How to avoid the 'I know you are a pedophile Email' scam
Phishing/ScamAlso Known As: I Know You Are A Pedophile spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of scam is "I know you are a pedophile"?
"I know you are a pedophile" is a scam, an email that scammers use to extort money from unsuspecting people. To achieve this, they claim that they have infected the computer with a remote access tool (RAT), which allowed them to record 'humiliating videos'.
They threaten to proliferate these videos unless recipients send them a specific cryptocurrency sum (ransom). Do not trust this scam, since all claims are false.
"I know you are a pedophile" scam overview
According to scammers responsible for the "I know you are a pedophile Email" scam, recipients have downloaded software that installed a RAT on their computers. This allowed scammers to access the desktop, connect a camera (or webcam), and to access various files, passwords, and contact lists.
They claim that they have recorded four videos within which recipients can be seen watching sexual videos involving minors. Scammers threaten to send these videos to family members, friends, colleagues, and even the local police office unless they receive $5000 (equivalent in the Bitcoin cryptocurrency) within one week.
As mentioned above, however, "I know you are a pedophile Email" is merely a scam. Emails of this type can never be trusted. If you receive such an email in the inbox or spam folder, ignore the message and and delete it.
| Name | "I know you are a pedophile Email" scam. |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Scammers claim that they have recorded humiliating videos and will spread them unless they are paid within one week. |
| Ransom Size | $5000 in Bitcoins |
| Cyber Criminal Cryptowallet Address | 3HdxVRvF48cdVunEpGXj2r5hqafsYG2nEH, 362uSUuVfAd9YobrJK3zohiHwEs3UpUAJM |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the user's computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Examples of similar scams
Other examples of email scams are "ChaosCC hacker group", "The last time you visited a Porn website", and "Hacker who has access to your operating system". Generally, scammers behind them claim that they have recorded humiliating videos or photos and threaten to distribute them unless a specific sum is paid (typically, using a cryptocurrency).
In any case, these emails should never be trusted. In many cases, cyber criminals send emails that are used to distribute malware. They send the emails with attached files - if opened, these install malicious programs such as TrickBot, Hancitor, Emotet, FormBook, and so on.
How do spam campaigns infect computers?
Downloads and installations of malware through emails happen only when people open website links or files included within them.
Therefore, these emails are harmless unless recipients open the attached files or presented links. Typically, cyber criminals attach files such as Microsoft Office documents, JavaScript files, executable files such as .exe, archives such as ZIP, RAR, PDF documents, and so on.
For example, if the attached file is a MS Office document, it will demand permission to enable macros command (to enable editing) if opened. Giving such permission will allow it to install high-risk malware. Note that attached files cannot do any harm as long as they remain unopened.
How to avoid installation of malware?
All software and files should be downloaded from official websites and via direct links. Third party downloaders, unofficial pages, Peer-to-Peer networks such as torrent clients, eMule and other sources of this kind should not be trusted. They might be used as channels to distribute malicious software.
Furthermore, it is unsafe to use software 'cracking' tools to activate installed programs or operating systems. These can cause installation of malware. It is also illegal to activate programs with them. Installed software should be updated via tools or implemented functions that are designed by official software developers.
Third party updaters often distribute malware or other unwanted software. If the MS Office suite is installed with a version older than 2010, update it. Later versions include "Protected View" mode, which prevents rogue documents from installing malicious software. Also have reputable anti-virus or anti-spyware software installed and scan the system with it regularly.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
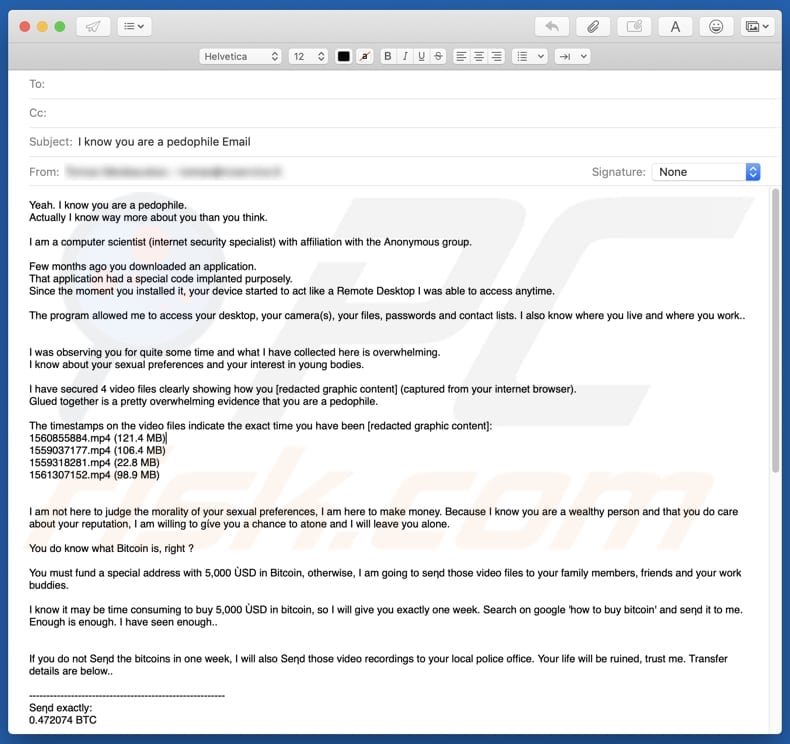
Text presented in the "I know you are a pedophile Email" message:
Yeah. I know you are a pedophile.
Actually I know way more about you than you think.I am a computer scientist (internet security specialist) with affiliation with the Anonymous group.
Few months ago you downloaded an application.
That application had a special code implanted purposely.
Since the moment you installed it, your device started to act like a Remote Desktop I was able to access anytime.The program allowed me to access your desktop, your camera(s), your files, passwords and contact lists. I also know where you live and where you work..
I was observing you for quite some time and what I have collected here is overwhelming.
I know about your sexual preferences and your interest in young bodies.I have secured 4 video files clearly showing how you - (captured from your internet browser).
Glued together is a pretty overwhelming evidence that you are a pedophile.The timestamps on the video files indicate the exact time you have been -:
1560855884.mp4 (121.4 MB)
1559037177.mp4 (106.4 MB)
1559318281.mp4 (22.8 MB)
1561307152.mp4 (98.9 MB)
I am not here to judge the morality of your sexual preferences, I am here to make money. Because I know you are a wealthy person and that you do care about your reputation, I am willing to give you a chance to atone and I will leave you alone.You do know what Bitcoin is, right ?
You must fund a special address with 5,000 USD in Bitcoin, otherwise, I am going to se?d those video files to your family members, friends and your work buddies.
I know it may be time consuming to buy 5,000 USD in bitcoin, so I will give you exactly one week. Search on google 'how to buy bitcoin' and send it to me.
Enough is enough. I have seen enough..
If you do not send the bitcoins in one week, I will also feed those video recordings to your local police office. Your life will be ruined, trust me. Transfer details are below..--------------------------------------------------------
Send exactly:
0.472074 BTCto my bitcoin address:
3HdxVRvF48cdVunEpGXj2r5hqafsYG2nEH
(copy and paste)
--------------------------------------------------------1 BTC is worth 10,485 USD right now, so send exactly: 0.472074 BTC.
Make sure the amount and address is copied correctly - this way I will know the transfer is coming from you.As soon as you send bitcoins, I will remove the videos from my drive and remove the software allowing me to access your device.
If you do not cooperate, I will start sending out those videos to people you care about.
Not excluded that after sending to one person, I will ask 10x more from you. I can make you suffer, trust me.Don't even think about going to police. If you try, I will immediately know it and I will feed them your -.
5,000 USD is a fair price for my Silence don't you think?You have only one week & better act fast.
--------------------------------------------------------
Send exactly:
0.472074 BTCto my bitcoin address:
3HdxVRvF48cdVunEpGXj2r5hqafsYG2nEH
(copy and paste)
--------------------------------------------------------
Do not reply to this email, it's an untraceable one time message.
I will contact you.Remember, I am watching you.
Sp3ctr3 (N1ghTm4r3)
A Spanish variant of "I Know You Are A Pedophile" email scam:
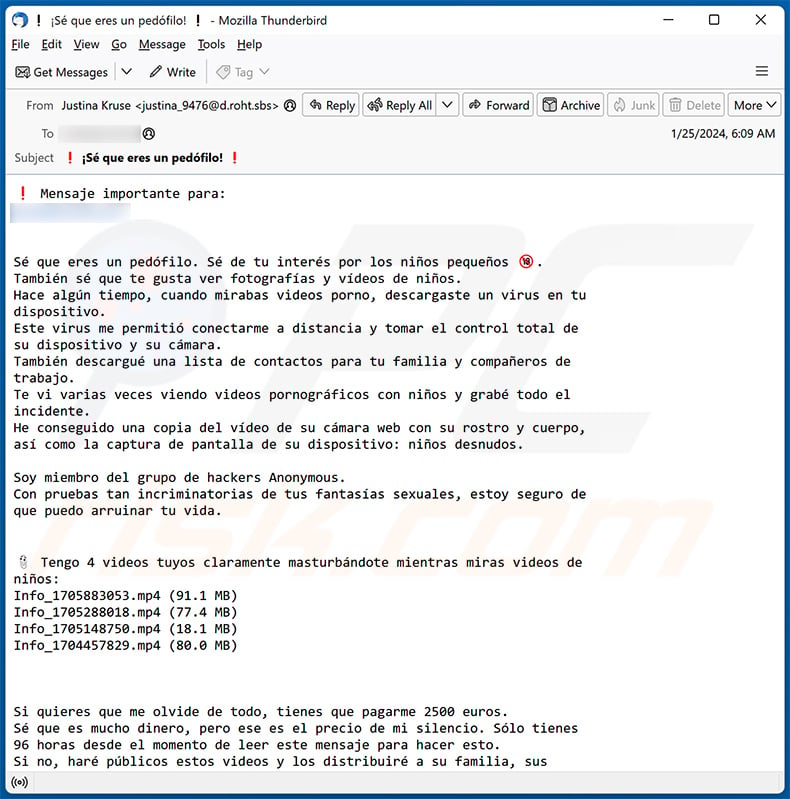
Text presented within:
Subject: ¡Sé que eres un pedófilo!
Mensaje importante para:
Sé que eres un pedófilo. Sé de tu interés por los niños pequeños.
También sé que te gusta ver fotografías y vídeos de niños.
Hace algún tiempo, cuando mirabas videos porno, descargaste un virus en tu
dispositivo.
Este virus me permitió conectarme a distancia y tomar el control total de
su dispositivo y su cámara.
También descargué una lista de contactos para tu familia y compañeros de
trabajo.
Te vi varias veces viendo videos pornográficos con niños y grabé todo el
incidente.
He conseguido una copia del vídeo de su cámara web con su rostro y cuerpo,
así como la captura de pantalla de su dispositivo: niños desnudos.Soy miembro del grupo de hackers Anonymous.
Con pruebas tan incriminatorias de tus fantasías sexuales, estoy seguro de
que puedo arruinar tu vida.
Tengo 4 videos tuyos claramente masturbándote mientras miras videos de
niños:
Info_1705883053.mp4 (91.1 MB)
Info_1705288018.mp4 (77.4 MB)
Info_1705148750.mp4 (18.1 MB)
Info_1704457829.mp4 (80.0 MB)Si quieres que me olvide de todo, tienes que pagarme 2500 euros.
Sé que es mucho dinero, pero ese es el precio de mi silencio. Sólo tienes
96 horas desde el momento de leer este mensaje para hacer esto.
Si no, haré públicos estos videos y los distribuiré a su familia, sus
colegas y la policía.
Tienes que pagar mediante transferencia de Bitcoin. Si no tienes suficientes
bitcoins, investiga cómo comprarlos y transfiérelos.
Puede utilizar intercambios en línea como Coinbase, Binance u otros para
comprar bitcoins.
1 Bitcoin ahora cuesta exactamente 36500 EUR.
Entonces envíe exactamente 0.0693694 BTC a la dirección a continuación.
Copie y pegue (¡tenga en cuenta las mayúsculas y minúsculas!).
Transferir:
0.0693694 BTC a:362uSUuVfAd9YobrJK3zohiHwEs3UpUAJM
¡Recuerda que solo tienes 96 horas para hacer esto y debes transferir la
cantidad exacta de 0.0693694 BTC (2500 EUR)!
Si envías la transferencia de Bitcoin, me olvidaré de todo, eliminaré el
virus de tu dispositivo y nunca más nos volveremos a ver.
Pero si no lo haces te garantizo que tu familia y todos tus amigos quedarán
asombrados con tus fantasías.
No hagas trampa... ¡Te vigilo!
Solo tienes 96 horas desde el momento en que recibiste este mensaje. Me
avisarán cuando leas esto.
Si tienes problemas para transferir o comprar bitcoins, puede que te dé
unos días más y me pondré en contacto contigo nuevamente, ¡pero tengo
que ver que estás intentando comprar btc para enviarme el dinero!Como tengo acceso a tus dispositivos y datos, sé mucho sobre ti y sé que
ganas bien.
¡Así que no trates de engañarme porque sé que puedes permitirte pagar!
Envío los detalles de la transferencia de Bitcoin a continuación.
Tienes que transferir el equivalente a 2500 EUR a BTC.
Transferir exactamente:
0.0693694 BTC a la dirección de Bitcoin:362uSUuVfAd9YobrJK3zohiHwEs3UpUAJM
(¡Copia esta dirección porque las mayúsculas y minúsculas son
importantes!)
Estoy esperando tu transferencia ... será mejor que pagues, de lo contrario
todos se enterarán de tus desviaciones ...---
.Anó.ni.mo
/No nos olvidamos. Nos espera./
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is I Know You Are A Pedophile spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Scammers often send out mass emails to a large number of email addresses, hoping that some recipients will fall for the scam.
I have provided my personal information when tricked by this email, what should I do?
In case you have shared your account credentials, it's essential to change your passwords right away. If you have disclosed personal details like credit card information or ID card details, it is important to notify the appropriate authorities as soon as possible.
I have downloaded and opened a malicious file attached to an email, is my computer infected?
If the file was an executable, it is very likely that your system could be infected. On the other hand, if it was a document file like .pdf or .doc, there is a chance you might be safe because simply opening such documents does not always lead to a malware infection.
Was my computer actually hacked and does the sender have any information?
It is unlikely that your computer has been hacked, infected, or compromised in any other way. Scammers often use previously obtained information, such as old passwords from leaked databases, to create a sense of legitimacy.
How did cyber criminals get my email password?
It is possible that cybercriminals gained access to your email through a data breach involving a website where you have an account. The stolen information from such breaches might include your login credentials. Additionally, these cybercriminals could have acquired your password through a phishing website or another deceptive page where it was provided.
I have sent cryptocurrency to the address presented in such email, can I get my money back?
Cryptocurrency transactions are practically impossible to trace, making it unlikely for you to recover the funds.
I have read the email but did not open the attachment, is my computer infected?
Simply accessing an email is safe. The potential for system infections arises when you interact by clicking on links or opening attached files within the email.
Will Combo Cleaner remove malware infections that were present in email attachment?
Combo Cleaner is effective in identifying and removing nearly all known malware infections. It is crucial to recognize that advanced malware tends to hide deeply within the system. A full system scan is highly recommended to ensure comprehensive detection and removal.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion