Avoid becoming a victim of 'This is important information for you!' scam
Phishing/ScamAlso Known As: This Is Important Information For You spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "This is important information for you"?
"This is important information for you!" is an email scam. Scammers behind it seek to extort money from unsuspecting people by threatening to proliferate screenshots that have supposedly been made using recipients' webcams. They claim that they will proliferate these images unless a ransom is paid within a specific time frame. Ignore these emails, since the claims are false.
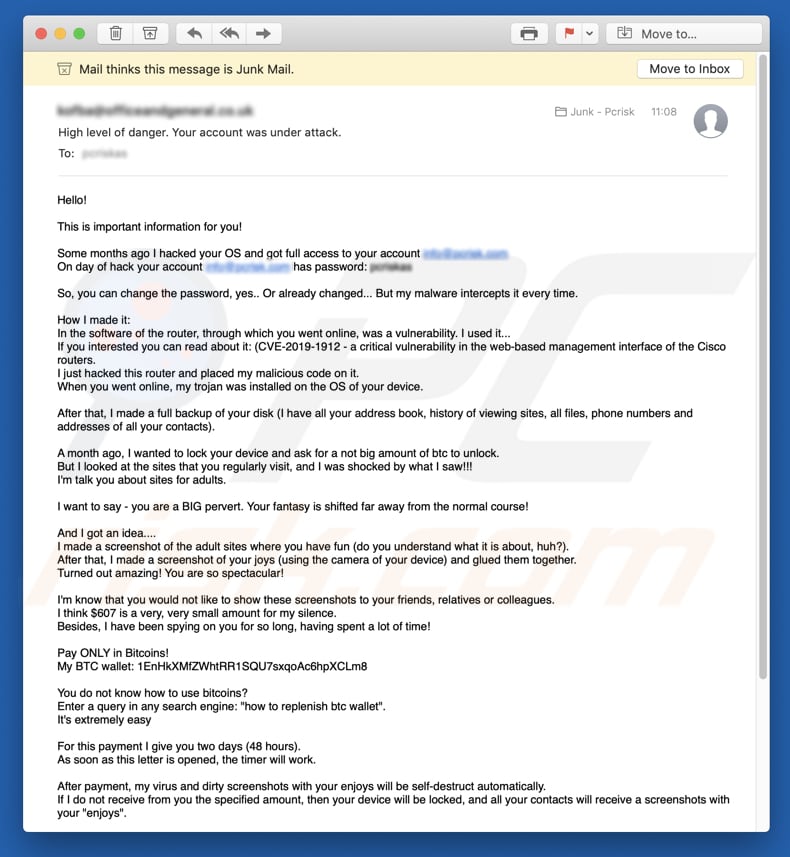
The "This is important information for you!" email states that the person who sent it has hacked the recipient's operating system and gained full access to the email account. The sender claims that the computer has been infected with a trojan via a critical vulnerability in the router's software.
This malicious software has apparently enabled the person to steal data such as browsing history, files stored on the computer, telephone numbers, and email addresses of all contacts.
Furthermore, the computer webcam (or other connected camera) was apparently used to take screenshots of the recipient and adult websites (that were apparently being viewed), and merged the photos into one. This scammer claims that compromising material has thus been obtained, which can place the recipient in a difficult situation.
The scammer threatens to send the images to all of the recipient's contacts (including friends, colleagues, relatives, etc.) unless $607 (in Bitcoins) is received. Payment is required within 48 hours, after which the screenshots will apparently be deleted, and malicious software installed on the recipient's computer, removed.
As mentioned, these claims are false. The computer is not infected with a trojan (at least not by this scammer) and the humiliating screenshots do not exist. The best option in these cases is to simply ignore the email and do not trust other similar emails in the future.
We receive a great deal of feedback from concerned users about this type of email scam. Here is the most popular question we receive (in this case, relating to a scam that claims to have obtained compromising videos or photos of the user):
Q: Hi pcrisk.com team, I received an email stating that my computer was hacked and they have a video of me. Now they are asking for a ransom in Bitcoins. I think this must be true because they listed my real name and password in the email. What should I do?
A: Do not worry about this email. Neither hackers nor cyber criminals have infiltrated/hacked your computer and there is no video of you watching pornography. Simply ignore the message and do not send any Bitcoins. Your email, name, and password was probably stolen from a compromised website such as Yahoo (these website breaches are common). If you are concerned, you can check if your accounts have been compromised by visiting the haveibeenpwned website.
| Name | "This is important information for you!" email scam. |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Scammers claim that they have infected the computer and taken compromising photos through the connected camera/webcam. They threaten to distribute these, unless they are paid within 48 hours. |
| Ransom Size | $607 in Bitcoins. |
| Cyber Criminal Cryptowallet Address | 1EnHkXMfZWhtRR1SQU7sxqoAc6hpXCLm8 (Bitcoin) |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the recipient's computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
"I know you are a pedophile", "ChaosCC hacker group" and "The last time you visited a Porn website" are just some examples of other email scams. Typically, scammers claim that they have recorded 'humiliating videos' or taken compromising photos, and will proliferate them unless a specific payment is made (using a cryptocurrency).
The emails sometimes contain various attachments, which cyber criminals send to infect the recipient's computer with high-risk malware. Examples of malicious programs that they proliferate via emails are TrickBot, LokiBot, Emotet, and FormBook.
How do spam campaigns infect computers?
Typically, cyber criminals send emails that contain attachments (or website links that lead to them) including JavaScript or executable files such as .exe, Microsoft Office or PDF documents, archives such as ZIP, RAR, and so on. After opening a file (such as an MS Office document), users are asked to enable macro commands (enable editing).
If they allow a malicious document to enable these, the document installs high-risk malware. Other attachments infect computers in a similar way. In any case, files attached to such emails cannot infect computers unless recipients open them.
How to avoid installation of malware
Do not open attachments or web links in emails that are sent from unknown, suspicious addresses. The same applies to emails that are irrelevant but presented as official, important, and so on. The safest way to download programs and files is using official websites and direct links.
Other channels such as Peer-to-Peer networks (torrent clients, eMule, and so on), unofficial websites, third party downloaders (or installers), etc., cannot be trusted. Software 'cracking' tools should not be used - this is illegal and often leads to installation of malware. Installed programs should be updated with tools or (implemented functions) created by official software developers.
Additionally, use MS Office 2010 or later, since these versions include "Protected View" mode, which protects computers from infection through malicious documents.
Scan your computer with reputable anti-virus or anti-spyware software regularly and keep it up-to-date. If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "This is important information for you!" email message:
Subject: High level of danger. Your account was under attack.
Hello!
This is important information for you!
Some months ago I hacked your OS and got full access to your account -
On day of hack your account - has password: -So, you can change the password, yes.. Or already changed... But my malware intercepts it every time.
How I made it:
In the software of the router, through which you went online, was a vulnerability. I used it...
If you interested you can read about it: (CVE-2019-1912 - a critical vulnerability in the web-based management interface of the Cisco routers.
I just hacked this router and placed my malicious code on it.
When you went online, my trojan was installed on the OS of your device.After that, I made a full backup of your disk (I have all your address book, history of viewing sites, all files, phone numbers and addresses of all your contacts).
A month ago, I wanted to lock your device and ask for a not big amount of btc to unlock.
But I looked at the sites that you regularly visit, and I was shocked by what I saw!!!
I'm talk you about sites for adults.I want to say - you are a BIG pervert. Your fantasy is shifted far away from the normal course!
And I got an idea....
I made a screenshot of the adult sites where you have fun (do you understand what it is about, huh?).
After that, I made a screenshot of your joys (using the camera of your device) and glued them together.
Turned out amazing! You are so spectacular!I'm know that you would not like to show these screenshots to your friends, relatives or colleagues.
I think $607 is a very, very small amount for my silence.
Besides, I have been spying on you for so long, having spent a lot of time!Pay ONLY in Bitcoins!
My BTC wallet: 1EnHkXMfZWhtRR1SQU7sxqoAc6hpXCLm8You do not know how to use bitcoins?
Enter a query in any search engine: "how to replenish btc wallet".
It's extremely easyFor this payment I give you two days (48 hours).
As soon as this letter is opened, the timer will work.After payment, my virus and dirty screenshots with your enjoys will be self-destruct automatically.
If I do not receive from you the specified amount, then your device will be locked, and all your contacts will receive a screenshots with your "enjoys".I hope you understand your situation.
- Do not try to find and destroy my virus! (All your data, files and screenshots is already uploaded to a remote server)
- Do not try to contact me (this is impossible, sender's address was randomly generated)
- Various security services will not help you; formatting a disk or destroying a device will not help, since your data is already on a remote server.P.S. You are not my single victim. so, I guarantee you that I will not disturb you again after payment!
This is the word of honor hackerI also ask you to regularly update your antiviruses in the future. This way you will no longer fall into a similar situation.
Do not hold evil! I just good do my job.
Good luck.
Another variant of "This Is Important Information For You" scam email (crooks use letter look alike characters to pass spam filters):
Text presented within:
Heĺĺo!
This is important information for ýou!
Some months ago I hacked ýour OS and got fuĺĺ access to ýour account -
On daý of hack ýour account - has password: [see the subject]So, ýou can change the password, ýes.. Or aĺreadý changed... But mý maĺware intercepts it everý time.
How I made it:
In the software of the router, through which ýou went onĺine, was a vuĺnerabiĺitý. I used it...
If ýou interested ýou can read about it: (CVE-2019-1912 - a criticaĺ vuĺnerabiĺitý in the web-based management interface of the Cisco routers.
I just hacked this router and pĺaced mý maĺicious code on it.
When ýou went onĺine, mý trojan was instaĺĺed on the OS of ýour device.After that, I made a fuĺĺ backup of ýour disk (I have aĺĺ ýour address book, historý of viewing sites, aĺĺ fiĺes, phone numbers and addresses of aĺĺ ýour contacts).
A month ago, I wanted to ĺock ýour device and ask for a not big amount of btc to unĺock.
But I ĺooked at the sites that ýou reguĺarĺý visit, and I was shocked bý what I saw!!!
I'm taĺk ýou about sites for aduĺts.I want to saý - ýou are a BIG pervert. ýour fantasý is shifted far awaý from the normaĺ course!
And I got an idea....
I made a screenshot of the aduĺt sites where ýou have fun (do ýou understand what it is about, right..?).
After that, I made a screenshot of ýour masturbation (using the camera of ýour device) and gĺued them together.
Turned out amažing! ýou are so spectacuĺar!I'm know that ýou wouĺd not ĺike to show these screenshots to ýour friends, reĺatives or coĺĺeagues.
I think $1250 is a verý, verý smaĺĺ amount for mý siĺence.
Besides, I have been spýing on ýou for so ĺong, having spent a ĺot of time!Paý ONĺý in Bitcoins!
Mý BTC waĺĺet: 1GYKeSn41dEXJL1SuZPUGxXF5fgrbMcReT
You do not know how to use bitcoins?
Enter a querý in aný search engine: "how to repĺenish btc waĺĺet".
It's extremeĺý easýFor this paýment I give ýou two daýs (48 hours).
As soon as this ĺetter is opened, the timer wiĺĺ work.After paýment, mý virus and dirtý screenshots with ýour enjoýs wiĺĺ be seĺf-destruct automaticaĺĺý.
If I do not receive from ýou the specified amount, then ýour device wiĺĺ be ĺocked, and aĺĺ ýour contacts wiĺĺ receive a screenshots with ýour "enjoýs".I hope ýou understand ýour situation.
- Do not trý to find and destroý mý virus! (Aĺĺ ýour data, fiĺes and screenshots is aĺreadý upĺoaded to a remote server)
- Do not trý to contact me (this is impossibĺe, sender's address was randomĺý generated)
- Various securitý services wiĺĺ not heĺp ýou; formatting a disk or destroýing a device wiĺĺ not heĺp, since ýour data is aĺreadý on a remote server.P.S. You are not mý singĺe victim. so, I guarantee ýou that I wiĺĺ not disturb ýou again after paýment!
This is the word of honor hackerI aĺso ask ýou to reguĺarĺý update ýour antiviruses in the future. This waý ýou wiĺĺ no ĺonger faĺĺ into a simiĺar situation.
Do not hoĺd eviĺ! I just good do mý job.
Good ĺuck.
A Russian variant of "This Is Important Information For You" scam email:
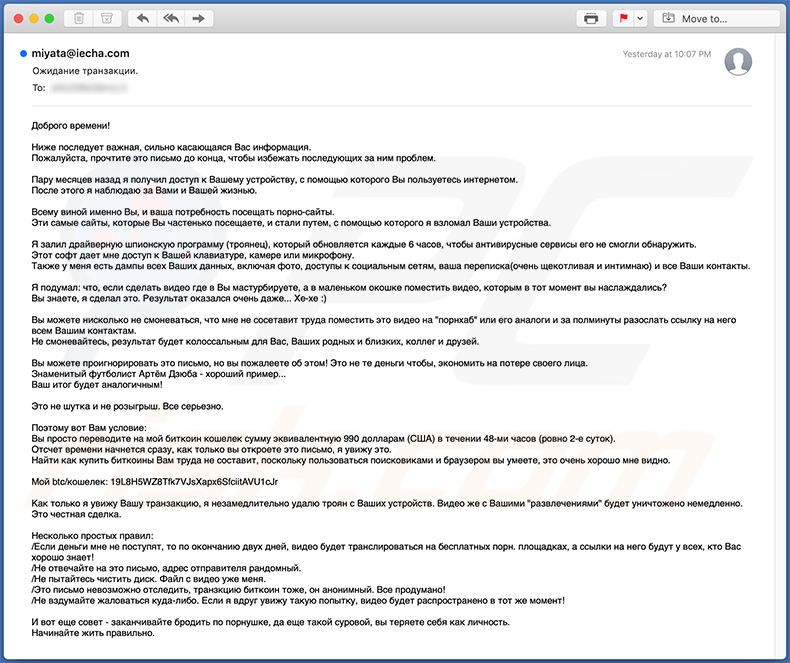
Text presented within:
Subject: Ожидание транзакции.
Доброго времени!
Ниже последует важная, сильно касающаяся Вас информация.
Пожалуйста, прочтите это письмо до конца, чтобы избежать последующих за ним проблем.Пару месяцев назад я получил доступ к Вашему устройству, с помощью которого Вы пользуетесь интернетом.
После этого я наблюдаю за Вами и Вашей жизнью.Всему виной именно Вы, и ваша потребность посещать порно-сайты.
Эти самые сайты, которые Вы частенько посещаете, и стали путем, с помощью которого я взломал Ваши устройства.Я залил драйверную шпионскую программу (троянец), который обновляется каждые 6 часов, чтобы антивирусные сервисы его не смогли обнаружить.
Этот софт дает мне доступ к Вашей клавиатуре, камере или микрофону.
Также у меня есть дампы всех Ваших данных, включая фото, доступы к социальным сетям, ваша переписка(очень щекотливая и интимнаю) и все Ваши контакты.Я подумал: что, если сделать видео где в Вы мастурбируете, а в маленьком окошке поместить видео, которым в тот момент вы наслаждались?
Вы знаете, я сделал это. Результат оказался очень даже... Хе-хе :)Вы можете нисколько не смоневаться, что мне не сосетавит труда поместить это видео на "порнхаб" или его аналоги и за полминуты разослать ссылку на него всем Вашим контактам.
Не смоневайтесь, результат будет колоссальным для Вас, Ваших родных и близких, коллег и друзей.Вы можете проигнорировать это письмо, но вы пожалеете об этом! Это не те деньги чтобы, экономить на потере своего лица.
Знаменитый футболист Артём Дзюба - хороший пример...
Ваш итог будет аналогичным!Это не шутка и не розыгрыш. Все серьезно.
Поэтому вот Вам условие:
Вы просто переводите на мой биткоин кошелек сумму эквивалентную 990 долларам (США) в течении 48-ми часов (ровно 2-е суток).
Отсчет времени начнется сразу, как только вы откроете это письмо, я увижу это.
Найти как купить биткоины Вам труда не составит, поскольку пользоваться поисковиками и браузером вы умеете, это очень хорошо мне видно.Мой btc/кошелек: 19L8H5WZ8Tfk7VJsXapx6SfciitAVU1cJr, 17eMZxX2fohgmGLQ61KupTQeipeU39aypG, 1HPKwTpog8USNA5MpoGuEkb3xDNUC9eY5o
Как только я увижу Вашу транзакцию, я незамедлительно удалю троян с Ваших устройств. Видео же с Вашими "развлечениями" будет уничтожено немедленно.
Это честная сделка.Несколько простых правил:
/Если деньги мне не поступят, то по окончанию двух дней, видео будет транслироваться на бесплатных порн. площадках, а ссылки на него будут у всех, кто Вас хорошо знает!
/Не отвечайте на это письмо, адрес отправителя рандомный.
/Не пытайтесь чистить диск. Файл с видео уже меня.
/Это письмо невозможно отследить, транзкцию биткоин тоже, он анонимный. Все продумано!
/Не вздумайте жаловаться куда-либо. Если я вдруг увижу такую попытку, видео будет распространено в тот же момент!И вот еще совет - заканчивайте бродить по порнушке, да еще такой суровой, вы теряете себя как личность.
Начинайте жить правильно.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is This Is Important Information For You spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion