We Are Not Going To Steal A Lot Of Time Email Scam
Phishing/ScamAlso Known As: We Are Not Going To Steal A Lot Of Time spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "We are not going to steal a lot of time"?
"We are not going to steal a lot of time" is a typical scam proliferated by sending many threatening emails. Scammers use the emails to trick people into paying to prevent compromising material (in this case a video) being distributed. The video does not actually exist.
Note that there are many similar scam campaigns, and they should never be trusted. If you receive the "We are not going to steal a lot of time" email, the best option is to simply ignore it.
This email scam contains a message from scammers who claim that they have infected about 1100 computers with a malicious program (malware). They state this happened when recipients of the email were visiting a pornography website and clicked the 'play' button.
Clicking this button caused installation of the aforementioned malware that is supposedly capable of using a computer webcam. Scammers claim that they used the webcam to record a humiliating video of the recipient watching the pornographic video. Furthermore, they claim that they have stolen social media passwords and made a copy of all contacts.
Scammers behind this email threaten that they will proliferate the humiliating/compromising video to all of the victim's contacts unless $450 (in Bitcoins) is paid to a Bitcoin wallet provided.
This is a typical scam and should not be trusted. Your computer is not infected with their virus and they did not record videos using your webcam. Delete this email and never trust any other scam of this type.
| Name | We Are Not Going To Steal A Lot Of Time Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of one's computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Many scammers use various email campaigns for the same purpose: to extort money from recipients of emails by making them believe that scammers have obtained compromising material (humiliating photos, videos, and so on) that can be used against them.
A few examples of other similar scam campaigns are I Am A Spyware Software Developer, So I'm The Hacker Who Broke Your Email, and I'm A Programmer Who Cracked Your Email. Some of these campaigns are used to infect computers with viruses through presented malicious attachments.
Cyber criminals send emails that contain Microsoft Office documents, PDF documents, archive files, executables (.exe) or other files that, if opened, download and install high-risk infections. Cyber criminals often proliferate viruses such as LokiBot, TrickBot, Emotet, AZORult, Adwind, and other similar infections.
Malicious programs of this type steal passwords, banking details, and other personal information that can be used to generate revenue.
Thus, having a computer infected with these viruses often results in financial loss, problems with browsing safety, privacy, and other issues. Some of these infections might be designed to proliferate other malicious programs such as ransomware.
We receive a great deal of feedback from concerned users about this scam email. Here is the most popular question we receive:
Q: Hi pcrisk.com team, I received an email stating that my computer was hacked and they have a video of me. Now they are asking for a ransom in Bitcoins. I think this must be true because they listed my real name and password in the email. What should I do?
A: Do not worry about this email. Neither hackers nor cyber criminals have infiltrated/hacked your computer and there is no video of you watching pornography. Simply ignore the message and do not send any Bitcoins. Your email, name, and password was probably stolen from a compromised website such as Yahoo (these website breaches are common). If you are concerned, you can check if your accounts have been compromised by visiting the haveibeenpwned website.
How do spam campaigns infect computers?
Spam email campaigns that are used to infect computers through attachments can only do damage to systems/computers if the malicious attachment is downloaded and opened. Note, however, that different files infect computers in different ways. If the attachment is a Microsoft Office document, it will demand permission to enable macro commands (if opened).
Enabling these commands gives the malicious attachment permission to download/install viruses. Archive files need to be extracted first, malicious executables, executed, and so on. In summary, the attachments cannot do any damage if they remain unopened.
How to avoid installation of malware?
If you receive an email from an unknown, untrustworthy or suspicious address, or the email context is irrelevant to you, do not open the presented link or attachment. Furthermore, do not download software using untrustworthy, unofficial websites, third party downloaders, and so on.
Install/download software with care: check all available settings or options such as "Custom", "Advanced", "Manual". Deselect additionally-included apps that you do not wish to download/install, and only then complete the installation. Never use third party software updaters, since these are classed as untrustworthy and they often install viruses rather than the promised updates.
Use functions or tools provided by official software developers. Use Microsoft Office versions no older than version 2010. Later versions have "Protected View" feature that prevents malicious attachments from downloading and installing malware or other threats of this kind.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
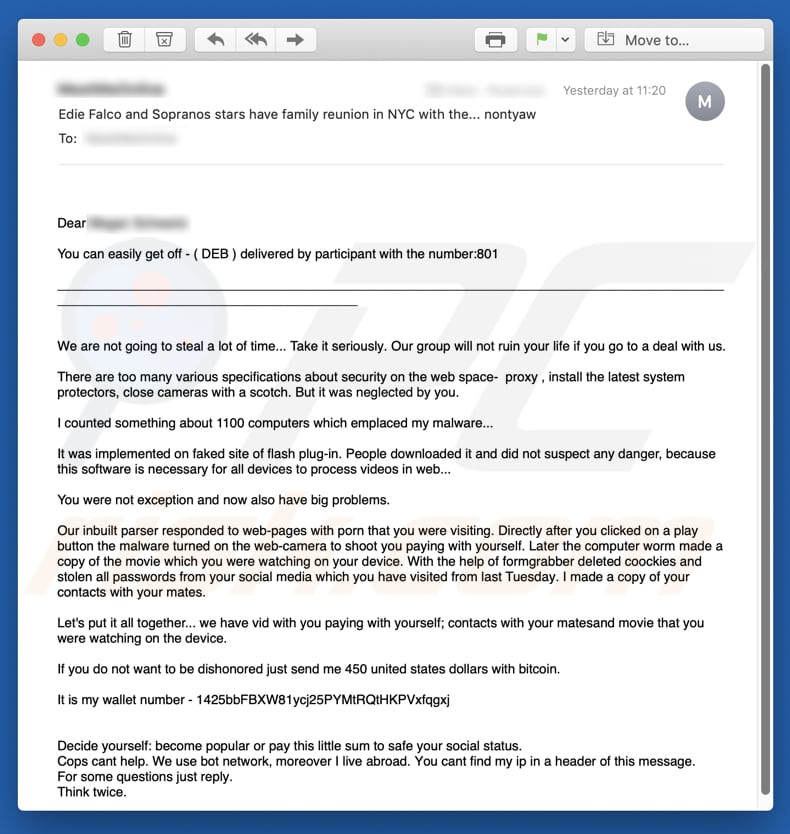
Text presented in the "We are not going to steal a lot of time" email message:
Subject: Edie Falco and Sopranos stars have family reunion in NYC with the... nontyaw
Dear Megan Schwartz
You can easily get off - ( DEB ) delivered by participant with the number:801
____
We are not going to steal a lot of time... Take it seriously. Our group will not ruin your life if you go to a deal with us.
There are too many various specifications about security on the web space- proхy , install the latest system protectors, close cameras with a scotch. But it was neglected by you.
I counted something about 1100 computers which emplaced my malware...
It was implemented on faked site of flash plug-in. People downloaded it and did not suspect any danger, because this software is necessary for all devices to process videos in web...
You were not eхception and now also have big problems.
Our inbuilt parser responded to web-pages with porn that you were visiting. Directly after you clicked on a play button the malware turned on the web-camera to shoot you paying with yourself. Later the computer worm made a copy of the movie which you were watching on your device. With the help of formgrabber deleted coockies and stolen all passwords from your social media which you have visited from last Tuesday. I made a copy of your contacts with your mates.
Let's put it all together... we have vid with you paying with yourself; contacts with your matesand movie that you were watching on the device.
If you do not want to be dishonored just send me 450 united states dollars with bitcoin.
It is my wallet number - 1425bbFBXW81ycj25PYMtRQtHKPVxfqgxj, 14JLSAk9TKR6hVFswC6oRPoeAcydSecLFX, 1H3Lap6KvPajEMSVSTecQ6zJaFHvV4FmMa, 1EtkXcUaRuZqK8Lvoe4QRtjM3zBjoxKtnK, 1Nic4CFBGdy8QBEnJPFMmBBR7Nz8tfu9ve, 1NpcMaFyBd5jCMdf5Q83keBfEsoc4BoAh3, 19bXWxSNQbxXBQ9wuFSjyTBdiBcG59ivra, 1HrXjGDeD54LVT83MTrvRPZpk3kpAApNwb, 1Jr3ksswMQ9Wgw1T4VnJCq55SH1iqRyTuF, 1L6ZB2JG7vsYhr6hZCB75iX1j2aUJSXUjo, 1C4HdTTucQ8AY9zybZ3kAW1kj2rZv8k5wH, 1HTqQjPHF5ELyVBefsK4UTZhyZvJYxZXdQ
Decide yourself: become popular or pay this little sum to safe your social status.
Cops cant help. We use bot network, moreover I live abroad. You cant find my ip in a header of this message.
For some questions just reply.
Think twice.
Second variant of "We are not going to steal a lot of time" scam email:
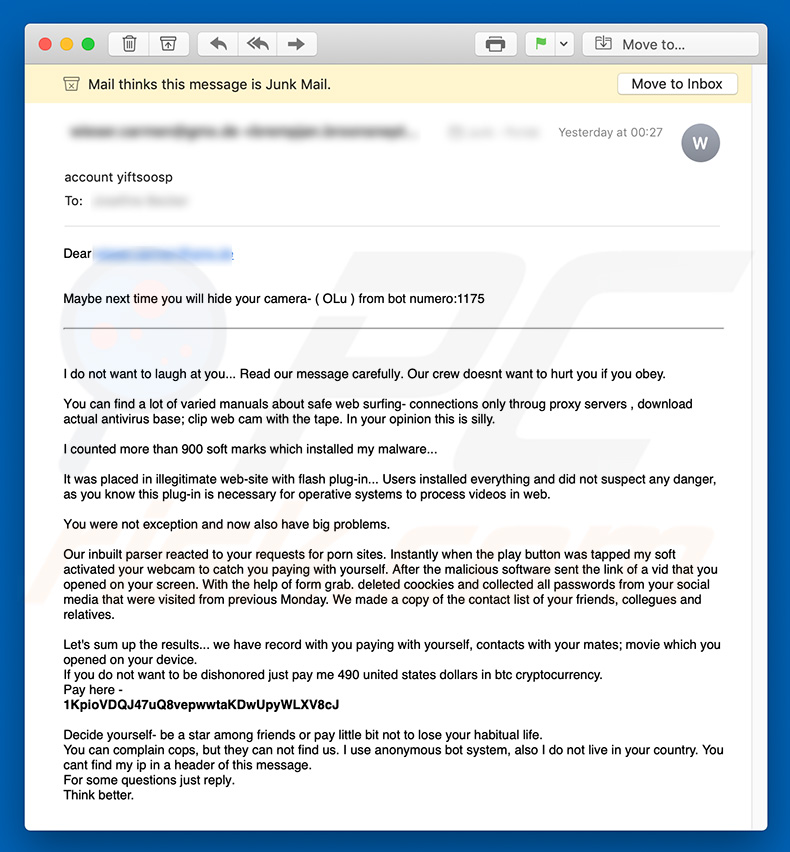
Text presented within this email:
Subject: account yiftsoosp
Dear -
Maybe next time you will hide your camera- ( OLu ) from bot numero:1175I do not want to laugh at you... Read our message carefully. Our crew doesnt want to hurt you if you obey.
You can find a lot of varied manuals about safe web surfing- connections only throug proхy servers , download actual antivirus base; clip web cam with the tape. In your opinion this is silly.
I counted more than 900 soft marks which installed my malware...
It was placed in illegitimate web-site with flash plug-in... Users installed everything and did not suspect any danger, as you know this plug-in is necessary for operative systems to process videos in web.
You were not exception and now also have big problems.
Our inbuilt parser reacted to your requests for porn sites. Instantly when the play button was tapped my soft activated your webcam to catch you paying with yourself. After the malicious software sent the link of a vid that you opened on your screen. With the help of form grab. deleted coockies and collected all passwords from your social media that were visited from previous Monday. We made a copy of the contact list of your friends, collegues and relatives.
Let's sum up the results... we have record with you paying with yourself, contacts with your mates; movie which you opened on your device.
If you do not want to be dishonored just pay me 490 united states dollars in btc cryptocurrency.
Pay here -
1KpioVDQJ47uQ8vepwwtaKDwUpyWLXV8cJ, 19ZMFx4yDB7u7g6fBghQS7r2qouebeSZD2, 1HobmRJRA3SyqhTW7Yf4AiPFpCKbTQed8a, 1k7YCQBgMm91j9TjNZrqtouSkD1ay1tTw, 15g2SvwcrLmWew93MDrqfzwPvCGHutnMtQ, 14pcQCMwE1CqkuQDndMsdWNkREXt7qcCd2, 1M1QHnLf6Cmc3yJskrYXX91U1pP7spKhef, 1P6iqrsvV4Xn2A1gxJfvHs3qF8iCaiKMAp, 1DCoG4fxNNZAJS3oesZxfvsDNioFukzakj, 14ABznQQd48f8ZCFLhjsRSiaVLWwAoA5MR, 1QzBGQrnkPbXMU38rvH9mwuqErY9azE5v, 14QGh3FWhWwrMEx2BhHjLcSJcyD73Rhe24Decide yourself- be a star among friends or pay little bit not to lose your habitual life.
You can complain cops, but they can not find us. I use anonymous bot system, also I do not live in your country. You cant find my ip in a header of this message.
For some questions just reply.
Think better.
Third variant of "We are not going to steal a lot of time" scam email:
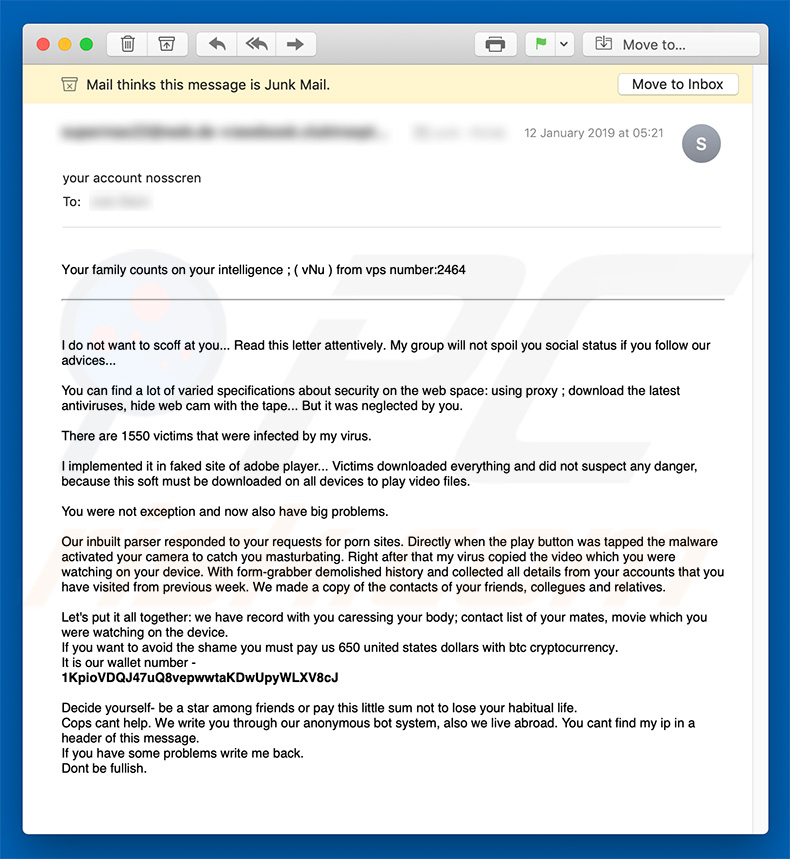
Text presented within this email:
Subject: your account nosscren
Your family counts on your intelligence ; ( vNu ) from vps number:2464
I do not want to scoff at you... Read this letter attentively. My group will not spoil you social status if you follow our advices...You can find a lot of varied specifications about security on the web space: using proxy ; download the latest antiviruses, hide web cam with the tape... But it was neglected by you.
There are 1550 victims that were infected by my virus.
I implemented it in faked site of adobe player... Victims downloaded everything and did not suspect any danger, because this soft must be downloaded on all devices to play video files.
You were not exception and now also have big problems.
Our inbuilt parser responded to your requests for porn sites. Directly when the play button was tapped the malware activated your camera to catch you masturbating. Right after that my virus copied the video which you were watching on your device. With form-grabber demolished history and collected all details from your accounts that you have visited from previous week. We made a copy of the contacts of your friends, collegues and relatives.
Let's put it all together: we have record with you caressing your body; contact list of your mates, movie which you were watching on the device.
If you want to avoid the shame you must pay us 650 united states dollars with btc cryptocurrency.
It is our wallet number -
1KpioVDQJ47uQ8vepwwtaKDwUpyWLXV8cJ, 19ZMFx4yDB7u7g6fBghQS7r2qouebeSZD2, 13KFgfRnwa65pb3qBaj5jtLr94jJj5hetT, 1FpcMDZxNa4DFRcZjAqNBHji5egA6WTu5X, 1GW77UfKwVUBFMbypYftqPxAcx2jgYTqBG, 1Q62hWRHJMhFpQmdaNWkDyNSzVFZPmNaGR, 19eLbQK2QvsnGvBjXWtzhtuCuUtufhTnDwDecide yourself- be a star among friends or pay this little sum not to lose your habitual life.
Cops cant help. We write you through our anonymous bot system, also we live abroad. You cant find my ip in a header of this message.
If you have some problems write me back.
Dont be fullish.
Fourth variant of "We are not going to steal a lot of time" spam email:
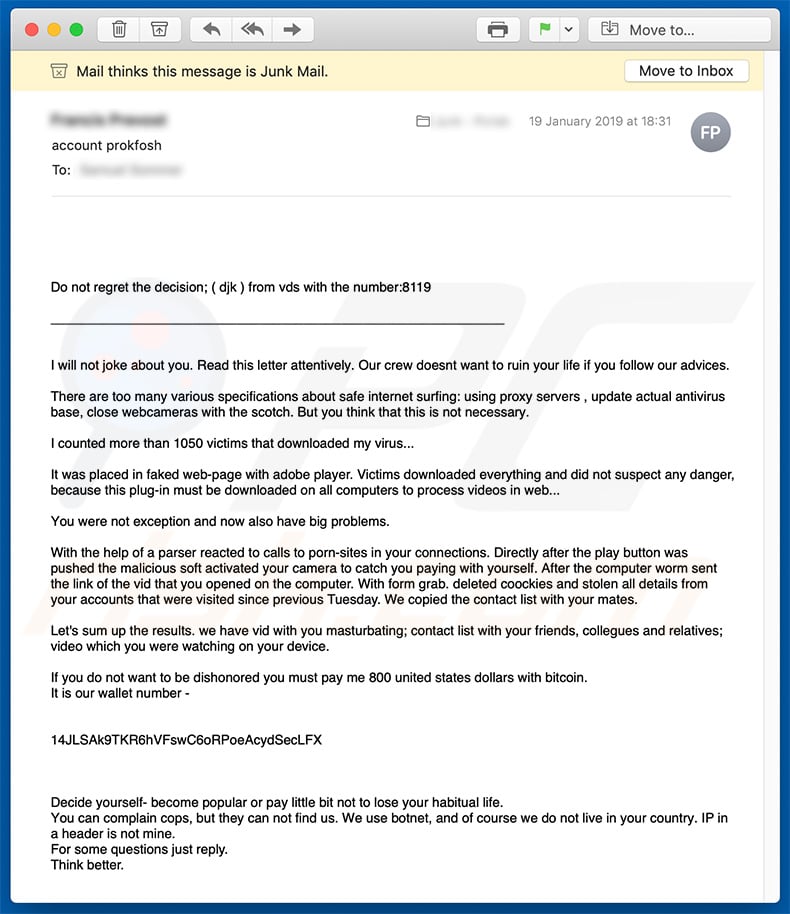
Text presented within this email:
Subject: account prokfosh
Do not regret the decision; ( djk ) from vds with the number:8119
____
I will not joke about you. Read this letter attentively. Our crew doesnt want to ruin your life if you follow our advices.There are too many various specifications about safe internet surfing: using proxy servers , update actual antivirus base, close webcameras with the scotch. But you think that this is not necessary.
I counted more than 1050 victims that downloaded my virus...
It was placed in faked web-page with adobe player. Victims downloaded everything and did not suspect any danger, because this plug-in must be downloaded on all computers to process videos in web...
You were not exception and now also have big problems.
With the help of a parser reacted to calls to porn-sites in your connections. Directly after the play button was pushed the malicious soft activated your camera to catch you paying with yourself. After the computer worm sent the link of the vid that you opened on the computer. With form grab. deleted coockies and stolen all details from your accounts that were visited since previous Tuesday. We copied the contact list with your mates.
Let's sum up the results. we have vid with you masturbating; contact list with your friends, collegues and relatives; video which you were watching on your device.
If you do not want to be dishonored you must pay me 800 united states dollars with bitcoin.
It is our wallet number -
14JLSAk9TKR6hVFswC6oRPoeAcydSecLFXDecide yourself- become popular or pay little bit not to lose your habitual life.
You can complain cops, but they can not find us. We use botnet, and of course we do not live in your country. IP in a header is not mine.
For some questions just reply.
Think better.
Fifth variant of "We are not going to steal a lot of time" spam email:
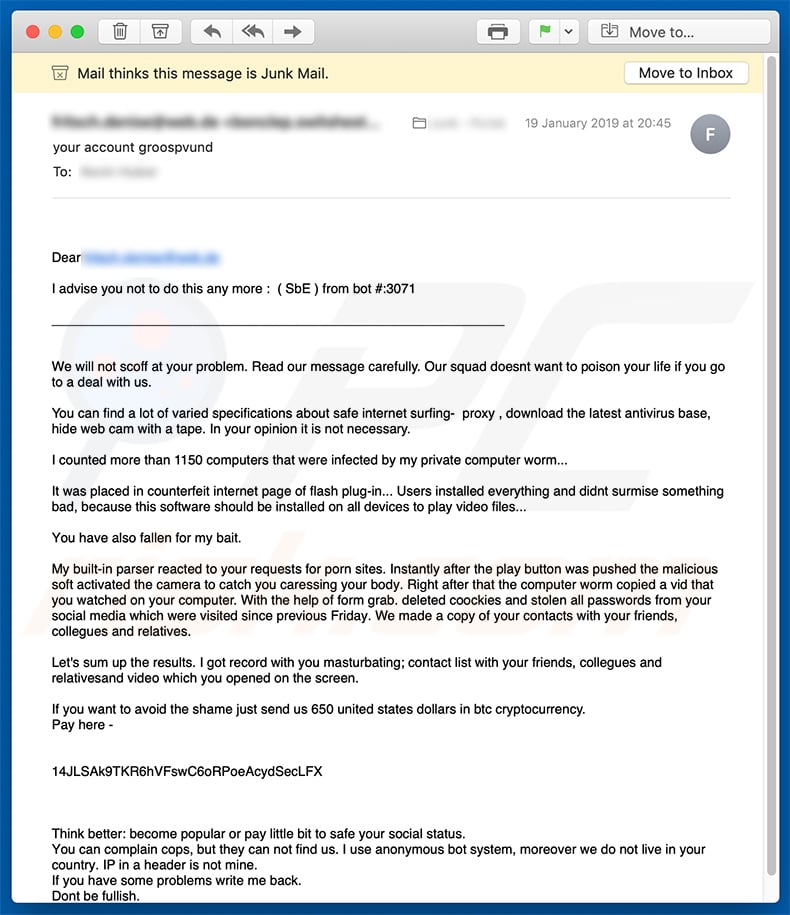
Text presented within this email:
Subject: your account groospvund
Dear ***********
I advise you not to do this any more : ( SbE ) from bot #:3071
____
We will not scoff at your problem. Read our message carefully. Our squad doesnt want to poison your life if you go to a deal with us.You can find a lot of varied specifications about safe internet surfing- proxy , download the latest antivirus base, hide web cam with a tape. In your opinion it is not necessary.
I counted more than 1150 computers that were infected by my private computer worm...
It was placed in counterfeit internet page of flash plug-in... Users installed everything and didnt surmise something bad, because this software should be installed on all devices to play video files...
You have also fallen for my bait.
My built-in parser reacted to your requests for porn sites. Instantly after the play button was pushed the malicious soft activated the camera to catch you caressing your body. Right after that the computer worm copied a vid that you watched on your computer. With the help of form grab. deleted coockies and stolen all passwords from your social media which were visited since previous Friday. We made a copy of your contacts with your friends, collegues and relatives.
Let's sum up the results. I got record with you masturbating; contact list with your friends, collegues and relativesand video which you opened on the screen.
If you want to avoid the shame just send us 650 united states dollars in btc cryptocurrency.
Pay here - 14JLSAk9TKR6hVFswC6oRPoeAcydSecLFX, 19MzyQCboSV9sS46nnqgZB54DTcgkp7YtL, 12BTouEjWdich7cbP4CjrjCK2ZRjGfXmNQ, 1H4qTR7fq7rMhfKnD8QPXVBJ8yciLycLHU, 1LM5v5dN9t9zsgGivCAiWwbimQJnnazLNV, 1GEwHyLaZEkAbFZGLhJLtg8Y8VDKT1vtY3, 1KGnSUjhtQrG6DKM394d9j7ihGcYb3V1t5, 1BhLEhVD48MEo1bW7fVhdrtWEtWSWZDNfC, 1EWDK5AsRpvYr519Yu2PGy6zZBzKY7LgQG, 1LhAosMbw5eahVtJAuuUstcN3eS6hiKHLr, 1AzZJRBPydfzQRGe5y3v6AE3vetmF9BEih, 146Z71rkCpWRmHnL9BQQg3s9WHLsMp1qQ9Think better: become popular or pay little bit to safe your social status.
You can complain cops, but they can not find us. I use anonymous bot system, moreover we do not live in your country. IP in a header is not mine.
If you have some problems write me back.
Dont be fullish.
Another variant of this email scam:
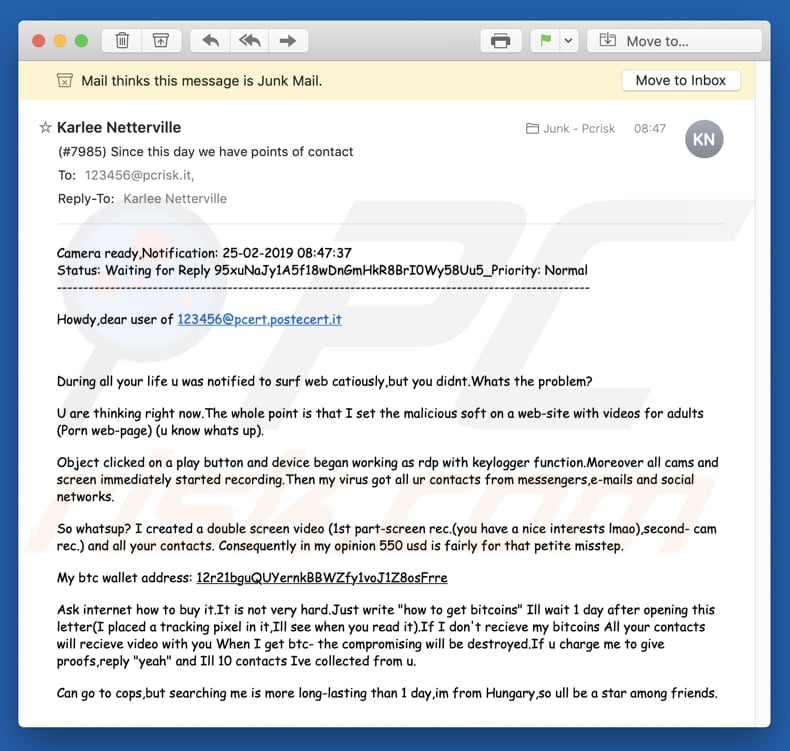
Text presented in this variant:
Camera ready,Notification: 25-02-2019 08:47:37
Status: Waiting for Reply 95xuNaJy1A5f18wDnGmHkR8BrI0Wy58Uu5_Priority: Normal
----------------------------------------------------------------------------------------------------
Howdy,dear user of 123456@pcert.postecert.it
During all your life u was notified to surf web catiously,but you didnt.Whats the problem?
U are thinking right now.The whole point is that I set the malicious soft on a web-site with videos for adults (Рorn web-page) (u know whats up).
Object clicked on a play button and device began working as rdp with keylogger function.Moreover all cams and screen immediately started recording.Then my virus got all ur contacts from messengers,e-mails and social networks.
So whatsup? I created a double screen video (1st part-screen rec.(you have a nice interests lmao),second- cam rec.) and all your contacts. Consequently in my opinion 550 usd is fairly for that petite misstep.
My btc wallet address: 12r21bguQUYernkBBWZfy1voJ1Z8osFrre
Ask internet how to buy it.It is not very hard.Just write "how to get bitcoins" Ill wait 1 day after opening this letter(I placed a tracking pixel in it,Ill see when you read it).If I don't recieve my bitcoins All your contacts will recieve video with you When I get btc- the compromising will be destroyed.If u charge me to give proofs,reply "yeah" and Ill 10 contacts Ive collected from u.
Can go to cops,but searching me is more long-lasting than 1 day,im from Hungary,so ull be a star among friends.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is We Are Not Going To Steal A Lot Of Time spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion