Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of software is Remcos?
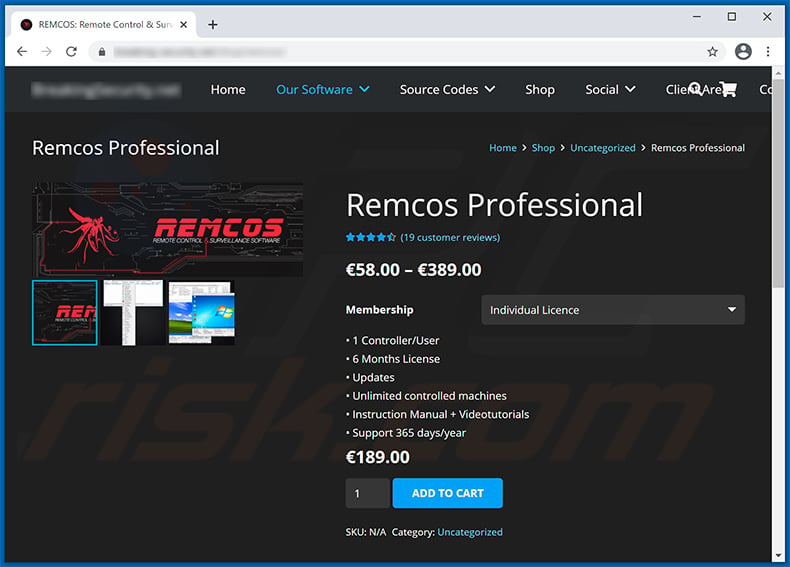
Remcos (Remote Control and Surveillance) is a Remote Access Tool (RAT) that anyone can purchase and use for whatever purpose they wish. The tool itself is is presented as legitimate, however, although Remcos's developers strictly forbid misuse, some cyber criminals use this tool to generate revenue by various malicious means.
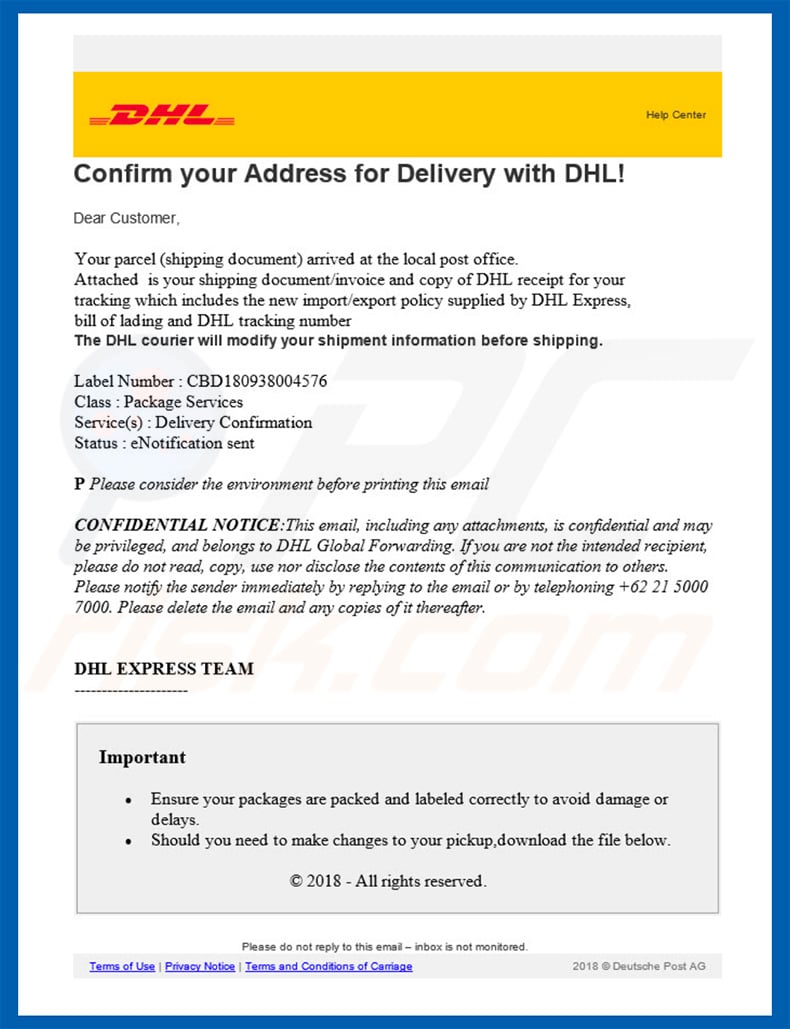
Research shows that many cyber criminals proliferate these infections using spam email campaigns. Some examples include "DHL Email Virus" and "Arrival Notice Email Virus".
More about Remcos
As mentioned above, Remcos is a high-end remote access tool that allows users to control systems remotely. If misused, however, Remcos can be an extremely dangerous threat. Research shows that cyber criminals send thousands of misleading emails that contain malicious attachments (typically MS Office documents) that infiltrate Remcos into the system.
All this is done without users' consent. Remcos grants access to computers and, thus cyber criminals can cause damage to systems and many other issues. They might retrieve personal information, such as saved passwords, private data, and so on. Cyber criminals can also monitor the screen in real-time, thus seeing what users are doing on their systems and on the internet.
The tool can also be used to download files. Therefore, cyber criminals might inject system with other viruses (e.g., ransomware). Ultimately, the presence of Remcos RAT can lead to significant financial/data issues, various privacy issues, and further system infections.
If you have recently opened malicious attachments and suspect that Remcos has infiltrated your system, scan the system with a reputable anti-virus/anti-spyware suite and eliminate all detected threats.
| Name | Remcos malware |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Detection Names | Avast (FileRepMalware), BitDefender (Trojan.GenericKD.5537999), ESET-NOD32 (A Variant Of Win32/Agent.SBY), Kaspersky (Trojan.Win32.Scar.pxmq), Full List (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Malware in general
There are dozens of various viruses distributed using spam campaigns. The list of examples includes (but is not limited to) Adwind, Hancitor, TrickBot, NanoCore, and Hawkeye.
These viruses are developed by different cyber criminals and their behavior/functionality also differs correspondingly - some gather information, others cause chain infections (infiltrate other malware into the system), provide access to the system, etc. Nevertheless, all pose a direct threat to your privacy and/or computer safety. Therefore, eliminate all malware immediately.
How did Remcos infiltrate my computer?
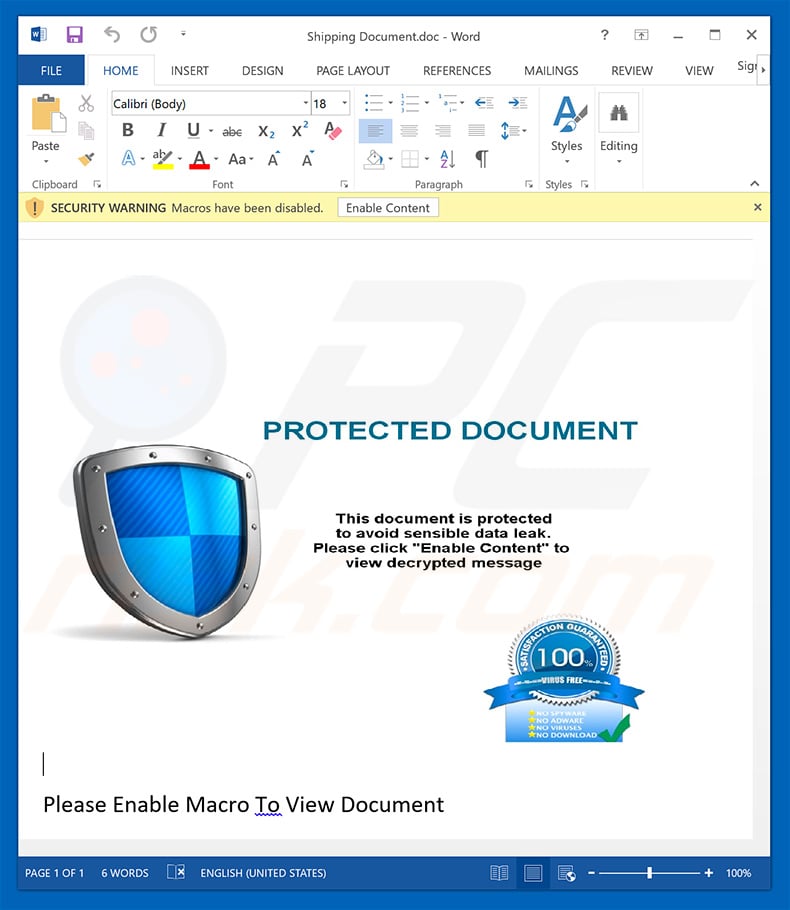
As mentioned above, Remcos is typically proliferated using spam campaigns. Users receive deceptive emails that contain malicious MS Office attachments. The messages typically states that the user has received a package, has a bill to pay, or similar. In any case, users are encouraged to open the attachment immediately.
Once opened, the file encourages users to enable macro commands, otherwise the content will not be displayed properly. By enabling macros, users grant files permission to execute commands that infiltrate viruses into the system. This malware distribution method is simple and effective, but does have flaws.
The malware will only be downloaded if the user opens attachments using MS Office. If the file is opened using any other software, the virus will not be able to infiltrate the system. Furthermore, Remcos works only on the Windows Operating System and users of other platforms are safe.
How to avoid installation of malware?
To prevent this situation, be very cautious when browsing the internet. Think twice before opening email attachments. If the file/link is irrelevant or has been received from a suspicious/unrecognizable sender, do not open it. You should delete these emails without reading. As mentioned above, many malicious attachments are MS Office documents.
Newer versions of Microsoft Office (2010 and later) have "Protected View" mode, which prevents malicious executables from automatically executing macros. Therefore, we advise to avoid using older versions of this software. Have a reputable anti-virus/anti-spyware suite installed and running.
These tools commonly detect and eliminate malware before any damage is done. The main reasons for computer infections are poor knowledge and careless behavior - the key to safety is caution. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Malicious attachment distributing Remcos:
Screenshot of a website used to sell Remcos RAT:
Update September 23, 2019 - Another email spam campaign (crooks pretend to be employees of a completely innocent company - IOUU) used to spread Remcos RAT. The malicious attachment is "Invoice.dmg" file (VirusTotal detection list), which contains "Invoice.exe" executable (VirusTotal detection list).
The latter has an icon of a PDF file and thus users are very likely to get tricked into opening, especially when their Windows settings are assigned to hide true file extensions. In other words, file named "Invoice" alongside with a PDF icon looks completely harmless, since the actual .exe extension cannot be seen:
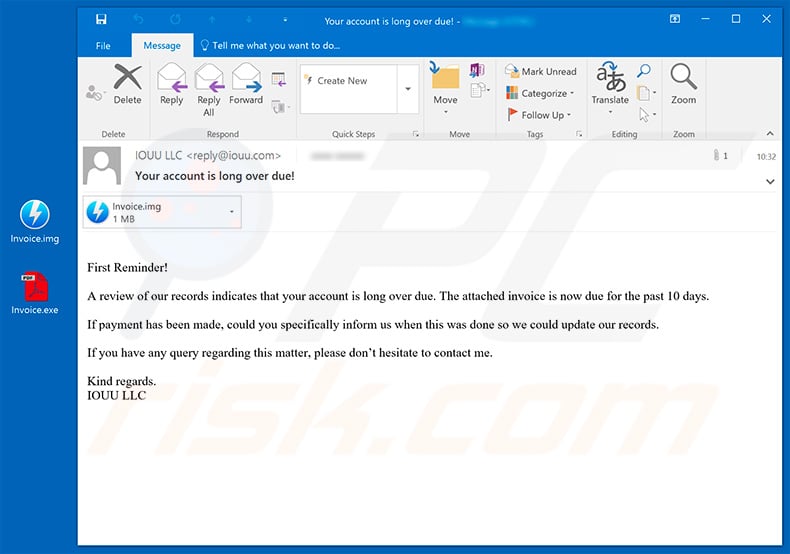
Text presented within this email:
Subject: Your account is long over due!
Attachment: Invoice.dmg
First Reminder!
A review of our records indicates that your account is long over due. The attached invoice is now due for the past 10 days.
If payment has been made, could you specifically inform us when this was done so we could update our records.
If you have any query regarding this matter, please don’t hesitate to contact me.
Kind regards.
IOUU LLC
Update May 5, 2020 - Due to the recent outbreak of Coronavirus (COVID-19) cyber criminals have started hundreds of email spam campaigns for phishing and malware distribution purposes. Remcos RAT is not an exception - there are plenty of deceptive emails encouraging users to open attached files which results in infiltration of Remcos.
One of the most recent spam campaigns is targeting small businesses in US, thus "U.S. Small Business Administration" spam campaign. You can find more examples of Coronavirus-related spam emails in this article.
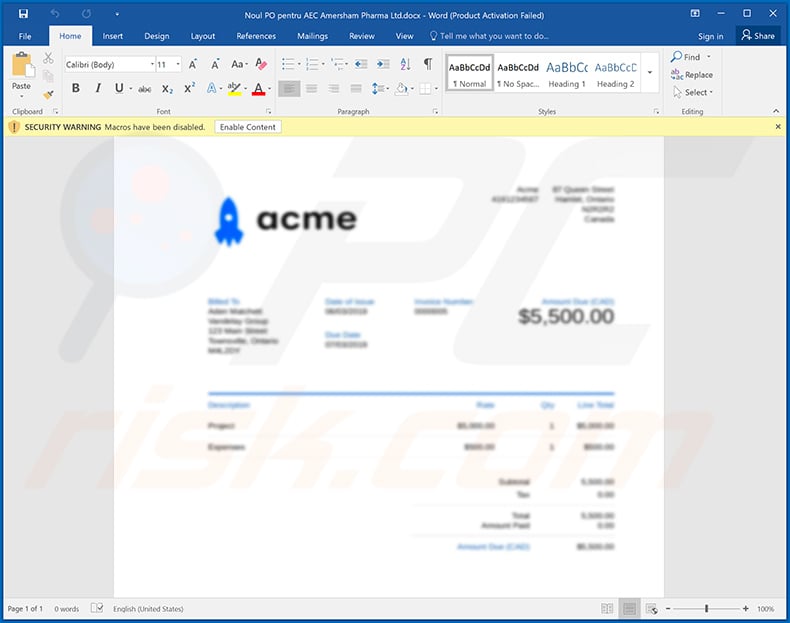
Screenshot of yet another malicious Microsoft Word document ("Noul PO pentru AEC Amersham Pharma Ltd.docx") designed to inject Remcos RAT into the system:
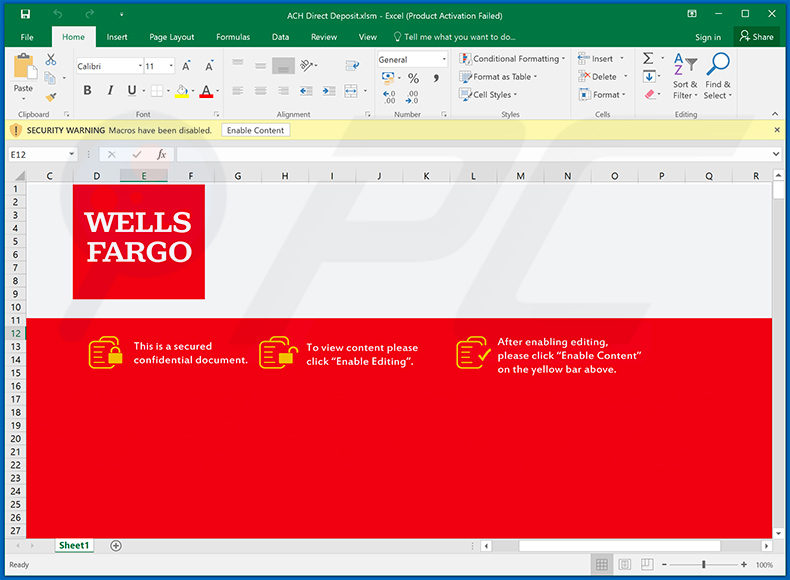
Example of a WELLS FARGO-themed malicious MS Excel document used to inject Remcos RAT into the system:
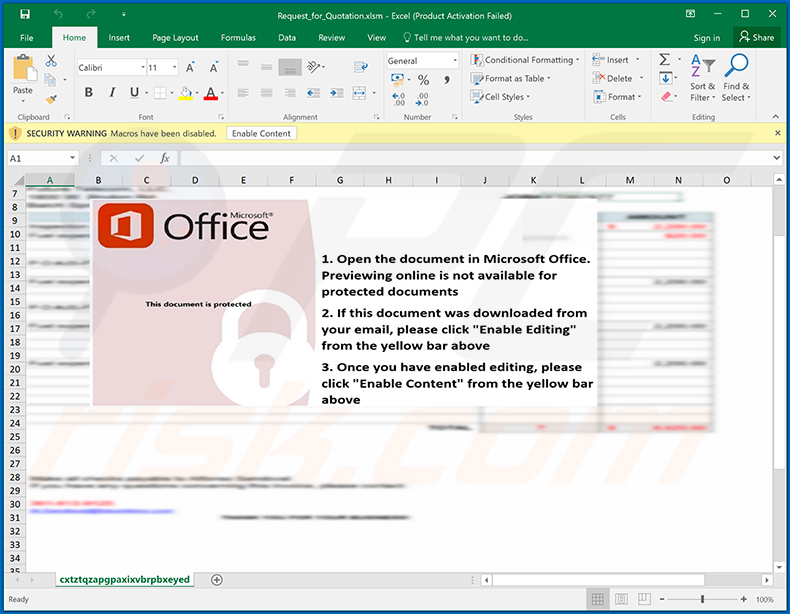
Screenshot of yet another MS Excel document used to spread Remcos RAT:
Example of a DHL-themed spam email used to spread Remcos RAT via attached .IMG file:
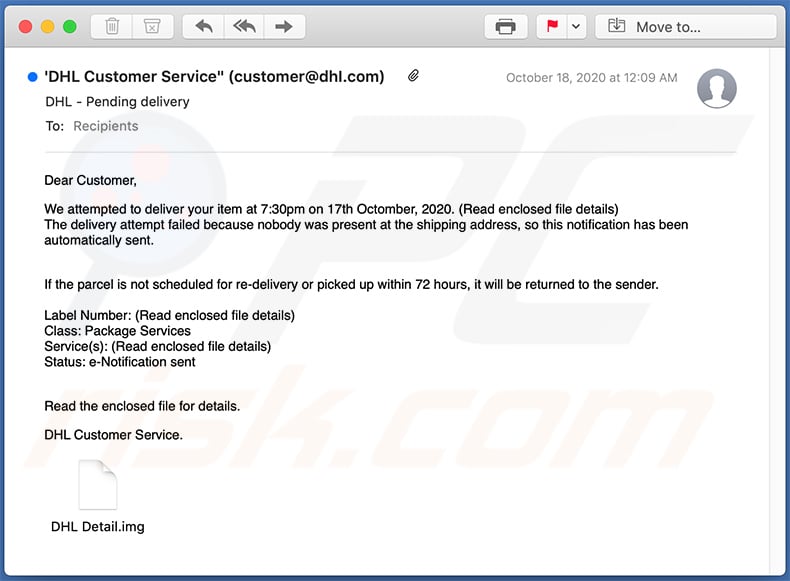
Text presented within:
Subject: DHL - Pending delivery
Dear Customer,
We attempted to deliver your item at 7:30pm on 17th Octomber, 2020. (Read enclosed file details)
The delivery attempt failed because nobody was present at the shipping address, so this notification has been automatically sent.
If the parcel is not scheduled for re-delivery or picked up within 72 hours, it will be returned to the sender.Label Number: (Read enclosed file details)
Class: Package Services
Service(s): (Read enclosed file details)
Status: e-Notification sent
Read the enclosed file for details.DHL Customer Service.
Yet another example of a spam email used to spread Remcos RAT:
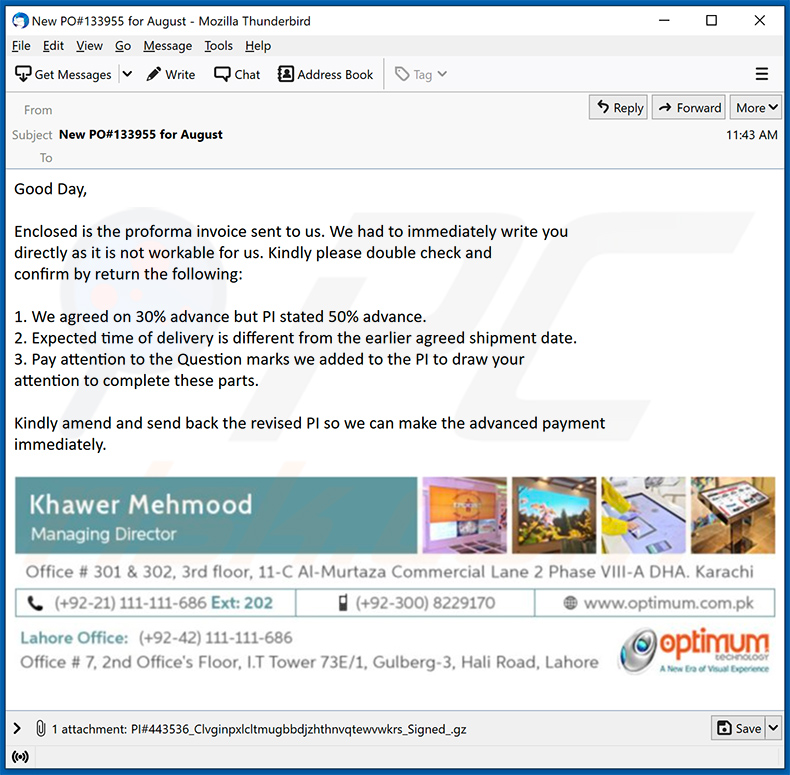
Text presented within:
Subject: New PO#133955 for August
Good Day,
Enclosed is the proforma invoice sent to us. We had to immediately write you
directly as it is not workable for us. Kindly please double check and
confirm by return the following:1. We agreed on 30% advance but PI stated 50% advance.
2. Expected time of delivery is different from the earlier agreed shipment date.
3. Pay attention to the Question marks we added to the PI to draw your
attention to complete these parts.Kindly amend and send back the revised PI so we can make the advanced payment
immediately.Khawer Mehmood
Managing Director
Office # 301 & 302, 3rd floor, 11-C Al-Murtaza Commercial Lane 2 Phase VIII-A DHA. Karachi
(+92-21) 111-111-686 Ext: 202 (+92-300) 8229180 www.optimum.com.pk
Lahore Office: (+92-21) 111-111-686
Office # 7, 2nd Office's Floor, I.T Tower 73E/1, Gulberg-3, Hali Road, Lahore
An example of DHL-themed spam email used to spread Remcos RAT:
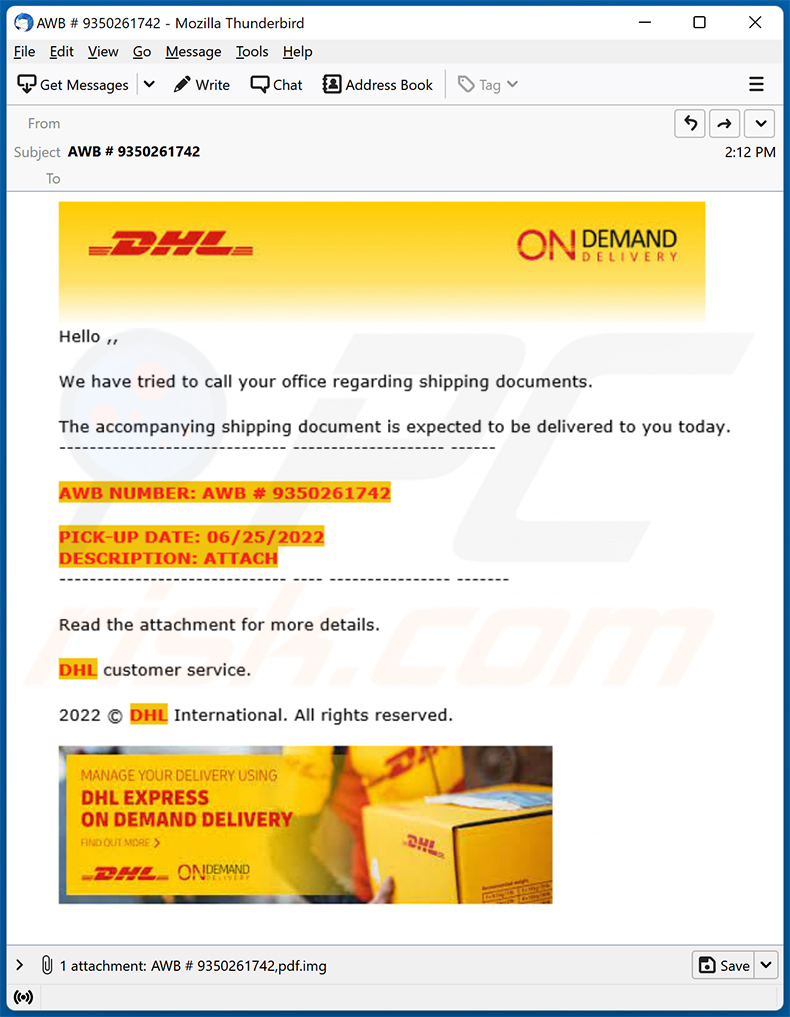
Text presented within:
Subject: AWB # 9350261742
DHL ON DEMAND DELIVERY
Hello ,,
We have tried to call your office regarding shipping documents.
The accompanying shipping document is expected to be delivered to you today.
----
AWB NUMBER: AWB # 9350261742
PICK-UP DATE: 06/25/2022
DESCRIPTION: ATTACH----
Read the attachment for more details.
DHL customer service.
2022 © DHL International. All rights reserved.
MANAGE YOUR DELIVERY USING
DHL EXPRESS
ON DEMAND DELIVERY
Update February 28, 2023 - Cybercriminals are utilizing a new version of Remcos RAT which employs a distinct approach for process hollowing in order to bypass antivirus detection. Furthermore, when developing a Remcos agent, a threat actor can enable a privilege escalation feature.
Remcos also utilizes the Dynamic Imports technique which is commonly employed by numerous malware samples to avoid detection by static analysis-based tools. Additionally, Remcos alters the data execution prevention (DEP) emulation settings.
Update February 19, 2024 - Cybercriminals are now employing a novel tactic to transfer malicious data while evading detection. This method involves leveraging "pipes" within the Windows operating system. By doing so, hackers can establish hidden communication channels, allowing them to bypass antivirus systems effectively.
In recent attacks, Ukrainian government agencies fell victim to this scheme, with cybercriminals utilizing the Remcos malware disguised as emails from trusted sources like the country's security service and telecom provider.
Update November 18, 2024 – a new variant of Remcos RAT has been discovered proliferated via an email spam campaign. These emails included malicious Microsoft Excel attachments that facilitate the infiltration of Remcos into systems via a Remote Code Execution vulnerability tracked as "CVE-2017-0199".
This RAT version boasts improved anti-detection and anti-analysis capabilities, as well as utilizes a refined persistence-ensuring mechanism. More information on these developments can be found in an article by Xiaopeng Zhang on Fortinet.
Update April 8, 2026 - A new Remcos RAT campaign has been observed spreading through phishing emails. The attack starts with a phishing email that is designed to look like a legitimate business message. The email contains a ZIP attachment that contains a disguised JavaScript file.
When a user opens it, the script runs and begins the infection process without obvious signs. The JavaScript then uses built-in Windows features to download a malicious PowerShell script from a remote server. This script is executed with security restrictions bypassed, allowing it to run even when normal protections would block it.
Instead of writing files to the hard drive where antivirus tools could inspect them, the malware runs in memory. This approach hides visible traces on disk and makes detection more difficult. It then loads a hidden .NET component using a technique called reflection, which allows it to execute additional code without clearly dropping new files onto the system.
The malware also abuses legitimate Windows tools to make its activity merge with normal system behavior. It communicates with a command-and-control server controlled by the attacker, allowing the attacker to send remote instructions to the infected device. Eventually, the full Remcos RAT payload is delivered.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Remcos, should I format my storage device to get rid of it?
No, you can remove Remcos from your computer without formatting the storage device.
What are the biggest issues that malware can cause?
Malware can steal sensitive information, slow down a computer, restrict access to files, disrupt daily operations, and cause other damage. Usually, cybercriminals use it to encrypt files, steal identities, personal accounts, money, etc.
What is the purpose of Remcos RAT?
Remcos is a legitimate remote access tool (RAT) allowing users to control computers remotely. Cybercriminals can misuse it to infect computers with other malware (e.g., ransomware), steal sensitive information (e.g., passwords, credit card details), and other purposes.
How did a Remcos infiltrate my computer?
It is known that threat actors distribute Remcos by sending emails containing attachments. Their goal is to trick recipients into opening files designed to install Remcos on computers. Cybercriminals also use cracked software distribution pages and other unreliable sources for downloading software, fake installers/updaters, and similar methods to trick users into executing malware or other software.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner will scan your computer and remove detected malware (it can detect almost all known malware). It can remove legitimate software too. Computers infected with high-end malware must be scanned using a full scan option. Malware of this kind hides deep in the system. Thus, running a quick scan to detect such malware is usually not enough.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion