Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the fake "BRT" email?
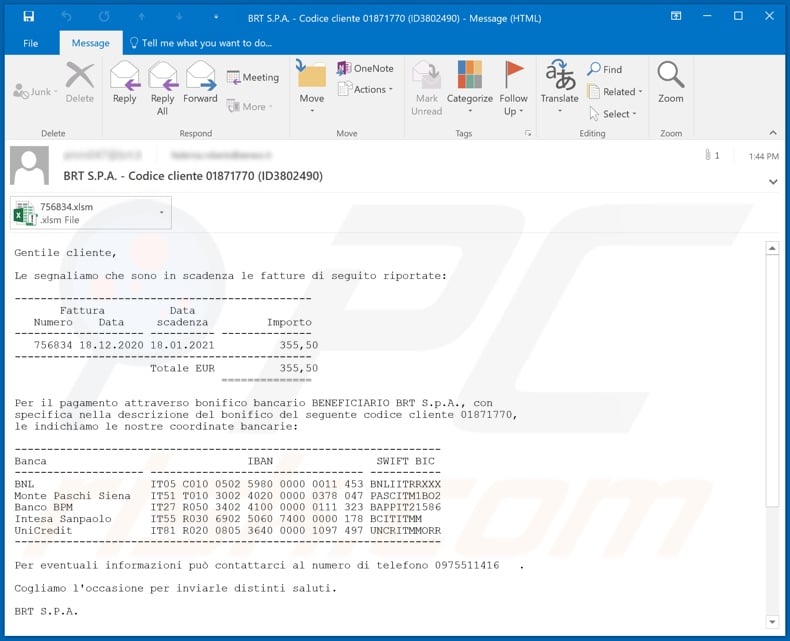
"BRT Email Virus" refers to a spam campaign spreading the Ursnif trojan. The term "spam campaign" defines a large-scale operation, during which thousands of deceptive emails are distributed. The "BRT" scam emails target Italian users and are presented as notifications about due invoices.
These messages have infectious files attached. When these are opened (thereby executing malicious macro commands), the infection chain of Ursnif malware starts.
More about the fake "BRT" email
The "BRT Email Virus" messages (the subject/title "BRT S.P.A. - Codice cliente 01871770 (ID3802490)" might vary) are disguised as due invoice alerts. The total pending sum is stated to be 355,50 EUR.
To give the impression of legitimacy, the scam emails list five real Italian banks: Banca Nazionale del Lavoro (BNL), Banca Monte dei Paschi di Siena, Banco BPM, Intesa Sanpaolo and UniCredit. The messages are concluded with a statement that, according to current law, these messages and/or their attachments may contain confidential/privileged information.
Should users not be the intended recipients, they are warned against taking action, using, copying or otherwise disclosing this information. Additionally, if the fake invoices have been received by error, recipients are asked to contact the sender and delete the emails.
Note that "BRT Email Virus" messages are fake and none of the information provided by them is true. The sole purpose of these emails is to infect recipients' systems with the Ursnif Trojan.
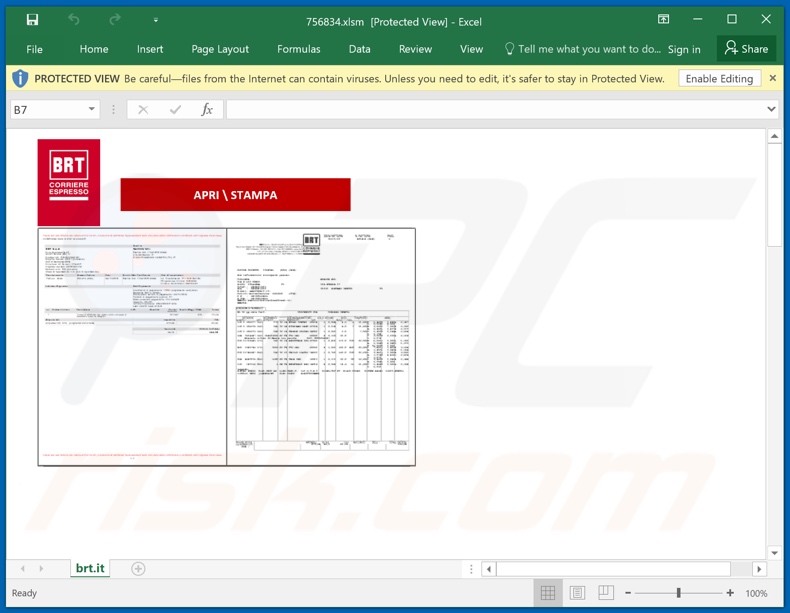
The infection process (i.e. malware download/installation) is triggered by opening the Microsoft Office document ("756834.xlsm" - the filename may vary) attached to the "BRT" scam emails. Specifically, infection begins the moment macro commands (i.e. editing/content) are enabled.
The main functionality of the Ursnif Trojan is stealing information from infected devices. Data of interest includes: user and system information, browsing activity, log-in credentials (i.e. IDs, usernames and passwords) stored on browsers and other applications, as well as key strokes (i.e. typed data).
Other capabilities of this malicious program is restarting the system, taking screenshots and infiltrating/executing files (typically used to download/install additional malware). To summarize, Ursnif infections can result in severe privacy issues, financial losses and even identity theft.
If it is suspected or known that Ursnif (or other malware) has already infected the system, use anti-virus software to remove it immediately.
| Name | BRT Email Virus |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
| Hoax | Scam emails are disguised as due invoices |
| Attachment(s) | 756834.xlsm |
| Detection Names | Avast (SNH:Script [Dropper]), BitDefender (Trojan.GenericKD.45553196), ESET-NOD32 (VBA/Agent.VR), Kaspersky (HEUR:Trojan.Script.Generic), Microsoft (TrojanDownloader:O97M/Dridex.AJ!MTB), Full List Of Detections (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Payload | Ursnif |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Examples of other malspam campaigns
"DHL Failed Delivery Notification", "Bill Of Lading", "Order Confirmation", "EniGaseLuce" and "Universal Medical Equipment" are some examples of other malware-proliferating spam campaigns.
Emails sent through these operations are usually presented as "important", "urgent", "priority" and similar. They may even be disguised as mail from genuine institutions, companies, service providers and other entities. Deceptive emails are not employed just for distributing malicious software, they are also used for phishing and other scams.
How did "BRT Email Virus" infect my computer?
Typically, cyber criminals behind malspam campaigns send emails with a file attached to them or a download link to the malicious file. Their main goal is to trick recipients into opening/executing the rogue file, which then installs malicious software.
Some examples of files that cyber criminals send via email are Microsoft Office and PDF documents, executables (.exe), JavaScript, and archives (ZIP, RAR).
Note that malicious documents that are opened with Microsoft Office 2010 or newer versions install malicious software only if users enable macros commands (enable editing/content). These versions include "Protected View" mode, which does not allow opened malicious documents to install malware automatically. Older versions do not include this feature and install malicious software without asking permission.
How to avoid installation of malware
To avoid malware spread via spam mail, you are strongly advised against opening suspicious or irrelevant emails, especially those with any attachments or links present within them.
Additionally, use Microsoft Office versions released after 2010. Malicious programs also proliferate through untrusted download channels (e.g. unofficial and free file-hosting sites, Peer-to-Peer sharing networks and other third party downloaders), illegal software activation ("cracking") tools, and fake updaters.
Therefore, only download from official/verified sources and activate and update software with tools/functions provided by legitimate developers.
To ensure device integrity and user privacy, have a reputable anti-virus/anti-spyware suite installed and kept updated. Furthermore, use these programs to run regular system scans and to remove detected/potential threats.
If you have already opened "BRT Email Virus" attachment, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "BRT" scam email message:
Subject: BRT S.P.A. - Codice cliente 01871770 (ID3802490)
Gentile cliente,
Le segnaliamo che sono in scadenza le fatture di seguito riportate:
----------------------------------------------
Fattura Data
Numero Data scadenza Importo
-------------------- ---------- --------------
756834 18.12.2020 18.01.2021 355,50
----------------------------------------------
Totale EUR 355,50
==============
Per il pagamento attraverso bonifico bancario BENEFICIARIO BRT S.p.A., con
specifica nella descrizione del bonifico del seguente codice cliente 01871770,
le indichiamo le nostre coordinate bancarie:
------------------------------------------------------------------
Banca IBAN SWIFT BIC
-------------------- --------------------------------- -----------
BNL IT05 C010 0502 5980 0000 0011 453 BNLIITRRXXX
Monte Paschi Siena IT51 T010 3002 4020 0000 0378 047 PASCITM1BO2
Banco BPM IT27 R050 3402 4100 0000 0111 323 BAPPIT21586
Intesa Sanpaolo IT55 R030 6902 5060 7400 0000 178 BCITITMM
UniCredit IT81 R020 0805 3640 0000 1097 497 UNCRITMMORR
------------------------------------------------------------------
Per eventuali informazioni può contattarci al numero di telefono 0975511416 .
Cogliamo l'occasione per inviarle distinti saluti.
BRT S.P.A.
Ai sensi della vigente normativa in ambito di protezione dei dati personali si precisa che le informazioni contenute in questo messaggio sono riservate ed a uso esclusivo del destinatario. Qualora il messaggio in parola Le fosse pervenuto per errore, la preghiamo di eliminarlo senza copiarlo e di non inoltrarlo a terzi, dandocene gentilmente comunicazione. Grazie.
This message, according to the present law, may contain confidential and/or privileged information. If you are not the addressee or authorized to receive this for the addressee, you should not use, copy, disclose or take any action based on this message or any information herein If you have received this message in error, please advise the sender immediately by reply e-mail and delete this message. Thank you for your cooperation.
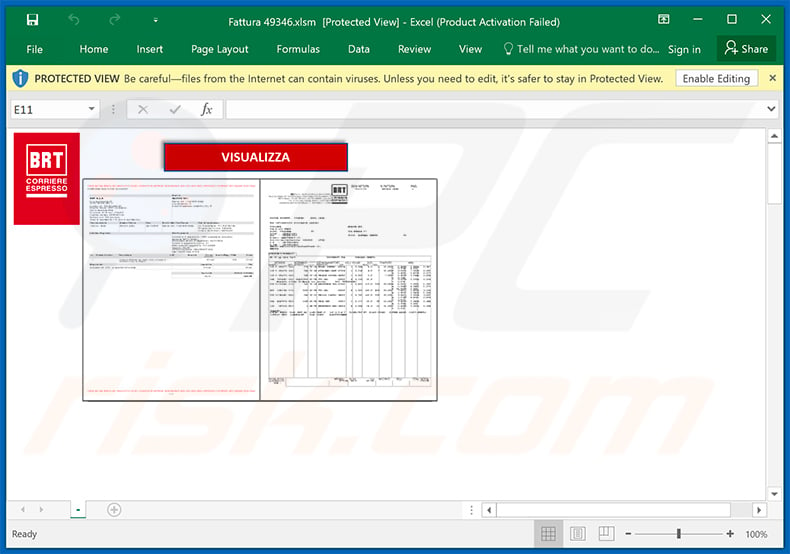
Malicious attachment distributed via "BRT Email Virus" spam campaign ("756834.xlsm"):
An example of BRT-themed spam email used to promote a phishing website:
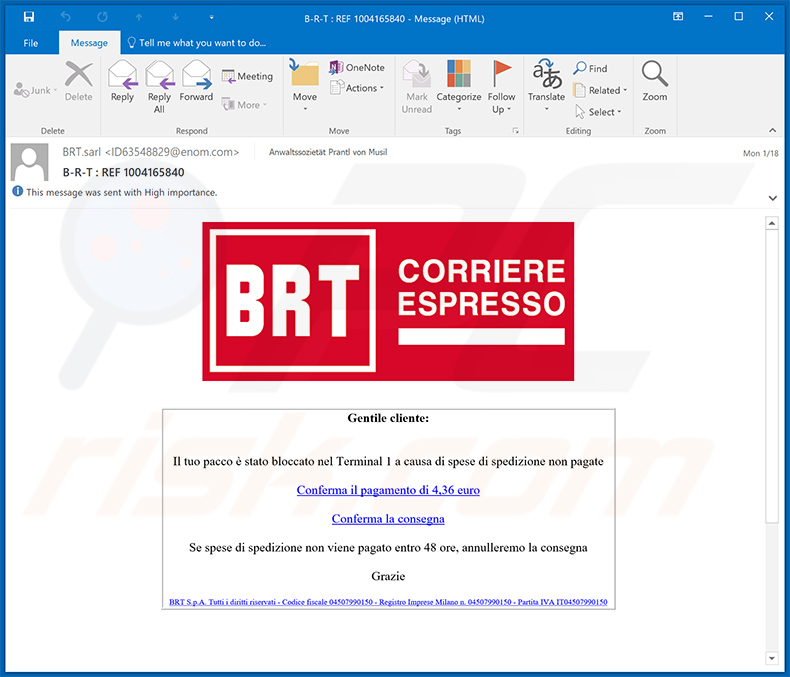
Text presented within:
Subject: B-R-T : REF 1004165840
Gentile cliente:Il tuo pacco è stato bloccato nel Terminal 1 a causa di spese di spedizione non pagate
Conferma il pagamento di 4,36 euro
Conferma la consegna
Se spese di spedizione non viene pagato entro 48 ore, annulleremo la consegna
Grazie
BRT S.p.A. Tutti i diritti riservati - Codice fiscale 04507990150 - Registro Imprese Milano n. 04507990150 - Partita IVA IT04507990150
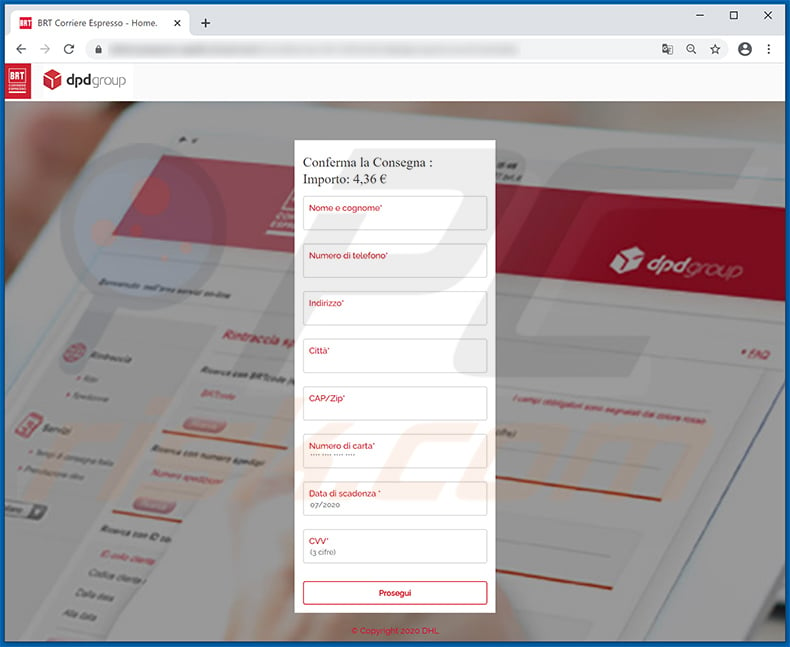
Screenshot of the promoted phishing site:
Another example of BRT S.P.A.-themed spam email used to spread Ursnif malware:
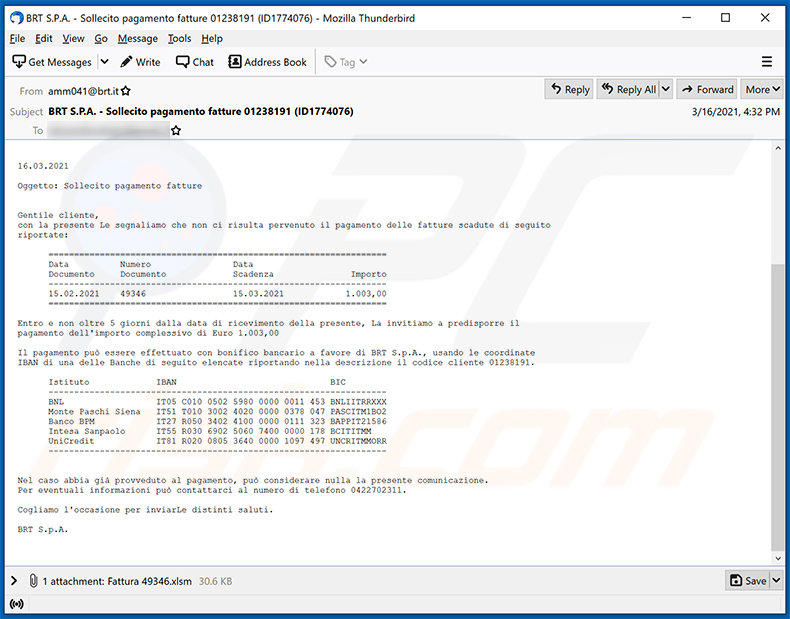
Text presented within:
Subject: BRT S.P.A. - Sollecito pagamento fatture 01238191 (ID1774076)
16.03.2021
Oggetto: Sollecito pagamento fatture
Gentile cliente,
con la presente Le segnaliamo che non ci risulta pervenuto il pagamento delle fatture scadute di seguito
riportate:===================================
Data Numero Data
Documento Documento Scadenza Importo
-----------------------------------
15.02.2021 49346 15.03.20211.003,00
===================================Entro e non oltre 5 giorni dalla data di ricevimento della presente, La invitiamo a predisporre il
pagamento dell'importo complessivo di Euro 1.003,00Il pagamento può essere effettuato con bonifico bancario a favore di BRT S.p.A., usando le coordinate
IBAN di una delle Banche di seguito elencate riportando nella descrizione il codice cliente 01238191.Istituto IBANBIC
-----------------------------------
BNLIT05 C010 0502 5980 0000 0011 453 BNLIITRRXXX
Monte Paschi Siena IT51 T010 3002 4020 0000 0378 047 PASCITM1BO2
Banco BPMIT27 R050 3402 4100 0000 0111 323 BAPPIT21586
Intesa SanpaoloIT55 R030 6902 5060 7400 0000 178 BCITITMM
UniCreditIT81 R020 0805 3640 0000 1097 497 UNCRITMMORR
-----------------------------------Nel caso abbia già provveduto al pagamento, può considerare nulla la presente comunicazione.
Per eventuali informazioni può contattarci al numero di telefono 0422702311.Cogliamo l'occasione per inviarLe distinti saluti.
BRT S.p.A.
Screenshot of the attached malicious MS Excel document:
Yet another example of BRT-themed spam email promoting a phishing website:
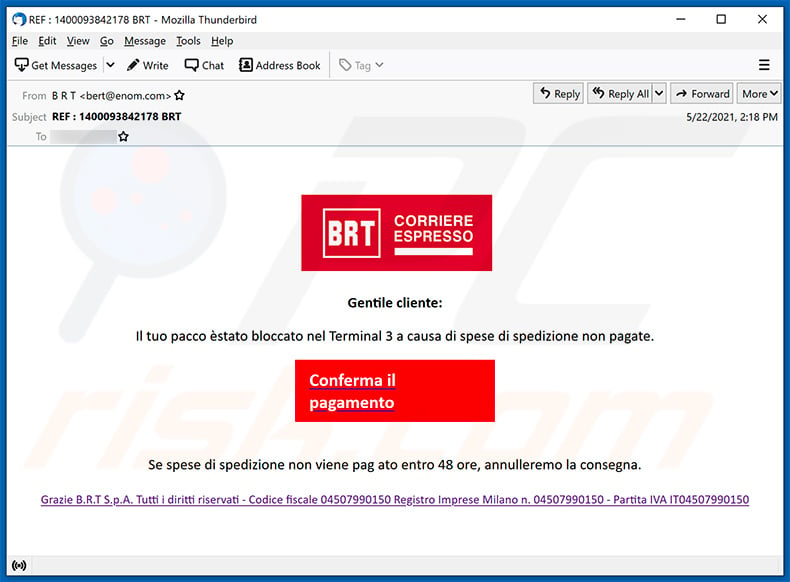
Text presented within:
Subject: REF : 1400093842178 BRT
BRT
CORRERIE
ESPRESSOGentile cliente:
Il tuo pacco èstato bloccato nel Terminal 3 a causa di spese di spedizione non pagate.
Conferma il pagamento
Se spese di spedizione non viene pag ato entro 48 ore, annulleremo la consegna.
Grazie B.R.T S.p.A. Tutti i diritti riservati - Codice fiscale 04507990150 Registro Imprese Milano n. 04507990150 - Partita IVA IT04507990150
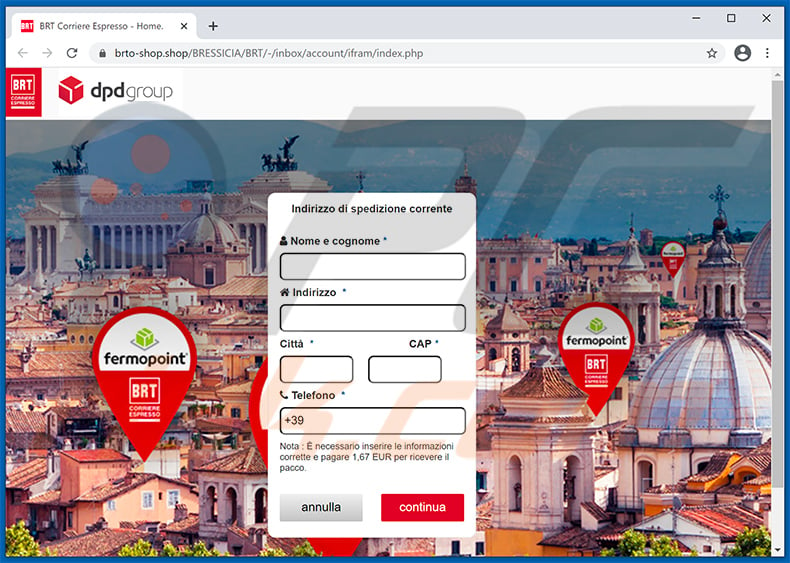
Screenshot of the promoted phishing website (brto-shop[.]shop):
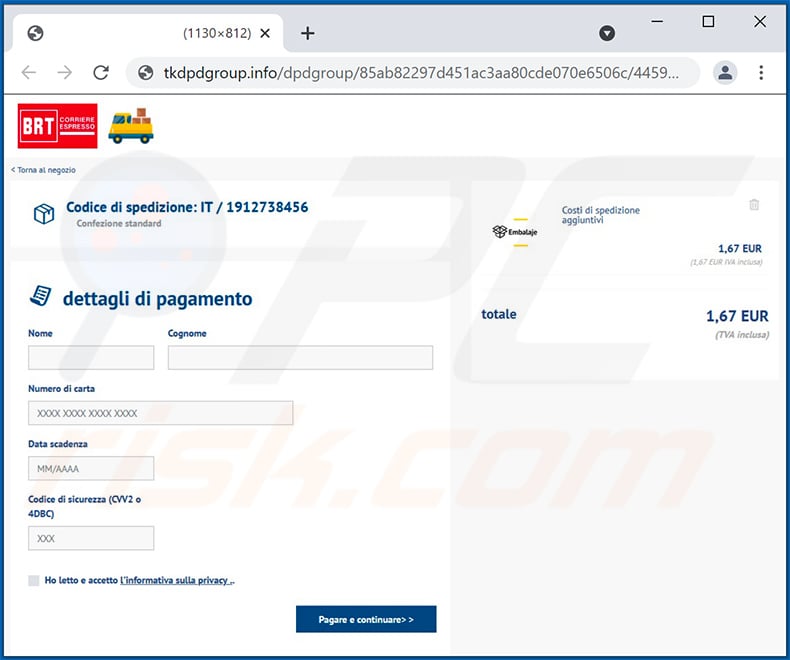
Another example of BRT-themed spam email used to promote a phishing website:
Text presented within:
Subject: Il tuo pacco non può essere consegnato
Caro cliente,
Il tuo pacco non può essere consegnato oggi a causa delle spese di sdoganamento aggiuntive non pagate. Verrà consegnato non appena verrà pagato il costo.
Commissioni pagabili : 1,67 EUR.
Area Clienti
Data : 15/07/2021
BRT S.p.A. Tutti i diritti riservati
Codice fiscale 04507990150 - Registro Imprese Milano n. 04507990150- Partitz IVA IT04507990150
Screenshot of the promoted phishing site:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is BRT spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
The intention of scammers is to send out identical letters to a large number of recipients in the hopes that someone will be tricked into falling for it. Thus, spam emails are never personalized.
I have provided my personal information when tricked by this email, what should I do?
In case you have shared any of your account login information, it is recommended that you change all passwords without delay. If you have disclosed any sensitive personal data, such as credit card details or ID card information, it is important to promptly inform the relevant authorities.
I have downloaded and opened a file attached to this email, is my computer infected?
If the file in question was an executable, it is highly likely that it could have caused an infection. However, if it was a document such as .pdf or .doc, there is a possibility that the system may not have been infiltrated, as merely opening the document does not always lead to a malware infection.
I have read the email but didn't open the attachment, is my computer infected?
Merely opening an email does not pose any harm to the system. However, system infections may occur as a result of clicking on links within the email or opening attached files.
Will Combo Cleaner remove malware infections that were present in email attachment?
Combo Cleaner can identify and remove almost all known malware infections. It is important to note that advanced malware tends to conceal itself deeply within the system, so conducting a complete system scan is essential.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion