Do not trust the You've Been Hacked! email scam
Phishing/ScamAlso Known As: You've Been Hacked! spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the You've Been Hacked! email scam?
Commonly, scammers send emails claiming that they have stolen some personal information from people and demand payment in return for not publishing the details. This scam is no exception. These emails should never be trusted or opened.
Scammers behind this email claim that they have stolen login credentials for payment systems, social networks, email accounts, messengers, browser cookies, correspondence history from email accounts, messengers and social networks. They also claim that they have stolen text, photo, video and audio files stored on the computer.
According to scammers, they will not make any of the aforementioned information public as long as recipients pay US$250 equivalent in Bitcoins to the provided BTC wallet.
Note that there are many cases whereby, rather than asking for payment directly, scammers attempt to trick recipients into providing private, sensitive information (e.g., credit card details, passwords). These emails should be ignored.
| Name | You've Been Hacked! Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Sensitive information has been stolen. |
| Cyber Criminal Cryptowallet Address | 1MaRdde6X7SGuoCdFNL2fmgpLomdx7peGC |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
More examples of email scams are "PASSWORD EXPIRATION NOTICE Email Scam", "POLÍCIA SEGURANÇA PÚBLICA Email Scam" and "Xerox Scanned Document Email Scam". Generally, scammers behind them attempt to deceive unsuspecting recipients to transfer funds or provide personal information.
Note that emails can be used to proliferate malicious programs (e.g., Trojans, ransomware-type software) as well.
How do spam campaigns infect computers?
Ransomware and other malware infections are commonly spread through malspam campaigns, untrusted file/software download sources, fake (third party) software updating tools, Trojans and unofficial software activation tools. Using malspam, criminals send emails that have a malicious file attached, or include a website link designed to download a malicious file.
Their main goal is to trick recipients into executing the file, which then infects the computer with malware. Cyber criminals usually attach a Microsoft Office document, archive file (ZIP, RAR), PDF document, executable file (.exe) or JavaScript file, and wait until recipients open it.
Note that malicious MS Office documents can install malware only when users enable editing/content (macros commands). If the documents are opened with MS Office versions prior to 2010, however, the documents install malicious software automatically, since these older versions do not include "Protected View" mode.
Examples of untrusted file and software download sources are Peer-to-Peer networks (torrent clients), free file hosting websites, freeware download sites, and unofficial web pages. These are used to distribute malicious files by disguising them as legitimate and regular.
When users download and open (execute) the files, however, they inadvertently install malware. Fake software updating tools cause damage by installing malware rather than updates/fixes for installed software, or by exploiting bugs/flaws of outdated software.
Trojans are malicious programs that can cause chain infections by installing other software of this kind. Note that malware can only be distributed in this way if Trojans are already installed on computers.
Unofficial activation ('cracking') tools are illegal programs that supposedly activate licensed software free of charge and bypass activation, however, they often install other malicious programs instead.
How to avoid installation of malware
Download software and files from official websites and via direct links. It is not safe to use torrent clients, eMule (or other Peer-to-Peer networks), third party downloaders, unofficial websites or other sources of this kind. Avoid third party installers. Check "Advanced", "Custom" and other settings, and decline offers to download or install unwanted software.
Do not click ads that are displayed on dubious websites, since they can open other untrusted websites or even cause unwanted downloads and installations. Remove any unwanted, suspicious applications (extensions, add-ons, and plug-ins) that are installed on the browser.
The same should be applied to programs of this kind that are installed on the operating system. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
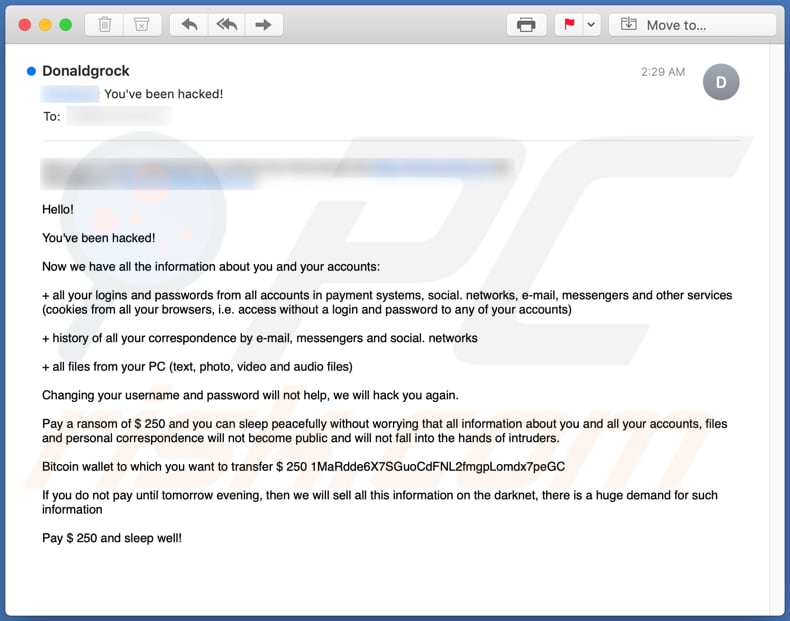
Text presented in the You've Been Hacked! email scam message:
Hello!
You've been hacked!
Now we have all the information about you and your accounts:
+ all your logins and passwords from all accounts in payment systems, social. networks, e-mail, messengers and other services (cookies from all your browsers, i.e. access without a login and password to any of your accounts)
+ history of all your correspondence by e-mail, messengers and social. networks
+ all files from your PC (text, photo, video and audio files)
Changing your username and password will not help, we will hack you again.
Pay a ransom of $ 250 and you can sleep peacefully without worrying that all information about you and all your accounts, files and personal correspondence will not become public and will not fall into the hands of intruders.
Bitcoin wallet to which you want to transfer $ 250 1MaRdde6X7SGuoCdFNL2fmgpLomdx7peGC
If you do not pay until tomorrow evening, then we will sell all this information on the darknet, there is a huge demand for such information
Pay $ 250 and sleep well!
Another variant of "You've Been Hacked!" scam email:
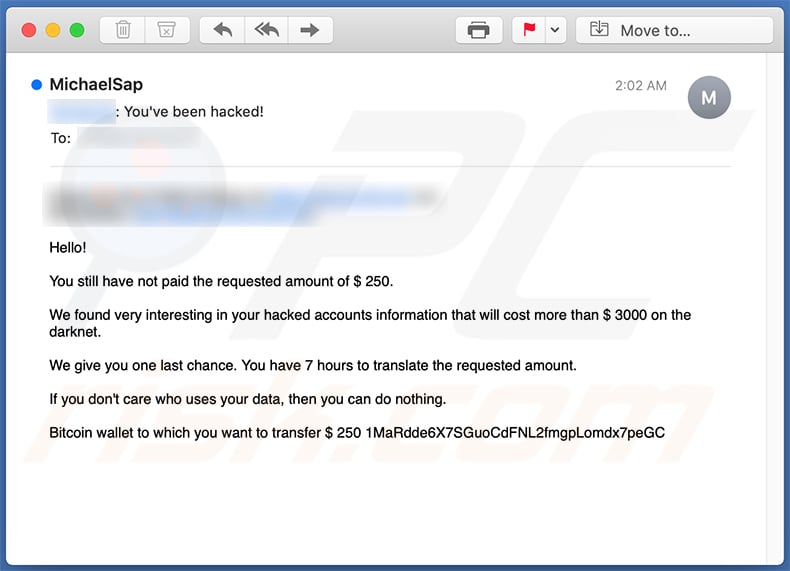
Text presented within:
Subject: - You've been hacked!
Hello!
You still have not paid the requested amount of $ 250.
We found very interesting in your hacked accounts information that will cost more than $ 3000 on the darknet.
We give you one last chance. You have 7 hours to translate the requested amount.
If you don't care who uses your data, then you can do nothing.
Bitcoin wallet to which you want to transfer $ 250 1MaRdde6X7SGuoCdFNL2fmgpLomdx7peGC
A Spanish variant of "You've Been Hacked!" spam email:
Text presented within:
Subject: Inicio de sesión completado con éxito, todos los datos de su dispositivo fueron copiados. Lea las instrucciones en el interior.
Buenos días!
Ésta es la última advertencia.
Su sistema ha sido hackeado.
Todos los datos de su dispositivo fueron copiados en nuestros servidores.
Además, hemos grabado un video de su cámara en el que está viendo una película porno.
Mi virus infectó su dispositivo a través de un sitio web para adultos que visitó recientemente.
Si no sabe cómo el funciona, compartiré los detalles.
El virus troyano me da un acceso completo y el control sobre el dispositivo que está utilizando.Como resultado, puedo ver su pantalla completa y encender la cámara y el micrófono sin que usted lo sabrá.
Capturé un video de su pantalla y de cámara del dispositivo y edité un video en el que en una parte de la pantalla se ve como usted se masturba, y la otra parte muestra un video pornográfico que abriste en ese momento.
Puedo ver la lista completa de sus contactos del teléfono y de todas las redes sociales.
Puedo enviar este video a toda la lista de contactos de su teléfono, del correo electrónico y de las redes sociales con un solo clic.
Además, puedo enviar los datos de sus correos electrónicos y mensajeros a todo el mundo.
En otras palabras, puedo destruir su reputación para siempre.
Si desea evitar un tal desarrollo de eventos, haga lo siguiente:Transfiera 1000 USD (dólares estadounidenses) a mi billetera bitcoin.
(Si no sabe cómo hacerlo, escriba en el cuadro de búsqueda de Google: "Comprar bitcoins").
Mi billetera bitcoin (BTC Wallet): bc1qvm5e9787awqcpul7zgkphzdeg46rz05t7azc5h
Tan pronto como llegue el pago, destruiré inmediatamente su video y garantizaré que no le molestaré más.
Tiene 50 horas (un poco más de 2 días) para completar este pago.
Recibo una notificación automática sobre lectura de esta carta.
El temporizador también se iniciará automáticamente después que usted ha leído esta carta electrónica.No intente quejarse donde sea, ya que mi billetera no puede ser rastreada.
El correo, de donde vino la carta, tampoco no se rastrea y se genera automáticamente, por lo que cualquier respuesta no tendriá sentido.Si intentas compartir esta carta con alguien, el sistema enviará automáticamente una solicitud a los servidores y ellos comenzarán a enviar todos los datos en las redes sociales.
El cambio de contraseñas en las redes sociales, en el correo electrónico o en su dispositivo no le ayudará, ya que todos los datos ya se han descargado en el clúster de mis servidores.
Le deseo buena suerte y no hacer nada estúpido. Considere su reputación.
A Czech variant of "You've Been Hacked!" scam email:
Text presented within:
Subject: Přihlášení bylo úspěšně vytvořeno, zkopírovalo všechna data z vašeho zařízení. Přečtěte si pokyny uvnitř.
Dobrý den
Tohle je poslední varování.
Váš systém byl hacknut.
Všechna data byla zkopírována z vašeho zařízení na naše servery.
Také z fotoaparátu bylo nahráno video s vaší účastí při sledování porna.
Můj virus infikoval vaše zařízení prostřednictvím webu pro dospělé,které jste nedávno navštívili.
Jestli nevíš, jak to funguje, podělím se o detaily.
Trojský virus mi dává plný přístup a kontrolu nad zařízením, které používáte.
V důsledku toho vidím celou obrazovku, zapínám kameru a mikrofon a ani o tom nebudete vědět.Zachytil jsem video z obrazovky a kamerového zařízení a namontoval video, na které je v jedné části obrazovky video jako masturbujete, a v jiném pornografickém videu, které jste v tu chvíli otevřeli.
Vidím celý seznam vašich kontaktů s vaším telefonem a všemi sociálními sítěmi.
V jednu chvíli mohu toto video odeslat do celého seznamu vašich telefonních, poštovních a sociálních médií.
Kromě toho mohu také odeslat všechna data z vašeho e-mailu i z poslů.Můžu ti navždy zničit reputaci.
Pokud se chcete těmto důsledkům vyhnout, pak:
Převádět $1200 (US$) do mé bitcoinové peněženky
(pokud nevíte, jak to udělat, napište na vyhledávací řádek Google: "Koupit Bitcoin").Moje bitcoinová peněženka (PENĚŽENKA BTC): bc1q4j4tz7mrtv858w9py3xgjxma2z0sfp6rez7mhq
Jakmile dorazí platba, okamžitě zničím vaše video a zaručím, že vás nebudu obtěžovat znovu.
Na tuto platbu máte 50 hodin (něco přes 2 dny).Dostal jsem automatické oznámení, abych si přečetl tento dopis.Podobně Časovač se automaticky přepne po přečtení aktuální zprávy.
Nepokoušejte se nikde stěžovat, protože peněženka nemůže sledovat, pošta, odkud dopis pochází, také není sledována a vytvořena automaticky, takže pro mě nemá smysl psát.
Pokud se pokusíte tento e-mail s někým sdílet, systém automaticky odešle požadavek na servery a začnou odesílat všechna data na sociální sítě.
změna hesel na sociálních sítích, na poště, v zařízení vám nepomůže, protože všechna data již byla stažena do clusteru mých serverů.
Hodně štěstí a neumož nic hloupého. Mysli na svou reputaci.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is You've Been Hacked! spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion