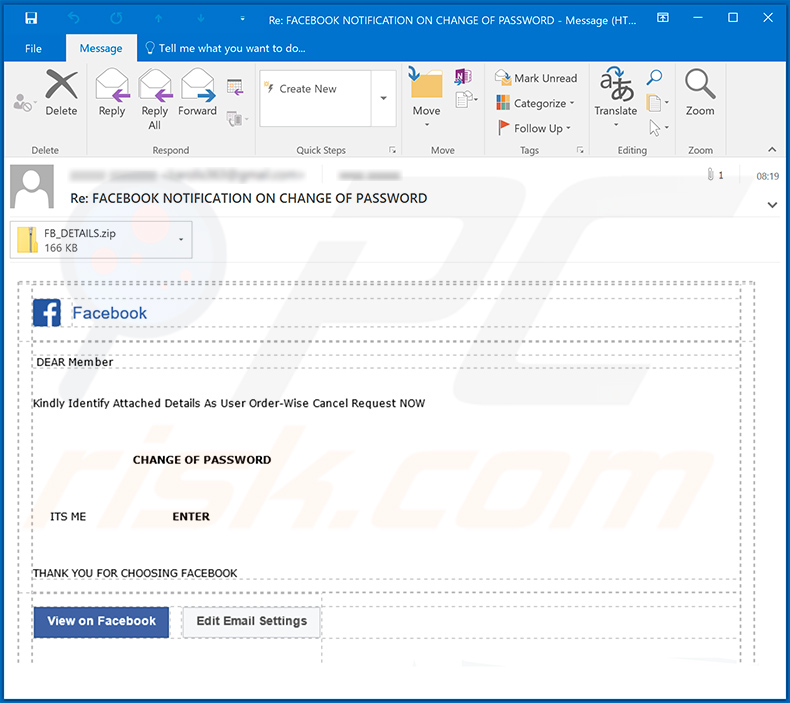
Text presented within:
Subject: Re: FACEBOOK NOTIFICATION ON CHANGE OF PASSWORD
DEAR Member
Kindly Identify Attached Details As User Order-Wise Cancel Request NOWCHANGE OF PASSWORD
ITS ME ENTER
THANK YOU FOR CHOOSING FACEBOOK
View on Facebook Edit Email Settings
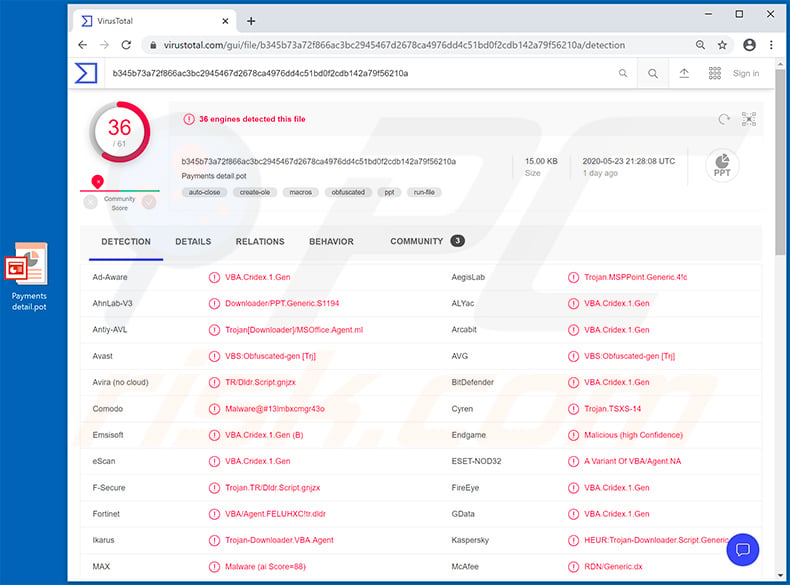
Update May 25, 2020 - Using Microsoft Office software to spread malware is very common nowadays. However, it is worth mentioning that in most cases cyber criminals use either Word or Excel documents which execute macro commands once opened.
In this case, however, cyber criminals are spreading a .pot file ("Payments detail.pot" - a PowerPoint add-in), which basically does the exact same job. As with most of malicious Word/Excel documents, this .pot file is also distributed using email spam campaigns. Once opened, the .pot file opens the PowerPoint program.
However, since its a mere add-in, the PowerPoint shows a blank document. As user sees nothing, he/she will probably simply close PowerPoint. That's where the infection starts. Once PowerPoint is closed, the malicious add-in runs a command that opens the default web browser and redirects to an URL, which in turn executes a JavaScript.
The script is designed to download and execute a malicious payload, which eventually results in Agent Tesla RAT's infiltration. You can find more details in InfoSec's article.
Detection names of the malicious PowerPoint add-in in VirusTotal:
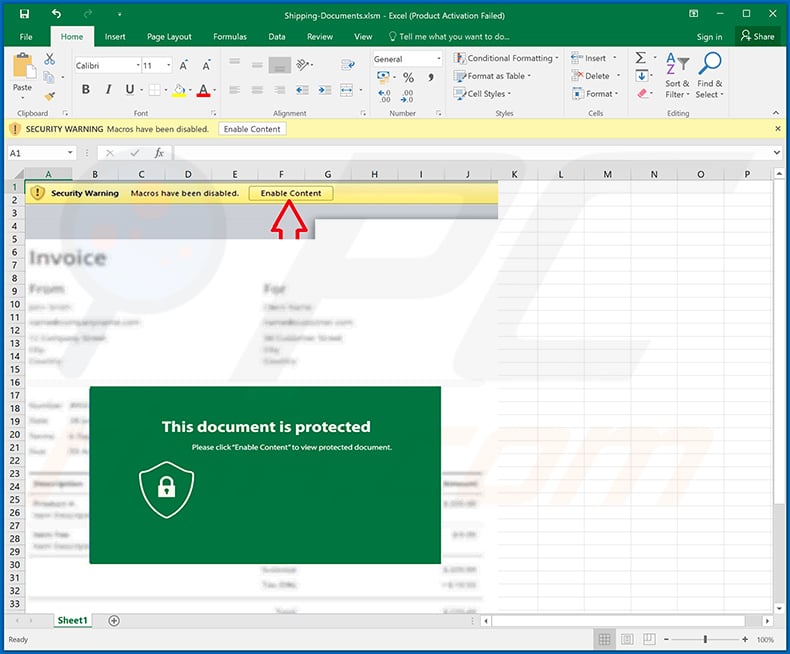
Example of yet another MS Excel document designed to inject Agent Tesla RAT into the system:
Example of yet another MS Word document used to inject Agent Tesla RAT into the system:
Example of yet another malicious MS Excel document used to spread Agent Tesla RAT:
Yet another DHL-themed spam email used to spread Agent Tesla RAT via attached MS Word documents:
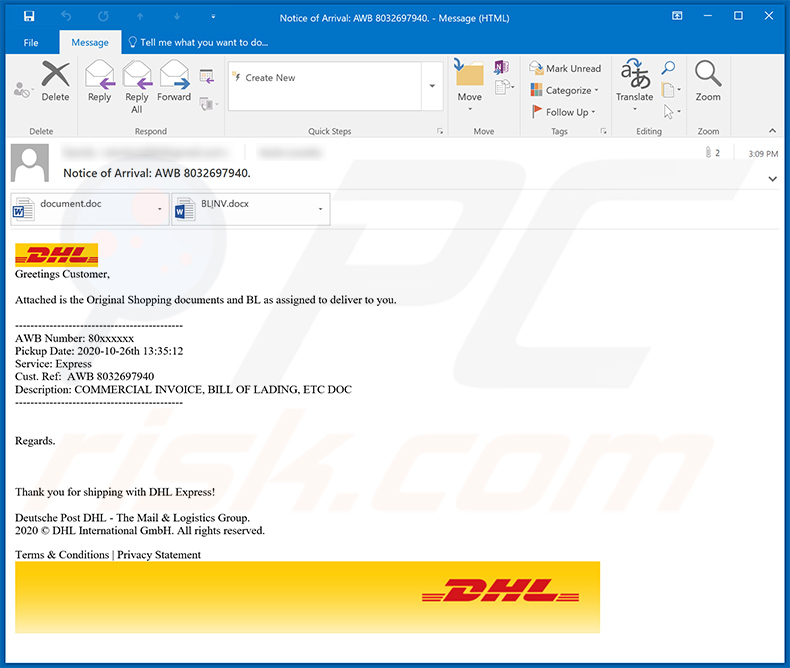
Text presented within:
Subject: Notice of Arrival: AWB 8032697940.
Greetings Customer,Attached is the Original Shopping documents and BL as assigned to deliver to you.
--------------------------------------------
AWB Number: 80xxxxxx
Pickup Date: 2020-10-26th 13:35:12
Service: Express
Cust. Ref: AWB 8032697940
Description: COMMERCIAL INVOICE, BILL OF LADING, ETC DOC
--------------------------------------------
Regards.
Thank you for shipping with DHL Express!Deutsche Post DHL - The Mail & Logistics Group.
2020 © DHL International GmbH. All rights reserved.Terms & Conditions | Privacy Statement
Yet another spam email used to spread Agent Tesla RAT:
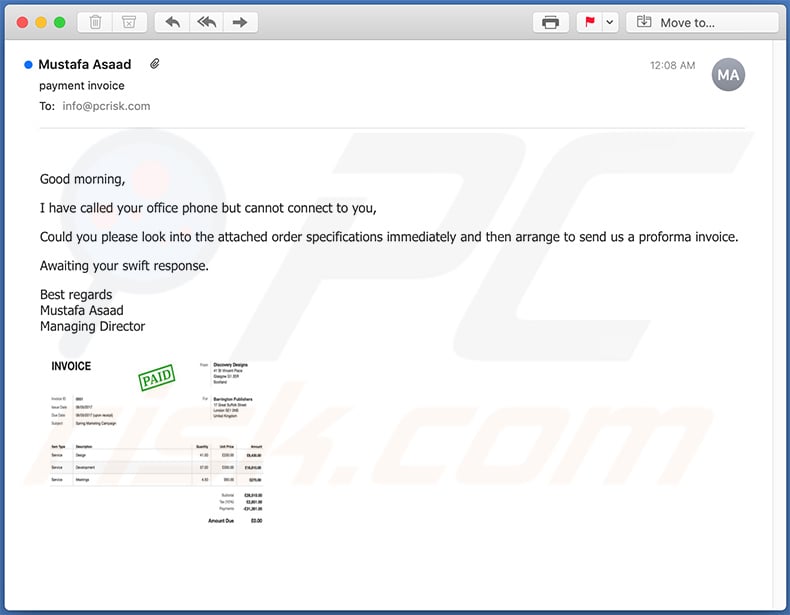
Text presented within:
Subject: payment invoice
Good morning,I have called your office phone but cannot connect to you,
Could you please look into the attached order specifications immediately and then arrange to send us a proforma invoice.
Awaiting your swift response.
Best regards
Mustafa Asaad
Managing Director
Screenshot of yet another malicious MS Excel document used to spread Agent Tesla RAT:
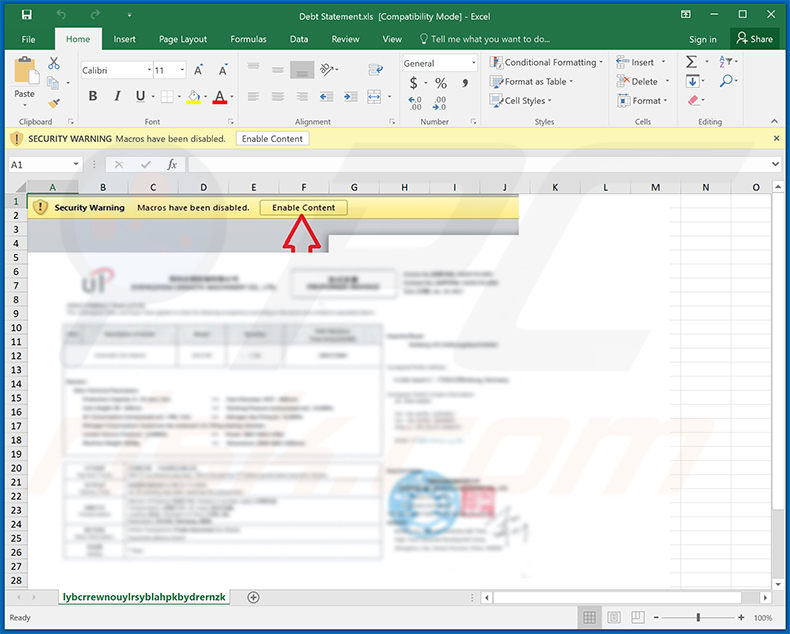
Yet another spam email used to spread a malicious MS Excel document that injects Agent Tesla RAT into the system:
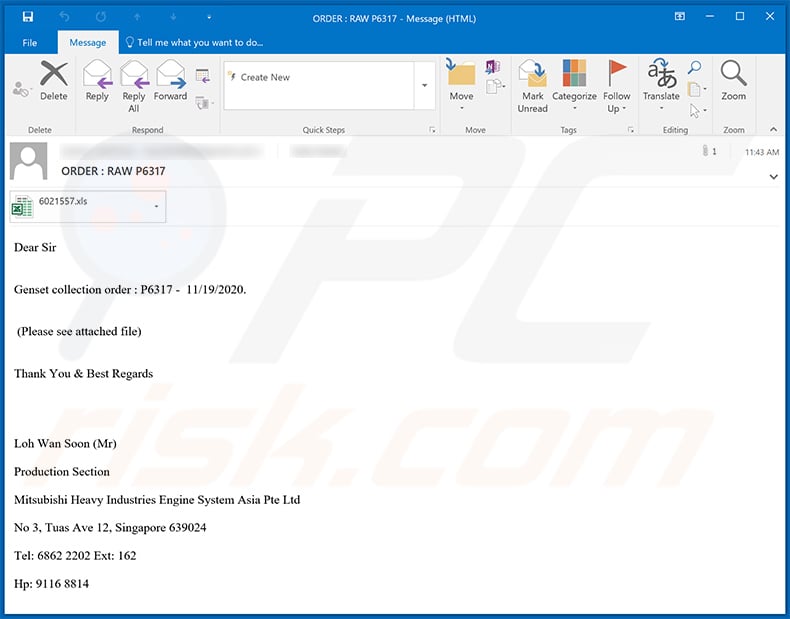
Text presented within:
Subject: ORDER : RAW P6317
Dear Sir
Genset collection order : P6317 - 11/19/2020.
(Please see attached file)
Thank You & Best Regards
Loh Wan Soon (Mr)Production Section
Mitsubishi Heavy Industries Engine System Asia Pte Ltd
No 3, Tuas Ave 12, Singapore 639024
Tel: 6862 2202 Ext: 162
Hp: 9116 8814
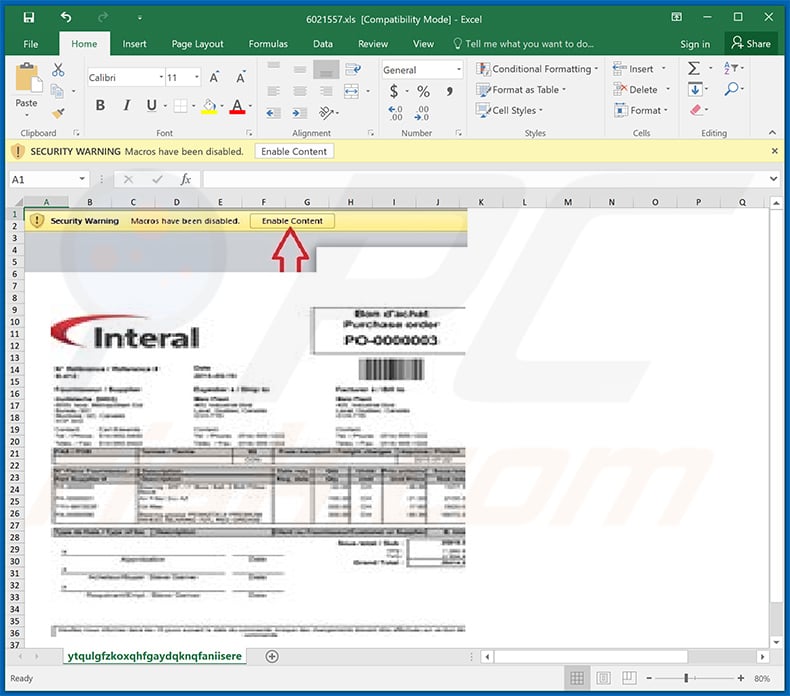
Screenshot of the attached document:
Yet another example of a DHL-themed spam email spreading Agent Tesla RAT:
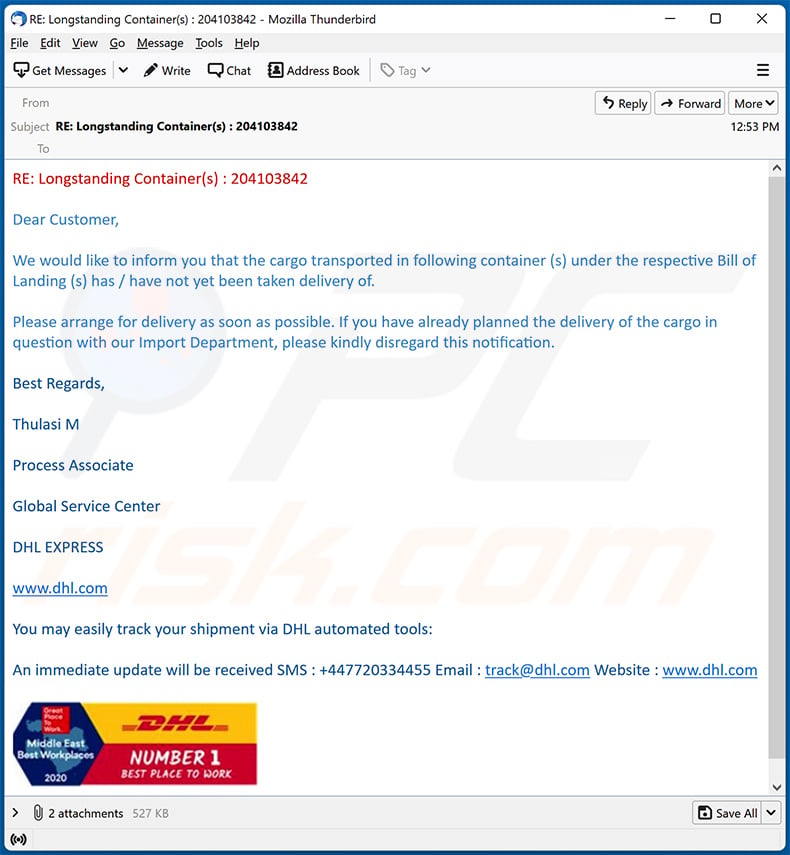
Text presented within:
Subject: RE: Longstanding Container(s) : 204103842
RE: Longstanding Container(s) : 204103842
Dear Customer,
We would like to inform you that the cargo transported in following container (s) under the respective Bill of Landing (s) has / have not yet been taken delivery of.
Please arrange for delivery as soon as possible. If you have already planned the delivery of the cargo in question with our Import Department, please kindly disregard this notification.
Best Regards,
Thulasi M
Process Associate
Global Service Center
DHL EXPRESS
www.dhl.com
You may easily track your shipment via DHL automated tools:
An immediate update will be received SMS : +447720334455 Email : track@dhl.com Website : www.dhl.com
Update October 25, 2022 - Another distribution method has been noted in use for the Agent Tesla RAT. It's been observed being proliferated via fake sites that mimic legitimate ones; the disguises can be good enough to be considered identical, while the URLs can differ by only a single letter. Malicious websites are often presented as those belonging or relating to social networking/media (particularly log-in pages), cryptocurrency, software and mobile apps, etc. For example, Agent Tesla has been spread through a fake Tor Project site that uses the tocproject[.]com domain. While such websites primarily depend on human error when entering URLs, they can also be accessed via redirects caused by sites using rogue advertising networks, spam browser notifications, intrusive ads, or installed adware.
Update November 22, 2023 - new distribution method used to spread Agent Tesla. Cybersecurity researchers have discovered an email spam campaign proliferating this malware via ZPAQ archive attachments.
Archived malware is more commonly compressed to popular formats like RAR or ZIP. However, ZPAQ has advantages in that this format allows for greater size compression and better journaling. The disadvantages include a limited selection of software capable of unpacking ZPAQs – including command-line tools, the use of which is not standard among average home users.
The archive attached to the email was 6KB in size and bore the title – "Purchase Order pdf.zpaq" (may vary). This file included a .NET executable, which increased to 1GB in size once unarchived (intentionally expanded to aid with detection evasion). This executable then downloaded a WAV file and decrypted it, thus triggering Agent Tesla's download/installation. It is noteworthy that in this infection, the trojan used Telegram for its C&C (Command and Control).
Update December 17, 2025 - A new malware campaign has been observed where attackers use a fake torrent disguised as a pirated Leonardo DiCaprio movie to infect devices. Instead of a real video file, the torrent contains a misleading shortcut that launches the attack chain. When the user opens it, embedded PowerShell scripts are executed, some of which are concealed inside subtitle files.
These scripts decrypt and unpack multiple layers of malicious code, relying heavily on built-in Windows tools rather than on noticeable malware files. The attack mainly runs in memory, which helps it evade traditional security detection. In the final stage, Agent Tesla is executed on the system.
The campaign is effective because it exploits interest in popular movies and the risky behavior of downloading pirated content.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Agent Tesla?
- STEP 1. Manual removal of Agent Tesla malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
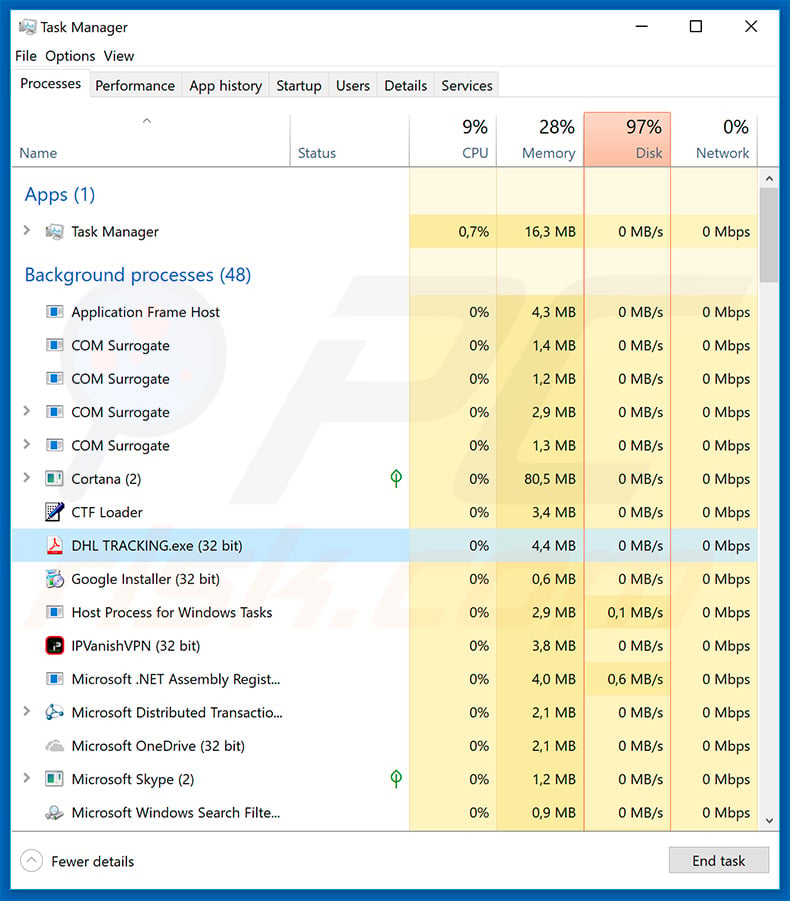
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Agent Tesla malware, should I format my storage device to get rid of it?
No, Agent Tesla can be removed without formatting.
What are the biggest issues that Agent Tesla malware can cause?
Agent Tesla is a RAT (Remote Access Trojan). It is designed to enable remote access/control over infected devices. This program can perform various actions on machines and extract a wide variety of vulnerable data from systems and installed applications. Therefore, Agent Tesla infections can cause severe privacy issues, financial losses, and even identity theft.
What is the purpose of Agent Tesla malware?
Typically, malware is used to generate revenue at victims' expense. However, cyber criminals can also use it to amuse themselves, disrupt processes (e.g., websites, services, companies, etc.), carry out personal grudges, or launch politically/geopolitically motivated attacks.
How did Agent Tesla malware infiltrate my computer?
Malware is primarily spread via spam emails and messages, drive-by (stealthy and deceptive) downloads, online scams, dubious download channels (e.g., freeware and third-party websites, Peer-to-Peer sharing networks, etc.), illegal software activation tools ("cracks"), and fake updates. Furthermore, some malicious programs can self-proliferate through local networks and removable storage devices (e.g., external hard drives, USB flash drivers, etc.).
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is capable of detecting and eliminating practically all known malware infections. It is noteworthy that sophisticated malicious programs usually hide deep within systems. Therefore, performing a full system scan is paramount.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion