Do not trust "World Health Organization (WHO)" email scams
Phishing/ScamAlso Known As: World Health Organization (WHO) spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the "World Health Organization (WHO)" email?
As discovered and researched by hiro_ and BleepingComputer respectively, "World Health Organization (WHO)" are spam campaigns, distributing deceptive emails disguised as mail from officials/representatives of the World Health Organization (WHO).
There are several variants of these messages, which claim to contain important information concerning the Coronavirus/COVID-19 pandemic. The purpose of these emails is phishing and malware proliferation.
At the time of research, they have been used to spread GuLoader, HawkEye, Agent Tesla and FormBook malicious programs. The messages might also be used to proliferate other malware.
There are four variants of the "World Health Organization (WHO)" email, however, there are likely to be more versions. Therefore, the text and subject of these messages can differ or be reused for other spam campaigns. Likewise, this model can potentially be used in other phishing scams and/or to proliferate different malware.
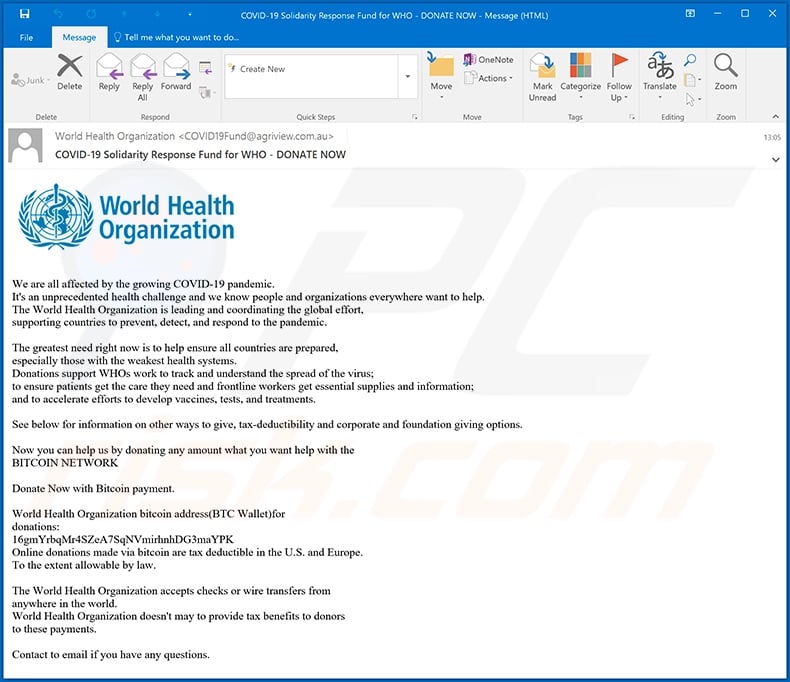
To give a short summary, the email with the subject "COVID-19 Solidarity Response Fund for WHO - DONATE NOW" asks recipients to donate to aid efforts against the coronavirus. This message provides a brief explanation of what the World Health Organization is and what measures it is taking to battle the pandemic.
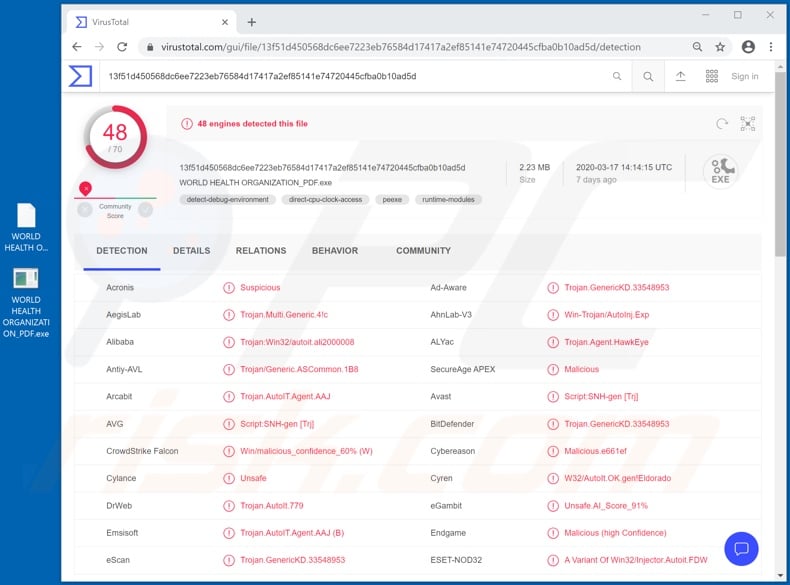
The donations are to be made in the Bitcoin cryptocurrency, which are transferred to the cryptowallets of cyber criminals. The second variant with the subject "W.H.O."CORONAVIRUS(COV,19) SAFETY&PREVENTIVE MEASURES" states that the attached file contains recommendations and everyday health and virus infection prevention steps.
Instead, the attachment is the executable file of HawkEye, which is information-stealing malware. The third variant, subject "RE: Coronavirus disease (COVID-19) outbreak prevention and cure update", claims that the attached file is a list of simple instructions and common, affordable medication to take as preventive measures against coronavirus.
This malicious file is actually used to infect systems with Agent Tesla RAT. The email with the subject "Latest on corona-virus" states that the archived file within it contains an e-book called "My-health".
The supposed electronic book contains important information concerning COVID-19 such as the origins and research of the virus, transmission scenarios, protection and prevention guidelines, as well as adaptation instructions and emergency plans for national and local authorities.
Rather than containing the promised information, however, it contains GuLoader downloader malware, which can download/install additional malicious programs.
At the time of research, it was used infect systems with the FormBook information stealer. Note that all of these emails are bogus and their claims are false. Therefore, never trust these "World Health Organization (WHO)" messages or other, similar emails.
| Name | World Health Organization (WHO) spam |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
| Hoax | The emails are disguised as mail from the World Health Organization (WHO), concerning important information about the Coronavirus/COVID-19. |
| Detection Names (second variant attachment) |
Avast (Script:SNH-gen [Trj]), BitDefender (Trojan.GenericKD.33548953), ESET-NOD32 (A Variant Of Win32/Injector.Autoit.FDW), Kaspersky (Trojan-Spy.MSIL.Heye.ln), Full List Of Detections (VirusTotal) |
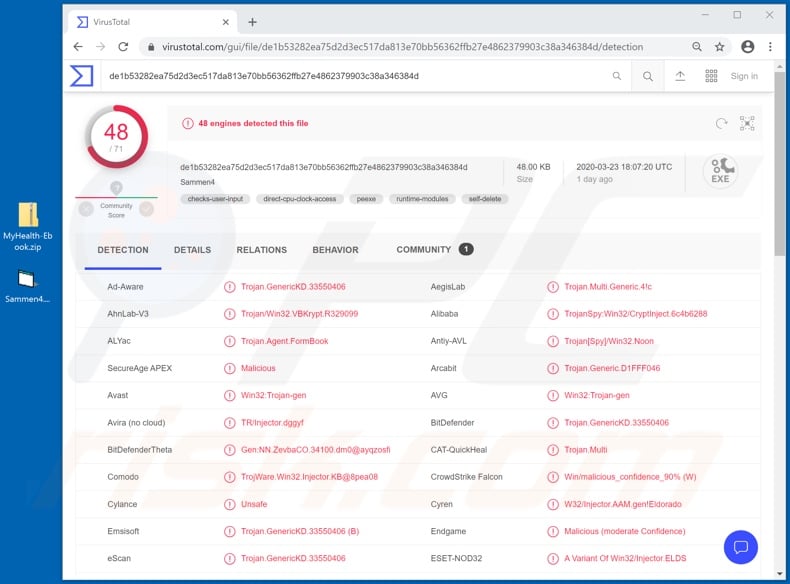
| Detection Names (fourth variant attachment) |
Avast (Win32:Trojan-gen), BitDefender (Trojan.GenericKD.33550406), ESET-NOD32 (A Variant Of Win32/Injector.ELDS), Kaspersky ( Trojan-Spy.Win32.Noon.awjt), Full List Of Detections (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Payload | HawkEye, Agent Tesla, GuLoader, FormBook and possibly other malicious programs. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Deceptive/Scam emails are sent by the thousand, during operations termed "spam campaigns". This mail is usually disguised as "official", "important", "urgent", "priority", or otherwise exploits the current social climate/pandemic. With rising public concern over the Coronavirus/COVID-19 pandemic, cyber criminals have taken to incorporating it into their schemes.
The "World Health Organization (WHO)" emails are just one example of this. "COVID-19 Solution Announced by WHO", "Coronavirus Face Mask", and "COVID-19 Insurance Plan From CIGNA" are examples of others, amongst dozens. All deceptive/scam emails are designed to generate revenue for the scammers (cyber criminals) behind them.
How did "World Health Organization (WHO) Email Virus" infect my computer?
Systems are infected via malicious files in deceptive emails. This content can be attached to the messages or linked within them (i.e., download links). Infectious files can be in various formats such as Microsoft Office and PDF documents, archive (ZIP, RAR, etc.) and executable (.exe, .run, etc.) files, JavaScript, etc.
When these files are opened (executed, run, etc.), the infection starts (download/installation of malware). For example, Microsoft Office documents infect systems by executing malicious macro commands.
When opened, the documents ask users to enable macro commands (i.e., to enable editing), after which the infection begins, however, in MS Office programs releases prior to 2010, this process is started immediately the infectious document is opened (without permission being requested).
How to avoid installation of malware
Do not open suspicious or irrelevant emails, especially those received from suspect/unknown senders. Any attachments or links found in such mail must never be opened, as this can result in high-risk infection.
Additionally, you are advised to use Microsoft Office versions released after 2010, since newer releases have "Protected View" mode, which prevents macro commands from being executed when the document is opened.
As well as spam campaigns, malware is also commonly proliferated through untrusted download channels (e.g. unofficial and free file-hosting websites, Peer-to-Peer sharing networks and other third party downloaders), and via illegal activation ("cracking") tools and fake updates.
Therefore, download products from official and verified sources. Furthermore, all software should be activated and updated only with tools/functions provided by legitimate developers. To ensure device integrity and user safety, have a reputable anti-virus/anti-spyware suite installed.
These programs must be kept up to date, used to perform regular system scans and for the removal of detected threats/issues. If you have already opened a "World Health Organization (WHO) Email Virus" attachment, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the first variant of the "World Health Organization (WHO)" email message:
Subject: COVID-19 Solidarity Response Fund for WHO - DONATE NOW
World Health Organization
We are all affected by the growing COVID-19 pandemic.
It's an unprecedented health challenge and we know people and organizations everywhere want to help.
The World Health Organization is leading and coordinating the global effort,
supporting countries to prevent, detect, and respond to the pandemic.The greatest need right now is to help ensure all countries are prepared,
especially those with the weakest health systems.
Donations support WHOs work to track and understand the spread of the virus;
to ensure patients get the care they need and frontline workers get essential supplies and information;
and to accelerate efforts to develop vaccines, tests, and treatments.See below for information on other ways to give, tax-deductibility and corporate and foundation giving options.
Now you can help us by donating any amount what you want help with the
BITCOIN NETWORKDonate Now with Bitcoin payment.
World Health Organization bitcoin address(BTC Wallet) for
donations:
16gmYrbqMr4SZeA7SqNVmirhnhDG3maYPK
Online donations made via bitcoin are tax deductible in the U.S. and Europe.
To the extent allowable by law.The World Health Organization accepts checks or wire transfers from
anywhere in the world.
World Health Organization doesn't may to provide tax benefits to donors
to these payments.Contact to email if you have any questions.
Screenshot of the second variant of "World Health Organization (WHO)" email used to distribute HawkEye malware:
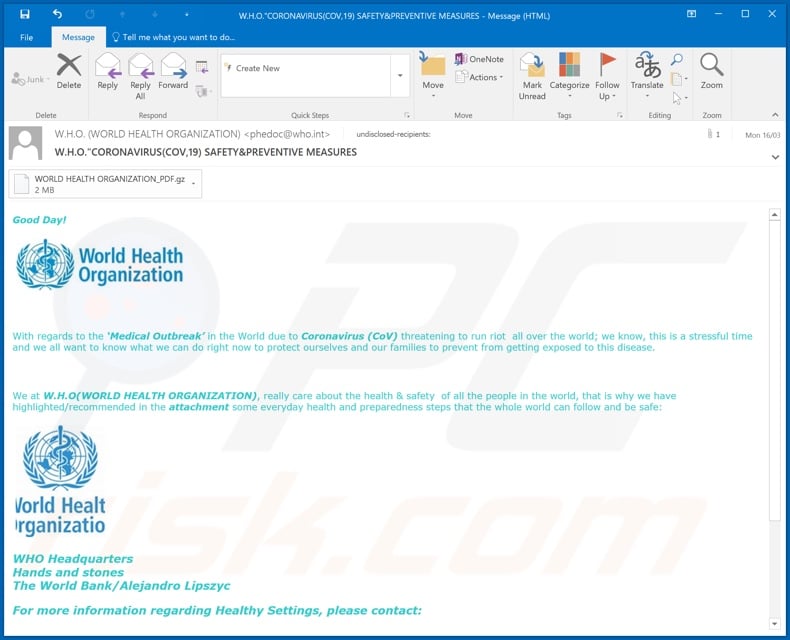
Text presented in this message:
Subject: W.H.O."CORONAVIRUS(COV,19) SAFETY&PREVENTIVE MEASURES
Good Day!
With regards to the ‘Medical Outbreak’ in the World due to Coronavirus (CoV) threatening to run riot all over the world; we know, this is a stressful time and we all want to know what we can do right now to protect ourselves and our families to prevent from getting exposed to this disease.
We at W.H.O(WORLD HEALTH ORGANIZATION), really care about the health & safety of all the people in the world, that is why we have highlighted/recommended in the attachment some everyday health and preparedness steps that the whole world can follow and be safe:
WHO Headquarters
Hands and stones
The World Bank/Alejandro LipszycFor more information regarding Healthy Settings, please contact:
Interventions for Healthy Environments Unit (IHE)
Public Health and Environment Department (PHE)
World Health Organization
20 Avenue Appia
1211 Geneva 27
Switzerland
Fax No.: +41 22 791 13 83 Attention: Healthy Settings
E-mail: phedoc@who.int
Screenshot of detections on VirusTotal of the malicious attachment distributed through this variant:
Appearance of the third variant of "World Health Organization (WHO)" email used to distribute Agent Tesla RAT (GIF):
Text presented in this message:
Subject: RE: Coronavirus disease (COVID-19) outbreak prevention and cure update.
Dear ******
Please find the attached file with the instructions on comon drugs to take for prevention and fase cure to this deadly virus called
Coronavirus Disease (COVID-19).This is an instruction from WHO (World Health Organization) to help fight agaisnt coronavirus.
NOTE : once received this mail review the attached file and follow the instructions .
please forward to your family members and friends to help us reach every one on how to fight
this virus , and the instructions are very simple and affordable.
Thanks
Best regard
Director WHO (World Health Organization)
Dr. Tedros Adhanom W.H.OVeriforce and PEC Safety have merge. Learn more.
This e-mail is confidential and is intended solely for the use of the recipient. If you are not the intended recipient, be advised that you have received this e-mail in error and that any use, dissemination, forwarding, printing, or copying of this e-mail is strictly prohibited.
Screenshot of the fourth variant of "World Health Organization (WHO)" email used to distribute GuLoader (which injects FormBook malware):
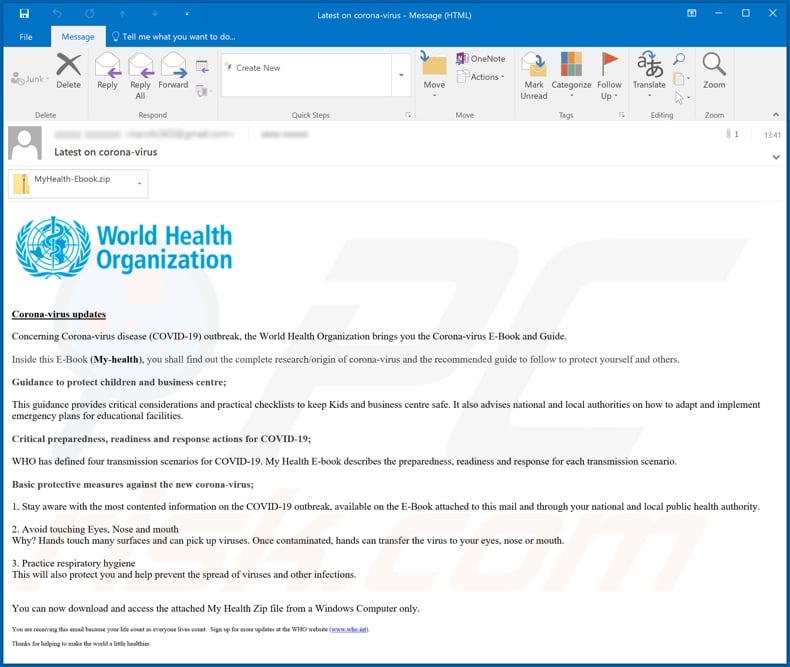
Text presented in this message:
Subject: Latest on corona-virus
Corona-virus updates
Concerning Corona-virus disease (COVID-19) outbreak, the World Health Organization brings you the Corona-virus E-Book and Guide.Inside this E-Book (My-health), you shall find out the complete research/origin of corona-virus and the recommended guide to follow to protect yourself and others.
Guidance to protect children and business centre;
This guidance provides critical considerations and practical checklists to keep Kids and business centre safe. It also advises national and local authorities on how to adapt and implement emergency plans for educational facilities.
Critical preparedness, readiness and response actions for COVID-19;
WHO has defined four transmission scenarios for COVID-19. My Health E-book describes the preparedness, readiness and response for each transmission scenario.
Basic protective measures against the new corona-virus;
1. Stay aware with the most contented information on the COVID-19 outbreak, available on the E-Book attached to this mail and through your national and local public health authority.
2. Avoid touching Eyes, Nose and mouth
Why? Hands touch many surfaces and can pick up viruses. Once contaminated, hands can transfer the virus to your eyes, nose or mouth.3. Practice respiratory hygiene
This will also protect you and help prevent the spread of viruses and other infections.You can now download and access the attached My Health Zip file from a Windows Computer only.
You are receiving this email because your life count as everyone lives count. Sign up for more updates at the WHO website (www.who[.]int).
Thanks for helping to make the world a little healthier.
Screenshot of detections on VirusTotal of the malicious attachment distributed through this variant:
Yet another variant of a coronavirus-related spam email (which is supposedly sent by the World Health Organization) designed to spread the FormBook Trojan:
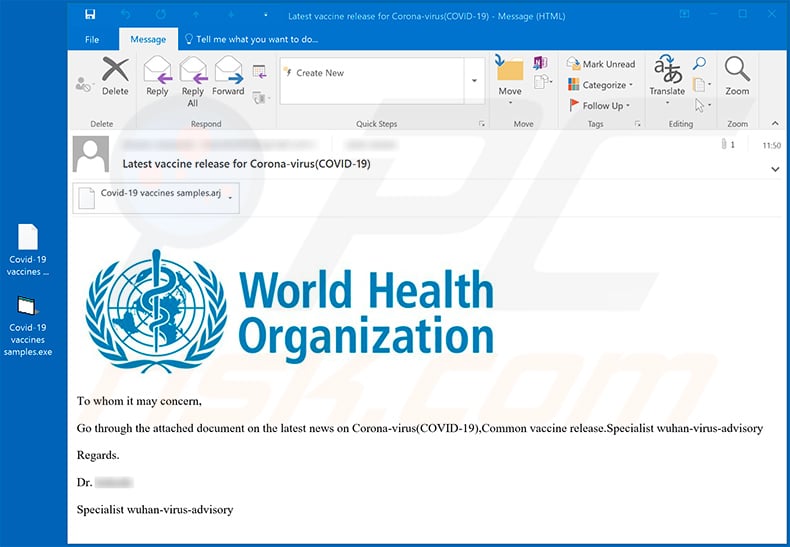
Text presented within this email:
Subject: Latest vaccine release for Corona-virus(COVID-19)
To whom it may concern,Go through the attached document on the latest news on Corona-virus(COVID-19),Common vaccine release.Specialist wuhan-virus-advisory
Regards.
Dr. -
Specialist wuhan-virus-advisory
Coronavirus-related phishing email, which claims to be from the World Health Organization (WHO) asking for monetary support in Bitcoins:
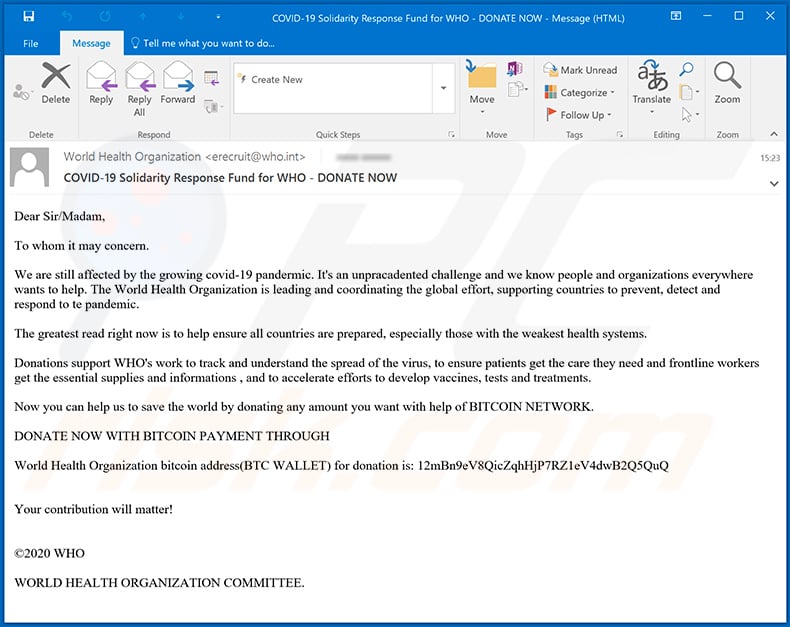
Text presented within this email:
Subject: COVID-19 Solidarity Response Fund for WHO - DONATE NOW
Dear Sir/Madam,
To whom it may concern.
We are still affected by the growing covid-19 pandermic. It's an unpracadented challenge and we know people and organizations everywhere wants to help. The World Health Organization is leading and coordinating the global effort, supporting countries to prevent, detect and respond to te pandemic.
The greatest read right now is to help ensure all countries are prepared, especially those with the weakest health systems.
Donations support WHO's work to track and understand the spread of the virus, to ensure patients get the care they need and frontline workers get the essential supplies and informations , and to accelerate efforts to develop vaccines, tests and treatments.
Now you can help us to save the world by donating any amount you want with help of BITCOIN NETWORK.
DONATE NOW WITH BITCOIN PAYMENT THROUGH
World Health Organization bitcoin address(BTC WALLET) for donation is: 12mBn9eV8QicZqhHjP7RZ1eV4dwB2Q5QuQ
Your contribution will matter!
©2020 WHOWORLD HEALTH ORGANIZATION COMMITTEE.
Another variant of "World Health Organization (WHO)" spam email:
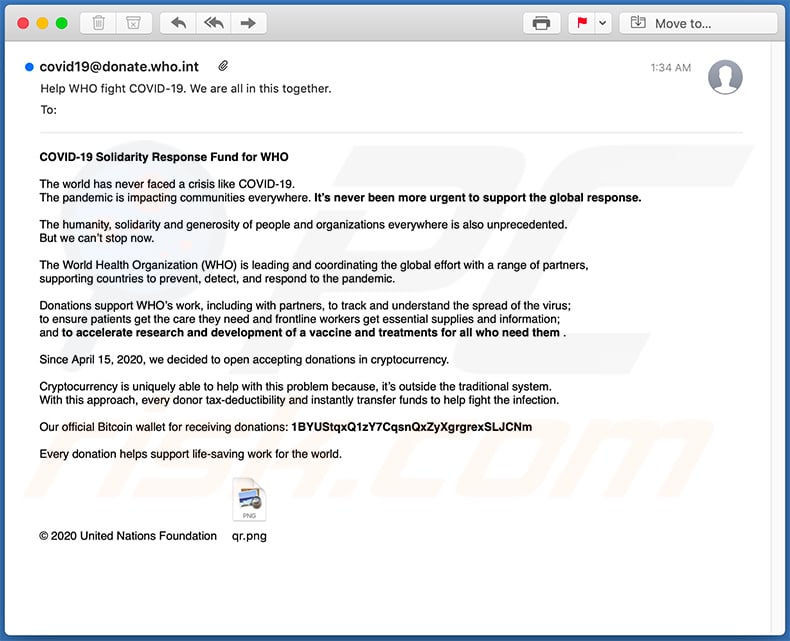
Text presented within this email:
Subject: Help WHO fight COVID-19. We are all in this together.
COVID-19 Solidarity Response Fund for WHO
The world has never faced a crisis like COVID-19.
The pandemic is impacting communities everywhere. It’s never been more urgent to support the global response.The humanity, solidarity and generosity of people and organizations everywhere is also unprecedented.
But we can’t stop now.The World Health Organization (WHO) is leading and coordinating the global effort with a range of partners,
supporting countries to prevent, detect, and respond to the pandemic.Donations support WHO’s work, including with partners, to track and understand the spread of the virus;
to ensure patients get the care they need and frontline workers get essential supplies and information;
and to accelerate research and development of a vaccine and treatments for all who need them .Since April 15, 2020, we decided to open accepting donations in cryptocurrency.
Cryptocurrency is uniquely able to help with this problem because, it’s outside the traditional system.
With this approach, every donor tax-deductibility and instantly transfer funds to help fight the infection.Our official Bitcoin wallet for receiving donations: 1BYUStqxQ1zY7CqsnQxZyXgrgrexSLJCNm
Every donation helps support life-saving work for the world.
© 2020 United Nations Foundation
Yet another scam email presented as a notification from the World Health Organization (WHO):
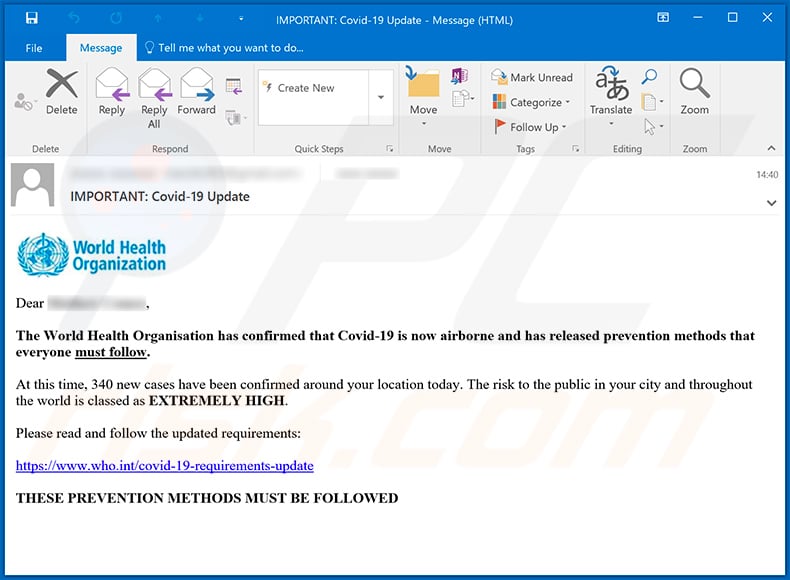
Text presented within:
IMPORTANT: Covid-19 Update
Dear -,
The World Health Organisation has confirmed that Covid-19 is now airborne and has released prevention methods that everyone must follow.
At this time, 340 new cases have been confirmed around your location today. The risk to the public in your city and throughout the world is classed as extremely high.
Please read and follow the updated requirements:
-
THESE PREVENTION METHODS MUST BE FOLLOWED
Yet another fake World Health Organization (WHO) email used to spread Agent Tesla RAT via an attached .iso file ("Xerox_Scan_Covid19_urgent-information-letter.xlxs.iso"):
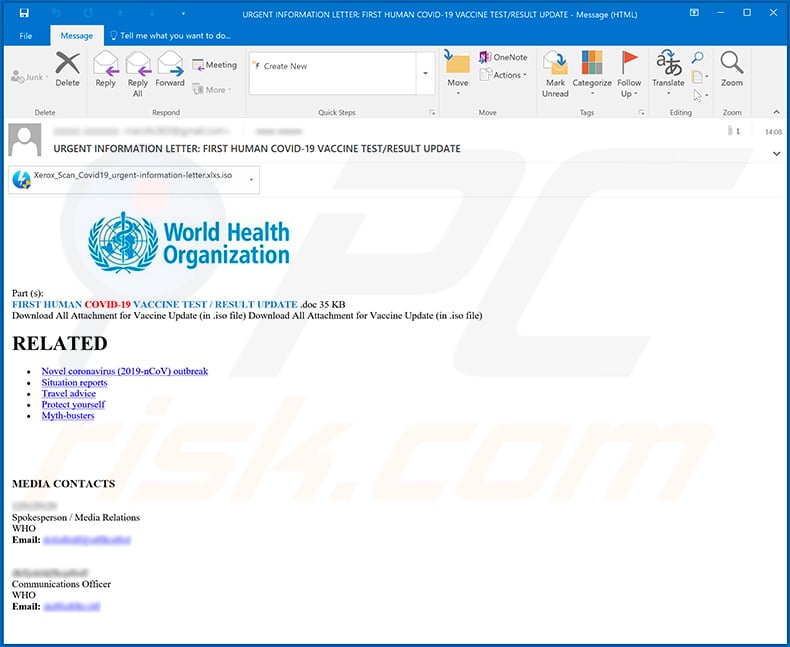
Text presented within:
Subject: URGENT INFORMATION LETTER: FIRST HUMAN COVID-19 VACCINE TEST/RESULT UPDATE
Part (s):
FIRST HUMAN COVID-19 VACCINE TEST / RESULT UPDATE .doc 35 KB
Download All Attachment for Vaccine Update (in .iso file) Download All Attachment for Vaccine Update (in .iso file)RELATED
Novel coronavirus (2019-nCoV) outbreak
Situation reports
Travel advice
Protect yourself
Myth-busters
MEDIA CONTACTS**********
Spokesperson / Media Relations
WHO
Email: **********
**********
Communications Officer
WHO
Email: **********
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is World Health Organization (WHO) spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion