Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is ChromeLoader?
ChromeLoader was first analyzed by x3ph, and later dubbed by G-Data researchers as Choziosi loader. This malware is designed to install malicious extension(s) onto browsers. Currently, two distinct variants of ChromeLoader have been detected - one targeting Windows Operating Systems and another - Mac Operating Systems.
It is noteworthy that this piece of malicious software has been actively spread through Twitter in the form of QR codes promoting pirated software (predominantly video games) and media (movies/TV).
ChromeLoader malware overview
As mentioned in the introduction, ChromeLoader is intended to install malicious extensions onto browsers. The observed infection chain began with Tweets (Twitter posts) advertising pirated content through QR codes (presented in meme format) that tricked victims into downloading an ISO file.
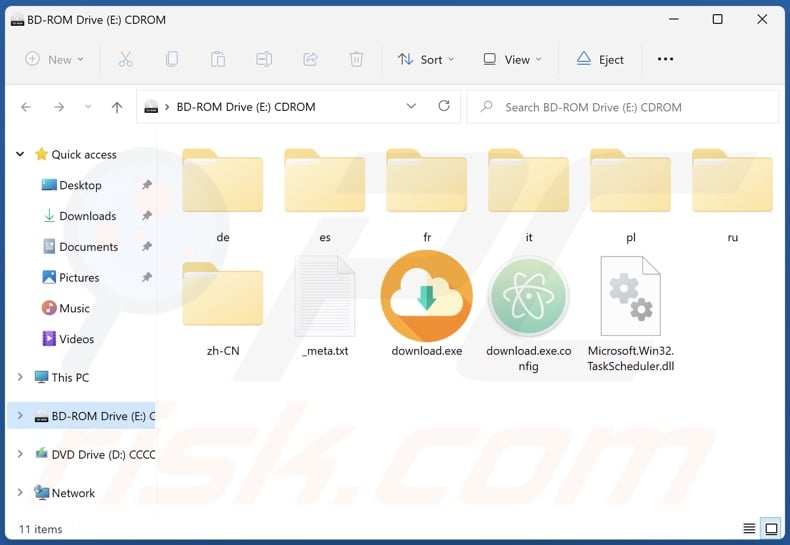
G-Data researchers performed an in-depth analysis of this loader and the malicious extension. Their research uncovered that the ISO file consists of two components - "_meta.txt" and "downloader.exe", the former contains encrypted PowerShell script while the latter is used to decrypt it.
The PowerShell creates a task titled "ChromeTask" (may vary), which is scheduled to run every ten minutes. The PowerShell script also downloads the malicious Google Chrome browser extension "archive.zip". However, due to the task repetition - some victims of this malware have reported that their Chrome browsers continuously close themselves (which is an oversight that likely encourages swifter detection of ChromeLoader).
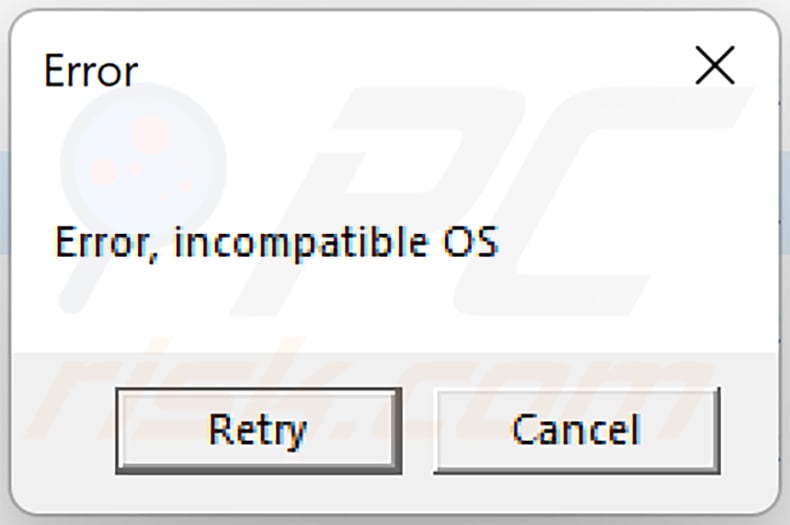
It is noteworthy that "downloader.exe" may show users an alert stating that the Operating System is incompatible with the software.
G-Data's analysis focused on the malicious browser extension as it had not been thoroughly researched prior. The Chrome extension is heavily obfuscated - which complicates analysis.
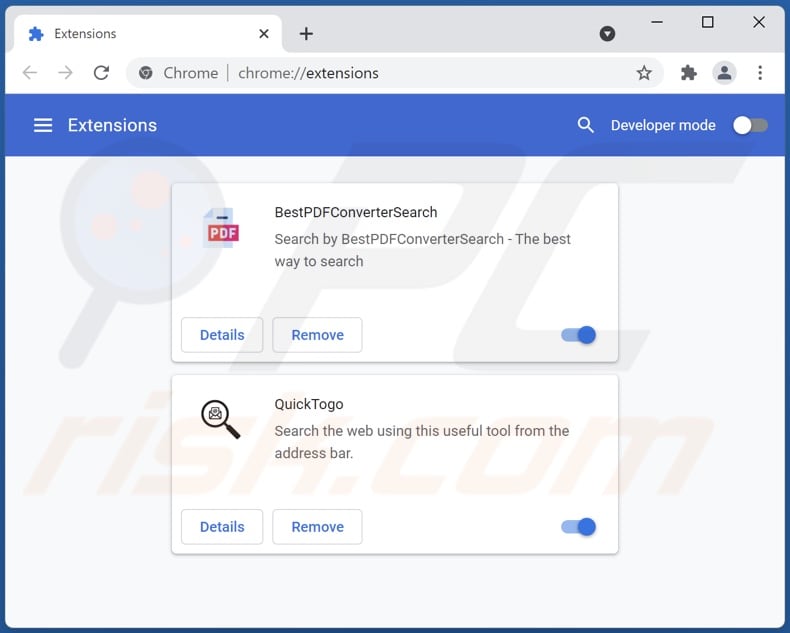
This piece of software employs persistence-ensuring techniques; specifically, it denies access to the Google Chrome extensions list ("chrome://extensions/") by redirecting users to general settings ("chrome://settings") - thereby preventing them from removing the malicious extension.
The functionalities of the Chrome extension were revealed to be adware and browser hijacker activity. In other words, this malware aims to display deceptive/malicious advertisements and modify browser settings to cause redirects to fake search engines (potentially concluding with legitimate ones like Google, Yahoo, Bing, etc.).
Using PowerShell and extensive obfuscation is uncommon for adware and browser hijackers, but it is standard for information-stealing programs, spyware, and other malware. However, it is not unlikely that ChromeLoader is still in development and will be updated with additional harmful functionalities. Regardless, ChromeLoader still poses significant threats in its current form (more information on new variants below).
The research done by Colin Cowie, determined that the Mac version of ChromeLoader operates similarly to the Windows variant (i.e., shows ads, causes redirects). What is notable about this version is that it can install malicious extensions both on Google Chrome and Safari browsers.
If you suspect that your device is infected with ChromeLoader malware, we strongly advise using an anti-virus to remove it without delay.
| Name | ChromeLoader virus |
| Threat Type | Unwanted ads, Pop-up ads, Unwanted redirects |
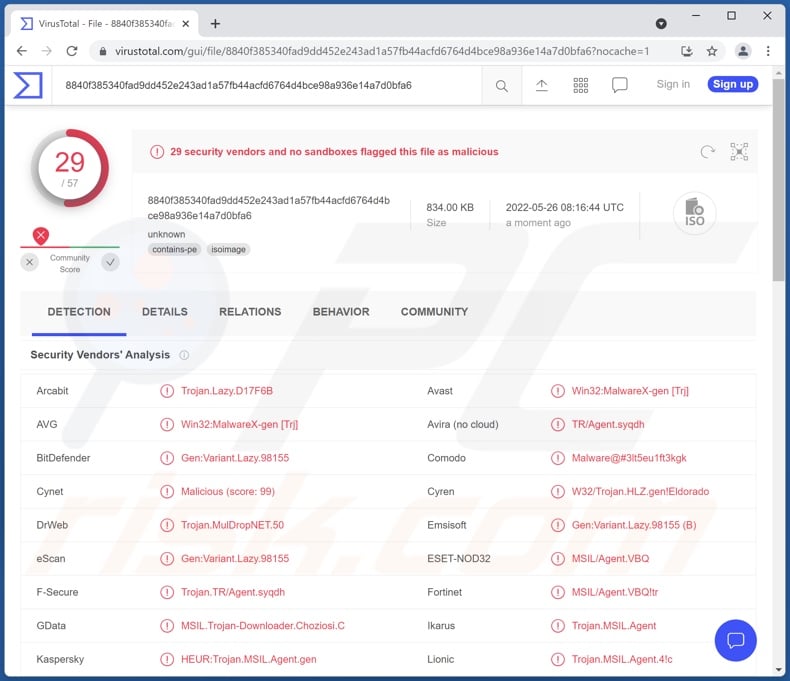
| Detection Names (ISO) | Avast (Win32:MalwareX-gen [Trj]), Combo Cleaner (Gen:Variant.Lazy.98155), ESET-NOD32 (MSIL/Agent.VBQ), Kaspersky (HEUR:Trojan.MSIL.Agent.gen), Microsoft (Trojan:MSIL/Tnega!mclg), Full List Of Detections (VirusTotal) |
| Detection Names (EXE within ISO) | Avast (Win32:MalwareX-gen [Trj]), Combo Cleaner (Trojan.GenericKD.38585118), ESET-NOD32 (MSIL/Agent.VBQ), Kaspersky (HEUR:Trojan.MSIL.Agent.gen), Microsoft (Trojan:Win32/Tnega!ml), Full List Of Detections (VirusTotal) |
| Detection Names (Mac variant) | Avast (MacOS:Agent-TJ [Trj]), Combo Cleaner (Adware.MAC.Chropex.B), GData (Adware.MAC.Chropex.B), Kaspersky (Not-a-virus:HEUR:AdWare.OSX.Agent.ag), Full List Of Detections (VirusTotal) |
| Symptoms | Seeing advertisements not originating from the sites you are browsing. Intrusive pop-up ads. Decreased Internet browsing speed. Manipulated Internet browser settings. Users are forced to visit the hijacker's website and search the Internet using their search engines. |
| Distribution Methods | Deceptive pop-up ads, false claims within visited websites, potentially unwanted applications (adware) |
| Damage | Decreased computer performance, browser tracking - privacy issues, possible additional malware infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Adware and browser hijacker examples
ChromeLoader has advertising-supported and browser-hijacker software functionalities. Typically, programs within the adware/ browser hijacker classifications do not use such sophisticated techniques as ChromeLoader (which could mean that this malware is intended to have additional malicious features like data theft, spying, etc.).
To Go Web, Keep Secure Search, Tap togo are a few examples of regular browser hijackers that we have analyzed, and fake Google Translate extension, Files Download Now, Down Assist - of adware.
Note that regardless of how a malicious program operates, its presence on a system endangers device/user safety. Therefore, all threats must be eliminated immediately upon detection.
How did ChromeLoader infiltrate my computer?
As previously detailed, ChromeLoader has been notably proliferated through Tweets promoting illegal content (i.e., pirated video games, editing software, movies, TV series, etc.) via QR codes designed to lure users into downloading an infectious ISO file. Also, it is distributed via malicious ads, browser redirects, and YouTube comments.
However, it is possible that ChromeLoader malware is distributed on other platforms and potentially under different disguises as well.
Malware is commonly spread using various techniques; phishing and social engineering are heavily used in malicious software distribution. Virulent files can be archives, executables, PDF and Microsoft Office documents, JavaScript, etc. Once a malicious file is opened - the infection chain is initiated.
The most common malware proliferation methods include: drive-by (stealthy and deceptive) downloads, spam emails/messages, online scams, freeware and third-party download websites, P2P sharing networks (e.g., Torrent clients, eMule, etc.), illegal program activation tools ("cracks"), fake updates, and malvertising.
How to avoid installation of malware?
We strongly advise exercising caution when browsing since illegitimate and malicious content tends to appear harmless. Additionally, we recommend downloading only from official and verified sources.
It is just as important to activate and update software by using functions/tools provided by genuine developers, as those acquired from third-parties may contain malware.
Another recommendation is to approach incoming mail with care. The attachments and links found in suspicious/irrelevant emails and messages - must not be opened - since that can lead to a system infection.
We must emphasize the importance of having a dependable anti-virus installed and kept updated. Security programs must be used to run regular system scans and to remove threats and issues. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Screenshot of ChromeLoader ISO file contents:
Error message displayed when ChromeLoader is executed:
Update September 20, 2022 – Recently, ChromeLoader has been used to distribute malicious browser extensions, node-WebKit malware, and even ransomware. Multiple (at least ten) Chromeloader variants have been found disguised as other programs (such as apps for searching subtitles for movies and TV shows, video players). Examples include Tone, Bloom, Energy, Healthy, Strength, Diet, OpenSubtitles Uploader, Cash, and many others.
Depending on the variant, it can be used to install the malware and establish persistence, load modules for network communication, destroy systems by overloading them with data, infect computers with ransomware (e.g., Enigma ransomware), and more.
Update February 27, 2023 – Previous ChromeLoader campaigns relied on ISO format files to initiate infection chains. However, newly discovered campaigns spread VHD files with filenames related to popular video games. The malicious files bore titles associated with the following games: Elden Ring, Dark Souls 3, ROBLOX, Pokemon, Legend of Zelda, Animal Crossing, Minecraft, Mario Kart, Red Dead Redemption 2, Portal 2, Call of Duty, Need for Speed, and others.
These ChromeLoader files were hosted on malicious websites, which were promoted using search engine poisoning techniques. Basically, the fake sites appeared in Google search results when users' searches included keywords associated with said video games.
Quick menu:
- What is ChromeLoader?
- STEP 1. Uninstall adware applications using Control Panel.
- STEP 2. Remove rogue plug-ins from Google Chrome.
- STEP 3. Remove adware-type extensions from Mozilla Firefox.
- STEP 4. Remove malicious extensions from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
Adware removal:
Windows 11 users:
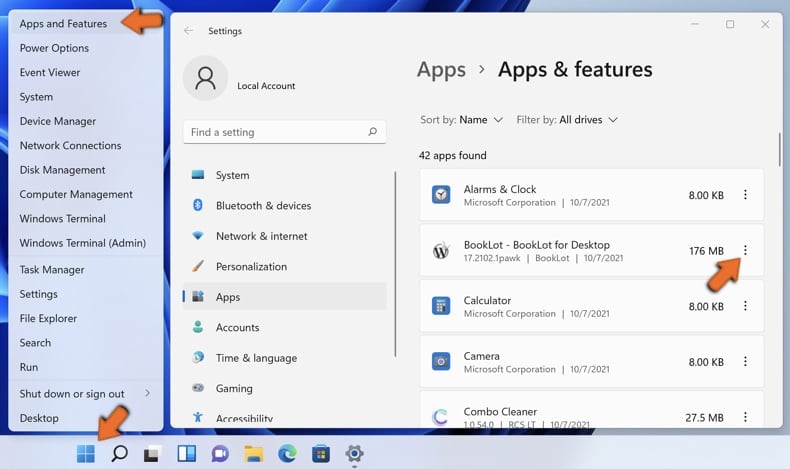
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
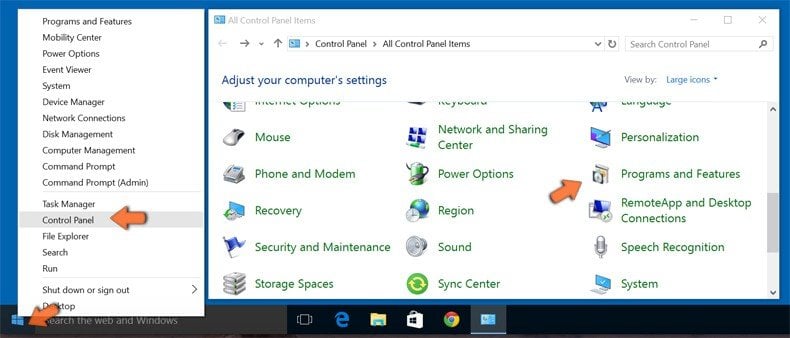
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.
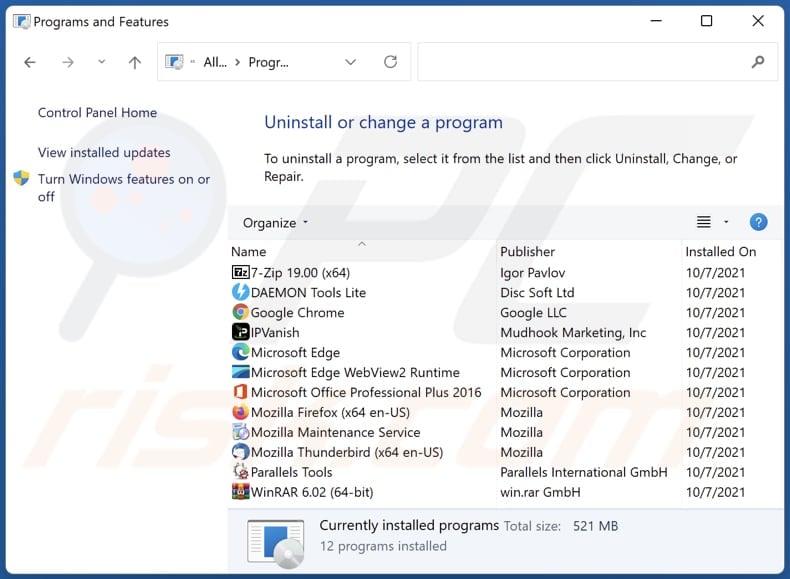
In the uninstall programs window, look for any unwanted applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the unwanted application, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware from Internet browsers:
Video showing how to remove unwanted browser add-ons:
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
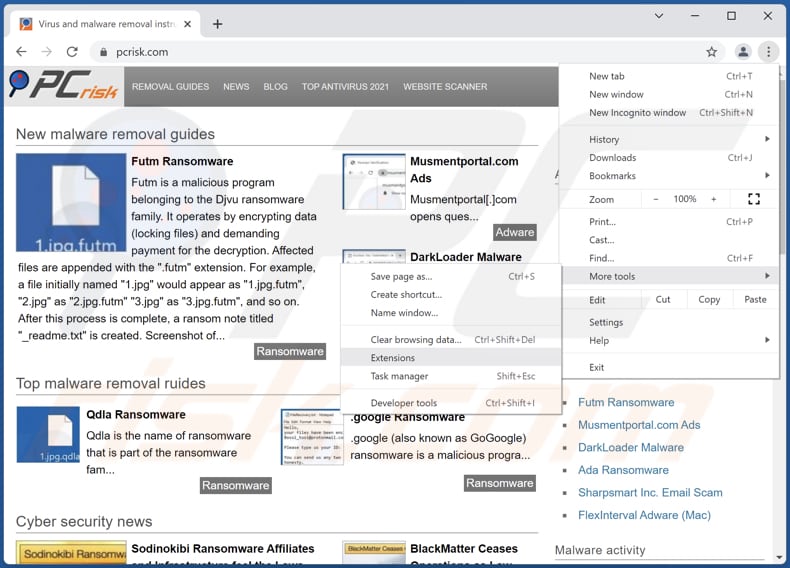
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate recently-installed suspicious browser add-ons and remove them.
(at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate recently-installed suspicious browser add-ons and remove them.
Optional method:
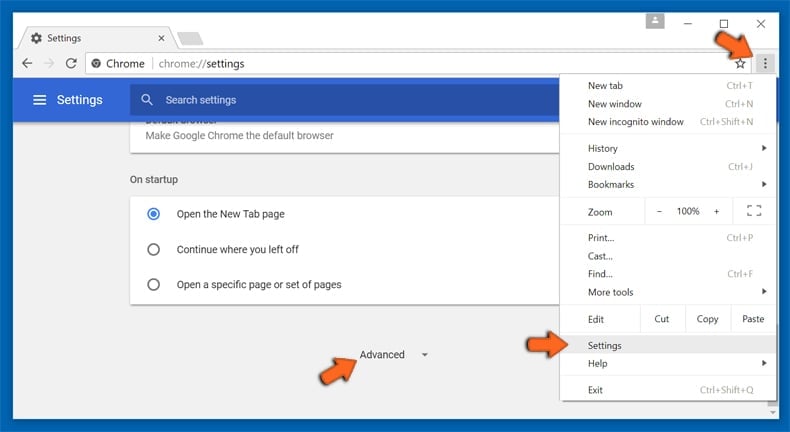
If you continue to have problems with removal of the chromeloader virus, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
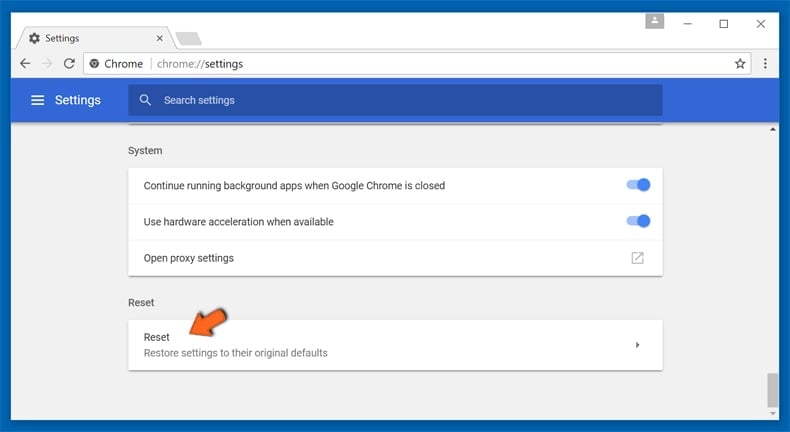
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
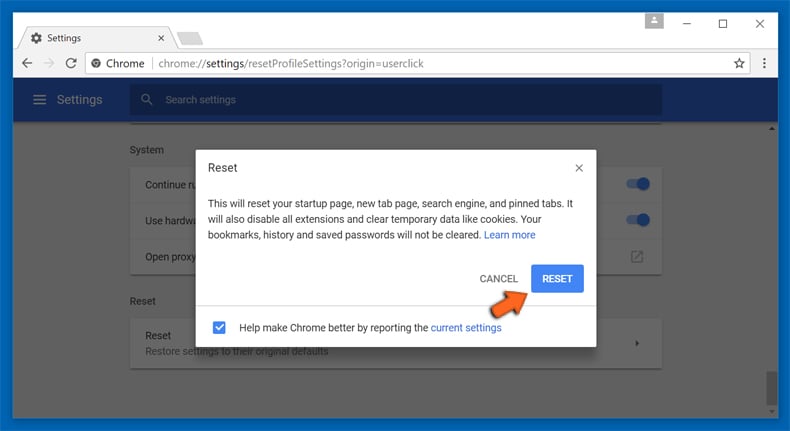
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious plug-ins from Mozilla Firefox:
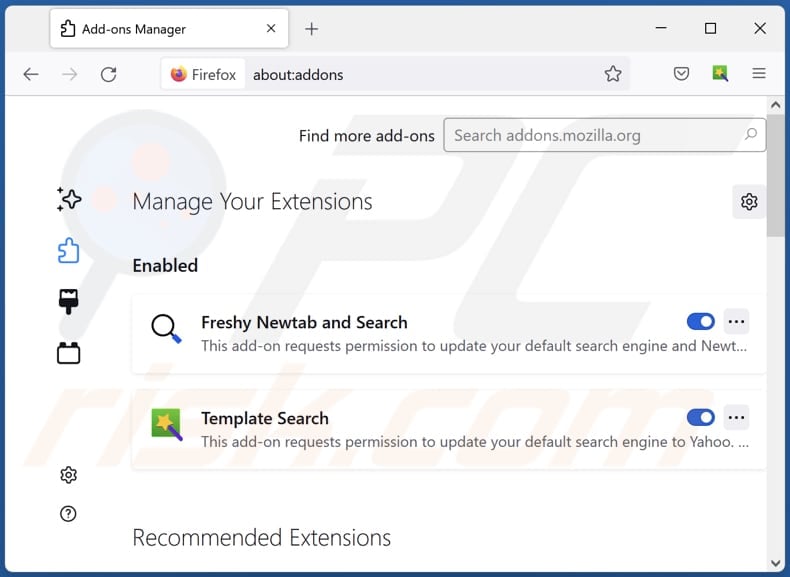
Remove malicious plug-ins from Mozilla Firefox:
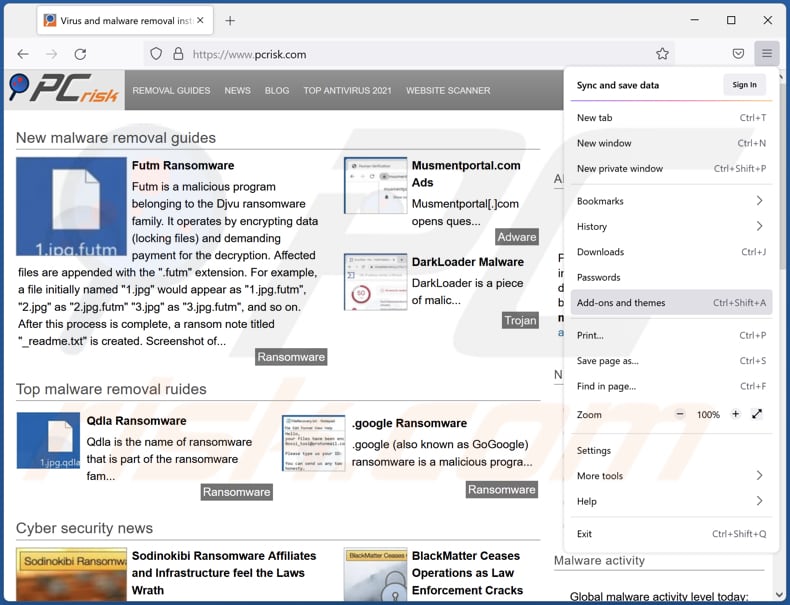
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons". Click "Extensions", in the opened window, remove all recently-installed suspicious browser plug-ins.
(at the top right corner of the main window), select "Add-ons". Click "Extensions", in the opened window, remove all recently-installed suspicious browser plug-ins.
Optional method:
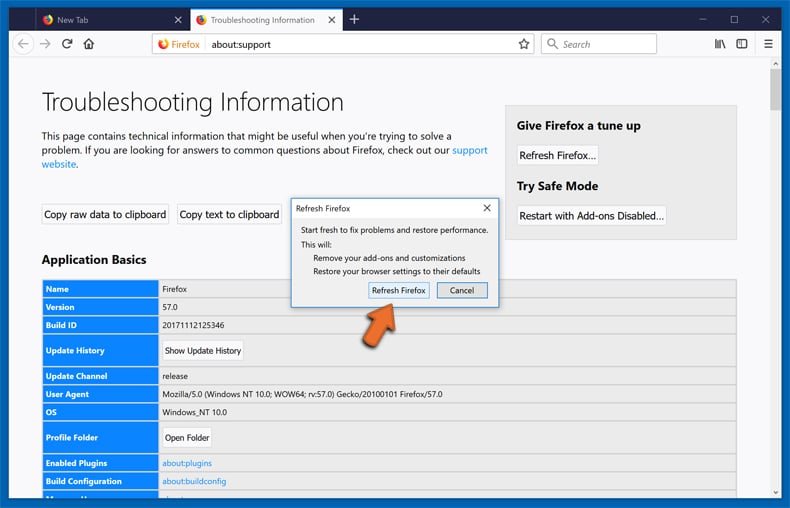
Computer users who have problems with chromeloader virus removal can reset their Mozilla Firefox settings.
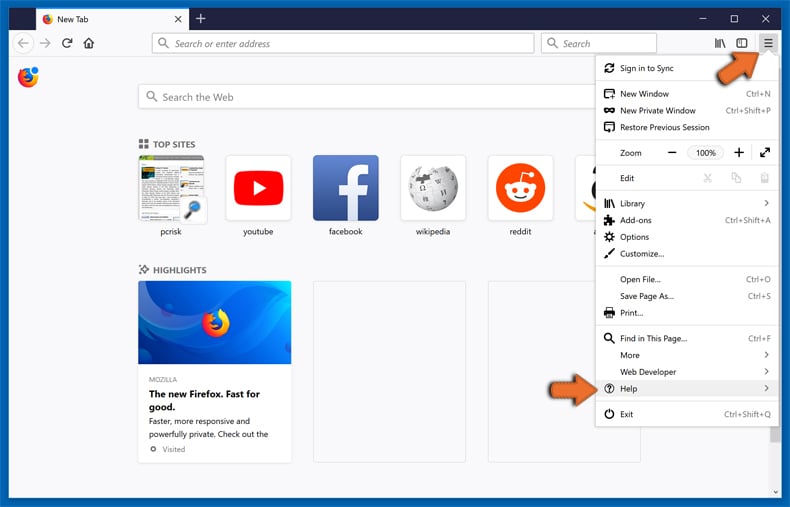
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
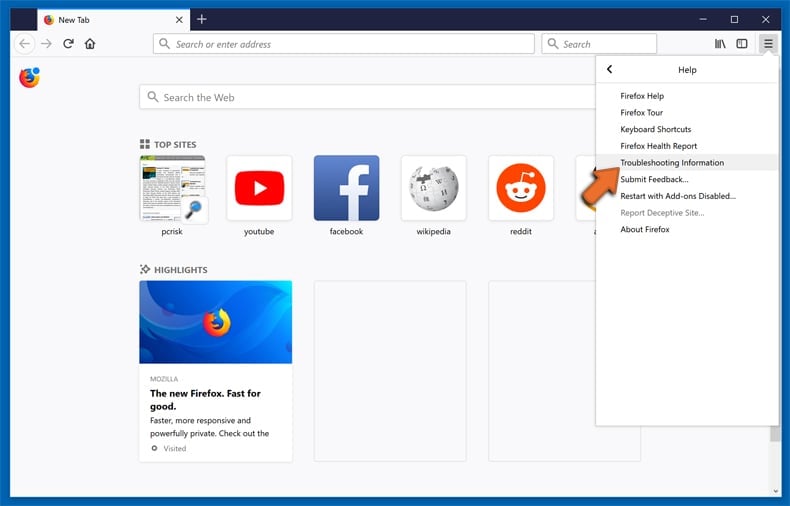
Select Troubleshooting Information.
In the opened window, click the Refresh Firefox button.
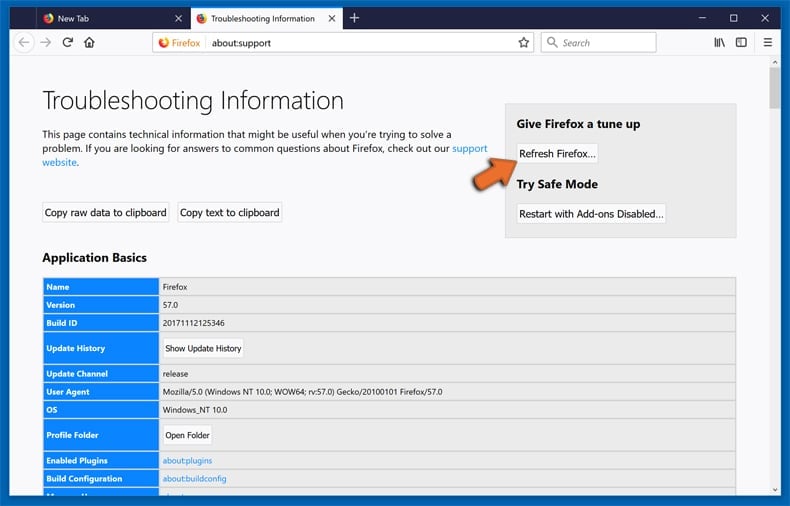
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
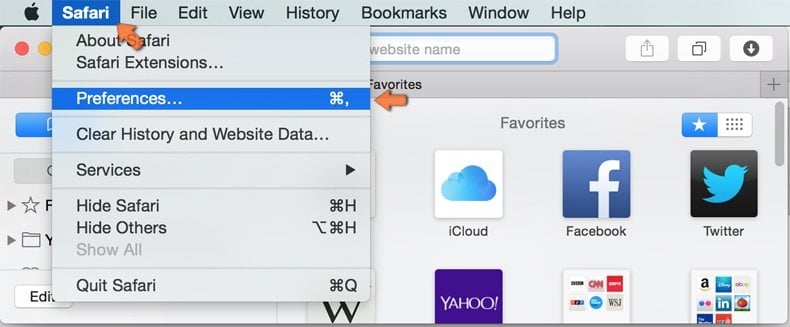
Make sure your Safari browser is active and click Safari menu, then select Preferences...
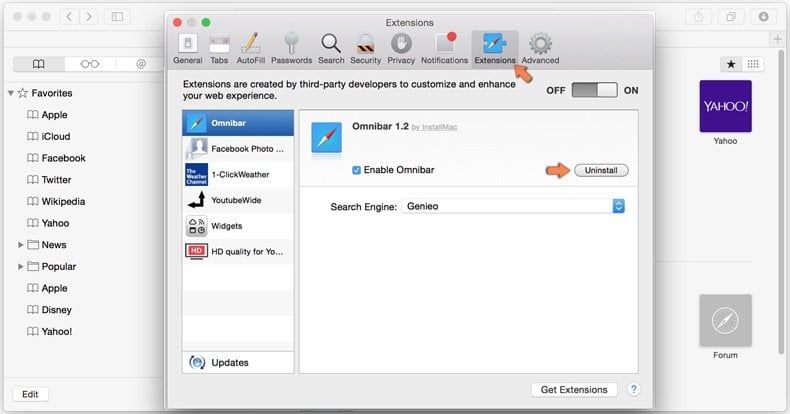
In the preferences window select the Extensions tab. Look for any recently installed suspicious extensions and uninstall them.
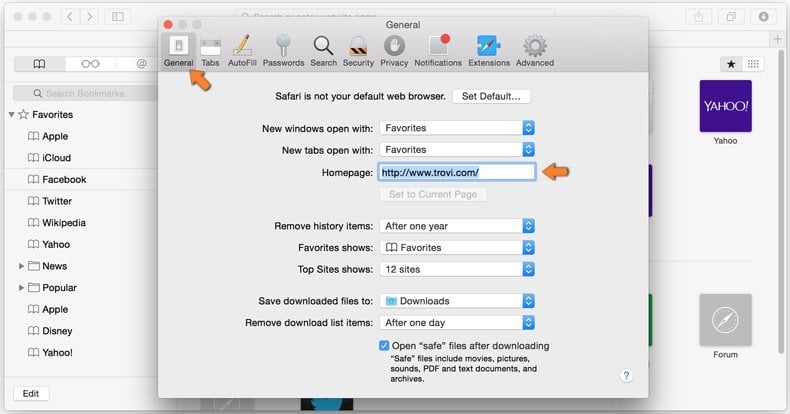
In the preferences window select General tab and make sure that your homepage is set to a preferred URL, if its altered by a browser hijacker - change it.
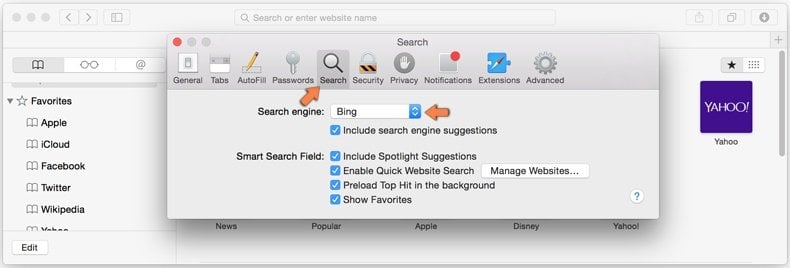
In the preferences window select Search tab and make sure that your preferred Internet search engine is selected.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
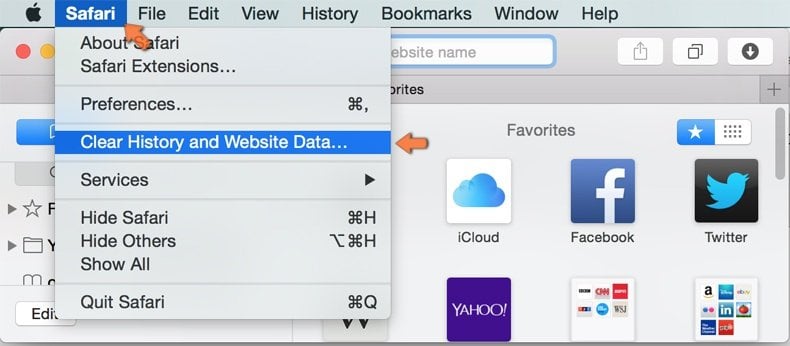
In the opened window select all history and click the Clear History button.

If you continue having problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
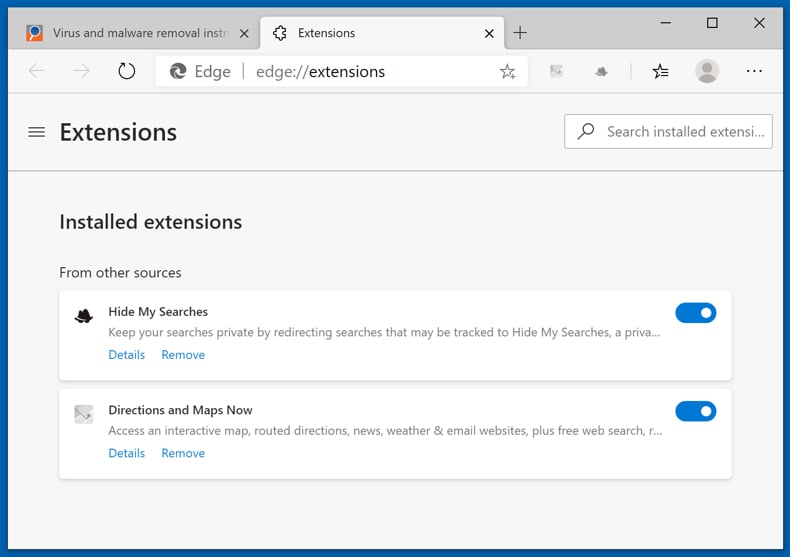
Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Extensions". Locate any recently-installed suspicious browser add-ons, and remove them.
(at the top right corner of Microsoft Edge), select "Extensions". Locate any recently-installed suspicious browser add-ons, and remove them.
Change your homepage and new tab settings:
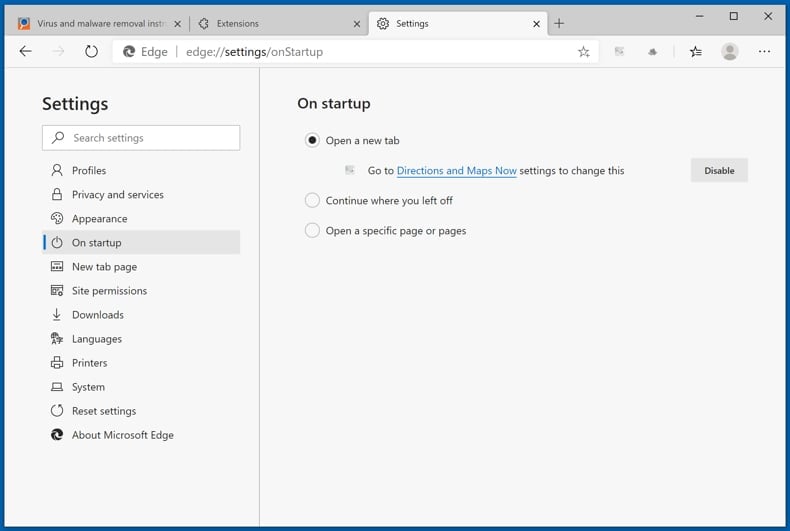
Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Settings". In the "On startup" section look for the name of the browser hijacker and click "Disable".
(at the top right corner of Microsoft Edge), select "Settings". In the "On startup" section look for the name of the browser hijacker and click "Disable".
Change your default Internet search engine:
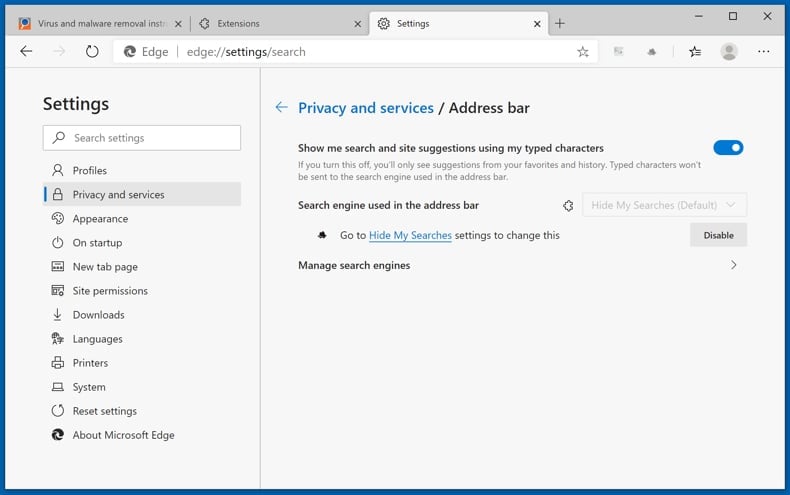
To change your default search engine in Microsoft Edge: Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Privacy and services", scroll to bottom of the page and select "Address bar". In the "Search engines used in address bar" section look for the name of the unwanted Internet search engine, when located click the "Disable" button near it. Alternatively you can click on "Manage search engines", in the opened menu look for unwanted Internet search engine. Click on the puzzle icon
(at the top right corner of Microsoft Edge), select "Privacy and services", scroll to bottom of the page and select "Address bar". In the "Search engines used in address bar" section look for the name of the unwanted Internet search engine, when located click the "Disable" button near it. Alternatively you can click on "Manage search engines", in the opened menu look for unwanted Internet search engine. Click on the puzzle icon ![]() near it and select "Disable".
near it and select "Disable".
Optional method:
If you continue to have problems with removal of the chromeloader virus, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
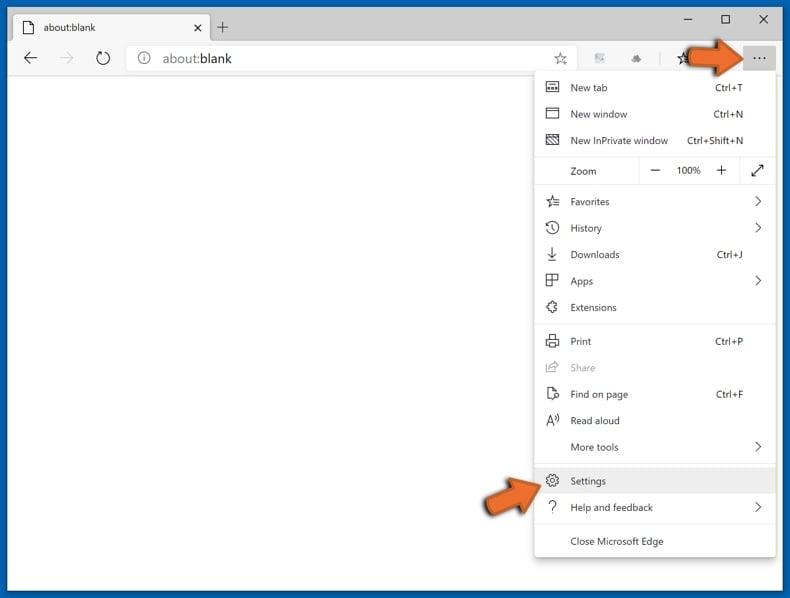
In the opened settings menu select Reset settings.
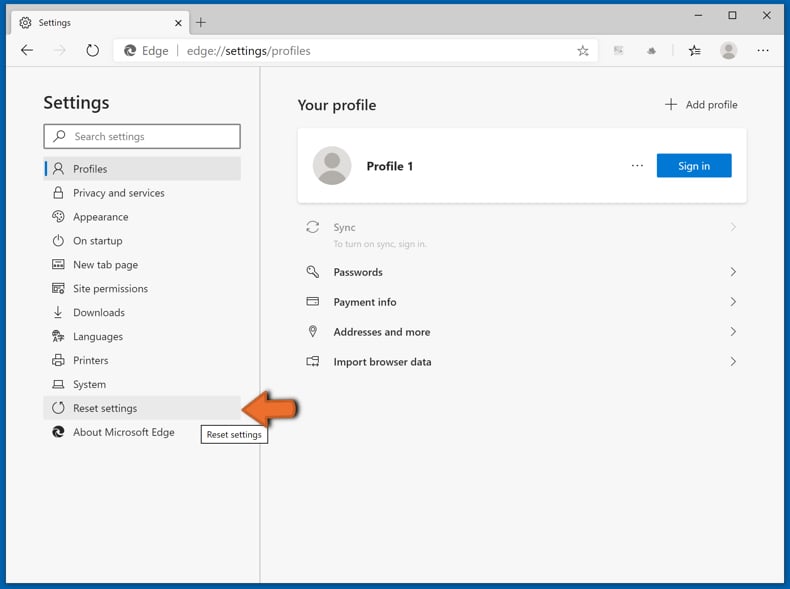
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
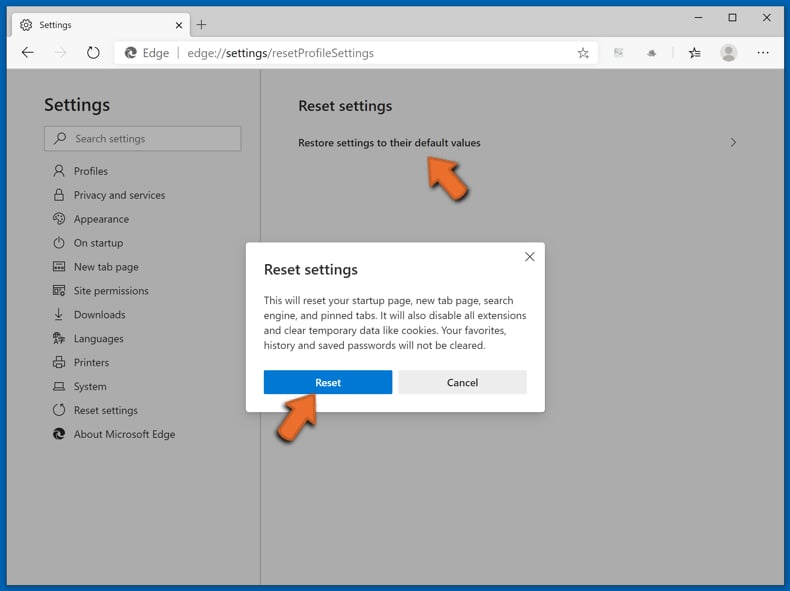
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
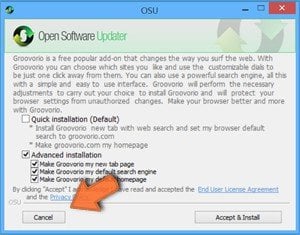 A browser hijacker is a type of adware infection that modifies Internet browser settings by assigning the homepage and default Internet search engine settings to some other (unwanted) website URL. Commonly, this type of adware infiltrates operating systems through free software downloads. If your download is managed by a download client, ensure that you decline offers to install advertised toolbars or applications that seek to change your homepage and default Internet search engine settings.
A browser hijacker is a type of adware infection that modifies Internet browser settings by assigning the homepage and default Internet search engine settings to some other (unwanted) website URL. Commonly, this type of adware infiltrates operating systems through free software downloads. If your download is managed by a download client, ensure that you decline offers to install advertised toolbars or applications that seek to change your homepage and default Internet search engine settings.
Post a comment:
If you have additional information on chromeloader virus or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
What is the purpose of ChromeLoader malware?
ChromeLoader is designed to install malicious extensions onto victims' browsers. At the time of research, ChromeLoader's browser extension exhibited adware and browser hijacker qualities. In other words, it displayed ads and modified browser settings to cause redirects. Due to the rather complicated make of ChromeLoader, it is possible that this malicious program will be updated with more harmful features (e.g., extraction of sensitive data, recording information, etc.).
What are the threats posed by adware and browser hijacker infections?
Browser hijackers alter browser settings (and can use persistence-ensuring tactics to prevent users from accessing/changing them) to cause redirects to fake search engines. The redirects can occur when new browser tabs/windows are opened, search queries are typed into the URL bar, etc. Illegitimate search engines typically collect information about their visitors. Since these websites are rarely capable of generating search results, they redirect to legitimate ones (e.g., Google, Bing, Yahoo, etc.).
Adware is designed to display advertisements on visited websites and/or other interfaces; some types can also force-open sites and gather private data. The delivered ads are known to promote deceptive/malicious content, and some can make stealthy downloads/installations (when clicked).
Therefore, the presence of these programs on a device can lead to system infections, severe privacy issues, financial losses, and identity theft.
How did ChromeLoader malware infiltrate my computer?
ChromeLoader has been actively proliferated through Twitter posts promoting pirated programs/media via QR codes that trick users into installing a virulent ISO file. In general, malware is primarily spread through drive-by downloads, online scams, spam emails and messages, untrustworthy download sources (e.g., unofficial and freeware websites, Peer-to-Peer sharing networks, etc.), illegal program activation ("cracking") tools, fake updates, and malicious advertisemets.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and eliminate almost all known malware infections. However, performing a complete system scan is essential - since high-end malicious programs usually hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion