Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is the Snake keylogger?
Snake is a malicious program classified as a keylogger. As the classification implies, the primary function of this malware is keylogging. Therefore, Snake infections pose a threat to the privacy/safety of all typed information.
Snake keylogger in detail
Snake malware's main feature is keylogging (records key strokes), however, this program has other functionality as well. It can take screenshots and extract data stored in the clipboard (i.e. copy/paste buffer).
Furthermore, Snake can extract and exfiltrate stored information from certain browsers (e.g. Google Chrome, Mozilla Firefox, Opera, 360, etc.) and email clients (e.g. Mozilla Thunderbird, Microsoft Outlook, Foxmail, etc.). Malicious programs such as Snake are typically used to steal account log-in credentials (i.e. IDs, usernames and passwords) and financial information (e.g. banking account and credit card details etc.).
Communication/Messaging accounts (e.g. social media, social networking, messenger, etc.) are targeted by cyber criminals. Through these platforms, they can ask contacts/friends for loans and proliferate malware (by sharing infectious files) under the guise of the accounts' genuine owners.
Furthermore, should any sensitive/compromising content be found on hijacked data storage accounts, it can be held for ransom under threat of publication and/or sale to the victims' competitors. Accounts that directly deal with finances and/or store financial information (e.g. e-commerce, online money transfers, digital wallet, banking, etc.) are of particular interest, as through them, criminals can make fraudulent transactions and make online purchases.
To summarize, Snake infections can lead to serious privacy issues, financial loss and identity theft. If it is known or suspected that the Snake keylogger (or other malware) has already infected the system, use anti-virus software to remove it without delay.
| Name | Snake malware |
| Threat Type | Keylogger, password-stealing virus, banking malware, spyware. |
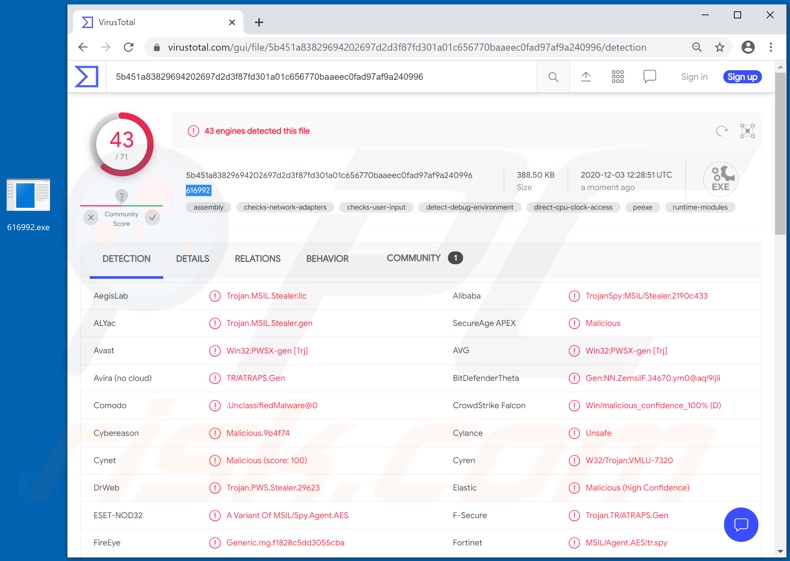
| Detection Names | Avast (Win32:PWSX-gen [Trj]), BitDefenderTheta (Gen:NN.ZemsilF.34670.ym0@aq!9ljli), ESET-NOD32 (A Variant Of MSIL/Spy.Agent.AES), Kaspersky (HEUR:Trojan-Spy.MSIL.Stealer.gen), Microsoft (Trojan:Win32/Meterpreter!ml), Full List Of Detections (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Malware of this type in general
404 Keylogger, Kutaki, Matiex, Hakops and Cheetah are some examples of other keyloggers. These malicious programs can have a wide variety of dangerous functionality in different combinations.
Common malware types/capabilities include (but are not limited to): download/installation of additional malicious programs, data encryption and/or screen-locking for ransom purposes (ransomware), audio/video recording via integrated and/or connected microphones and webcams, enablement of remote access and control over an infected machine, use of system resources for cryptocurrency mining (cryptominers), and so on.
Regardless of how malware operates, it always poses a threat to device/user safety. Therefore, it is crucial to eliminate all threats immediately upon detection.
How did Snake keylogger infiltrate my computer?
The Snake keylogger is offered for sale online with prices varying from US$25 to $US500 (USD) depending on operation timeframe, and support and range of functionality/customizability. Hence, how it is spread depends on the cyber criminals using it.
Popular malware proliferation methods are via backdoor/loader Trojans, spam campaigns, illegal activation ("cracking") tools, fake updaters and dubious download sources. Some types of Trojans are designed to cause chain infections (i.e. download/install additional malware).
When cyber criminals attempt to distribute malware via malspam campaigns, they send emails that contain malicious attachments or download links for malicious files. Typically, they disguise their emails as official and important. If recipients open the attached file (or a file downloaded via a website link), they cause installation of malicious software.
Cyber criminals commonly attach executable files (.exe), archive files such as RAR, ZIP, PDF documents, JavaScript files and Microsoft Office documents to their emails. Software 'cracking' tools supposedly activate licensed software illegally (bypass activation), however, they often install malicious programs and do not activate any legitimate installed software.
Trojans are other rogue programs that can cause chain infections. I.e., when a Trojan is installed on the operating system, it can install additional malware.
Free file hosting websites, freeware download websites, Peer-to-Peer networks (e.g., torrent clients, eMule), unofficial websites, and third party downloaders are examples of other sources that are used to distribute malware. Cyber criminals disguise malicious files as legitimate and regular. When users download and open them, they inadvertently infect their computers with malware.
Fake software updating tools install malicious software rather than updates/fixes for installed programs, or they exploit bugs/flaws of outdated software that is installed on the operating system.
How to avoid installation of malware
Do not trust irrelevant emails that have files attached (or contain website links) and are received from unknown, suspicious addresses. Software should not be downloaded or installed through third party downloaders, installers, unofficial pages or other similar sources/tools.
Use only official websites and direct links. Installed software should never be updated or activated with third party, unofficial tools, since they can install malware. Furthermore, it is illegal to use third party tools to activate licensed software.
The only legitimate way to update and activate software is to use tools and functions that are provided by the official developers. Regularly scan your computer with reputable antivirus or anti-spyware software and keep this software up to date.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Appearance of the website used to promote Snake keylogger (GIF):
An example of a spam email used to spread Snake keylogger:
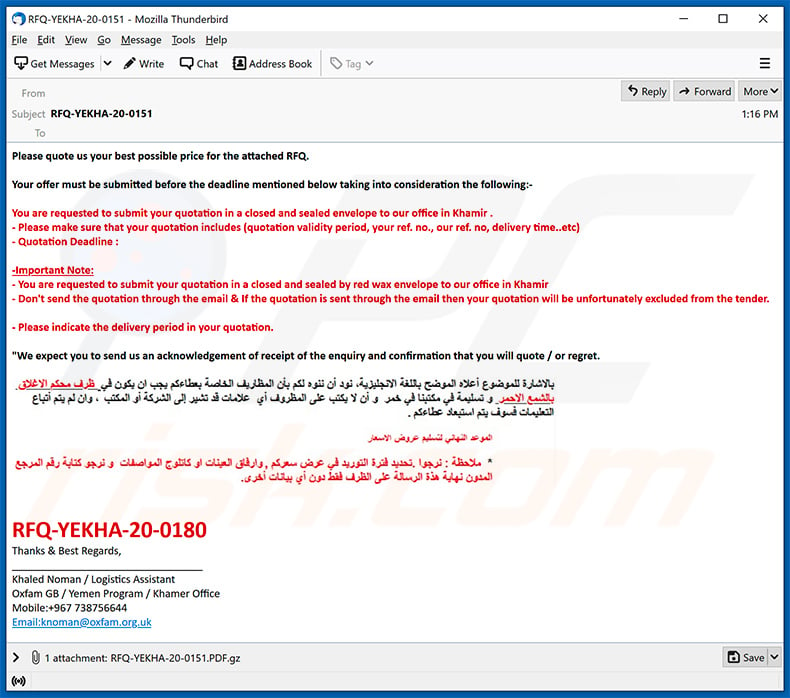
Text presented within:
Subject: RFQ-YEKHA-20-0151
Please quote us your best possible price for the attached RFQ.
Your offer must be submitted before the deadline mentioned below taking into consideration the following:-
You are requested to submit your quotation in a closed and sealed envelope to our office in Khamir .
- Please make sure that your quotation includes (quotation validity period, your ref. no., our ref. no, delivery time..etc)
- Quotation Deadline :-Important Note:
- You are requested to submit your quotation in a closed and sealed by red wax envelope to our office in Khamir
- Don't send the quotation through the email & If the quotation is sent through the email then your quotation will be unfortunately excluded from the tender.- Please indicate the delivery period in your quotation.
"We expect you to send us an acknowledgement of receipt of the enquiry and confirmation that you will quote / or regret.
RFQ-YEKHA-20-0180
Thanks & Best Regards,
_________________________________
Khaled Noman / Logistics Assistant
Oxfam GB / Yemen Program / Khamer Office
Mobile:+967 738756644
Email:knoman@oxfam.org.uk
Another example of a spam email spreading Snake keylogger:
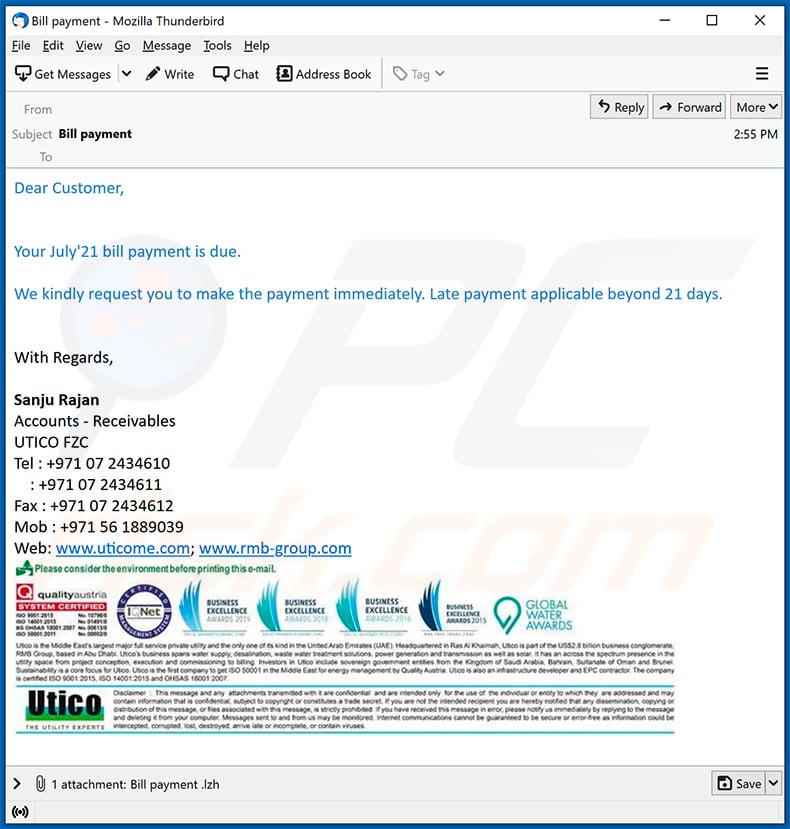
Text presented within:
Subject: Bill payment
Dear Customer,
Your July'21 bill payment is due.
We kindly request you to make the payment immediately. Late payment applicable beyond 21 days.
With Regards,
Sanju Rajan
Accounts - Receivables
UTICO FZC
Tel : +971 07 2434610
: +971 07 2434611
Fax : +971 07 2434612
Mob : +971 56 1889039
Web: www.uticome.com; www.rmb-group.com
A quotation-themed spam email spreading Snake keylogger via malicious attachment (MS Word document):
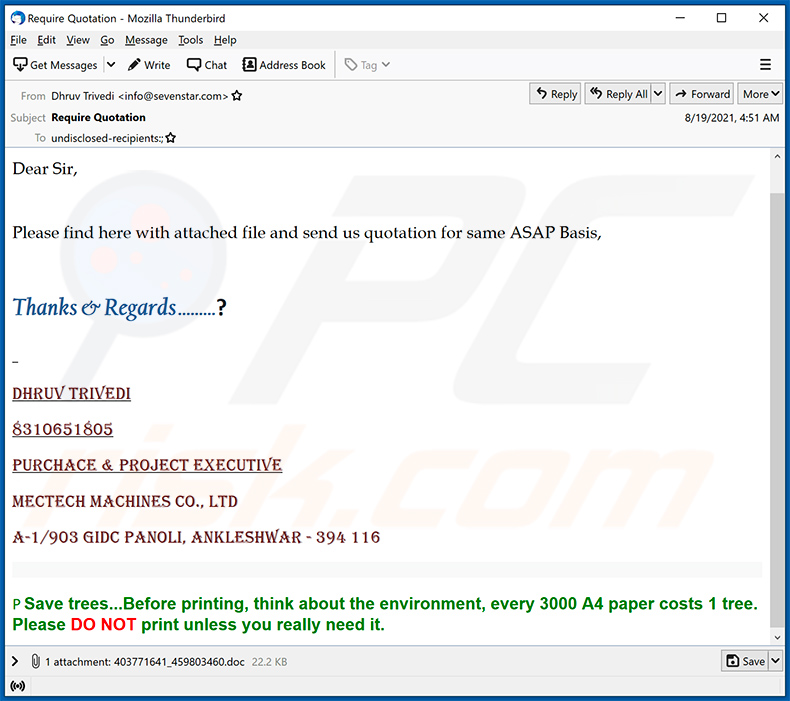
Text presented within:
Subject: Require Quotation
Dear Sir,
Please find here with attached file and send us quotation for same ASAP Basis,
Thanks & Regards .........?
Dhruv Trivedi
8310651805
Purchace & Project Executive
MECTECH MACHINES CO., LTD
A-1/903 GIDC Panoli, Ankleshwar - 394 116
P Save trees...Before printing, think about the environment, every 3000 A4 paper costs 1 tree. Please DO NOT print unless you really need it.
Yet another example of a spam email spreading Snake keylogger:
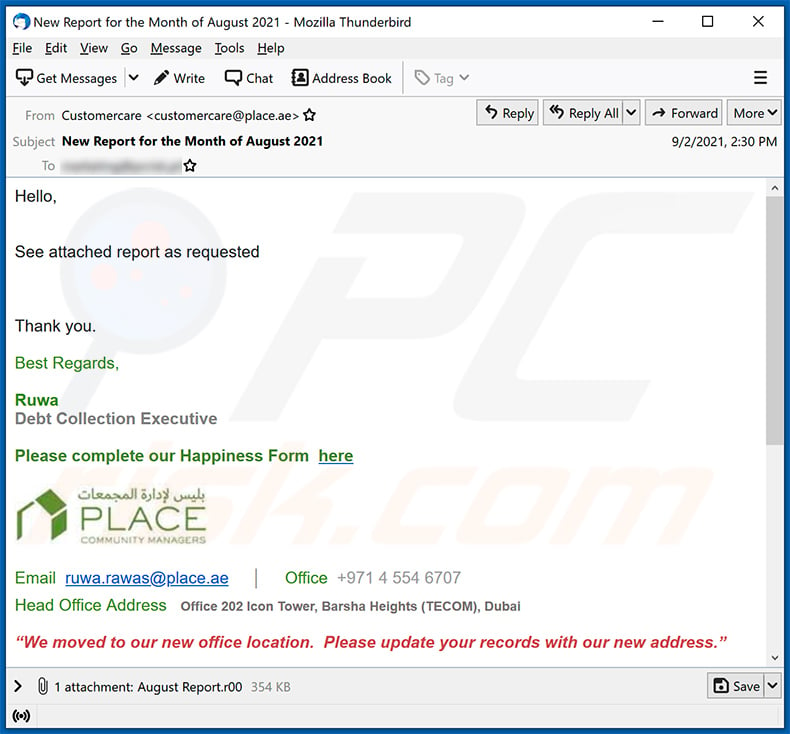
Text presented within:
Subject: New Report for the Month of August 2021
Hello,
See attached report as requested
Thank you.
Best Regards,
Ruwa
Debt Collection Executive
Please complete our Happiness Form here
Email ruwa.rawas@place.ae │ Office +971 4 554 6707
Head Office Address Office 202 Icon Tower, Barsha Heights (TECOM), Dubai
“We moved to our new office location. Please update your records with our new address.”
Please consider the environment before printing this e-mailDisclaimer
The information contained in this communication is intended solely for the use of the individual or entity to whom it is addressed and others authorised to receive it. It may contain confidential or legally privileged information. If you are not the intended recipient you are hereby notified that any disclosure, copying, distribution or taking any action in reliance on the contents of this information is strictly prohibited and may be unlawful. If you have received this communication in error, please notify us immediately by responding to this email and then delete it from your system. Place Strata Management LLC is neither liable for the proper and complete transmission of the information contained in this communication nor for any delay in its receipt.
All original content in this mail and attachments are subject to © PLACE Strata Management LLC 2009.
Yet another spam email spreading Snake Keylogger:
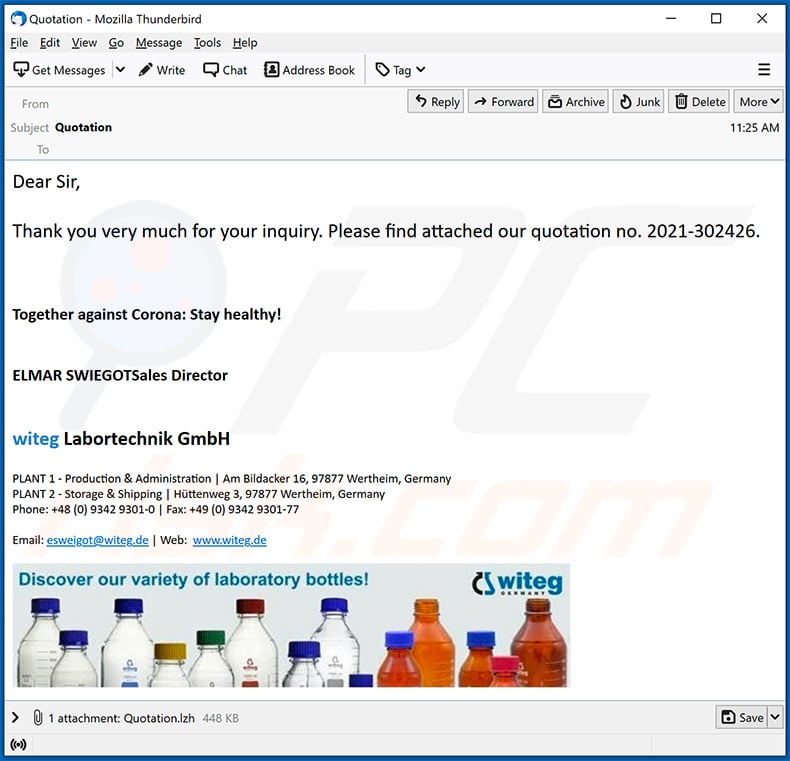
Text presented within:
Subject: Quotation
Dear Sir,
Thank you very much for your inquiry. Please find attached our quotation no. 2021-302426.
Together against Corona: Stay healthy!
ELMAR SWIEGOTSales Directorwiteg Labortechnik GmbH
PLANT 1 - Production & Administration | Am Bildacker 16, 97877 Wertheim, Germany
PLANT 2 - Storage & Shipping | Hüttenweg 3, 97877 Wertheim, Germany
Phone: +48 (0) 9342 9301-0 | Fax: +49 (0) 9342 9301-77
Email: esweigot@witeg.de | Web: www.witeg.de
Screenshot of a malicious email attachment (MS Exel document) usred to inject Snake keylogger into the system:
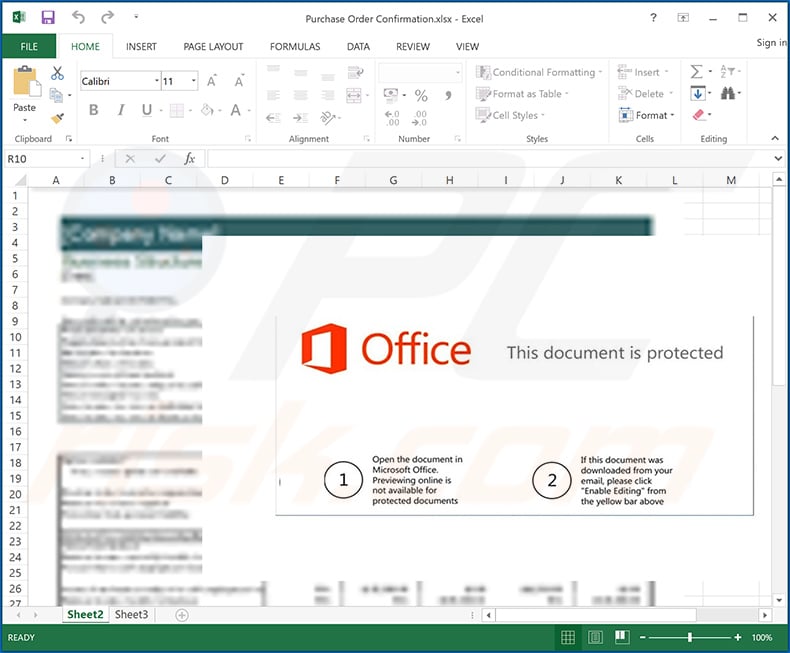
Update May 25, 2022 - a new spam campaign proliferating the Snake keylogger has been discovered. The spam emails carried a PDF attachment titled "REMMITANCE INVOICE.pdf". Once opened, the Adobe Reader program displays a request to open a Microsoft Word document.
This file is intentionally named "has been verified. However PDF, Jpeg, xlsx, .docx" - so that the filename would match Adobe Reader's warning. Hence, instead of seeing that the document they're about to open might be malicious - users are presented with a statement that the file was verified, but the following formats may be harmful.
After the MS Word document is opened, the infection chain depends on whether the "Protected View" mode is enabled or disabled. If the mode is active, the infection process begins after users enable the malicious macro commands (i.e., editing/content).
Detailed description of the infection process employed in this campaign can be found in an article on the HP Wolf Security Blog.
Update February 20, 2025 – new version of the Snake keylogger has been discovered. This variant relies on a new anti-detection mechanism wherein the primary payload (Snake) is infiltrated and executed through the use of the AutoIt programming language. Basically, an AutoIt-compiled binary serves as the executable containing Snake – thus, the infection can evade traditional detection measures.
The preferred method for distributing this malware remains to be email spam campaigns. Significantly affected areas include Taiwan, China, Indonesia, Turkey, and Spain.
Update March 26, 2025 – Snake keylogger's design shows a continued emphasis on stealth and anti-analysis. The latest variant is still distributed using the same method – email spam campaigns. Snake malware infiltrates devices through a multi-stage infection chain.
The email attachment is a .IMG (Disc Image Data File) disguised as a PDF document. When this file is opened, it creates a virtual drive to access the data therein. The file within the .IMG is an executable – and with it begins the first stage of the infection.
The executable is a downloader and loader that, upon launch – connects to the attackers' C&C server to retrieve an encrypted payload. In the second stage, a DLL file (Dynamic Link Library) is dynamically loaded into memory. The DLL is likewise highly obfuscated.
The payload (Snake keylogger) is then injected by using the process hollowing technique – wherein a new process is created in a suspended state, and the legitimate memory region is unmapped while malicious code is inserted into the hallowed space prior to the process resuming.
More information on these developments can be found in an article on the Seqrite blog.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Snake keylogger?
- STEP 1. Manual removal of Snake keylogger.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Snake keylogger, should I format my storage device to get rid of it?
No, it is not necessary to format the storage device to eliminate this malware. Snake keylogger can be removed without formatting.
What are the biggest issues that malware can cause?
The problems that malware can cause depend on the type of malware. Victims can lose access to personal accounts, files, suffer monetary loss, have their identities stolen, and encounter other issues.
What is the purpose of Snake keylogger?
This malware is used to steal sensitive information such as banking account and credit card details, login credentials, and other information typed with a keyboard, saved on certain browsers and the clipboard. Cybercriminals behind it can misuse obtained information to steal accounts, make fraudulent purchases, transactions, trick other users into providing information (or installing malware), and other purposes.
How did a malware infiltrate my computer?
Usually, malware is distributed using various phishing and other social engineering techniques (such as malicious emails, fake system warning messages, etc.), drive-by downloads, Peer-to-Peer (P2P) networks, unofficial websites. Also, cybercriminals distribute malware using software cracking tools/installers for pirated software, fake installers.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and eliminate almost all known malicious software. In order to remove high-end malware from the operating system, it is required to scan it fully (using a full scan).
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion