Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is a website sextortion scam?
Typically, scammers proliferate sextortion scams via email, however, in this case, they are implemented through hacked WordPress and Blogger accounts, which post scam messages on the homepages of various websites.
Once opened, the sites display posts stating that the visitor's computer is hacked and the camera was used to record a video, whereby the visitor can be seen watching a video on an adult website. Scammers behind these posts attempt to trick people by stating that they will distribute recorded videos unless victims pay the ransoms.
Never trust these scams, even if they are posted on legitimate blogging websites (such as hacked WebPress, Blogger pages) or elsewhere.
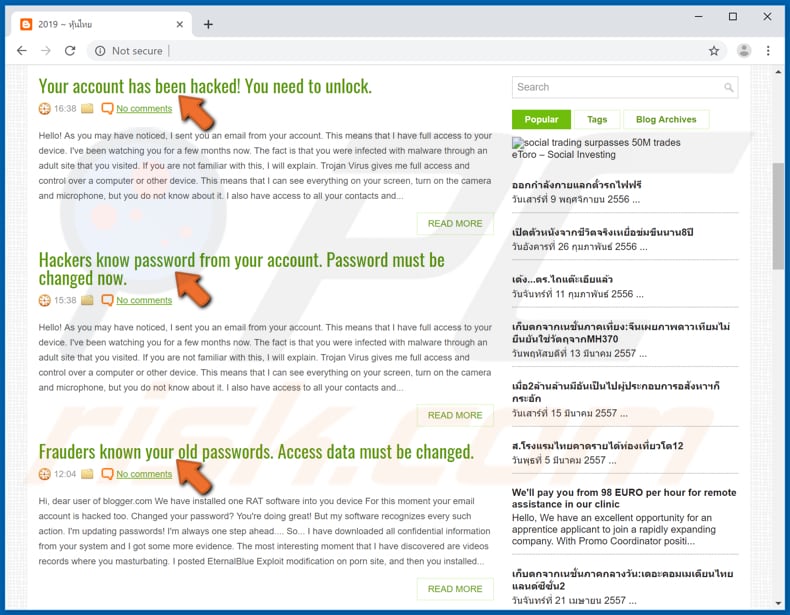
The text within sextortion scams can differ (some examples are provided below), however, scammers use them for the same purpose: to extort money from unsuspecting people.
Scammers claim that the user's computer has been infected with malicious software, which allowed them to access the computer's camera and record a video (or take photos) whilst the user was supposedly visiting an adult website and/or watching an adult video.
They often claim that installed malware was used to record the screen and access the microphone. In any case, scammers threaten to send the compromising material to the user's contacts, friends, and/or to distribute it across the internet, unless they receive a certain sum (typically, in a cryptocurrency).
In our example, they demand approximately $700. If these scams are displayed on legitimate web pages such as WordPress, Blogger, etc., it is likely that another user's account was hacked and employed for fraudulent purposes. As mentioned, scammers often proliferate sextortion scams via email.
In all cases, the messages within these scams should never be trusted. We receive a great deal of feedback from concerned users about this type of email scam.
Here is the most popular question we receive (in this case, relating to a scam that claims to have obtained compromising videos or photos of the user):
Q: Hi pcrisk.com team, I received an email stating that my computer was hacked and they have a video of me. Now they are asking for a ransom in Bitcoins. I think this must be true because they listed my real name and password in the email. What should I do?
A: Do not worry about this email. Neither hackers nor cyber criminals have infiltrated/hacked your computer and there is no video of you watching pornography. Simply ignore the message and do not send any Bitcoins. Your email, name, and password was probably stolen from a compromised website such as Yahoo (these website breaches are common). If you are concerned, you can check if your accounts have been compromised by visiting the haveibeenpwned website.
| Name | Website Sextortion Scam. |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Scammers claim that they have infected a computer with malware that allowed them to record a compromising video or photos. |
| Examples Of Cryptowallet Addresses Owned By Cyber Criminals | 158r99HsERpiBqWg3w2FCPHbUfkXG8Zxsd, 13nsNBfoVwXDHY4puRD1AHjARbomKhsxEL, 3G8a83Y6HgzuyMV4SW4TvBJGyr7Cp2mL3Q, 1MeSv4fBS9BPEV5N5oySxDqnR2JLbchqF9, 1DJakk2a9Z18NMRo4Z8TV6eWu1NvWP5UCW, 15yF8WkUg8PRjJehYW4tGdqcyzc4z7dScM, 1N6dubqFmnyQ2qDWvi32ppVbc3kKMTYcGW |
| Ransom Amount | In these examples, scammers demand to be paid approximately $700. |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Other examples of scams of this type include "Jeanson J. Ancheta Email Scam", "WannaCry Hacker Group Email Scam", and "The Last Time You Visited A Porn Website Email Scam". Scammers behind all claim that they have recorded compromising videos or taken photos and will distribute them unless paid.
The criminals often use emails to trick people into installing malware. They attach a malicious file and hope that recipients opens it. When opened, it installs some high-risk malware. Some examples of malicious programs that are being proliferated through spam campaigns are TrickBot, LokiBot, Emotet, and FormBook.
How do spam campaigns infect computers?
Operating systems can be infected through emails only when people open attached malicious files, or the files are downloaded through website links that are included within the messages. Typically, cyber criminals attach files such as Microsoft Office of PDF documents, JavaScript files, executable files (.exe), and archive files (ZIP, RAR, and so on).
For example, when a recipient opens a malicious MS Office document, it asks for permission to enable editing (macros commands). If this permission is given, the document installs malicious software. In any case, no files attached to emails sent from cyber criminals can infect systems if recipients leave them unopened.
How to avoid installation of malware
Do not open web links or attachments included in irrelevant emails sent from suspicious or unknown addresses. Cyber criminals usually disguise them as official, important, etc.
Download software only from official websites and via direct download links. Third party downloaders and installers, Peer-to-Peer networks such as torrent clients, eMule, dubious pages and other similar channels should not be trusted/used - they are often used to distribute malware.
Keep installed programs and operating systems up-to-date, however, use implemented functions or tools provided by the official developers. The same applies to software activation. Third party 'activators' ('cracking' tools) are illegal and often infect systems by installing high-risk malware.
Have a reputable antivirus or anti-spyware suite installed - keep it up-to-date and scan the system with it regularly. If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Examples of sextortion messages posted on various blogger pages:
Examples of sextortion messages posted on various hijacked WordPress websites:
Examples of sextortion messages presented on these hijacked websites:
Example 1:
Title: Your account is being used by another person!
Hi, dear user of blogger.com
We have installed one RAT software into you device
For this moment your email account is hacked too.
I know your password. I logged in to your account and wrote this letter to you from there.Changed your password? You're doing great!
But my software recognizes every such action. I'm updating passwords!
I'm always one step ahead....So... I have downloaded all confidential information from your system and I got some more evidence.
The most interesting moment that I have discovered are videos records where you masturbating.I posted EternalBlue Exploit modification on porn site, and then you installed my malicious code (trojan) on your operation system.
When you clicked the button Play on porn video, at that moment my trojan was downloaded to your device.
After installation, your front camera shoots video every time you masturbate, in addition, the software is synchronized with the video you choose.For the moment, the software has harvrested all your contact information from social networks and email addresses.
If you need to erase all of your collected data and videos, send me $725 in BTC (crypto currency).This is my Bitcoin wallet: 158r99HsERpiBqWg3w2FCPHbUfkXG8Zxsd
You have 48 hours after reading this letter.After your transaction I will erase all your data.
Otherwise, I will send a video with your sweepstakes to all your colleagues, friends and relatives!!!P.S. I ask you not to reply to this email, this is impossible (the sender's address is your own address).
And henceforth be more careful!
Please visit only secure sites!
Bye,Bye...
Example 2:
Title: Security Notice. Someone have access to your system.
Hello!As you may have noticed, I sent you an email from your account.
This means that I have full access to your device.I've been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited.If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts on social networks.
I can also post access to all your e-mail correspondence and messengers that you use.If you want to prevent this,
transfer the amount of $702 to my bitcoin address (if you do not know how to do this, write to Google: "Buy Bitcoin").My bitcoin address (BTC Wallet) is: 13nsNBfoVwXDHY4puRD1AHjARbomKhsxEL
After receiving the payment, I will delete the video and you will never hear me again.
I give you 50 hours (more than 2 days) to pay.
I have a notice reading this letter, and the timer will work when you see this letter.Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.If I find that you have shared this message with someone else, the video will be immediately distributed.
Best regards!
Example 3:
Title: We Can Make A Deal
Hello!
I have very bad news for you.
25/02/2019 - on this day I hacked your OS and got full access to your account ********So, you can change the password, yes... But my malware intercepts it every time.
How I made it:
In the software of the router, through which you went online, was a vulnerability.
I just hacked this router and placed my malicious code on it.
When you went online, my trojan was installed on the OS of your device.After that, I made a full dump of your disk (I have all your address book, history of viewing sites, all files, phone numbers and addresses of all your contacts).
A month ago, I wanted to lock your device and ask for a not big amount of btc to unlock.
But I looked at the sites that you regularly visit, and I was shocked by what I saw!!!
I'm talk you about sites for adults.I want to say - you are a BIG pervert. Your fantasy is shifted far away from the normal course!
And I got an idea....
I made a screenshot of the adult sites where you have fun (do you understand what it is about, huh?).
After that, I made a screenshot of your joys (using the camera of your device) and glued them together.
Turned out amazing! You are so spectacular!I'm know that you would not like to show these screenshots to your friends, relatives or colleagues.
I think $750 is a very, very small amount for my silence.
Besides, I have been spying on you for so long, having spent a lot of time!Pay ONLY in Bitcoins!
My BTC wallet: 1MeSv4fBS9BPEV5N5oySxDqnR2JLbchqF9You do not know how to use bitcoins?
Enter a query in any search engine: "how to replenish btc wallet".
It's extremely easyFor this payment I give you two days (48 hours).
As soon as this letter is opened, the timer will work.After payment, my virus and dirty screenshots with your enjoys will be self-destruct automatically.
If I do not receive from you the specified amount, then your device will be locked, and all your contacts will receive a screenshots with your "enjoys".I hope you understand your situation.
- Do not try to find and destroy my virus! (All your data, files and screenshots is already uploaded to a remote server)
- Do not try to contact me (this is impossible, sender's address was randomly generated)
- Various security services will not help you; formatting a disk or destroying a device will not help, since your data is already on a remote server.P.S. You are not my single victim. so, I guarantee you that I will not disturb you again after payment!
This is the word of honor hackerI also ask you to regularly update your antiviruses in the future. This way you will no longer fall into a similar situation.
Do not hold evil! I just do my job.
Have a nice day!
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is website sextortion scam?
- STEP 1. Manual removal of possible malware infections.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically.
To remove this malware we recommend using Combo Cleaner Antivirus for Windows. If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
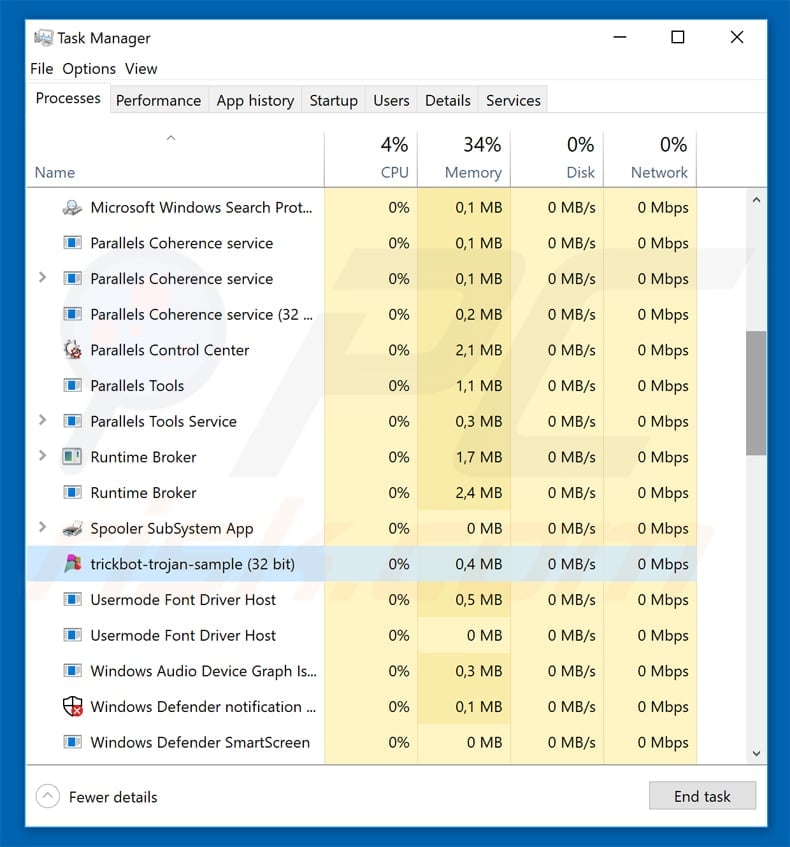
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
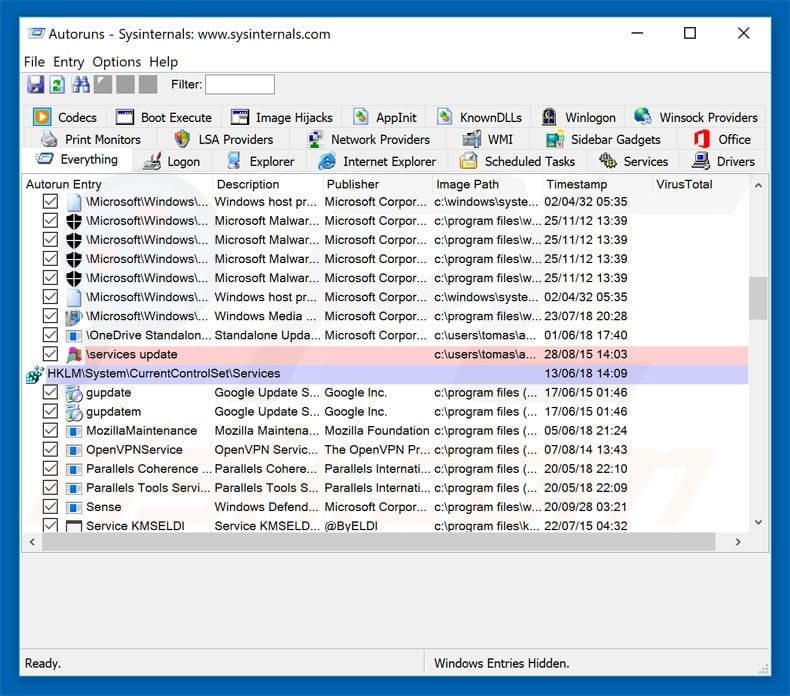
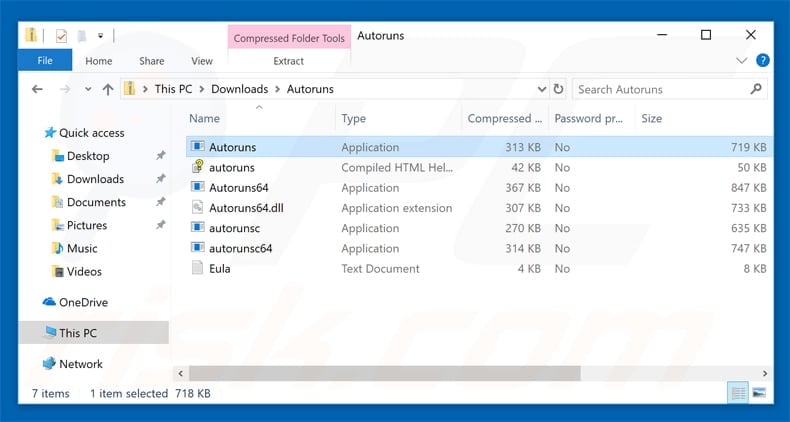
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
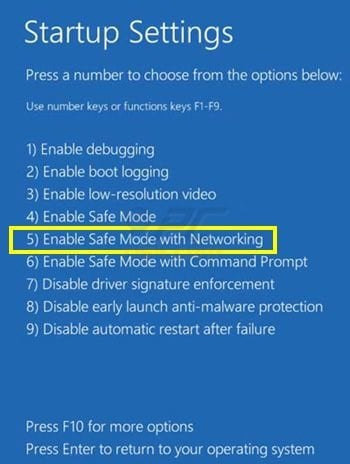
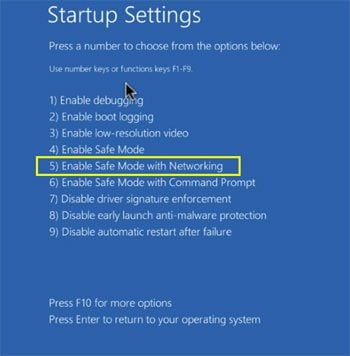
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
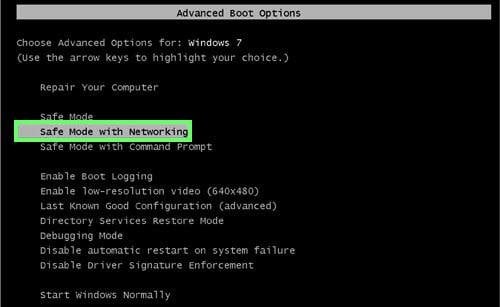
Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings". Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options". In the advanced options menu select "Startup Settings" and click on the "Restart" button.
In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
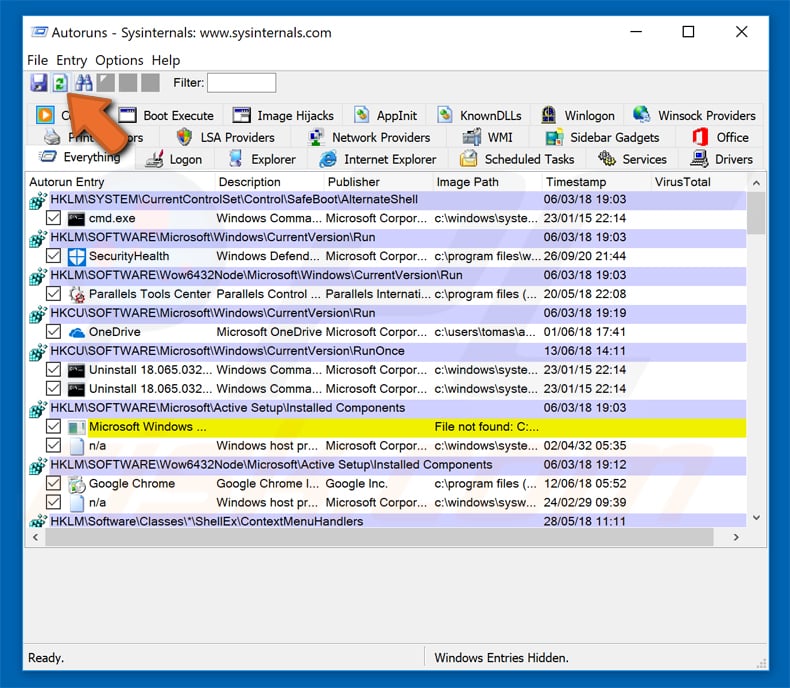
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
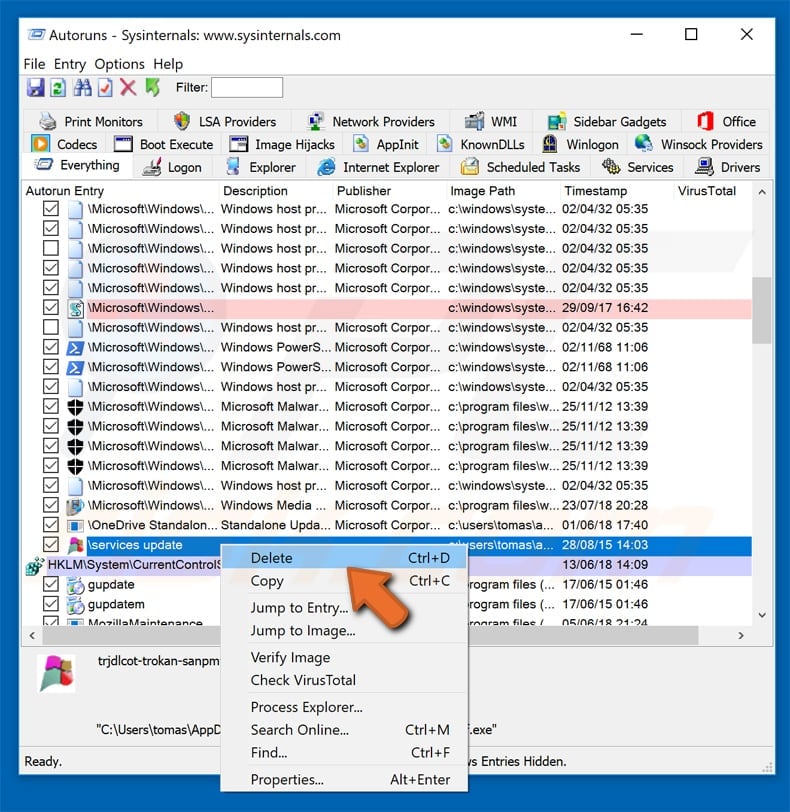
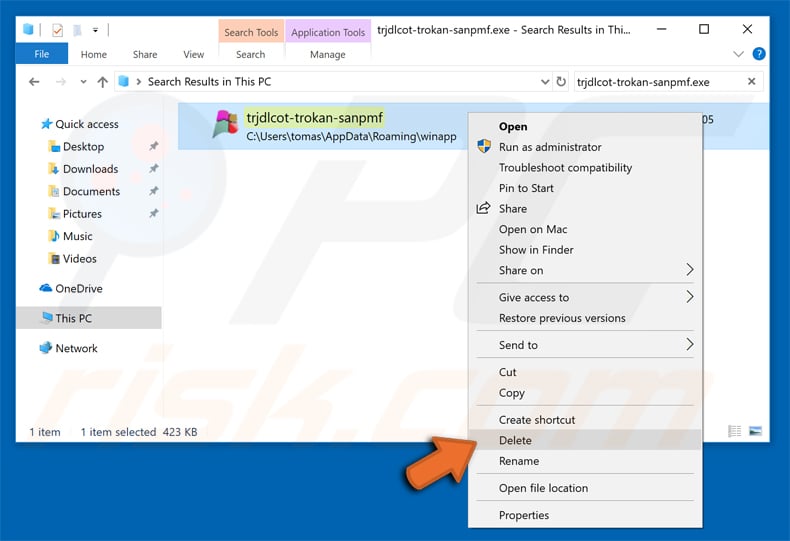
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software.
To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate










▼ Show Discussion