Avoid infecting your system with malware via fake "HSBC" emails
Phishing/ScamAlso Known As: HSBC spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is HSBC Email Virus?
"HSBC Email Virus" is another spam email campaign similar to ADP Invoice, Barclays Secured Message, Sage Invoice, and many others.
This campaign is designed to distribute a trojan-type virus called TrickBot. The emails essentially state that the a money payment has not been processed and encourages users to open an attached MS Word document for more information. This is a scam - once opened, the attachment stealthily downloads and installs malware.
"HSBC" email virus overview
Firstly, HSBC is one of the largest banks in the world and has nothing to do with this spam campaign. Cyber criminals simply hide behind the name to trick unsuspecting users into opening the attachment.
As mentioned above, the email states that a payment cannot be processed and encourages the user to open the attached document and perform a number of steps to resolve this issue. As mentioned, this is a scam.
Cyber criminals use the names of legitimate companies and governmental agencies, since it is much simpler to trick users into opening files received from people or companies with familiar names (in this case, a large bank). TrickBot is a very dangerous virus.
After system infiltration, it hijacks browsers and modifies visited websites so that entered logins/passwords are sent to a remote server controlled by TrickBot's developers. Therefore, cyber criminals might gain access to users' private accounts, including social networks, banks, and so on.
Cyber criminals aim to generate as much revenue as possible, and so there is a high probability that these people will take advantage of any information obtained. Therefore, the presence of TrickBot malware can lead to serious privacy issues and significant financial loss.
If you have recently opened attachments distributed via an "HSBC Email Virus" spam campaign, you should immediately scan the system with a legitimate anti-virus/anti-spyware suite and eliminate all detected threats.
| Name | HSBC spam |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Detection Names (attachment "Payment Slip.ace") | Combo Cleaner (Gen:Variant.Strictor.265550), Ikarus (Win32.SuspectCrc), Kaspersky (UDS:Trojan-PSW.MSIL.Agensla.gen), Lionic (Trojan.MSIL.Agensla.i!c), Microsoft (Trojan:Win32/Tnega!ml), Full List Of Detections (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Spam-proliferated malware examples
There are many trojan-type viruses that share similarities with TrickBot (including, for example, LokiBot, Emotet, Adwind, and FormBook).
As with HSBC Email Virus, these viruses are also distributed using spam email campaigns. In addition, most trojans are designed to record personal information. Some, however, proliferate other viruses (usually, ransomware). In any case, all pose a direct threat to your privacy and browsing safety.
How did HSBC Email Virus infect my computer?
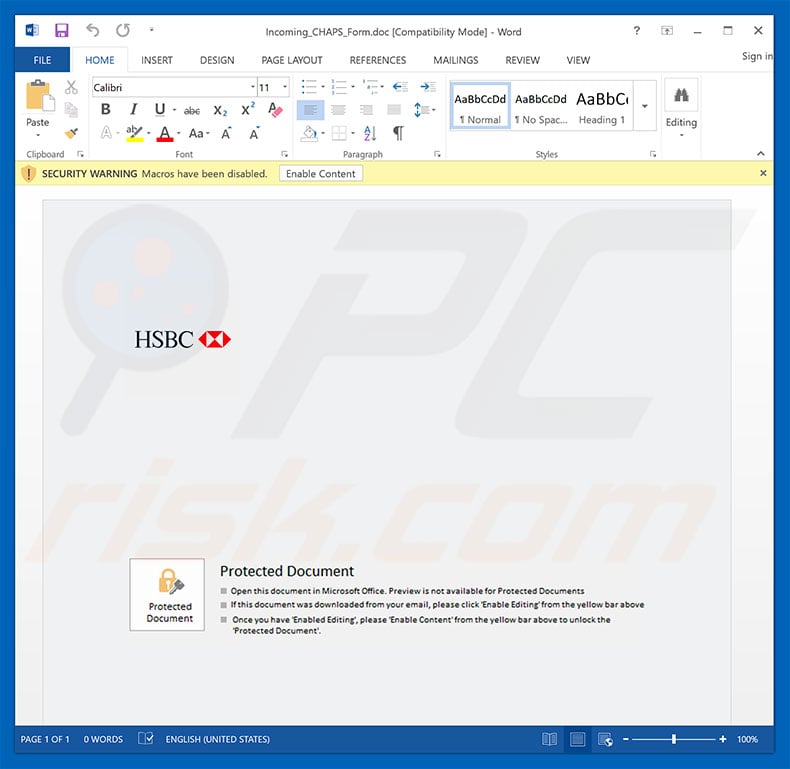
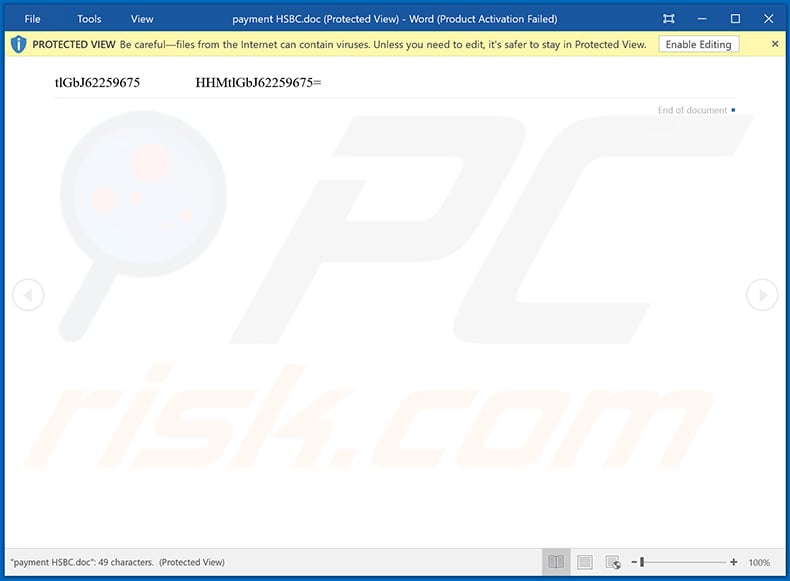
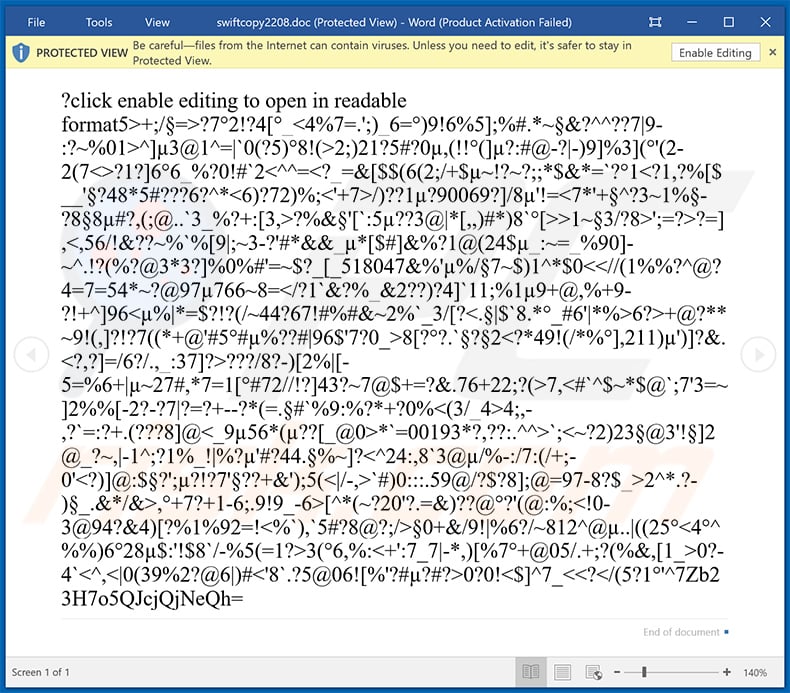
As mentioned above, "HSBC Email Virus" distributes a malicious MS Word document. After opening this file, users are encouraged to enable macro commands (otherwise the content will not be displayed properly), however, this is a trick - by enabling macros, users allow the document to execute commands that stealthily download and install TrickBot.
This distribution method, however, has a major flaw - documents are able to download malware only if the user opens them using the MS Word program. Therefore, if the file is opened using any other app, malware will not be downloaded. Furthermore TrickBot targets the Microsoft Windows Operating System only - if you are using another platform, you are safe.
How to avoid installation of malware?
Lack of knowledge and careless behavior are the main reasons for computer infections - the key to safety is caution. Therefore, it is very important to pay close attention when browsing the Internet. Think twice before opening email attachments. If the file seems irrelevant or has been received from a suspicious email address, it should never be opened.
2010 and newer MS Office versions are developed to open new documents in "Protected View" mode. This prevents download and installation of malware.
Therefore, using old versions is risky. We also strongly recommend that you have a reputable anti-virus/anti-spyware suite installed and running. If you have already opened "HSBC Email Virus" attachment, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
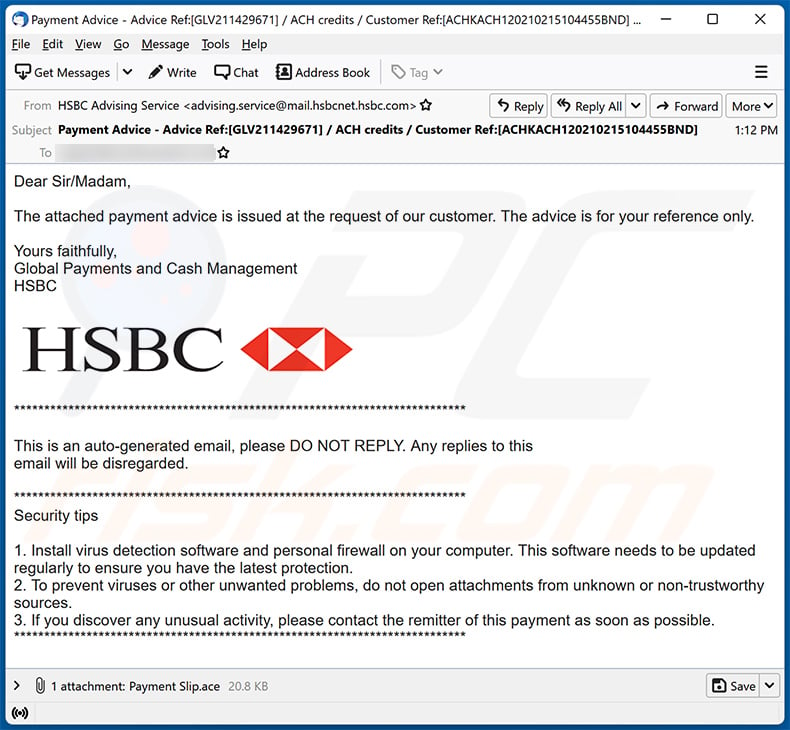
Text presented within this spam email:
Subject: Payment Advice - Advice Ref:[GLV211429671] / ACH credits / Customer Ref:[ACHKACH120210215104455BND]
Dear Sir/Madam,The attached payment advice is issued at the request of our customer. The advice is for your reference only.
Yours faithfully,
Global Payments and Cash Management
HSBC***********************************
This is an auto-generated email, please DO NOT REPLY. Any replies to this
email will be disregarded.***********************************
Security tips1. Install virus detection software and personal firewall on your computer. This software needs to be updated regularly to ensure you have the latest protection.
2. To prevent viruses or other unwanted problems, do not open attachments from unknown or non-trustworthy sources.
3. If you discover any unusual activity, please contact the remitter of this payment as soon as possible.
***********************************
Example of HSBC-themed spam email:
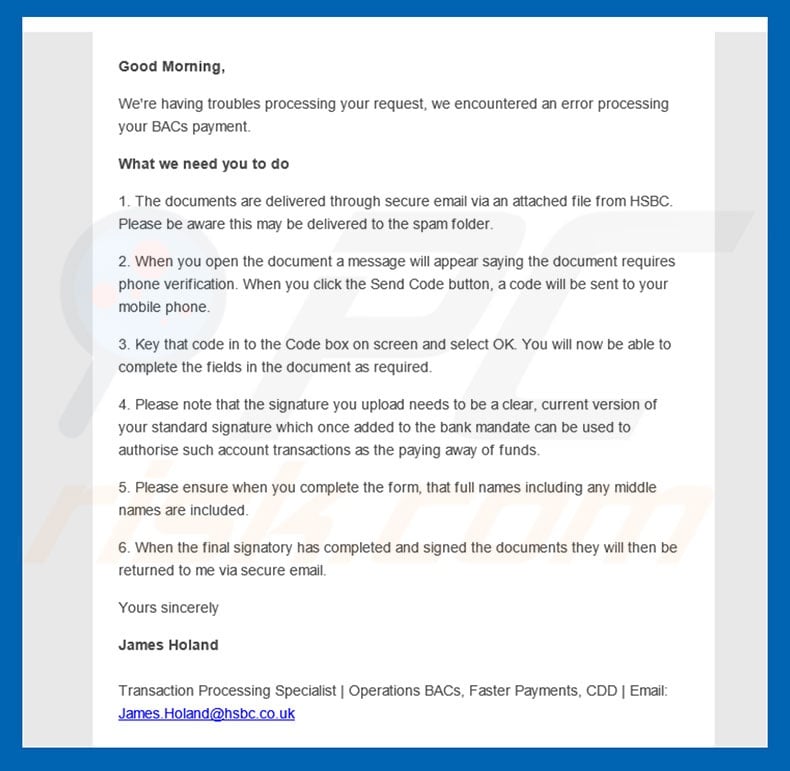
Text presented in the "HSBC Email Virus" email message:
Subject: Important : Troubles processing BACs payment
Good Morning,
We’re having troubles processing your request, we encountered an error processing your BACs payment.
What we need you to do
1. The documents are delivered through secure email via an attached file from HSBC. Please be aware this may be delivered to the spam folder.
2. When you open the document a message will appear saying the document requires phone verification. When you click the Send Code button, a code will be sent to your mobile phone.
3. Key that code in to the Code box on screen and select OK. You will now be able to complete the fields in the document as required.
4. Please note that the signature you upload needs to be a clear, current version of your standard signature which once added to the bank mandate can be used to authorise such account transactions as the paying away of funds.
5. Please ensure when you complete the form, that full names including any middle names are included.
6. When the final signatory has completed and signed the documents they will then be returned to me via secure email.
Yours sincerely
James Holand
Transaction Processing Specialist | Operations BACs, Faster Payments, CDD | Email: James.Holand@hsbc.co.uk
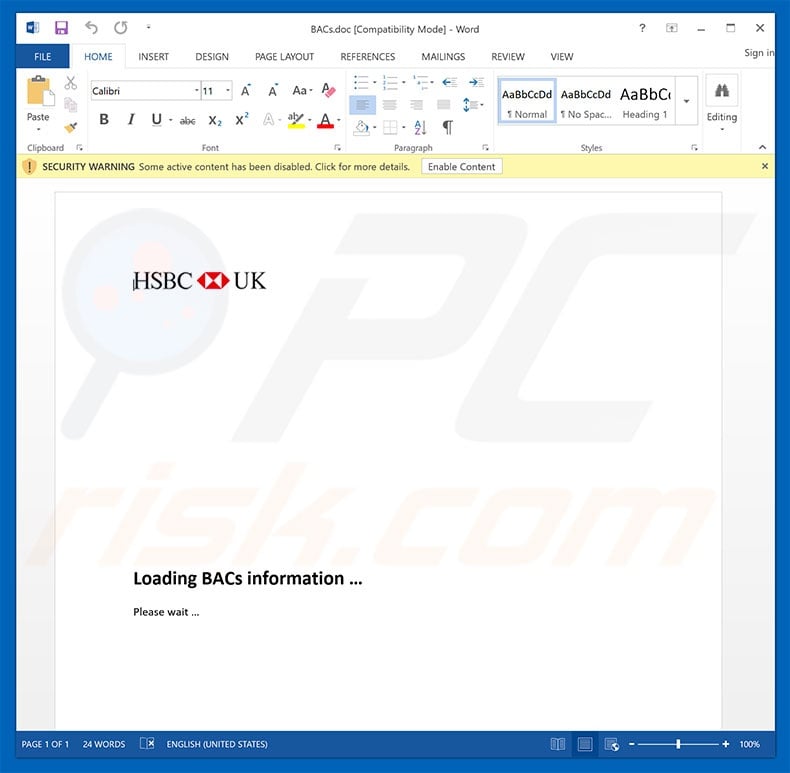
Malicious attachment distributed via "HSBC Email Virus" spam campaign:
Second variant of "HSBC Email Virus":
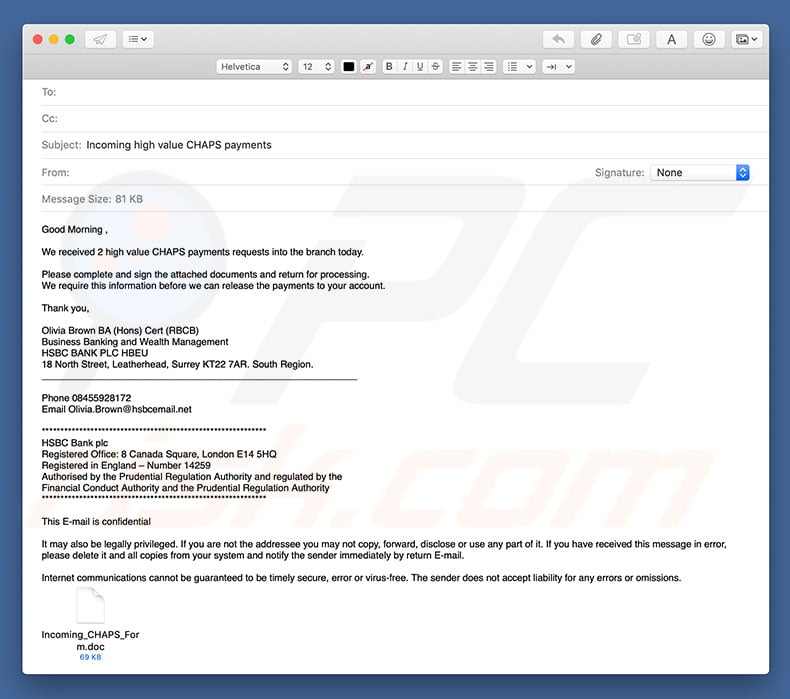
Text presented within this email:
Subject: Incoming high value CHAPS payments
Good Morning ,
We received 2 high value CHAPS payments requests into the branch today.
Please complete and sign the attached documents and return for processing.
We require this information before we can release the payments to your account.
Thank you,
Olivia Brown BA (Hons) Cert (RBCB)
Business Banking and Wealth Management
HSBC BANK PLC HBEU
18 North Street, Leatherhead, Surrey KT22 7AR. South Region.
___________________________________________________________
Phone 08455928172
Email Olivia.Brown@hsbcemail.net
************************************************************
HSBC Bank plc
Registered Office: 8 Canada Square, London E14 5HQ
Registered in England – Number 14259
Authorised by the Prudential Regulation Authority and regulated by the
Financial Conduct Authority and the Prudential Regulation Authority
************************************************************
This E-mail is confidential
It may also be legally privileged. If you are not the addressee you may not copy, forward, disclose or use any part of it. If you have received this message in error, please delete it and all copies from your system and notify the sender immediately by return E-mail.
Internet communications cannot be guaranteed to be timely secure, error or virus-free. The sender does not accept liability for any errors or omissions.
Screenshot of the malicious attachment proliferated using the second variant of "HSBC Email Virus":
Third variant of "HSBC Email Virus":
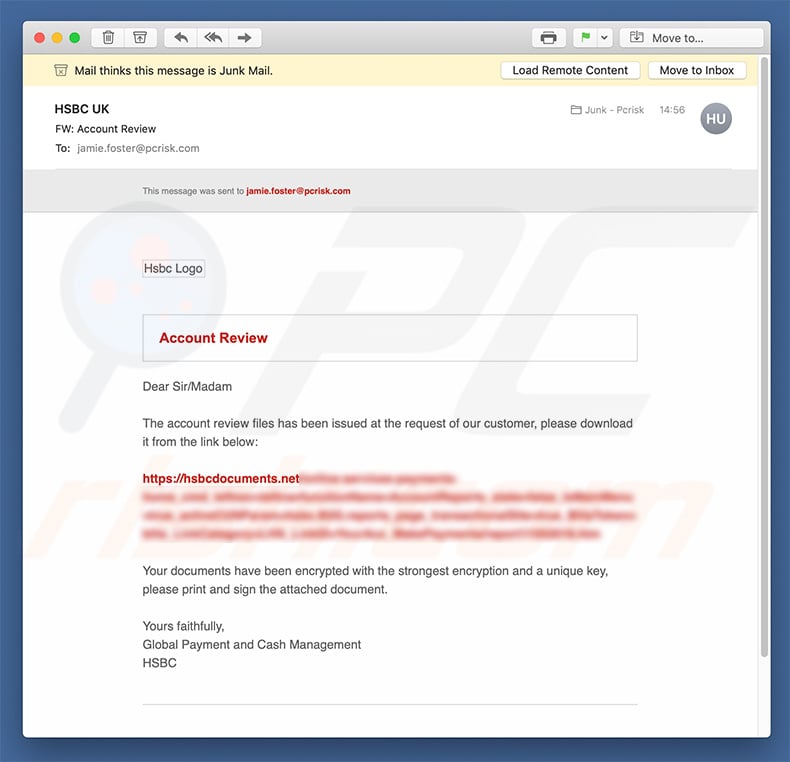
Text presented within this email:
Subject: Account Review
Account Review
Dear Sir/MadamThe account review files has been issued at the request of our customer, please download it from the link below:
hxxps://hsbcdocuments.net/.............
Your documents have been encrypted with the strongest encryption and a unique key, please print and sign the attached document.
Yours faithfully,
Global Payment and Cash Management
HSBC
Screenshot of the malicious attachment proliferated using the third variant of "HSBC Email Virus":
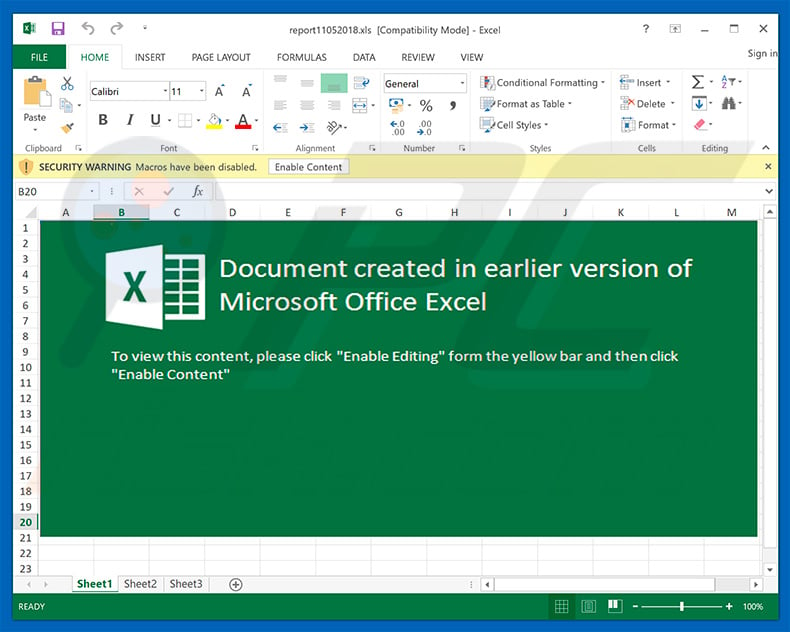
Yet another variant of HSBC email spam campaign:
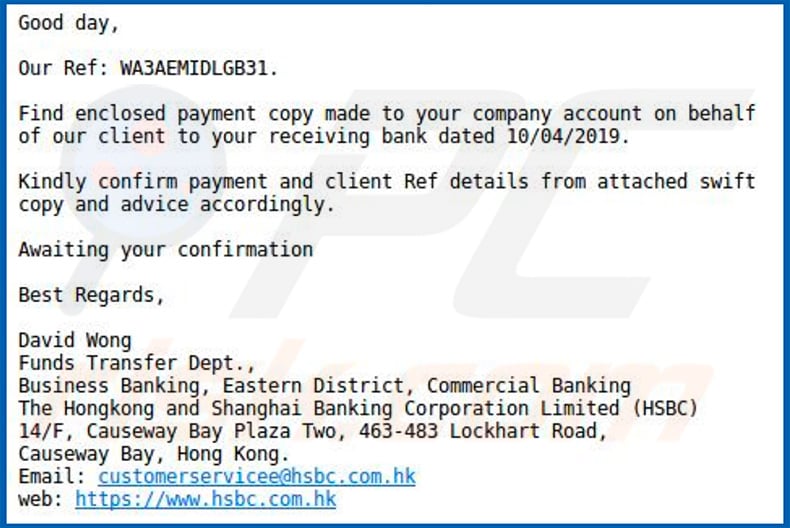
Text presented within this email:
Good day, Our Ref: WA3AEMIDLGB31.
Find enclosed payment copy made to your company account on behalf of our client to your receiving bank dated 10/04/2019. Kindly confirm payment and client Ref details from attache' swift copy and advice accordingly.
Awaiting your confirmation
Best Regards,
David Wong Funds Transfer Dept., Business Banking, Eastern District, Commercial Banking The Hongkong and Shanghai Banking Corporation Limited (1-1SBC 14/F, Causeway Bay Plaza Two, 463-483 Lockhart Road, Causeway Bay, Hong Kong. Email: customerserviceeOhsbcpcom.hk web: hxxps://www.hsbc.com.hk
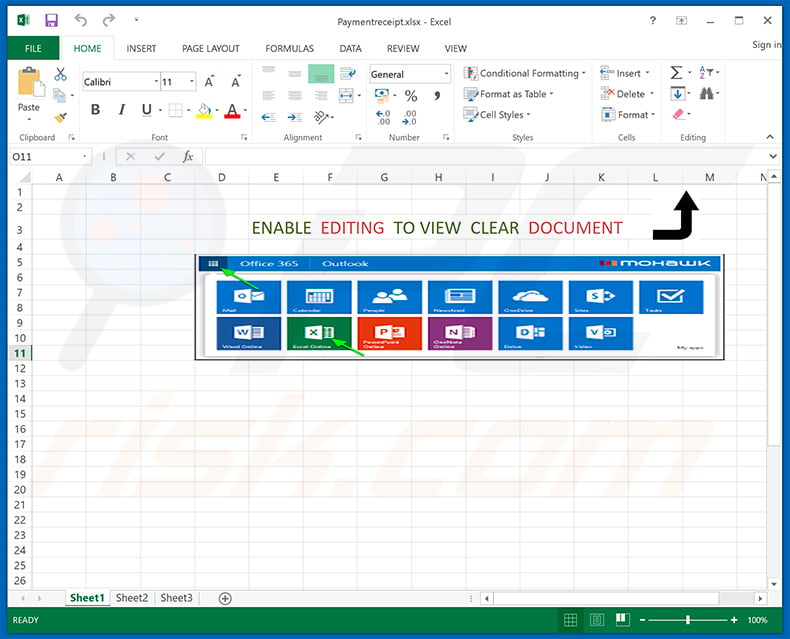
Screenshot of the malicious Microsoft Excel attachment ("Paymentreceipt.xlsx"):
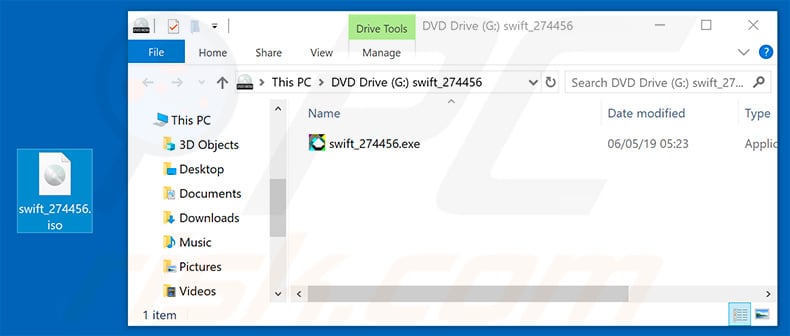
Yet another variant of "HSBC" email spam campaign. This variant distributes NanoCore remote access trojan and the attachment is "swift_274456.iso", which contains "swift_274456.exe" file.
Screenshot of deceptive email:
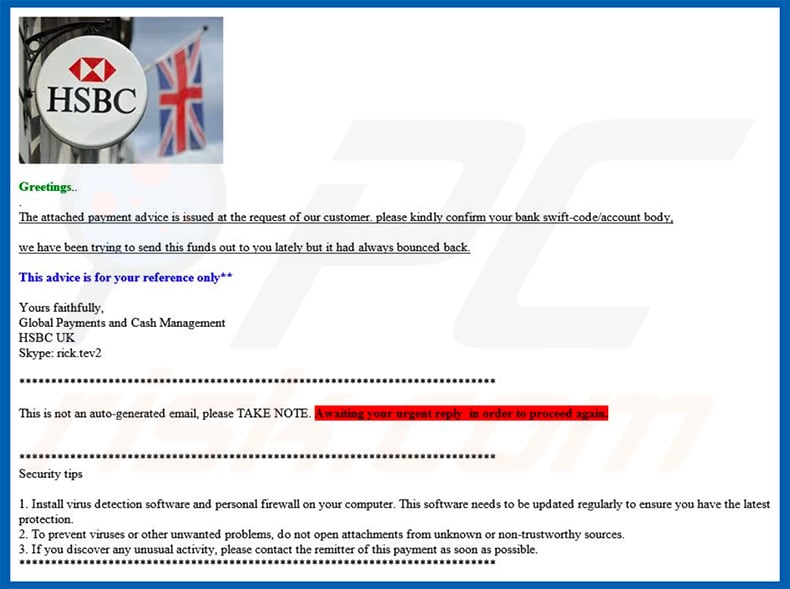
Text presented within this email:
Greetings.. The attached payment advice is issued at the request of our customer. please kindly confirm your bank swift-code/account body,
we have been trying to send this funds out to you lately but it had always bounced back.
This advice is for your reference only**
Yours faithfully,Global Payments and Cash Management
HSBC UK
Skype: rick.tev2
This is not an auto-generated email, please TAKE NOTE. Awaiting your urgent reply in order to proceed again.
Security tips1. Install virus detection software and personal firewall on your computer. This software needs to be updated regularly to ensure you have the latest protection.
2. To prevent viruses or other unwanted problems, do not open attachments from unknown or non-trustworthy sources.
3. If you discover any unusual activity, please contact the remitter of this payment as soon as possible.
Screenshot of the malicious attachment:
Update September 12, 2019 - Cyber criminals have recently started using "HSBC" email spam campaign to spread Agent Tesla remote access tool (RAT) and LokiBot trojan:
Example of "HSBC" spam email spreading Agent Tesla:
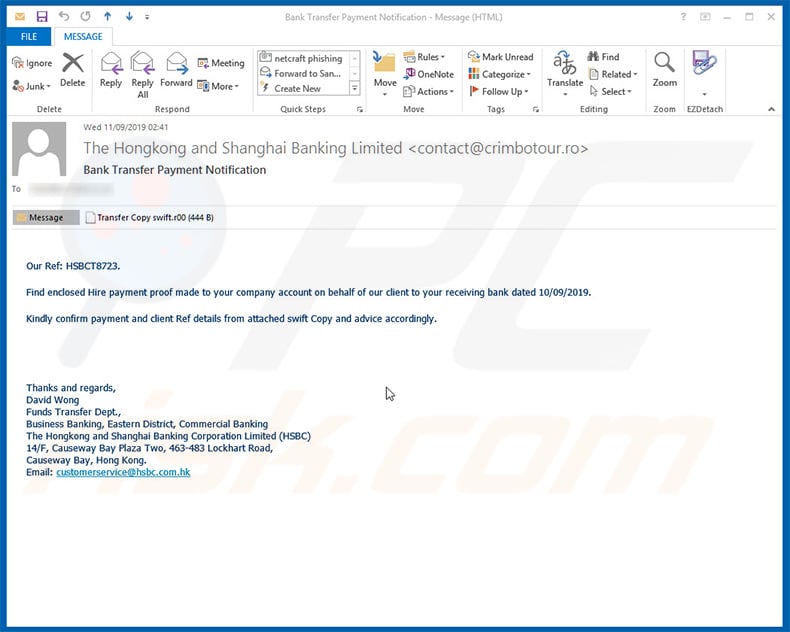
Text presented within this email:
Subject: Bank Transfer Payment Notification
Attachment: Transfer Copy swift.r00
Our Ref: HSBCT8723.Find enclosed Hire payment proof made to your company account on behalf of our client to your receiving bank dated 10/09/2019.
Kindly confirm payment and client Ref details from attached swift Copy and advice accordingly.
Thanks and regards,
David Wong
Funds Transfer Dept.,
Business Banking, Eastern District, Commercial Banking
The Hongkong and Shanghai Banking Corporation Limited (HSBC)
14/F, Causeway Bay Plaza Two, 463-483 Lockhart Road,
Causeway Bay, Hong Kong.
Email: customerservice@hsbc.com.hk
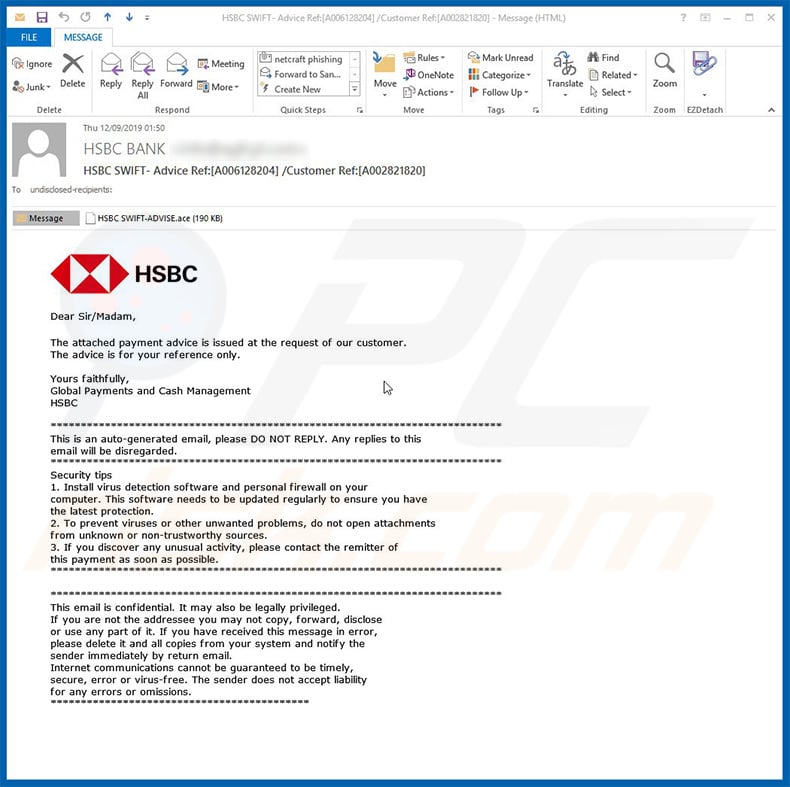
Example of "HSBC" spam email spreading LokiBot:
Text presented within this email:
Subject: HSBC SWIFT - Advice Ref:[A006128204]/Customer Ref:[A002821820]
Attachment: HSBC SWIFT-ADVISE.ace
Dear Sir/Madam,
The attached payment advice is issued at the request of our customer.
The advice is for your reference only.Yours faithfully,
Global Payments and Cash Management
HSBC***************
This is an auto-generated email, please DO NOT REPLY. Any replies to this email will be disregarded.
***************
Security tips
1. Install virus detection software and personal firewall on your computer. This software needs to be updated regularly to ensure you have the latest protection.
2. To prevent viruses or other unwanted problems, do not open attachments from unknown or non-trustworthy sources.
3. If you discover any unusual activity, please contact the remitter of this payment as soon as possible.
******************************
This email is confidential. It may also be legally privileged.
If you are not the addressee you may not copy, forward, disclose or use any part of it. If you have received this message in error, please delete it and all copies from your system and notify the sender immediately by return email.
Internet communications cannot be guaranteed to be timely, secure or virus-free. The sender does not accept liability for any errors or omissions.
***************
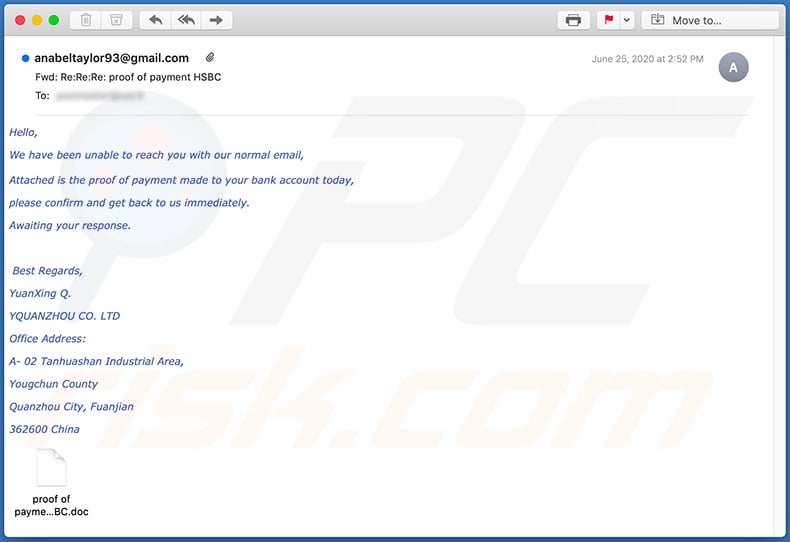
Appearance of yet another HSBC-themed spam email which distributes TrickBot malware:
Text presented within:
Subject: Fwd: Re:Re:Re: proof of payment HSBC
Hello,
We have been unable to reach you with our normal email,
Attached is the proof of payment made to your bank account today,
please confirm and get back to us immediately.
Awaiting your response.
Best Regards,
YuanXing Q.
YQUANZHOU CO. LTD
Office Address:
A- 02 Tanhuashan Industrial Area,
Yougchun County
Quanzhou City, Fuanjian
362600 China
Appearance of the malicious MS Word document attached to this email (GIF):

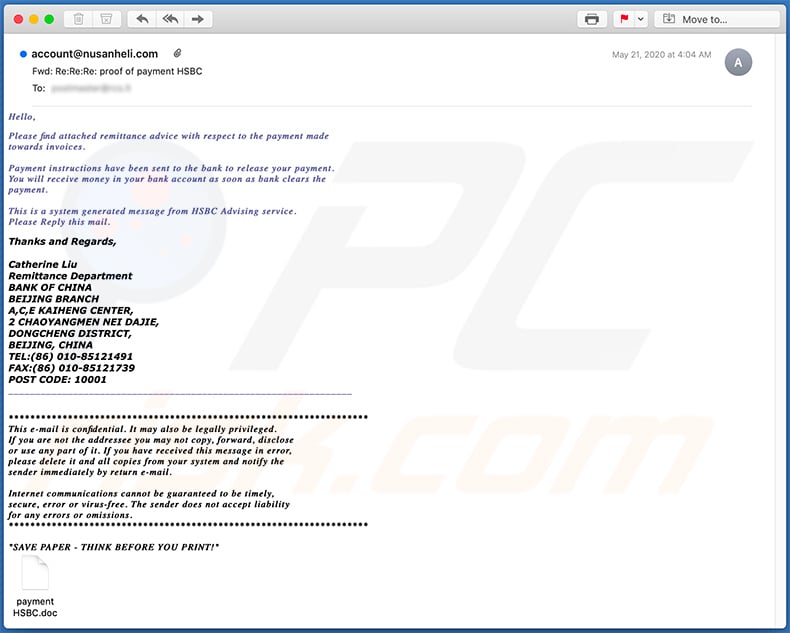
Yet another HSBC-themed spam email distributing a malicious attachment (MS Word document):
Text presented within:
Subject: Fwd: Re:Re:Re: proof of payment HSBC
Hello,
Please find attached remittance advice with respect to the payment made
towards invoices.
Payment instructions have been sent to the bank to release your payment.
You will receive money in your bank account as soon as bank clears the
payment.
This is a system generated message from HSBC Advising service.
Please Reply this mail.
Thanks and Regards,Catherine Liu
Remittance Department
BANK OF CHINA
BEIJING BRANCH
A,C,E KAIHENG CENTER,
2 CHAOYANGMEN NEI DAJIE,
DONGCHENG DISTRICT,
BEIJING, CHINA
TEL:(86) 010-85121491
FAX:(86) 010-85121739
POST CODE: 10001
________
*********
This e-mail is confidential. It may also be legally privileged.
If you are not the addressee you may not copy, forward, disclose
or use any part of it. If you have received this message in error,
please delete it and all copies from your system and notify the
sender immediately by return e-mail.
Internet communications cannot be guaranteed to be timely,
secure, error or virus-free. The sender does not accept liability
for any errors or omissions.
*********
"SAVE PAPER - THINK BEFORE YOU PRINT!"
Screenshot of the attached MS Word document:
A Norwegian version of HSBC-themed spam email used to spread Agent Tesla RAT. The attachment is a .img file which contains a malicious executable:
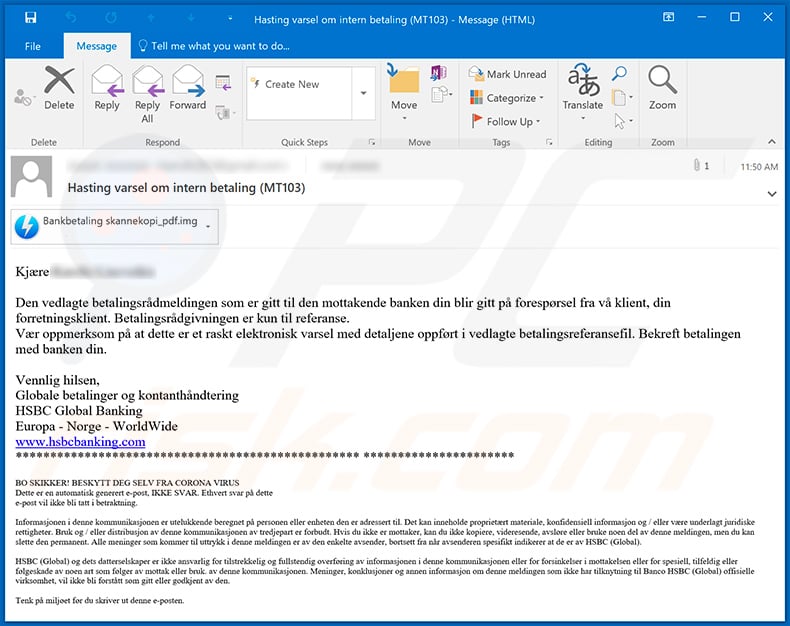
Text presented within:
Subject: Hasting varsel om intern betaling (MT103)
Kjære -
Den vedlagte betalingsrådmeldingen som er gitt til den mottakende banken din blir gitt på forespørsel fra vå klient, din forretningsklient. Betalingsrådgivningen er kun til referanse.
Vær oppmerksom på at dette er et raskt elektronisk varsel med detaljene oppført i vedlagte betalingsreferansefil. Bekreft betalingen med banken din.Vennlig hilsen,
Globale betalinger og kontanthåndtering
HSBC Global Banking
Europa - Norge - WorldWide
www.hsbcbanking.com
************************************************** **********************BO SKIKKER! BESKYTT DEG SELV FRA CORONA VIRUS
Dette er en automatisk generert e-post, IKKE SVAR. Ethvert svar på dette
e-post vil ikke bli tatt i betraktning.Informasjonen i denne kommunikasjonen er utelukkende beregnet på personen eller enheten den er adressert til. Det kan inneholde proprietært materiale, konfidensiell informasjon og / eller væere underlagt juridiske rettigheter. Bruk og / eller distribusjon av denne kommunikasjonen av tredjepart er forbudt. Hvis du ikke er mottaker, kan du ikke kopiere, videresende, avsløre eller bruke noen del av denne meldingen, men du kan slette den permanent. Alle meninger som kommer til uttrykk i denne meldingen er av den enkelte avsender, bortsett fra når avsenderen spesifikt indikerer at de er av HSBC (Global).
HSBC (Global) og dets datterselskaper er ikke ansvarlig for tilstrekkelig og fullstendig overføring av informasjonen i denne kommunikasjonen eller for forsinkelser i mottakelsen eller for spesiell, tilfeldig eller følgeskade av noen art som følger av mottak eller bruk. av denne kommunikasjonen. Meninger, konklusjoner og annen informasjon om denne meldingen som ikke har tilknytning til Banco HSBC (Global) offisielle virksomhet, vil ikke bli forstått som gitt eller godkjent av den.
Tenk på miljøet før du skriver ut denne e-posten.
Another HSBC-themed spam email used to spread Agent Tesla RAT (the attached archive contains a malicious executable):
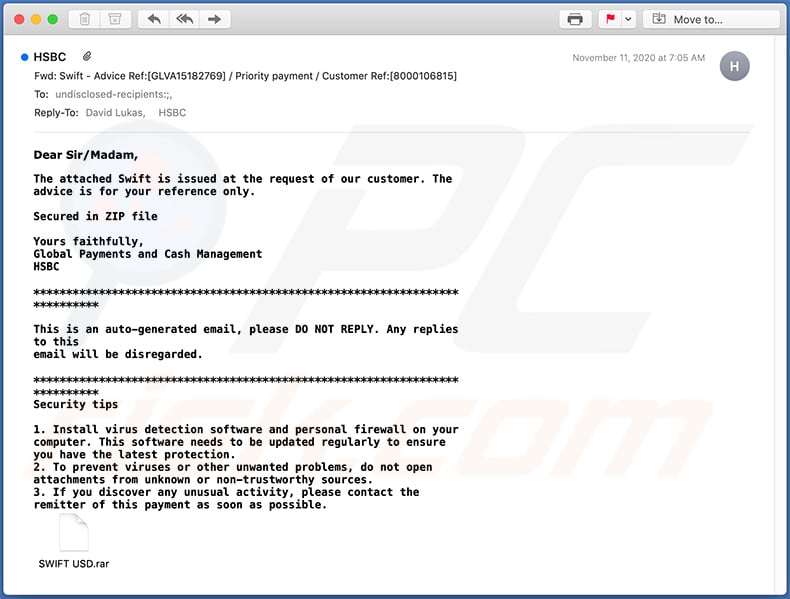
Text presented within:
Subject: Fwd: Swift - Advice Ref:[GLVA15182769] / Priority payment / Customer Ref:[8000106815]
Dear Sir/Madam,
The attached Swift is issued at the request of our customer. The
advice is for your reference only.Secured in ZIP file
Yours faithfully,
Global Payments and Cash Management
HSBC****************
This is an auto-generated email, please DO NOT REPLY. Any replies
to this
email will be disregarded.****************
Security tips
1. Install virus detection software and personal firewall on your
computer. This software needs to be updated regularly to ensure
you have the latest protection.
2. To prevent viruses or other unwanted problems, do not open
attachments from unknown or non-trustworthy sources.
3. If you discover any unusual activity, please contact the
remitter of this payment as soon as possible.
An example of HSBC-themed spam email promoting a phishing site:
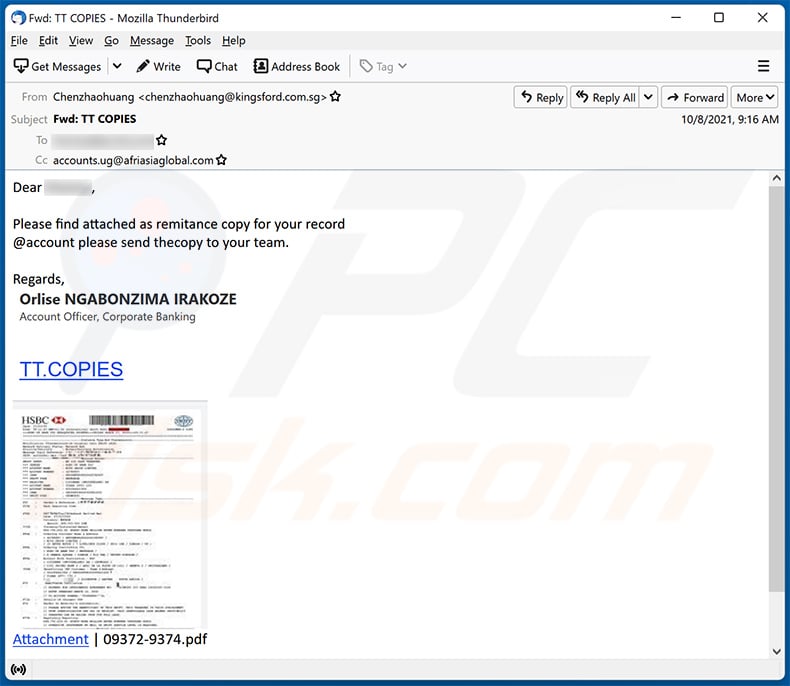
Text presented within:
Subject: Fwd: TT COPIES
Dear -,
Please find attached as remitance copy for your record
@account please send thecopy to your team.Regards,
Orlise NGABONZIMA IRAKOZE
Account Officer, Corporate BankingTT.COPIES
Attachment | 09372-9374.pdf
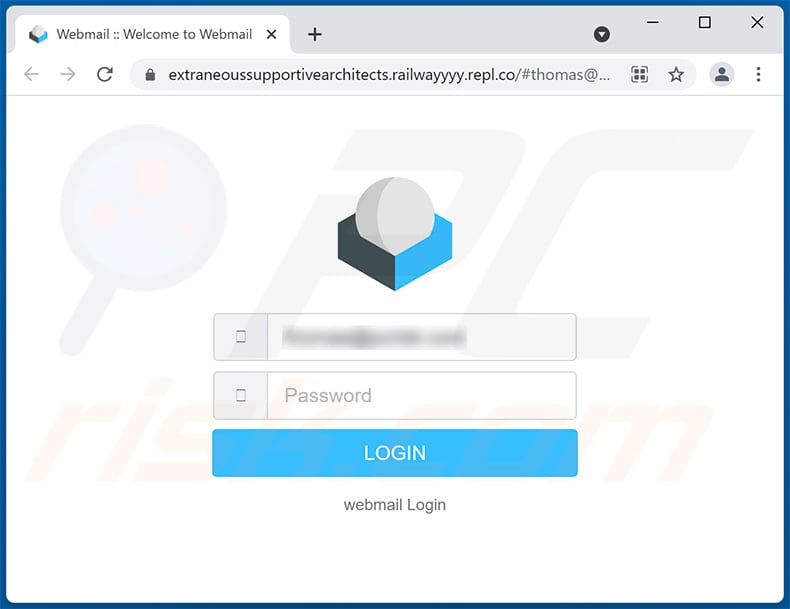
Screenshot of the promoted phishing site:
Yet another example of HSBC-themed spam email spreading the LokiBot malware:
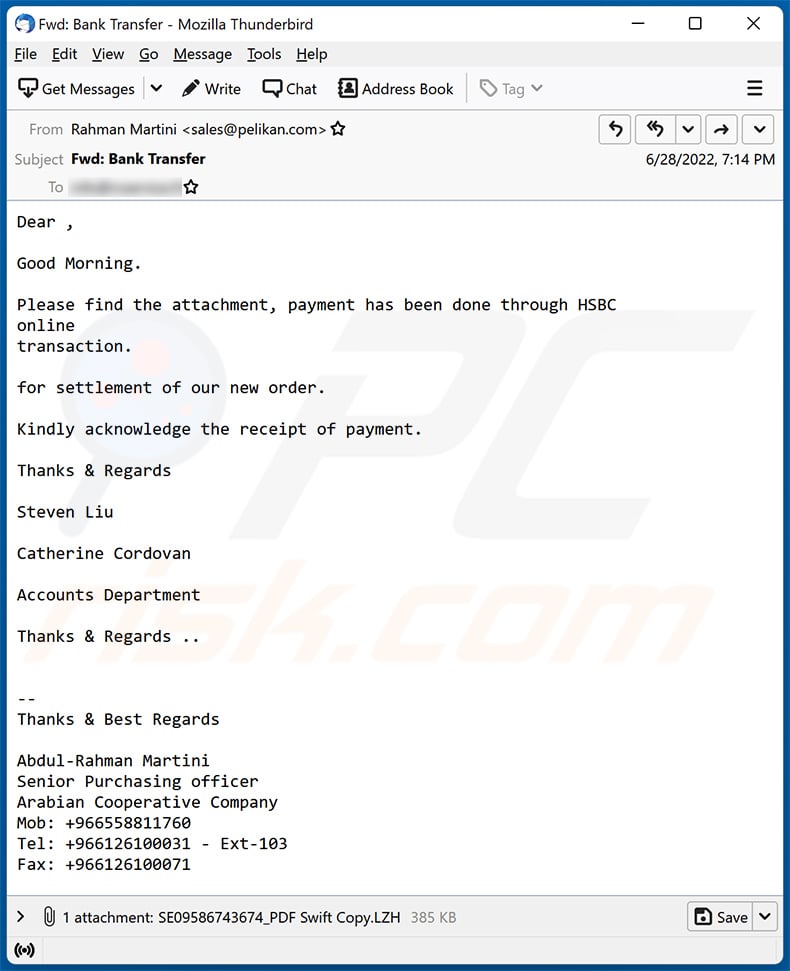
Text presented within:
Subject: Fwd: Bank Transfer
Dear ,
Good Morning.
Please find the attachment, payment has been done through HSBC
online
transaction.for settlement of our new order.
Kindly acknowledge the receipt of payment.
Thanks & Regards
Steven Liu
Catherine Cordovan
Accounts Department
Thanks & Regards ..
--
Thanks & Best RegardsAbdul-Rahman Martini
Senior Purchasing officer
Arabian Cooperative Company
Mob: +966558811760
Tel: +966126100031 - Ext-103
Fax: +966126100071
Yet another example of HSBC-themed spam email spreading a malicious MS Word document used to inject Agent Tesla malware into the system:
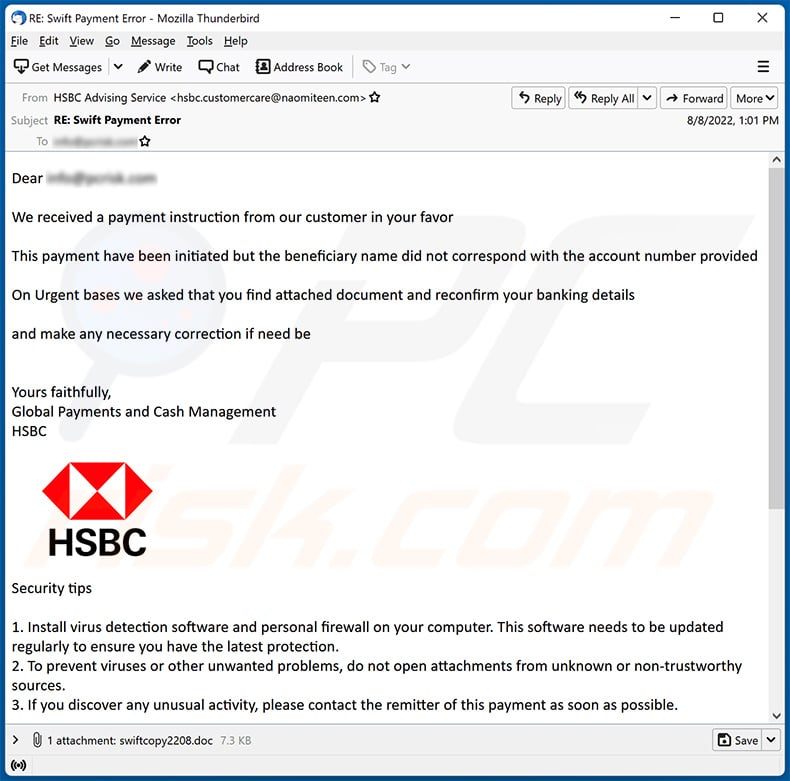
Text presented within:
Subject: RE: Swift Payment Error
Dear ********
We received a payment instruction from our customer in your favor
This payment have been initiated but the beneficiary name did not correspond with the account number provided
On Urgent bases we asked that you find attached document and reconfirm your banking details
and make any necessary correction if need be
Yours faithfully,
Global Payments and Cash Management
HSBCSecurity tips
1. Install virus detection software and personal firewall on your computer. This software needs to be updated regularly to ensure you have the latest protection.
2. To prevent viruses or other unwanted problems, do not open attachments from unknown or non-trustworthy sources.
3. If you discover any unusual activity, please contact the remitter of this payment as soon as possible.
This e-mail is confidential. It may also be legally privileged.
If you are not the addressee you may not copy, forward, disclose
or use any part of it. If you have received this message in error,
please delete it and all copies from your system and notify the
sender immediately by return e-mail.Internet communications cannot be guaranteed to be timely,
secure, error or virus-free. The sender does not accept liability
for any errors or omissions.
*******************************************************************
"SAVE PAPER - THINK BEFORE YOU PRINT!"
Screenshot of the attached MS Word document:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is HSBC spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal. Hence, thousands of users receive the same email letter. Cyber criminals distribute them hoping at least some recipients will fall for their scam.
I have read the "HSBC" spam email but didn't open the attachment, is my computer infected?
No, reading a spam email will not trigger any infection processes. Malware download/installation is jumpstarted when the files attached to or links included in the scam email - are opened/clicked.
I have downloaded and opened the file attached to the "HSBC" spam email, is my computer infected?
Whether your device was infected depends on the file's format. If it was an executable - most likely - yes. However, if it was a document (e.g., .pdf, .doc, etc.), you might have avoided a system infection. These formats can require additional user interaction (e.g., macro command enablement) to begin downloading/installing malicious programs.
My computer is infected with TrickBot malware, should I format my storage device to get rid of it?
No, such drastic measures are unnecessary for TrickBot's removal.
What are the biggest issues that malware can cause?
What threats a malicious program poses depends on its abilities and the cyber criminals' modus operandi. TrickBot primarily operates as an information-stealing and screen-locking malware; hence, its infections can lead to serious privacy issues, identity theft, financial losses, and permanent data loss.
What is the purpose of malware?
Most malicious programs are released with the goal of generating revenue. Other potential reasoning includes: cyber criminals' amusement, personal motivation (i.e., malware leveraged against specific victims), political or geopolitical reasons, process (e.g., website, service, company, etc.) distribution, and so on.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner can detect and eliminate almost all of the known malware infections. However, performing a complete system scan is paramount - since sophisticated malicious software usually hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion