LockBit (.lockbit) Mac ransomware virus – removal and decryption options
RansomwareAlso Known As: LockBit virus
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is LockBit ransomware?
LockBit is the name of a ransomware targeting Mac Operating Systems (OSes). It is associated with the LockBit ransomware gang – the developers of LockBit, LockBit 2.0, LockBit 3.0, and various other variants. The aforementioned malware target Windows, Linux, and VMware ESXi servers.
At the time of writing, LockBit (Mac) is the first known ransomware for MacOS developed by a large cybercriminal gang. However, the sample we have researched is still in development and has been released for testing.
Typically, ransomware operates by encrypting victims' files in order to demand payment for decryption. This LockBit version is highly unlikely to carry out its purpose. Firstly, its invalid signature is detected as untrusted by OSes, and the ransomware tends to crash upon manual execution. Although, it must be mentioned that potential future variants may be capable of successfully encrypting Mac devices.
LockBit ransomware overview
The researched variant of LockBit targets devices running on Apple Silicon, but it can be launched on older versions as well. According to the analysis undertaken by Objective-See, LockBit's uses the Linux version's code compiled for Mac. It also contains artifacts of the ransomware's Windows variants, which are wholly irrelevant to Mac OSes.
Based on this malicious program being the first Mac ransomware from a large ransomware gang and its flawed design – it is evident that this LockBit version was released for testing purposes.
Even the ransom note ("!!!-Restore-My-Files-!!!.txt") created by a successful execution of this malware – contains generic text that would be appropriate for ransomware targeting companies and able to exfiltrate data (for double extortion purposes), which this variant is incapable of doing.
This ransomware currently poses little to no threat for Mac users. The Mac operating systems detect the malware's invalid signature and display warnings or are simply incapable of opening the infectious file.
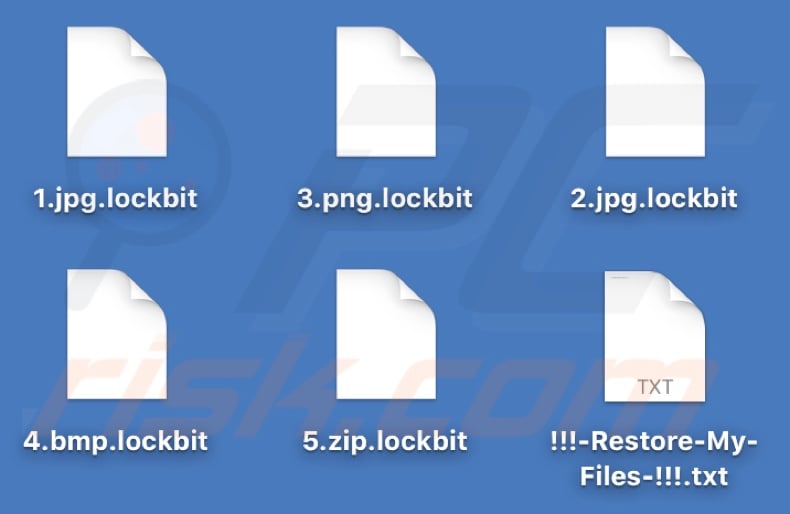
It could be possible for users to manually execute the file and thus trigger LockBit's encryption process, which would result in data encryption and append the filenames of affected files with a ".lockbit" extension (e.g., "1.jpg" would appear as "1.jpg.lockbit", "3.png" as "3.png.lockbit", etc.). However, during our analysis and in the research efforts undertaken by other analysts, the ransomware typically crashed due to its flawed code.
Therefore, while it could successfully encrypt data – that is unlikely to be the case in its current iteration. Although, the serious flaws of this variant may be rectified in future releases, meaning that the later versions could be capable of encrypting victims' devices.
Well-designed ransomware is highly dangerous. Files encrypted by such malware cannot be decrypted without the attackers' interference. However, meeting the ransom demands is strongly advised against, as data recovery is not guaranteed (cyber criminals often do not send the decryption keys/software), and paying also supports this illegal activity.
The general advice for ensuring data safety is to keep backups in multiple different locations (e.g., remote servers, unplugged storage devices, etc.).
| Name | LockBit virus |
| Threat Type | Mac malware, Mac virus, Ransomware, Crypto Virus, Files locker |
| Encrypted Files Extension | .lockbit |
| Ransom Demanding Message | !!!-Restore-My-Files-!!!.txt |
| Free Decryptor Available? | No (check out No More Ransom project website) |
| Cyber Criminal Contact | Tor network websites |
| Detection Names | Avast (Multi:Filecoder-X [Ransom]), Ikarus (Win32.Outbreak), Kaspersky (HEUR:Trojan-Ransom.OSX.Agent.gen), TrendMicro ( Ransom.MacOS.LOCKBIT.YXDDPZ), ZoneAlarm by Check Point (HEUR:Trojan-Ransom.OSX.Agent.gen), Full List Of Detections (VirusTotal) |
| Symptoms | Cannot open files stored on your computer, previously functional files now have a different extension (for example, 1.jpg.locked). A ransom demand message is displayed on your desktop. Cyber criminals demand payment of a ransom (usually in bitcoins) to unlock your files. |
| Distribution Methods | Infected email attachments, torrent websites, malicious ads. |
| Damage | All files are encrypted and cannot be opened without paying a ransom. Additional password-stealing trojans and malware infections can be installed together with a ransomware infection. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Mac malware examples
We have analyzed countless malicious programs targeting Mac OSes; MacStealer, GIMMICK, DazzleSpy, SysJoker – are merely a few examples, and EvilQuest is a Mac-specific ransomware.
Malware can have a wide variety of purposes, ranging from file encryption to data theft. While ransomware operates practically the same throughout (i.e., encrypts data and demands payment), these programs have two significant differences in-between. They can use different cryptographic algorithms (symmetric or asymmetric) and demand ransoms of varied sizes.
However, regardless of how malicious software operates – its presence on a system endangers device integrity and user safety. Therefore, all threats must be removed immediately upon detection.
How did ransomware infect my computer?
Malware is primarily distributed using phishing and social engineering tactics. It is commonly disguised as or bundled with regular programs/media. Virulent files can be in various formats and infect devices upon being opened.
The most widely used proliferation methods include: drive-by (stealthy/deceptive) downloads, malicious attachments or links in spam emails/messages, online scams, dubious download sources (e.g., freeware and free file-hosting websites, Peer-to-Peer sharing networks, etc.), pirated software and illegal program activation ("cracking") tools, and fake updates.
How to protect yourself from ransomware infections?
We highly recommend exercising caution while browsing since fraudulent and malicious online content usually appears legitimate and harmless. The same vigilance must be extended to incoming emails and other messages. The attachments or links found in suspicious/irrelevant mail must not be opened, as they can be infectious.
Additionally, all downloads must be performed from official and verified channels. It is just as important to activate and update software using genuine functions/tools, as those acquired from third-party sources may contain malware.
We must stress that having a reputable anti-virus installed and kept updated is essential to device/user safety. Security programs must be used to run regular system scans and to remove detected threats. If your computer is already infected with LockBit, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate this ransomware.
Screenshot of LockBit ransomware's ransom note ("!!!-Restore-My-Files-!!!.txt"):
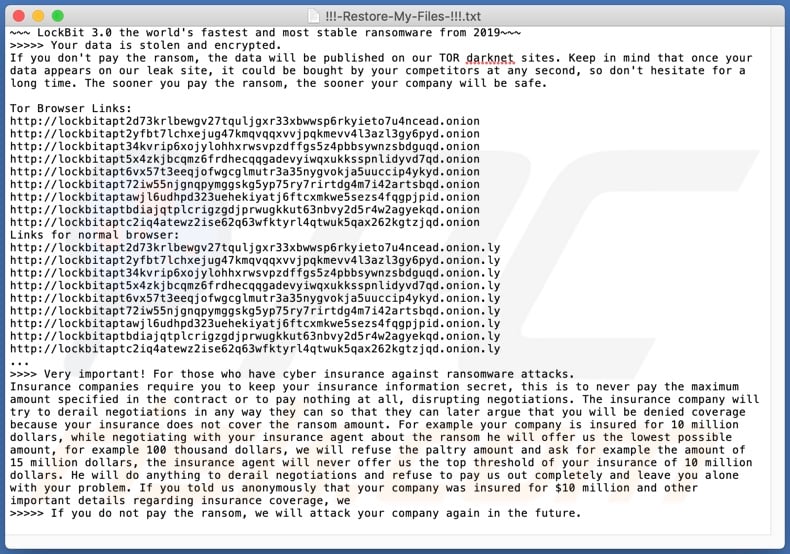
Text presented in this message:
~~~ LockBit 3.0 the world's fastest and most stable ransomware from 2019~~~
>>>>> Your data is stolen and encrypted.
If you don't pay the ransom, the data will be published on our TOR darknet sites. Keep in mind that once your data appears on our leak site, it could be bought by your competitors at any second, so don't hesitate for a long time. The sooner you pay the ransom, the sooner your company will be safe.
Tor Browser Links:
-
Links for normal browser:
-
...
>>>> Very important! For those who have cyber insurance against ransomware attacks.
Insurance companies require you to keep your insurance information secret, this is to never pay the maximum amount specified in the contract or to pay nothing at all, disrupting negotiations. The insurance company will try to derail negotiations in any way they can so that they can later argue that you will be denied coverage because your insurance does not cover the ransom amount. For example your company is insured for 10 million dollars, while negotiating with your insurance agent about the ransom he will offer us the lowest possible amount, for example 100 thousand dollars, we will refuse the paltry amount and ask for example the amount of 15 million dollars, the insurance agent will never offer us the top threshold of your insurance of 10 million dollars. He will do anything to derail negotiations and refuse to pay us out completely and leave you alone with your problem. If you told us anonymously that your company was insured for $10 million and other important details regarding insurance coverage, we
>>>>> If you do not pay the ransom, we will attack your company again in the future.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "LockBit"?
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
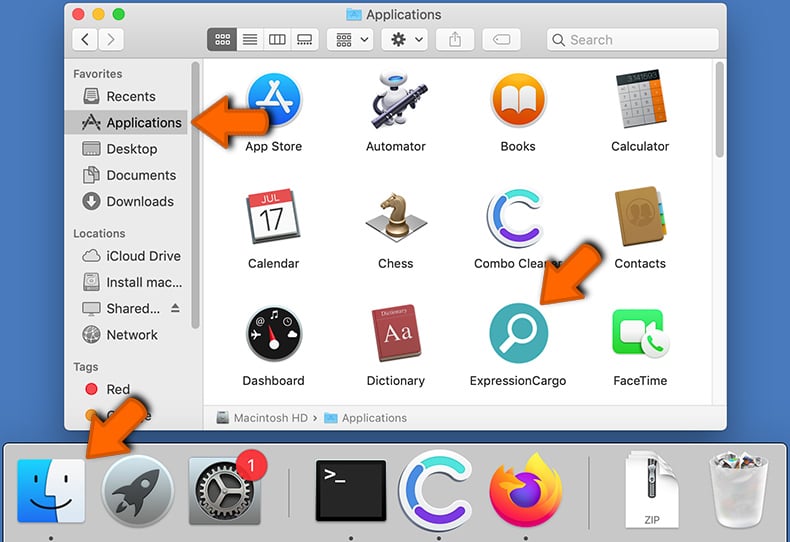
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware-related files and folders
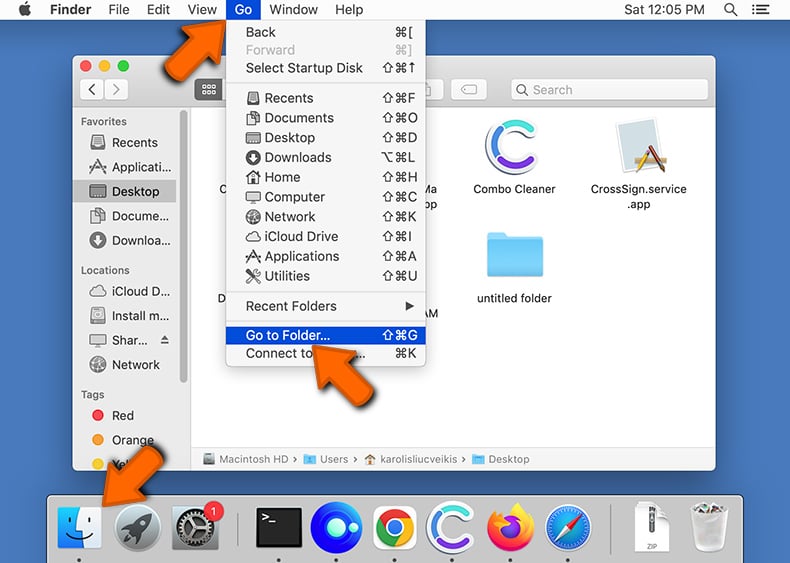
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
 Check for adware generated files in the /Library/LaunchAgents/ folder:
Check for adware generated files in the /Library/LaunchAgents/ folder:
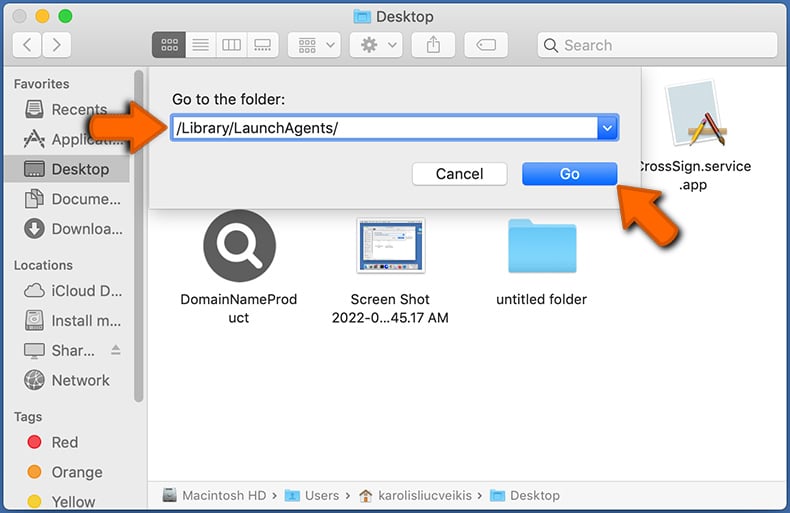
In the Go to Folder... bar, type: /Library/LaunchAgents/
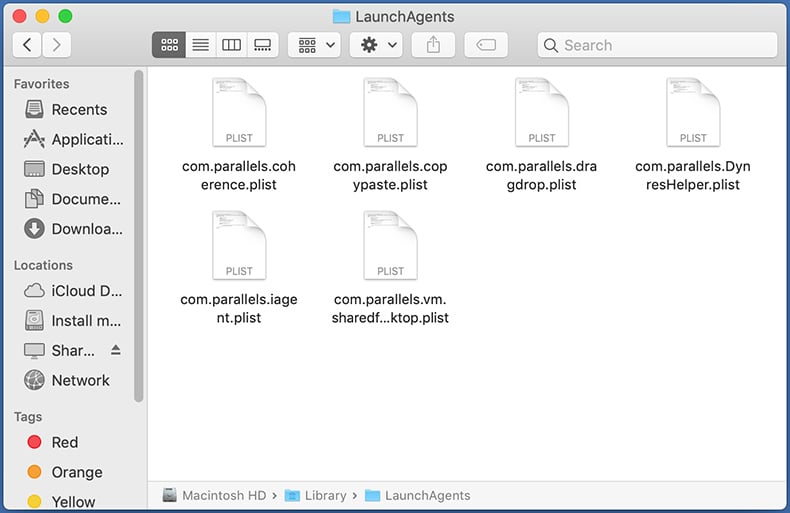
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the ~/Library/Application Support/ folder:
Check for adware generated files in the ~/Library/Application Support/ folder:
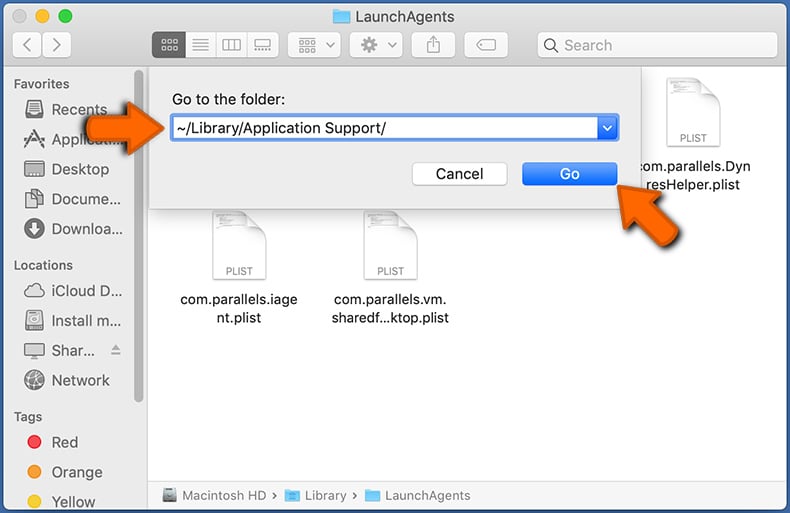
In the Go to Folder... bar, type: ~/Library/Application Support/
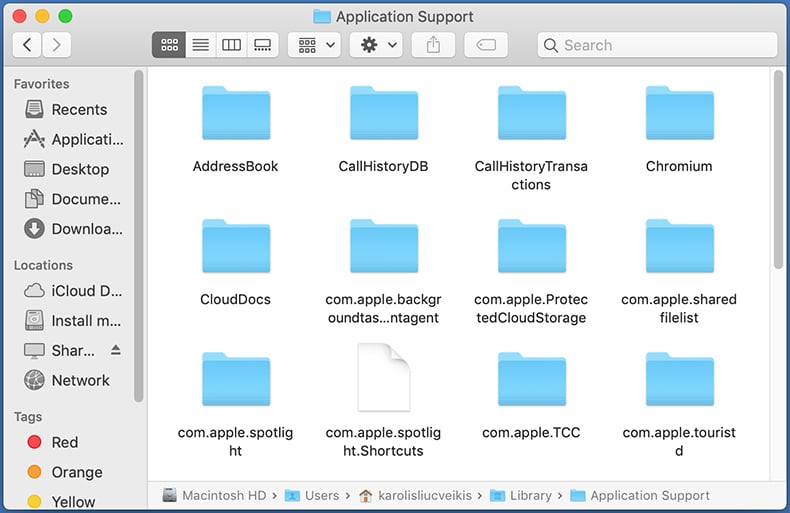
In the "Application Support" folder, look for any recently-added suspicious folders. For example, "MplayerX" or "NicePlayer", and move these folders to the Trash.
 Check for adware generated files in the ~/Library/LaunchAgents/ folder:
Check for adware generated files in the ~/Library/LaunchAgents/ folder:
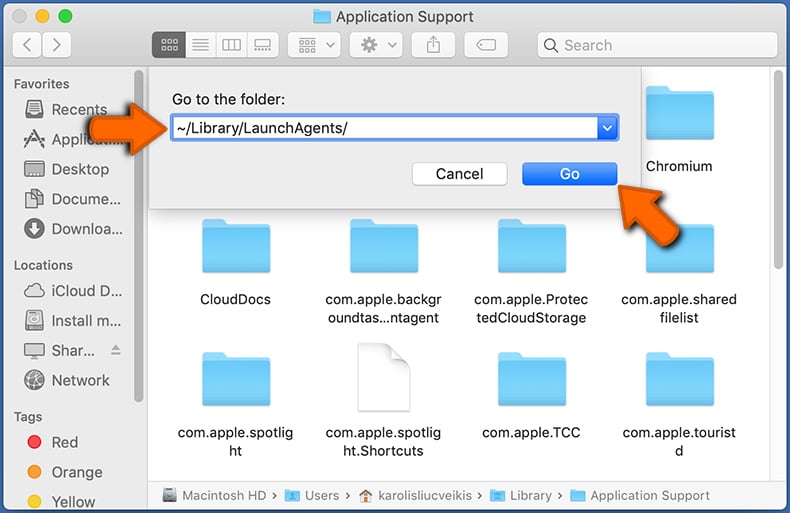
In the Go to Folder... bar, type: ~/Library/LaunchAgents/
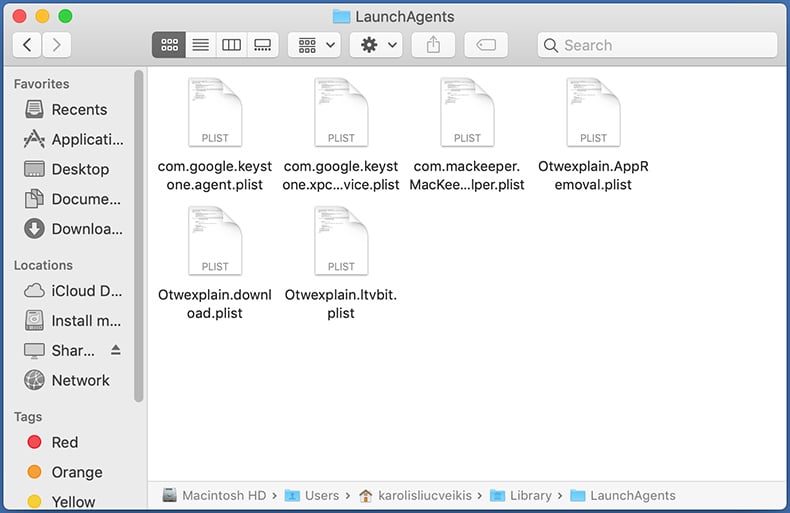
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the /Library/LaunchDaemons/ folder:
Check for adware generated files in the /Library/LaunchDaemons/ folder:
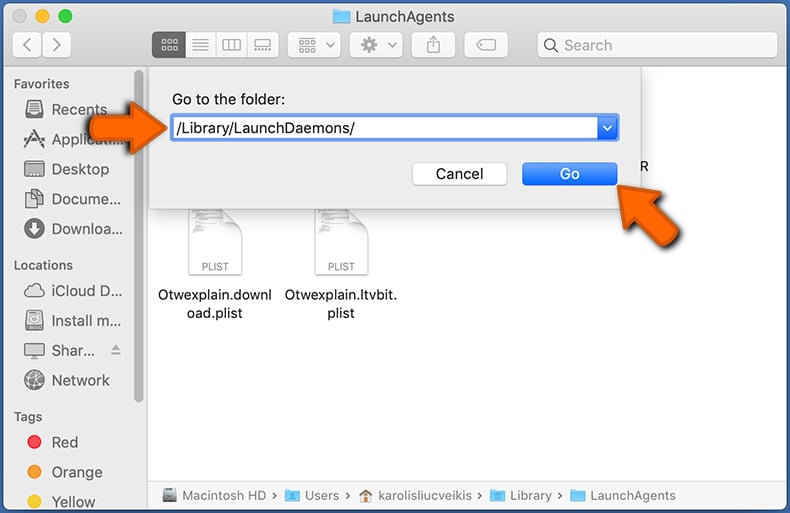
In the "Go to Folder..." bar, type: /Library/LaunchDaemons/
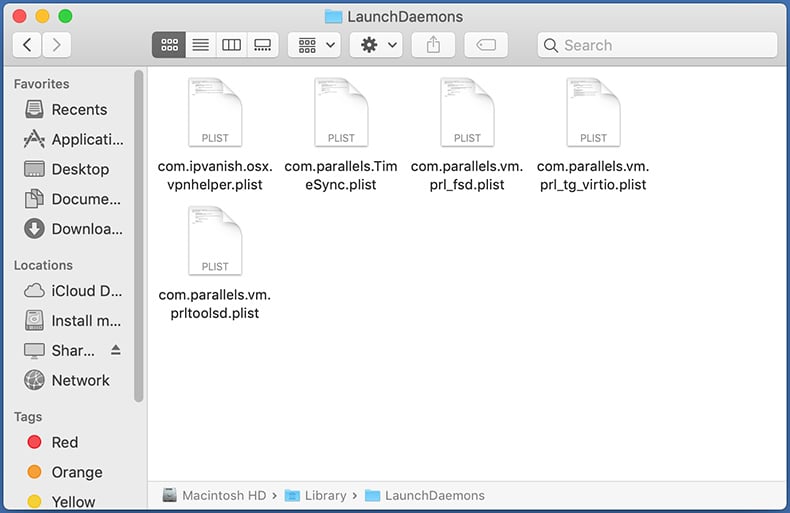
In the "LaunchDaemons" folder, look for recently-added suspicious files. For example "com.aoudad.net-preferences.plist", "com.myppes.net-preferences.plist", "com.kuklorest.net-preferences.plist", "com.avickUpd.plist", etc., and move them to the Trash.
 Scan your Mac with Combo Cleaner:
Scan your Mac with Combo Cleaner:
If you have followed all the steps correctly, your Mac should be clean of infections. To ensure your system is not infected, run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file, double click combocleaner.dmg installer. In the opened window, drag and drop the Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates its virus definition database and click the "Start Combo Scan" button.
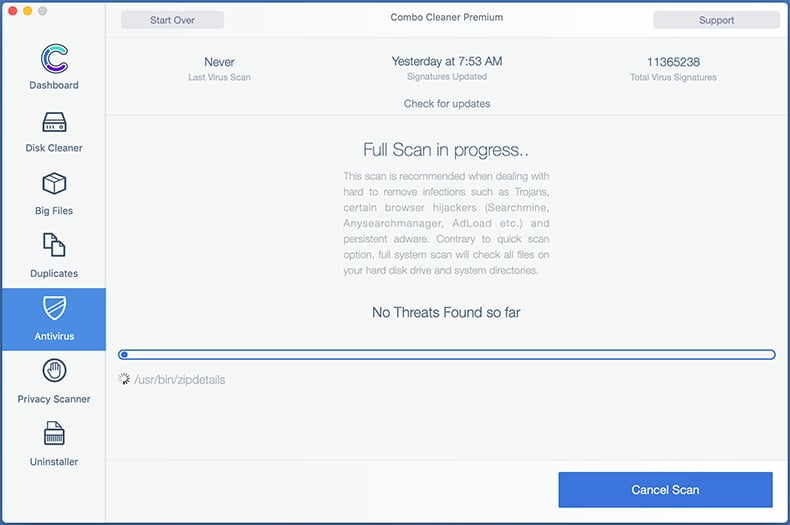
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays "no threats found" - this means that you can continue with the removal guide; otherwise, it's recommended to remove any found infections before continuing.
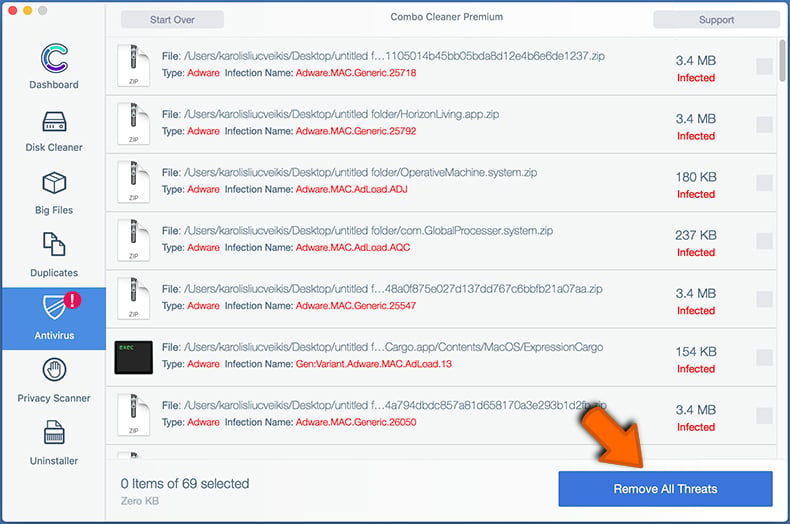
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Remove malicious extensions from Internet browsers
 Remove malicious Safari extensions:
Remove malicious Safari extensions:
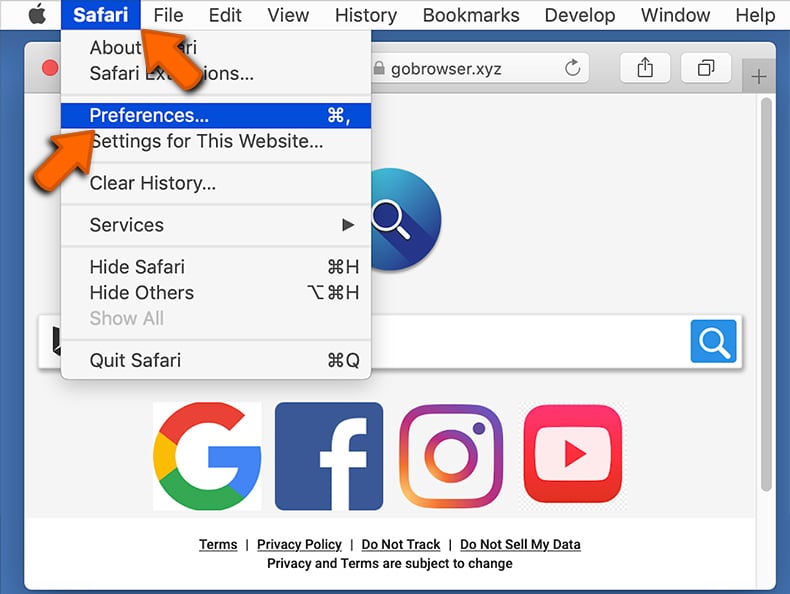
Open the Safari browser, from the menu bar, select "Safari" and click "Preferences...".
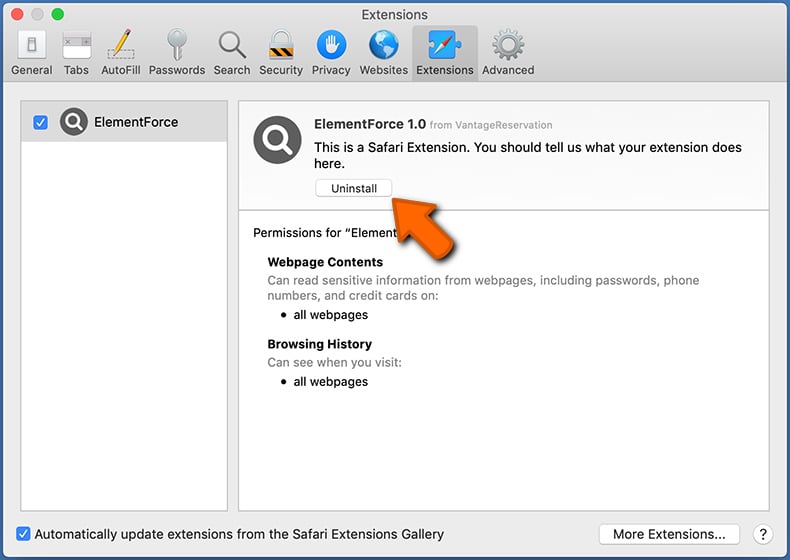
In the preferences window, select "Extensions" and look for any recently-installed suspicious extensions. When located, click the "Uninstall" button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for regular browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
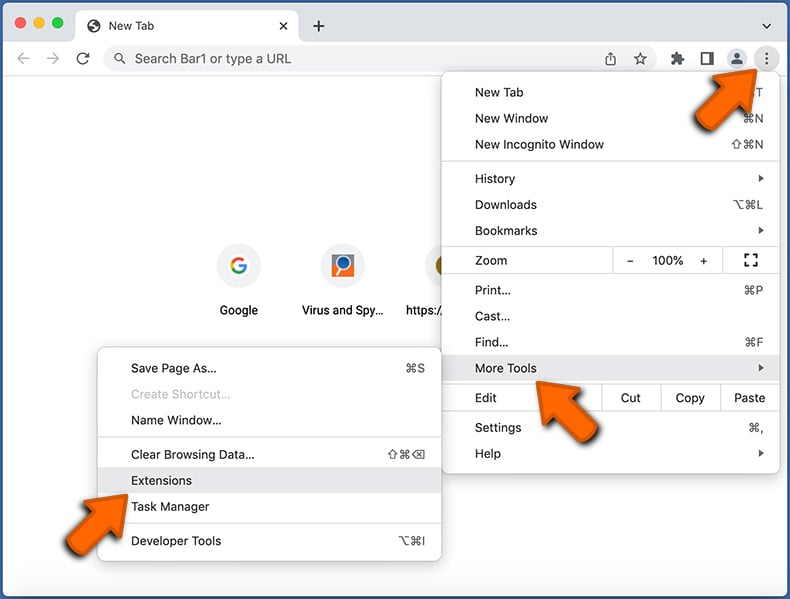
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
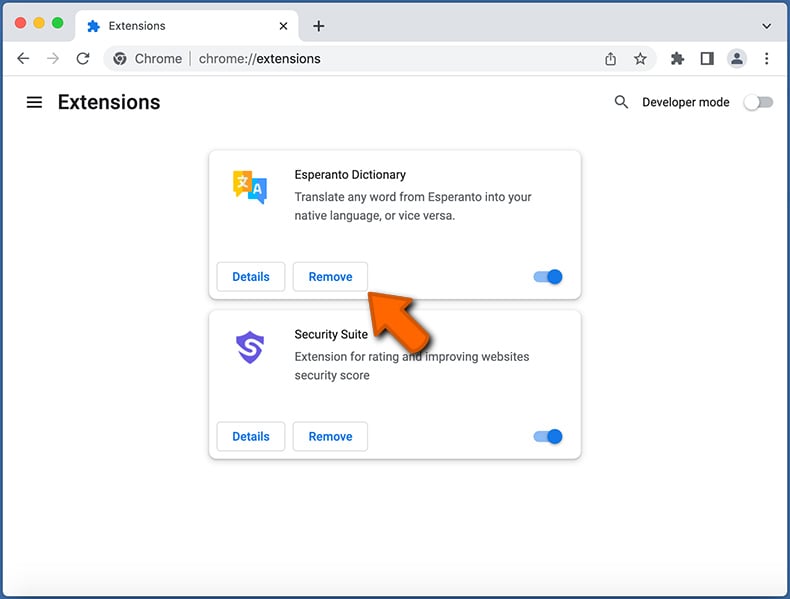
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
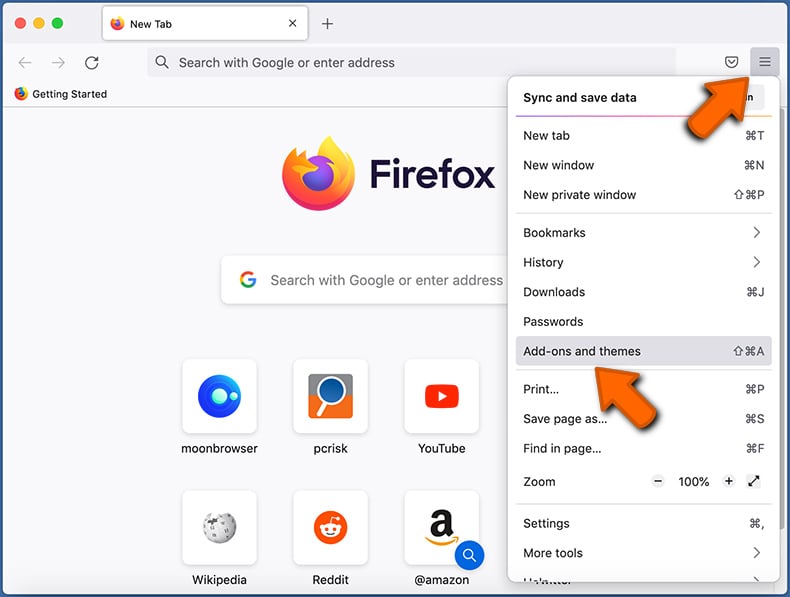
Click the Firefox menu ![]() (at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
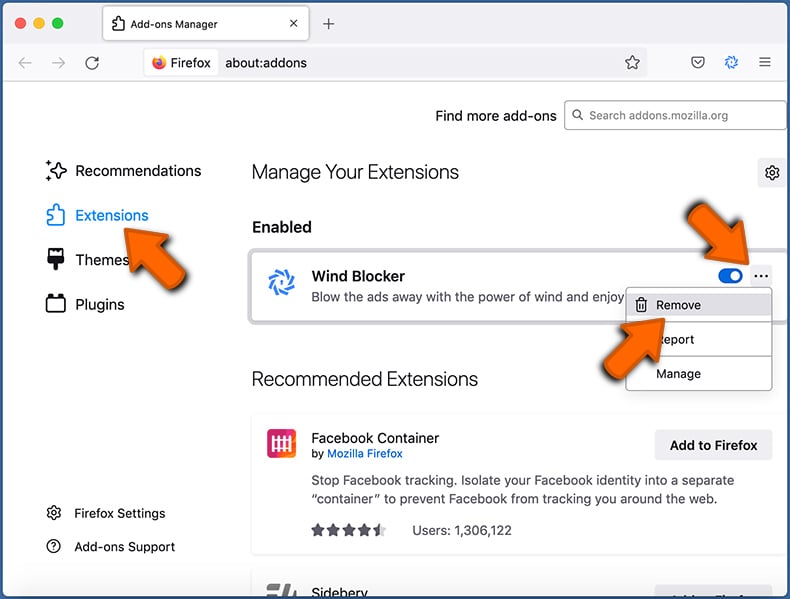
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Frequently Asked Questions (FAQ)
How was my computer hacked and how did hackers encrypt my files?
Victims themselves often execute (open) ransomware executables since these files can be disguised as or bundled with ordinary content. Ransomware-type programs are mainly distributed through drive-by downloads, spam emails/messages, online scams, untrustworthy download channels (e.g., freeware and third-party sites, P2P sharing networks, etc.), illegal software activation tools ("cracks"), and fake updates.
How to open ".lockbit" files?
If your files have been successfully encrypted by ransomware – then they can only be opened/used after being decrypted.
Where should I look for free decryption tools for LockBit ransomware?
In case of a ransomware attack, we advise you to check out the No More Ransom project website.
I can pay you a lot of money, can you decrypt files for me?
We do not offer such services. In fact, aside from cases involving deeply flawed ransomware, decryption is impossible without the cyber criminals' interference. Hence, third-parties offering paid decryption are often scams or middleman services between victims and criminals.
Will Combo Cleaner help me remove LockBit ransomware?
Yes, Combo Cleaner will scan your device and eliminate detected ransomware infections. It must be stressed that while using an anti-virus program is the first step in ransomware recovery, security software is incapable of decrypting data.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion