Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is JPMorgan Chase Email Virus?
"JPMorgan Chase Email Virus" is a spam email campaign identical to Bank of America Email Virus and Wells Fargo Email Virus. This campaign is used to proliferate trojan-type malware called Emotet.
As with the aforementioned spam campaigns, "JPMorgan Chase Email Virus" emails contain a message stating that a transaction is complete and encourages users to read the attached Microsoft Word document (.doc) for detailed information. This is a scam - the opened file immediately downloads and installs Emotet on the system.
As mentioned, "JPMorgan Chase Email Virus" emails encourages users to read the attached MS Word file for detailed information regarding a transaction. In addition, the email is presented as a message from JPMorgan Chase, which is a legitimate company. This technique is very common among cyber criminals.
These people hide behind the names of legitimate companies and governmental agencies, since it is much simpler to give an impression of legitimacy and convince users to open malicious files using familiar companies/names. After system infiltration, Emotet starts recording various information such as saved logins/passwords, web browsing activity, and so on.
These details might allow cyber criminals access to users' personal accounts (social networks, banks, etc.) Therefore, the presence of the Emotet trojan can lead to significant financial loss and even identity theft.
If you have recently opened a "JPMorgan Chase Email Virus" attachment, there is a high probability that your computer is infected. Therefore, you are advised to scan it with a legitimate anti-virus/anti-spyware suite and eliminate all detected threats.
| Name | JPMorgan Chase spam |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
There are many trojan-type viruses that have similar characteristics to Emotet including, for example, LokiBot, Adwind, FormBook, and TrickBot.
As with Emotet, most trojans are also distributed using spam email campaigns and collect information. In some cases, however, trojans might distribute other viruses (for example, ransomware). In summary, viruses such as Emotet pose a significant threat to your privacy and computer safety.
How did JPMorgan Chase Email Virus infect my computer?
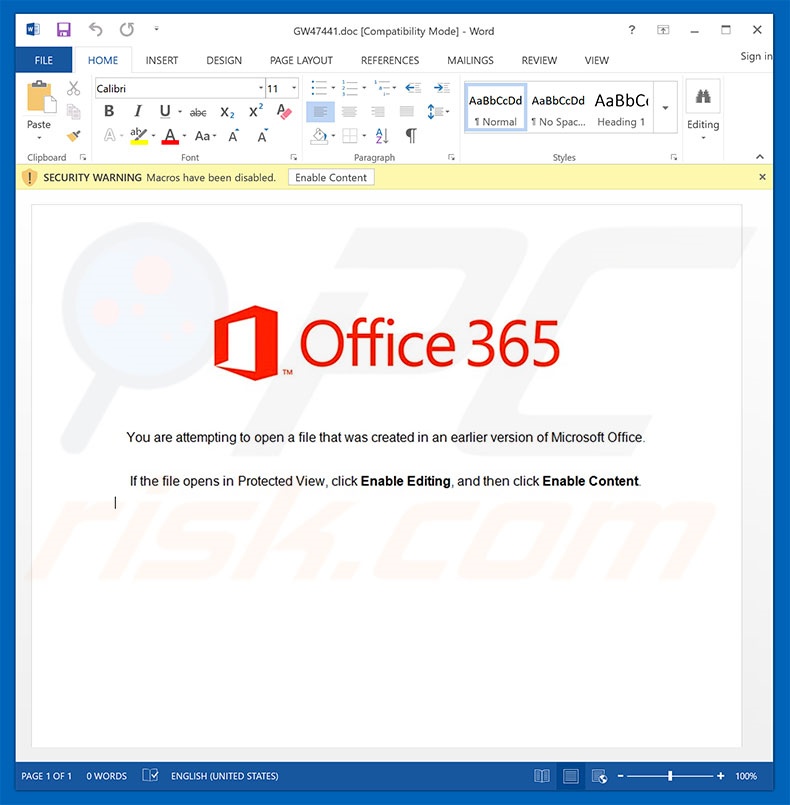
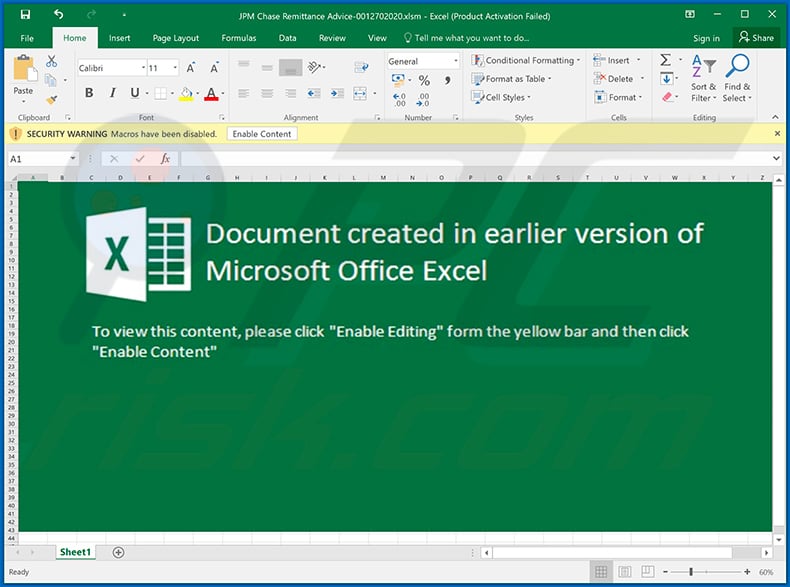
"JPMorgan Chase Email Virus" distributes a malicious Microsoft Word document that, once opened, asks users to enable macro commands, otherwise the content will not be displayed properly. By enabling macros, however, users grant permission to execute commands that stealthily install and download Emotet trojans.
This malware distribution method is effective, but has a major flaw. The malicious document is not able to download malware if opened using an application other than MS Word.
If the file is opened using other software capable of reading the .doc format, Emotet will not be infiltrated. In addition, this virus is designed to infect the Windows Operating System only and users of other platforms are safe.
How to avoid installation of malware?
Lack of knowledge and careless behavior are the main reasons for computer infections. Caution is the key to safety. Therefore, pay close attention when browsing the Internet. Carefully analyze each email attachment received.
If the file seems irrelevant or has been received from a suspicious/unrecognizable email address, it should never be opened - these emails should be deleted without reading. Having a reputable anti-virus/anti-spyware suite installed and running is also paramount.
2010 and newer versions of Microsoft Office open newly-downloaded documents in "Protected View" mode, which prevents malicious documents from downloading/installing malware.
Therefore, using older versions of MS Office is risky. If you have already opened a "JPMorgan Chase Email Virus" attachment, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
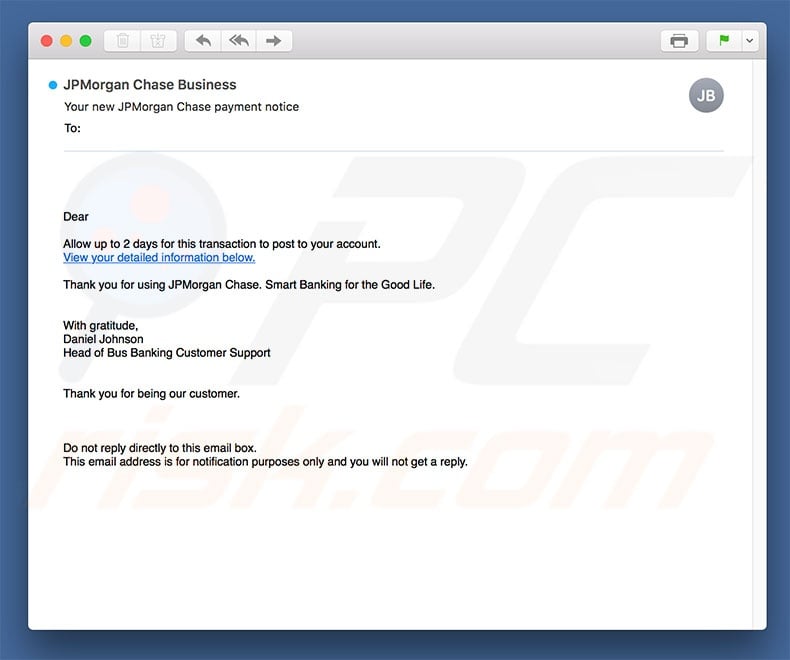
Text presented in the "JPMorgan Chase Email Virus" email letter:
Subject: Your new JPMorgan Chase payment notice
Allow up to 2 days for this transaction to post to your account.
View your detailed information below.
Thank you for using JPMorgan Chase. Smart Banking for the Good Life.
With gratitude,
Daniel Johnson
Head of Bus Banking Customer Support
Thank you for being our customer.
Do not reply directly to this email box.
This email address is for notification purposes only and you will not get a reply.
Malicious attachment distributed via "JPMorgan Chase Email Virus" spam campaign:
Update January 31, 2019 - "JPMorgan Chase" email spam campaign is also used to proliferate a high-risk trojan called TrickBot.
Screenshot of the "JPMorgan Chase" email letter distributing TrickBot (malicious MS Excel attachment):
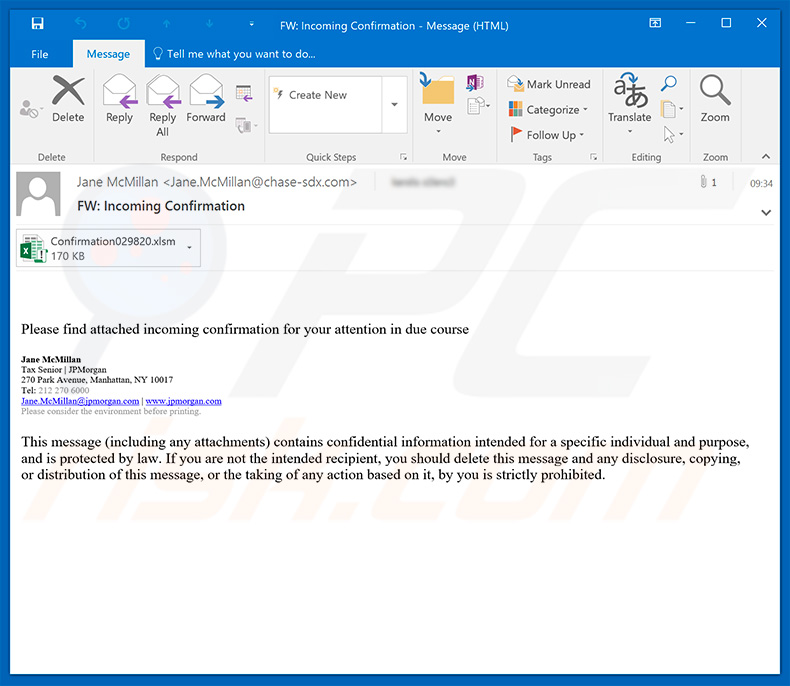
Text presented within this letter:
Subject: FW: Incoming Confirmation
Please find attached incoming confirmation for your attention in due course
Jane McMillan
Tax Senior | JPMorgan
270 Park Avenue, Manhattan, NY 10017
Tel: 212 270 6000
Jane.McMillan@jpmorgan.com | www.jpmorgan.com
Please consider the environment before printing.
This message (including any attachments) contains confidential information intended for a specific individual and purpose, and is protected by law. If you are not the intended recipient, you should delete this message and any disclosure, copying, or distribution of this message, or the taking of any action based on it, by you is strictly prohibited.
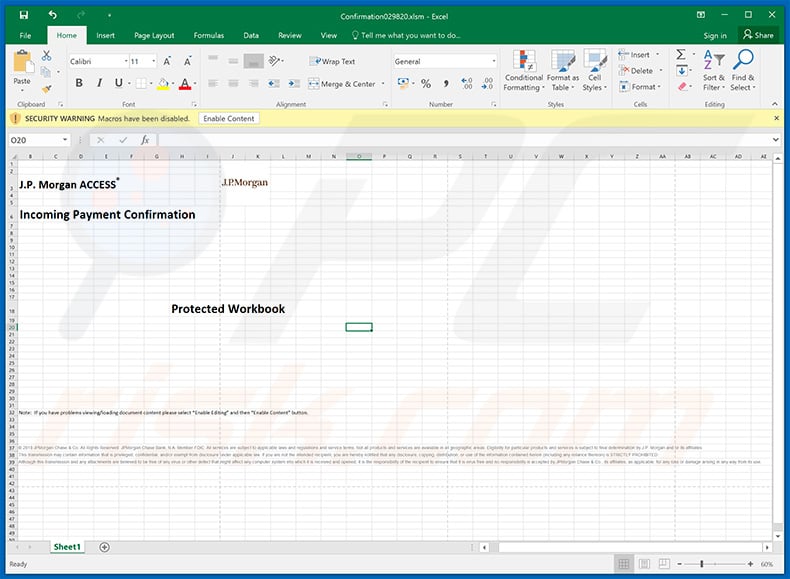
Screenshot of malicious attachment asking to enable macro commands:
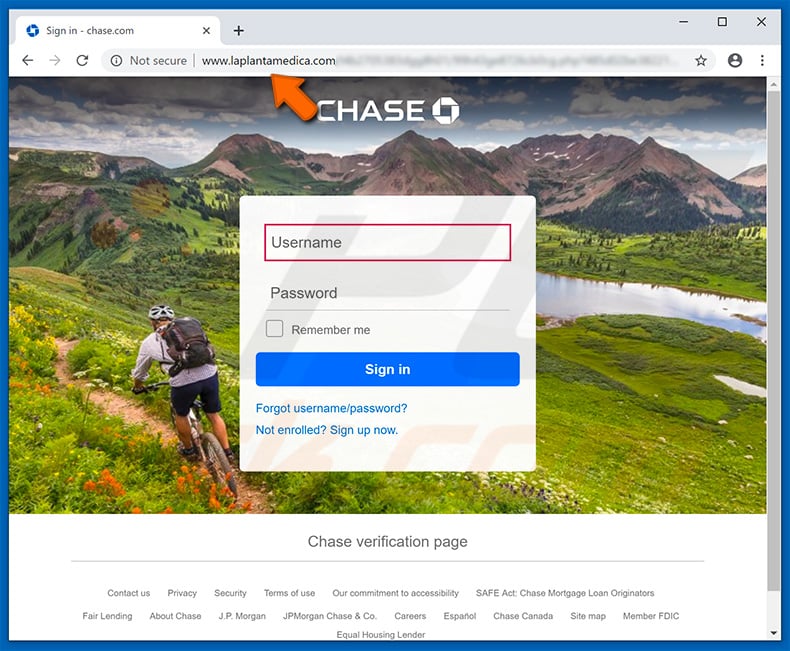
Update May 30, 2019 - Crooks have started using "JPMorgan Chase" email spam campaign to steal personal data. They send email letters encouraging recipients to verify their accounts by logging in. The email also contains a link to login page, which is actually a malicious website designed to save entered credentials in a remote server.
Screenshot of such email:
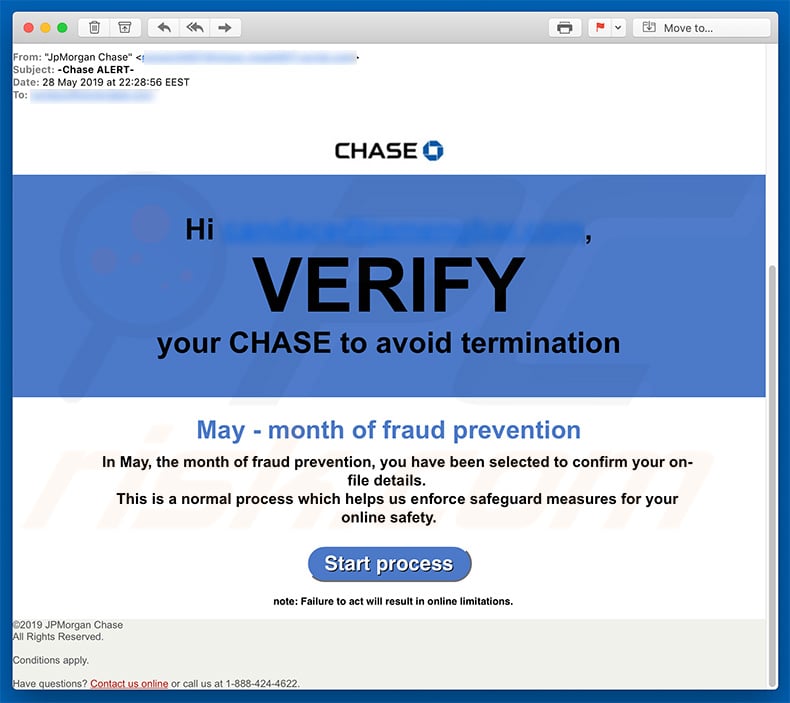
Text presented within this email:
Hi *,
VERIFY
your CHASE to avoid termination
May - month of fraud prevention
In May, the month of fraud prevention, you have been selected to confirm your on-file details.
This is a normal process which helps us enforce safeguard measures for your online safety.
Start processnote: Failure to act will result in online limitations.©2019 JPMorgan Chase
All Rights Reserved.Conditions apply.
Have questions? Contact us online or call us at 1-888-424-4622.
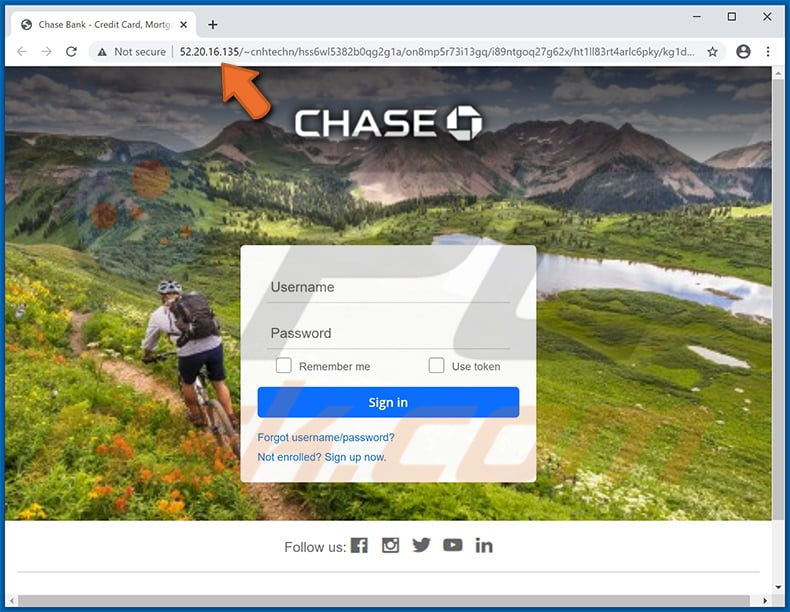
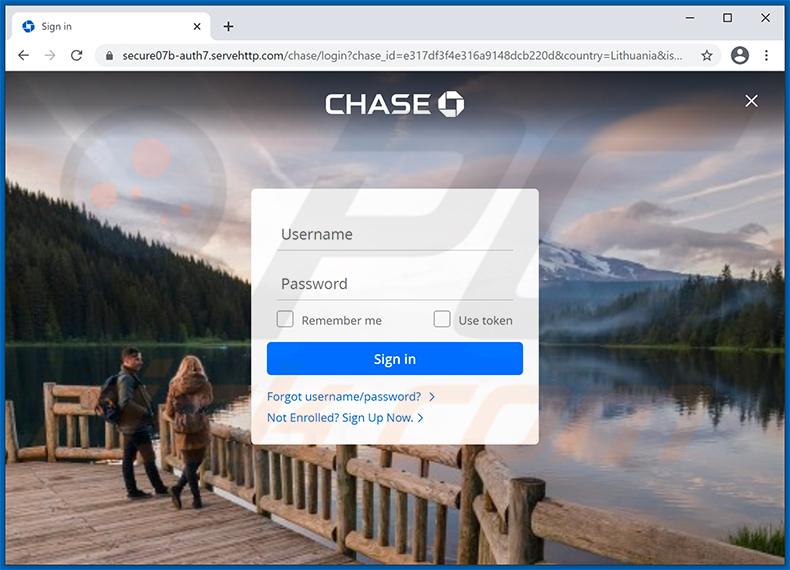
Screenshot of deceptive site:
A variant of JPMorgan Chase-themed spam email used to spread Remcos RAT:
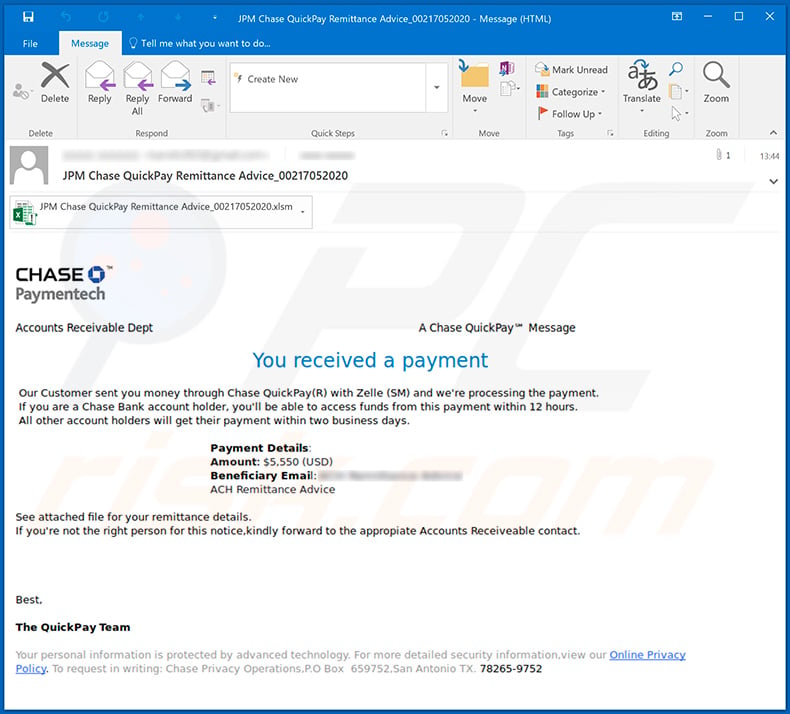
Text presented within:
Subject: JPM Chase QuickPay Remittance Advice_00217052020
CHASE
Paymentech
A Chase QuickPay℠ Message
Accounts Receivable Dept
You received a payment
Our Customer sent you money through Chase QuickPlay(R) with Zelle (SM) and we're processing the payment.
If you are a Chase Bank account holder, you'll be able to access funds from this payment within 12 hours.
All other account holders will get their payment within two business days.Payment Details:
Amount: $5,550 (USD)
Beneficiary Email: -
ACH Remittance AdviceSee attached file for your remittance details.
If you're not the right person for this notice,kindly forward to the appropiate Accounts Receiveable contact.Best,
The QuickPay Team
Your personal information is protected by advanced technology. For more detailed security information,view our Online Privacy Policy. To request in writing: Chase Privacy Operations, P.O Box 659752,San Antonio TX. 78265-9752
Screenshot of the malicious MS Excel document ("JPM Chase Remittance Advice-0012702020.xlsm") attached to this email:
Example of yet another JPMorgan Chase-themed spam email used for phishing purposes:
Text presented within:
Subject: Payment Authorization
Download Capital One App
Visit Capital One Sign In
Thanks for scheduling your payment.
Confirmation Number: XXXXXXXXX92491Hi,
Thanks for scheduling your credit card payment with Online Banking. Here are the details:
Payment amount: $650.00
Posted date: July 05,2020
If something doesn't look right to you, cancel scheduled payment now and review your details. We're here to help you, 24 hours a day, 7 days a week.Was this email helpful? Tell us what you think in one click.
Absolutely
Sure
Neutral
Not Really
Nope
Important Information from Chase BankContact Us | Privacy | Help Prevent Fraud
To ensure delivery, add capitalone@notification.chase.com to your address book.
This email was sent to and contains information directly related to your account with us, other services to which you have subscribed and/or any application you may have submitted.
Unsubscribe with one click if you and no longer want to receive this account alert.
The site may be unavailable during normal maintenance or due to unforeseen circumstances.
Please visit our Set Alerts page to modify your alerts subscription preferences.
Please do not reply to this message, as this email inbox is not monitored. To contact us, visit www.chase.com/contact.
Products and services offered by the Chase Bank family of companies, including Chase Bank Bank (USA), N.A., and Chase Bank, N.A., Members FDIC.
c 2020 Chase Bank. Chase Bank is a federally registered service mark.
PAYPST 10002 58914
Another example of JPMorgan Chase-themed spam website used to promote a phishing website:
Text presented within:
Subject: Action Needed: Please confirm you made these purchases
Having trouble viewing this e-mail? Please Click Here.
Dear Customer,
Please tell us if you, or someone you authorized, used your Account for direct debit:
BED BATH & BEYOND $795.00 Declined January 25
BED BATH & BEYOND $580.00 Declined January 25
BED BATH & BEYOND $449.50 Declined January 25
Do you recognize each transaction listed above?
- Your account remains active.
- If a purchase was declined, you will not be charged unless you try again.
- We'll block your account and call you.
- If you need to speak with us, call the number on the back of your card.
Sincerely,
Chase Fraud Protection ServicesPlease visit the Customer Center at www.chase.com to make sure your contact information is up to date.
Security Tip:
Chase will never ask you for your account number or password in an e-mail.
E-mail intended for your protection
If you have concerns about the authenticity of this message, please visit chase.com/CustomerService for options on how to contact us, or call the phone number on the back of your credit card and reference the Chase Library Code: PTRC. If you would like to learn more about e-mail security or want to report a suspicious e-mail, click here.ABOUT THIS MESSAGE
This service email gives you updates and information about your Chase relationship.This email was sent from an unmonitored mailbox, go to chase.com/CustomerService for options on how to contact us.
Your privacy is important to us. See our online Security Center to learn how to protect your information.
Chase Privacy Operations, PO Box 659752, San Antonio, Texas 78265-9752.
© 2021 JPMorgan Chase & Co.
Screenshot of the promoted phishing site:
Screenshot of yet another JPMorgan Chase-themed spam email:
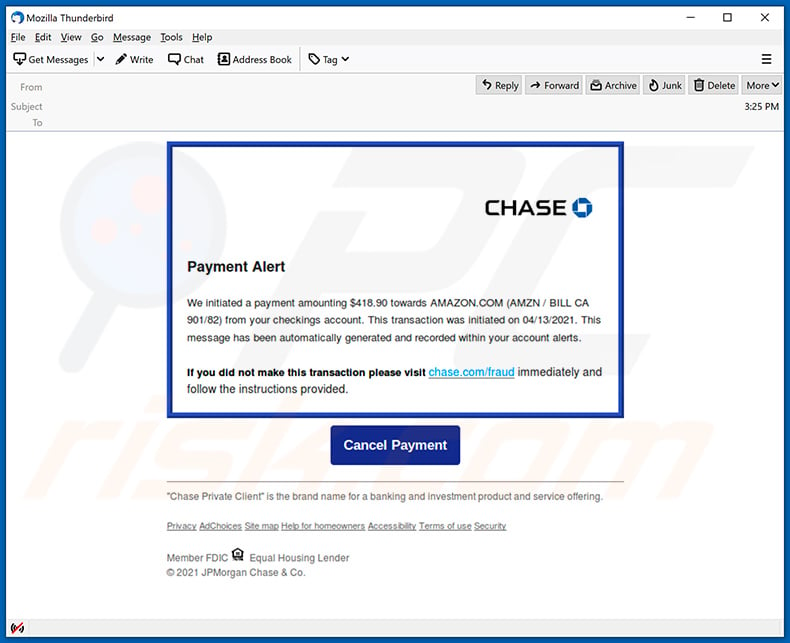
Text presented within:
CHASE
Payment Alert
We initiated a payment amounting $418.90 towards AMAZON.COM (AMZN / BILL CA 901/82) from your checkings account. This transaction was initiated on 04/13/2021. This message has been automatically generated and recorded within your account alerts.
If you did not make this transaction please visit chase.com/fraud immediately and follow the instructions provided.
[Cancel Payment]
"Chase Private Client" is the brand name for a banking and investment product and service offering.
Privacy AdChoices Site map Help for homeowners Accessibility Terms of use Security
Member FDIC Equal Housing Lender
© 2021 JPMorgan Chase & Co.
Screenshot of the promoted phishing website:
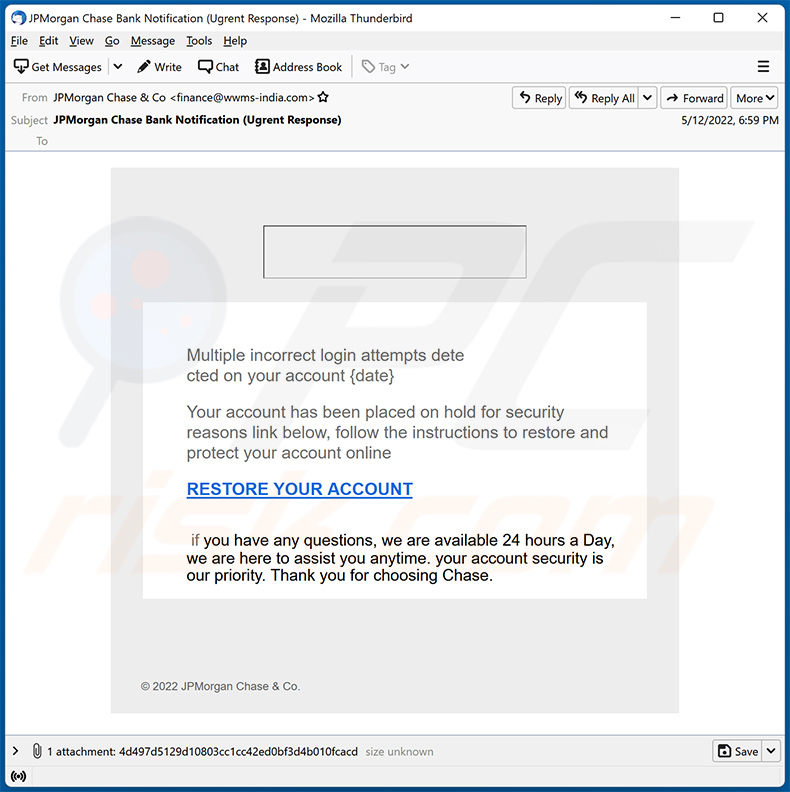
Additional example of JPMorgan Chase-themed spam email distributing a malicious attachment:
Text presented within:
Subject: JPMorgan Chase Bank Notification (Ugrent Response)
Multiple incorrect login attempts dete cted on your account {date}
Your account has been placed on hold for security reasons link below, follow the instructions to restore and protect your account online
RESTORE YOUR ACCOUNT
if you have any questions, we are available 24 hours a Day, we are here to assist you anytime. your account security is our priority. Thank you for choosing Chase.© 2022 JPMorgan Chase & Co.
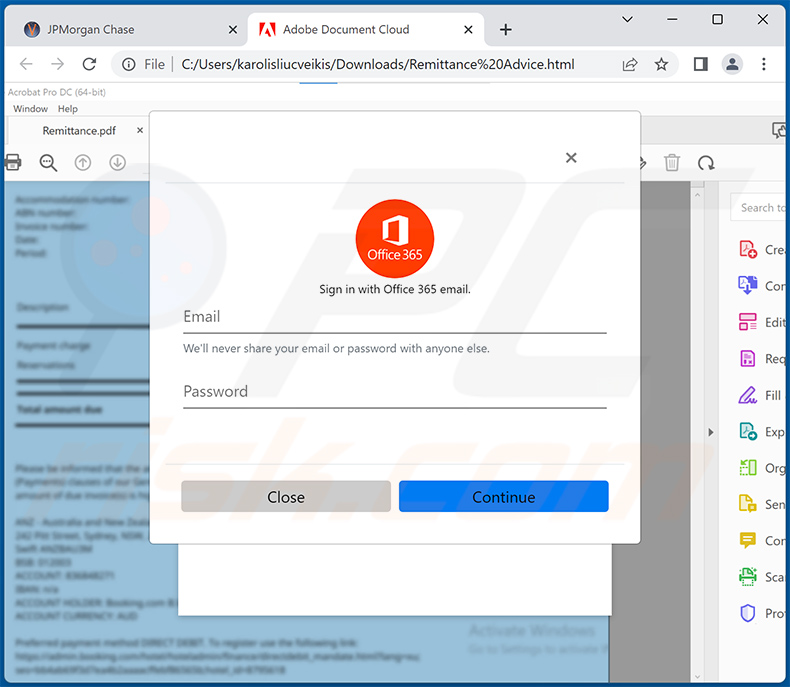
Here's an example of a malicious JPMorgan Chase-themed HTML document distributed via spam emails. The document contains a button ("View Remittance Advice") which downloads another HTML document used for phishing purposes.
Screenshot of the JPMorgan Chase-themed HTML document:
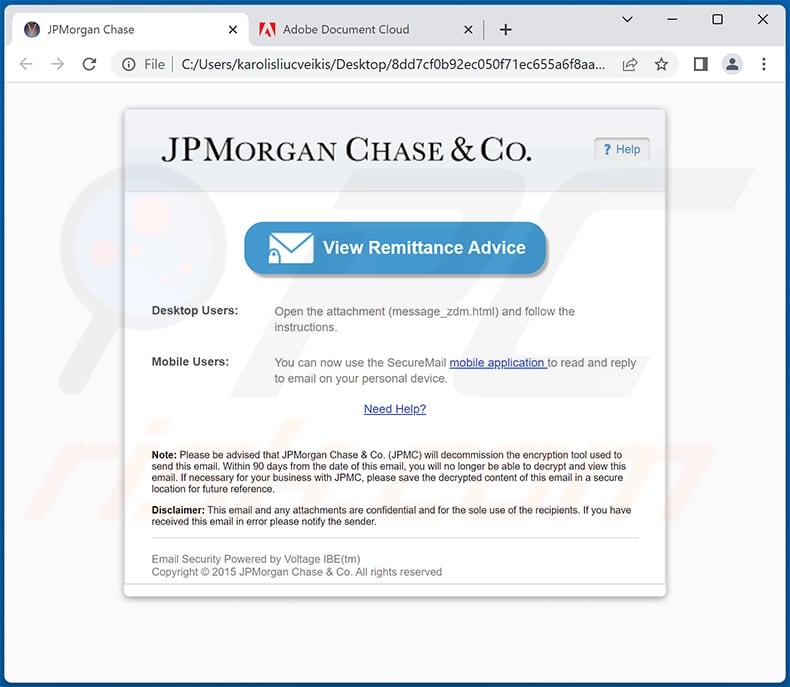
Text presented within:
JPMORGAN CHASE & Co.
View Remittance Advice
Desktop Users:
Open the attachment (message_zdm.html) and follow the instructions.Mobile Users:
You can now use the SecureMail mobile application to read and reply to email on your personal device.Need Help?
Note: Please be advised that JPMorgan Chase & Co. (JPMC) will decommission the encryption tool used to send this email. Within 90 days from the date of this email, you will no longer be able to decrypt and view this email. If necessary for your business with JPMC, please save the decrypted content of this email in a secure location for future reference.
Disclaimer: This email and any attachments are confidential and for the sole use of the recipients. If you have received this email in error please notify the sender.
Email Security Powered by Voltage IBE(tm)
Copyright © 2015 JPMorgan Chase & Co. All rights reserved
Screenshot of the downloaded HTML document:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is JPMorgan Chase spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion